Apple to Shatter the Walled Garden with iOS 27 “AI Extensions” and Third-Party Model Swapping
The post Apple to Shatter the Walled Garden with iOS 27 “AI Extensions” and Third-Party Model Swapping appeared first on Daily CyberSecurity.
Malicious browser extensions disguised as TikTok downloaders compromised 130,000 users, exposing a growing blind spot in enterprise security.
The post Malicious TikTok Downloader Extensions Quietly Compromised 130K Users appeared first on TechRepublic.
Researchers linked 108 malicious Chrome extensions to a coordinated campaign that exposed about 20,000 users to data theft, backdoors, and ad injection.
The post Massive Chrome Extension Scam Exposes 20,000 Users to Data Theft appeared first on TechRepublic.

How many browsers extensions do you have running? Most enterprise users have at least one and seven out of ten have seen an extension expand its permissions over the last 12 months—with AI extensions being the worst offenders…by sixfold.
The post Over Permissive and Proliferating, AI-Driven Browser Extensions Create Security Blindspots appeared first on Security Boulevard.

![]()
{ "extensionPack": ["xdebug.php-debug", "zobo.php-intellisense"] }However, GlassWorm operators have repurposed this functionality to distribute malware indirectly through open VSX extensions. Because these manifest fields do not require extensions to share the same publisher or namespace, any extension author can reference any other extension. This design allows attackers to publish seemingly harmless extensions that later become indirect malware installers.
OX Security researchers warn that security flaws in four widely used VS Code extensions (Live Server, Code Runner, Markdown Preview Enhanced, and Microsoft Live Preview) could allow attackers to steal local files and execute code remotely. These extensions have been installed over 125 million times, putting many users at risk.
“The OX Security Research team found vulnerabilities in four popular VS Code extensions (later confirmed on Cursor and Windsurf). Three were assigned CVEs – CVE-2025-65715, CVE-2025-65716, and CVE-2025-65717 – totaling over 120 million downloads and posing a significant threat to developers worldwide.” reads the report published by OX Security. “Our research demonstrates that a hacker needs only one malicious extension, or a single vulnerability within one extension, to perform lateral movement and compromise entire organizations.“
Below are the flaws discovered by the researchers:
| CVE ID | Extension Name | CVSS Score | Downloads | Vulnerability | Affected Versions | Link |
| CVE-2025-65717 | Live Server | 9.1 | 72M+ | Remote file exfiltration | All versions | Marketplace |
| CVE-2025-65715 | Code Runner | 7.8 | 37M+ | Remote code execution | All versions | Marketplace |
| CVE-2025-65716 | Markdown Preview Enhanced | 8.8 | 8.5M+ | JavaScript code execution leading to local port scanning with potential data exfiltration | All versions | Marketplace |
| No CVE issued | Microsoft Live Preview | 11M+ | One-Click XSS to full IDE files exfiltration | Fixed in v0.4.16+ (no CVE issued, no proper credit) |
IDE extensions act like mini-admins with broad access to users’ systems. If users install poorly designed or malicious extensions, attackers can run code, modify files, and take over their machines. Opening a project or clicking a file can let attackers move laterally, steal data, and gain full control, putting sensitive information at high risk.
Researchers disclosed three vulnerabilities in July–August 2025 but received no response from the maintainers, despite reaching out via email, GitHub, and social media. Months of disclosure attempts went unanswered, highlighting a systemic issue: extension security lacks accountability and incentives for timely fixes.
The experts remark that current “install at your own risk” model is no longer safe. Solutions include mandatory security reviews before publishing, AI-powered vulnerability scanning, and enforceable maintainer response rules. As AI coding assistants speed development and reliance on extensions grows, securing developer tools must start at the source.
The experts recommend users should avoid opening untrusted HTML while localhost servers run and avoid running unnecessary servers. They should never paste or run unverified snippets in global settings.json. Users must install only trusted extensions, monitor or back up settings.json, disable or remove non-essential extensions, harden local networks with firewalls, and promptly apply security updates to IDEs, extensions, OS, and development dependencies.
“The vulnerabilities discovered in these widely adopted VS Code extensions – collectively downloaded over 128 million times – expose a critical blind spot in modern development security.” concludes the report. “While organizations invest heavily in securing production environments, the developer’s local machine remains a largely unprotected gateway to an organization’s most sensitive assets.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, VS Code extensions)
Researchers have found yet another family of malicious extensions in the Chrome Web Store. This time, 30 different Chrome extensions were found stealing credentials from more than 260,000 users.
The extensions rendered a full-screen iframe pointing to a remote domain. This iframe overlaid the current webpage and visually appeared as the extension’s interface. Because this functionality was hosted remotely, it was not included in the review that allowed the extensions into the Web Store.
In other recent findings, we reported about extensions spying on ChatGPT chats, sleeper extensions that monitored browser activity, and a fake extension that deliberately caused a browser crash.
To spread the risk of detections and take-downs, the attackers used a technique known as “extension spraying.” This means they used different names and unique identifiers for basically the same extension.
What often happens is that researchers provide a list of extension names and IDs, and it’s up to users to figure out whether they have one of these extensions installed.
Searching by name is easy when you open your “Manage extensions” tab, but unfortunately extension names are not unique. You could, for example, have the legitimate extension installed that a criminal tried to impersonate.
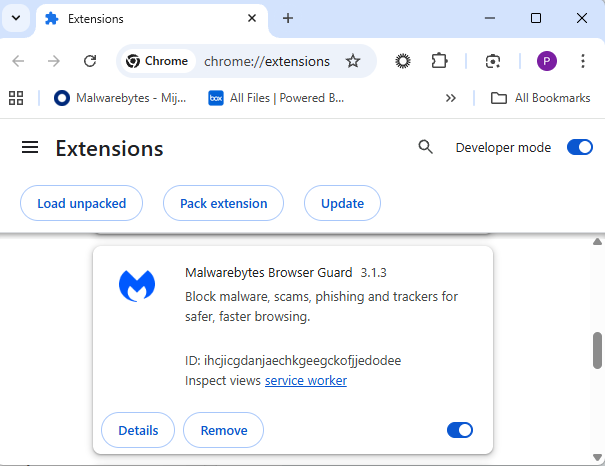
For Chrome and Edge, a browser extension ID is a unique 32‑character string of lowercase letters that stays the same even if the extension is renamed or reshipped.
When we’re looking at the extensions from a removal angle, there are two kinds: those installed by the user, and those force‑installed by other means (network admin, malware, Group Policy Object (GPO), etc.).
We will only look at the first type in this guide—the ones users installed themselves from the Web Store. The guide below is aimed at Chrome, but it’s almost the same for Edge.
You can review the installed Chrome extensions like this:
chrome://extensions/.
Use the Remove button to get rid of any unwanted entries.
If it disappears and stays gone after restart, you’re done. If there is no Remove button or Chrome says it’s “Installed by your administrator,” or the extension reappears after a restart, there’s a policy, registry entry, or malware forcing it.
Alternatively, you can also search the Extensions folder. On Windows systems this folder lives here: C:\Users\<your‑username>\AppData\Local\Google\Chrome\User Data\Default\Extensions.
Please note that the AppData folder is hidden by default. To unhide files and folders in Windows, open Explorer, click the View tab (or menu), and check the Hidden items box. For more advanced options, choose Options > Change folder and search options > View tab, then select Show hidden files, folders, and drives.

You can organize the list alphabetically by clicking on the Name column header once or twice. This makes it easier to find extensions if you have a lot of them installed.
Deleting the extension folder here has one downside. It leaves an orphaned entry in your browser. When you start Chrome again after doing this, the extension will no longer load because its files are gone. But it will still show up in the Extensions tab, only without the appropriate icon.
So, our advice is to remove extensions in the browser when possible.
Below is the list of credential-stealing extensions using the iframe method, as provided by the researchers.
| Extension ID | Extension name |
|---|---|
| acaeafediijmccnjlokgcdiojiljfpbe | ChatGPT Translate |
| baonbjckakcpgliaafcodddkoednpjgf | XAI |
| bilfflcophfehljhpnklmcelkoiffapb | AI For Translation |
| cicjlpmjmimeoempffghfglndokjihhn | AI Cover Letter Generator |
| ckicoadchmmndbakbokhapncehanaeni | AI Email Writer |
| ckneindgfbjnbbiggcmnjeofelhflhaj | AI Image Generator Chat GPT |
| cmpmhhjahlioglkleiofbjodhhiejhei | AI Translator |
| dbclhjpifdfkofnmjfpheiondafpkoed | Ai Wallpaper Generator |
| djhjckkfgancelbmgcamjimgphaphjdl | AI Sidebar |
| ebmmjmakencgmgoijdfnbailknaaiffh | Chat With Gemini |
| ecikmpoikkcelnakpgaeplcjoickgacj | Ai Picture Generator |
| fdlagfnfaheppaigholhoojabfaapnhb | Google Gemini |
| flnecpdpbhdblkpnegekobahlijbmfok | ChatGPT Picture Generator |
| fnjinbdmidgjkpmlihcginjipjaoapol | Email Generator AI |
| fpmkabpaklbhbhegegapfkenkmpipick | Chat GPT for Gmail |
| fppbiomdkfbhgjjdmojlogeceejinadg | Gemini AI Sidebar |
| gcfianbpjcfkafpiadmheejkokcmdkjl | Llama |
| gcdfailafdfjbailcdcbjmeginhncjkb | Grok Chatbot |
| gghdfkafnhfpaooiolhncejnlgglhkhe | AI Sidebar |
| gnaekhndaddbimfllbgmecjijbbfpabc | Ask Gemini |
| gohgeedemmaohocbaccllpkabadoogpl | DeepSeek Chat |
| hgnjolbjpjmhepcbjgeeallnamkjnfgi | AI Letter Generator |
| idhknpoceajhnjokpnbicildeoligdgh | ChatGPT Translation |
| kblengdlefjpjkekanpoidgoghdngdgl | AI GPT |
| kepibgehhljlecgaeihhnmibnmikbnga | DeepSeek Download |
| lodlcpnbppgipaimgbjgniokjcnpiiad | AI Message Generator |
| llojfncgbabajmdglnkbhmiebiinohek | ChatGPT Sidebar |
| nkgbfengofophpmonladgaldioelckbe | Chat Bot GPT |
| nlhpidbjmmffhoogcennoiopekbiglbp | AI Assistant |
| phiphcloddhmndjbdedgfbglhpkjcffh | Asking Chat Gpt |
| pgfibniplgcnccdnkhblpmmlfodijppg | ChatGBT |
| cgmmcoandmabammnhfnjcakdeejbfimn | Grok |
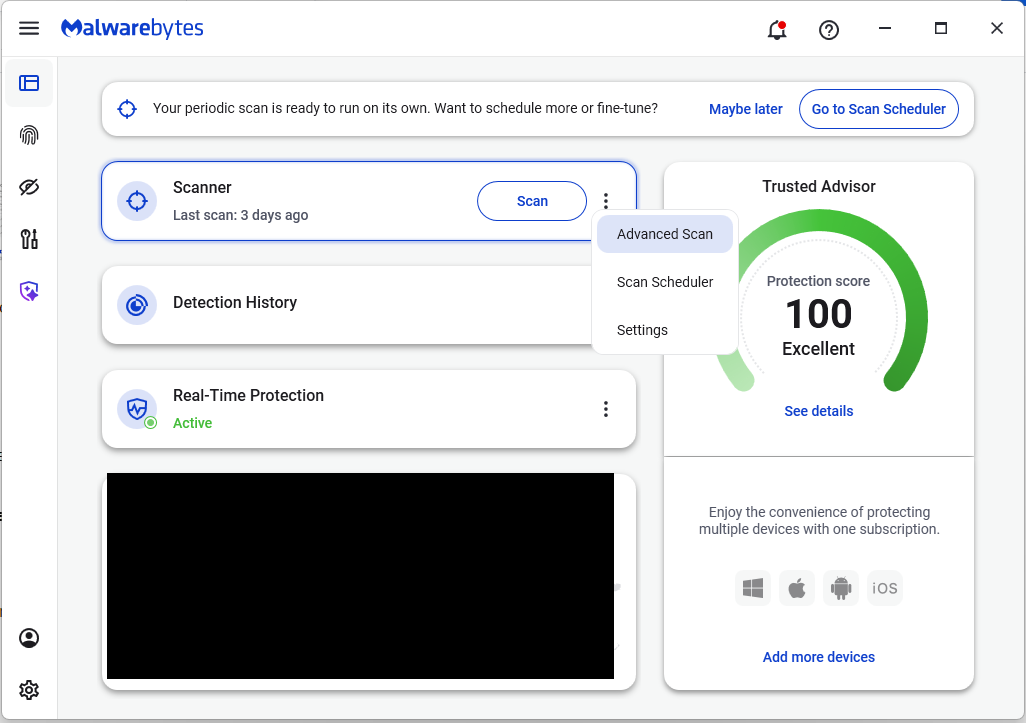
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
A zero-click flaw in Anthropic’s Claude Desktop Extensions allows attackers to trigger remote code execution via Google Calendar events.
The post 10K Claude Desktop Users Exposed by Zero-Click Vulnerability appeared first on TechRepublic.
Cybercriminals behind a campaign dubbed DEAD#VAX are taking phishing one step further by delivering malware inside virtual hard disks that pretend to be ordinary PDF documents. Open the wrong “invoice” or “purchase order” and you won’t see a document at all. Instead, Windows mounts a virtual drive that quietly installs AsyncRAT, a backdoor Trojan that allows attackers to remotely monitor and control your computer.
It’s a remote access tool, which means attackers gain remote hands‑on‑keyboard control, while traditional file‑based defenses see almost nothing suspicious on disk.
From a high-level view, the infection chain is long, but every step looks just legitimate enough on its own to slip past casual checks.
Victims receive phishing emails that look like routine business messages, often referencing purchase orders or invoices and sometimes impersonating real companies. The email doesn’t attach a document directly. Instead, it links to a file hosted on IPFS (InterPlanetary File System), a decentralized storage network increasingly abused in phishing campaigns because content is harder to take down and can be accessed through normal web gateways.
The linked file is named as a PDF and has the PDF icon, but is actually a virtual hard disk (VHD) file. When the user double‑clicks it, Windows mounts it as a new drive (for example, drive E:) instead of opening a document viewer. Mounting VHDs is perfectly legitimate Windows behavior, which makes this step less likely to ring alarm bells.
Inside the mounted drive is what appears to be the expected document, but it’s actually a Windows Script File (WSF). When the user opens it, Windows executes the code in the file instead of displaying a PDF.
After some checks to avoid analysis and detection, the script injects the payload—AsyncRAT shellcode—into trusted, Microsoft‑signed processes such as RuntimeBroker.exe, OneDrive.exe, taskhostw.exe, or sihost.exe. The malware never writes an actual executable file to disk. It lives and runs entirely in memory inside these legitimate processes, making detection and eventually at a later stage, forensics much harder. It also avoids sudden spikes in activity or memory usage that could draw attention.
For an individual user, falling for this phishing email can result in:
Because detection can be hard, it is crucial that users apply certain checks:
invoice.pdf.vhd the user would only see invoice.pdf. To find out how to do this, see below.To show file extensions in Windows 10 and 11:
Alternatively, search for File Explorer Options to uncheck Hide extensions for known file types.
For older versions of Windows, refer to this article.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
A Chrome extension posing as an Amazon ad blocker was caught hijacking affiliate links in the background, redirecting commissions without user consent.
The post Chrome Add-On Caught Stealing Amazon Commissions appeared first on TechRepublic.
Last week on Malwarebytes Labs:
On the ThreatDown blog:
Stay safe!
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.
A group of cybercriminals called DarkSpectre is believed to be behind three campaigns spread by malicious browser extensions: ShadyPanda, GhostPoster, and Zoom Stealer.
We wrote about the ShadyPanda campaign in December 2025, warning users that extensions which had behaved normally for years suddenly went rogue. After a malicious update, these extensions were able to track browsing behavior and run malicious code inside the browser.
Also in December, researchers uncovered a new campaign, GhostPoster, and identified 17 compromised Firefox extensions. The campaign was found to hide JavaScript code inside the image logo of malicious Firefox extensions with more than 50,000 downloads, allowing attackers to to monitor browser activity and plant a backdoor.
The use of malicious code in images is a technique called steganography. Earlier GhostPoster extensions hid JavaScript loader code inside PNG icons such as logo.png for Firefox extensions like “Free VPN Forever,” using a marker (for example, three equals signs) in the raw bytes to separate image data from payload.
Newer variants moved to embedding payloads in arbitrary images inside the extension bundle, then decoding and decrypting them at runtime. This makes the malicious code much harder for researchers to detect.
Based on that research, other researchers found an additional 17 extensions associated with the same group, beyond the original Firefox set. These were downloaded more than 840,000 times in total, with some remaining active in the wild for up to five years.
GhostPoster first targeted Microsoft Edge users and later expanded to Chrome and Firefox as the attackers built out their infrastructure. The attackers published the extensions in each browser’s web store as seemingly useful tools with names like “Google Translate in Right Click,” “Ads Block Ultimate,” “Translate Selected Text with Google,” “Instagram Downloader,” and “Youtube Download.”
The extensions can see visited sites, search queries, and shopping behavior, allowing attackers to create detailed profiles of users’ habits and interests.
Combined with other malicious code, this visibility could be extended to credential theft, session hijacking, or attacks targeting online banking workflows, even if those are not the primary goal today.
Although we always advise people to install extensions only from official web stores, this case proves once again that not all extensions available there are safe. That said, the risk involved in installing an extension from outside the web store is even greater.
Extensions listed in the web store undergo a review process before being approved. This process, which combines automated and manual checks, assesses the extension’s safety, policy compliance, and overall user experience. The goal is to protect users from scams, malware, and other malicious activity.
Mozilla and Microsoft have removed the identified add-ons from their stores, and Google has confirmed their removal from the Chrome Web Store. However, already installed extensions remain active in Chrome and Edge until users manually uninstall them. When Mozilla blocks an add-on it is also disabled, which prevents it from interacting with Firefox and accessing your browser and your data.
If you’re worried that you may have installed one of these extensions, Windows users can run a Malwarebytes Deep Scan with their browsers closed.
Manual check:
These are the names of the 17 additional extensions that were discovered:
Note: There may be extensions with the same names that are not malicious.
We don’t just report on threats—we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your, and your family’s, personal information by using identity protection.