The Fall of Versus: Dark Web Mastermind Extradited to the US to Face Life Behind Bars
The post The Fall of Versus: Dark Web Mastermind Extradited to the US to Face Life Behind Bars appeared first on Daily CyberSecurity.

A cybercriminal operation known as Jerry’s Store has reportedly exposed a large cache of stolen payment card data after leaving its own infrastructure accessible online. The service appears to have been used to test whether stolen credit and debit card details were still valid, effectively acting as a verification tool for fraudsters before the data was resold or abused.
“Jerry’s Store marketplace leaked 345,000 stolen credit card details through an exposed, insecurely configured server created using AI assistance.” reads the report published by CyberNews.
“The leak occurred after Cursor AI generated flawed code without authentication, exposing credit card numbers, names, addresses, and security codes.”
Researchers found that the exposed server contained information linked to roughly 345,000 payment cards. Of those, nearly 200,000 cards had been marked as invalid by the service, while more than 145,000 records were identified as valid. The leaked records reportedly included highly sensitive cardholder data such as card numbers, expiration dates, security codes, names, and billing addresses. Cybernews
The incident is notable not only because of the volume of exposed data, but also because it shows how organized and automated parts of the carding economy have become. Instead of manually checking stolen cards one by one, criminal marketplaces and fraud services increasingly rely on infrastructure that can validate payment data at scale. Once a card is confirmed as active, it becomes more valuable for resale, fraud attempts, or account takeover activity.
Cybernews estimated that valid stolen card records typically sell for around $7 to $18 on dark web markets. Using that range, the valid card data exposed through Jerry’s Store could be worth between $1 million and $2.6 million. The true value of the broader operation may be higher, since the platform reportedly handled more than just the leaked payment-card records.
CyberNews researchers found that Jerry’s Store operators used Cursor, an AI coding tool by Anysphere, to build their server and admin dashboards. However, flawed guidance from the AI likely led to misconfigurations, leaving the system exposed and causing the data leak.
“We were able to confirm that the leak originated from the user asking to create a statistics dashboard, and Cursor created an unauthenticated open web directory to serve the webpage, ignoring the need to set up authentication or ensure that only the intended dashboard would be accessible,” CyberNews team explained.


The case is ironic: a cybercriminal service built to profit from stolen card data exposed itself due to poor security. This failure creates added risk for victims, as data already circulating in underground markets can spread further, reaching new attackers who did not originally steal it.
The story also highlights a wider trend in cybercrime: illicit services are becoming more productized. Carding shops, validation tools, automated fraud services, and dark web marketplaces increasingly resemble commercial platforms, with pricing models, customer interfaces, and backend infrastructure. Rapid7 has described this broader ecosystem as “carding-as-a-service,” where stolen cards and fraud tooling are packaged for easier use by criminals with varying levels of technical skill.
A similar pattern has been seen in other carding-related incidents. BidenCash, a carding-focused marketplace, became known for releasing large batches of stolen payment-card data as a promotional tactic to attract users and vendors.
Law enforcement has also targeted related ecosystems. In a case involving B1ack’s Stash, authorities seized domains tied to underground vendors trafficking stolen financial data, including payment-card records. That case underlines how carding markets remain a priority for investigators because they support a chain of downstream crimes, from unauthorized purchases to identity theft and money laundering.
Consumers should closely monitor accounts, enable alerts, use virtual cards, and replace compromised ones. Banks must strengthen fraud detection, quickly block stolen cards, and monitor underground markets.
The Jerry’s Store leak shows that even cybercriminal platforms can have weak security. When they fail, the impact still hits ordinary users, whose stolen card data may spread further and be reused, traded, and exploited across the fraud ecosystem.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Jerry’s Store)
The dark web is often misunderstood, but it plays an important role in both privacy technology and cybercrime activity. In this episode, Tom Eston speaks with cybersecurity researcher and educator John Hammond about what the dark web actually is and how it has evolved in recent years. The discussion covers underground marketplaces, ransomware leak sites, […]
The post The Dark Web Explained with John Hammond appeared first on Shared Security Podcast.
The post The Dark Web Explained with John Hammond appeared first on Security Boulevard.

![]()

New research is shedding light on how infostealer malware turns a single careless click into full-blown credential exposure on dark web marketplaces in less than 48 hours far faster than traditional breach detection timelines. Unlike database breaches that take weeks or months to uncover, infostealer infections move at machine speed. A typical scenario begins when […]
The post New Study Reveals How Infostealer Infections Lead to Dark Web Exposure in Just 48 Hours appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.


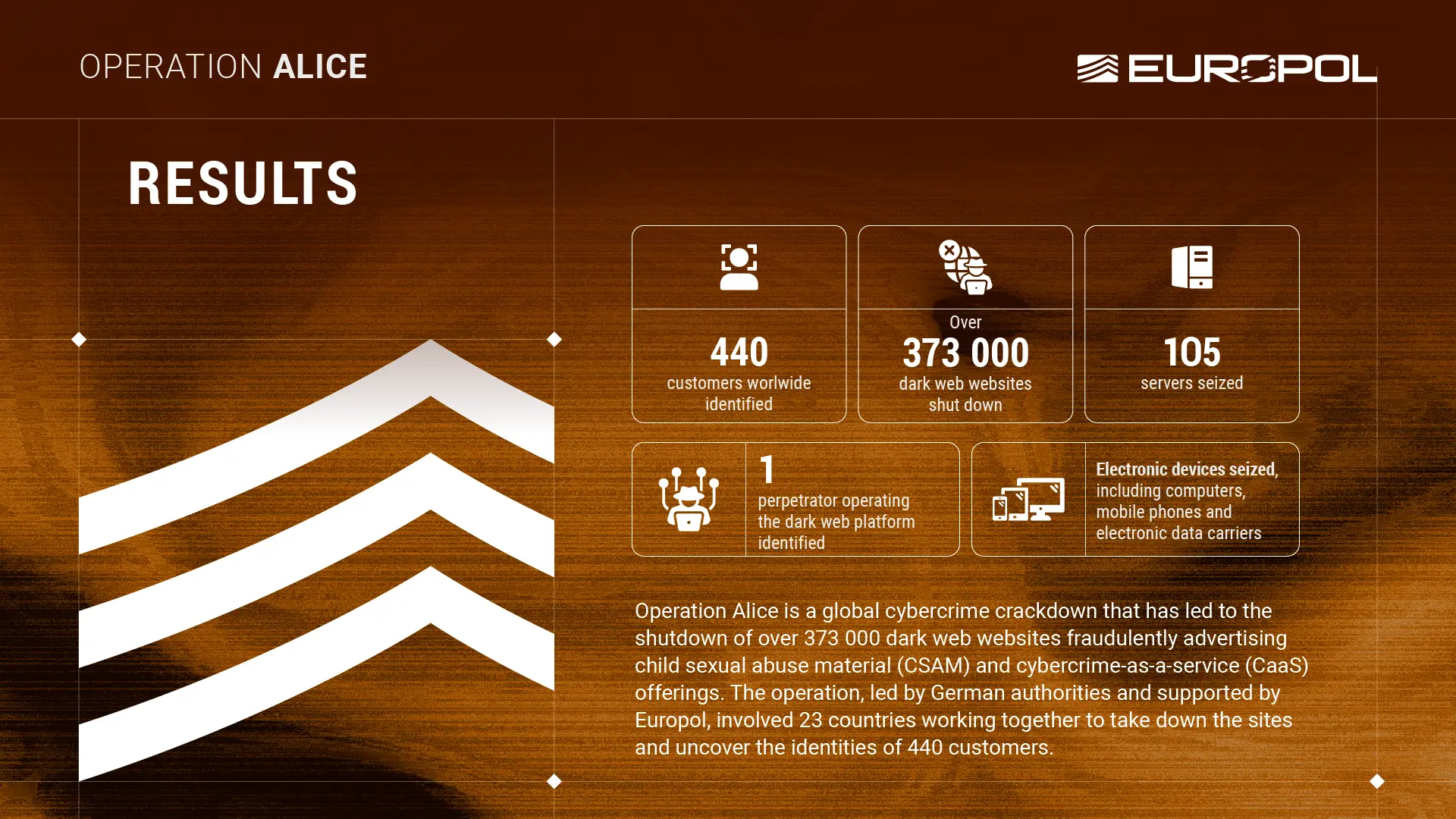
An international law enforcement operation, code named Operation Alice, shut down one of the largest dark web scams, uncovering over 373,000 fake sites tricking users seeking child sexual abuse content. The operation, first investigated in Germany in 2021, centered on the platform “Alice with Violence CP” and was allegedly run by a single individual controlling hundreds of thousands of fraudulent marketplaces for illicit material and cybercrime services.
“On 9 March 2026, a global operation led by German authorities and supported by Europol was launched against one of the largest networks of fraudulent platforms in the dark web. The investigation began in mid-2021 against the dark web platform “Alice with Violence CP”.” reads the press release by Europol. “During the investigation, authorities discovered that the platform’s operator was running more than 373 000 fraudulent websites advertising child sexual abuse material (CSAM) and cybercrime-as-a-service (CaaS) offerings.”
From 9 to 19 March 2026, law enforcement from 23 countries worked together to go after the operator of a dark web platform.
The investigation revealed 440 customers worldwide, prompting further probes against them, with ongoing actions against more than 100 individuals. So far, authorities have identified 1 operator based in the People’s Republic of China, shut down over 373,000 dark web sites, seized 105 servers, and confiscated computers, mobile phones, and other electronic devices, marking a major step against illicit online networks.
“From November 2019 until recently, he operated a network of up to 287 servers at its peak, 105 of which were located in Germany. German authorities have issued an international arrest warrant.” continues the press release.

Over nearly five years, German authorities uncovered a single individual running more than 373,000 dark web sites, including 90,000 offering fraudulent CSAM “packages” for Bitcoin. Prices ranged from €17 to €215 for data from gigabytes to terabytes, but nothing was delivered. The operator also promoted cybercrime services, such as stolen credit card data and system access, tricking users into paying without receiving any actual content or services.
The Europol pointed out that even though customers never received CSAM, paying for it made them suspects, and investigators saw them as potential high-value targets for intelligence. Authorities acted quickly to protect children at risk, such as a 31-year-old father convicted in 2023 for attempting to buy 70 GB of CSAM. Europol coordinated international information sharing, traced cryptocurrency payments, and supported authorities, helping identify the perpetrator. Europol also runs projects to prevent child sexual exploitation, including the “Stop Child Abuse – Trace an Object” initiative and the Help4U platform, offering children secure advice and support.
“Operation Alice sends a clear message: there is nowhere to hide for criminals when the international law enforcement community works hand in glove. We will find them and hold them accountable. Europol will continue to protect children, support victims, and track down the perpetrators.” said Europol’s Executive Director Catherine De Bolle.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – Operation Alice, dark web)
![]()
A 35-year-old man operating from China ran the largest fraudulent dark web network ever dismantled and the most disturbing detail is not the scale of the infrastructure he built, but what he was selling — child sexual abuse material that did not exist, to thousands of buyers who paid for it anyway.
On March 9, a global operation led by German authorities and supported by Europol was launched against one of the largest networks of fraudulent platforms in the dark web. The investigation began in mid-2021 against the dark web platform "Alice with Violence CP." During the investigation, authorities discovered that the platform's operator ran more than 373,000 fraudulent websites advertising child sexual abuse material and cybercrime-as-a-service offerings.
The first phase of Operation Alice ran for 10 days, with 23 countries joining forces. The participating nations included Spain, Germany, the United States, the United Kingdom, Ukraine, Mexico, Canada, and Australia. Europol facilitated intelligence exchange, provided analytical support, coordinated the international response, and played a critical role in tracing cryptocurrency payments across jurisdictions.
The criminal model this operator constructed sits at an unusual intersection of two distinct threats that security teams rarely analyze together. From February 2020 to July 2025, the suspect advertised child sexual abuse material on different platforms accessible through more than 90,000 of those onion domains. The perpetrator offered material in purchasable packages after buyers provided an email address and made a payment in Bitcoin, with each package costing between €17 and €215 and promising data volumes ranging from a few gigabytes to several terabytes.
The material was never delivered. Customers were tricked into providing payment for these products but received nothing in return. Europol estimated the suspect made around €345,000 — approximately $400,000 — from around 10,000 people who attempted to buy the illicit material.
The fraud architecture layered two criminal economies on top of each other. Alongside child abuse material, the platform also offered cybercrime-as-a-service listings — including stolen credit card data and access to compromised backend computer systems — extending the operator's reach from child exploitation into enterprise-grade cybercrime services.
The CaaS dimension means the operator's customer base included not only individuals seeking abuse material but also cybercriminals seeking ready-made access to corporate networks, broadening the downstream harm considerably.
The infrastructure scale alone places this case in a different category from any previous dark web takedown. The dark web runs on onion domains — a special type of website address engineered specifically to conceal the identity and location of both the operator and visitors by routing traffic through layered encryption relays.
Over nearly five years of investigation, German authorities discovered that a single individual operated over 373,000 onion domains on the dark web. Managing that volume of infrastructure requires automation, deliberate operational security planning, and sustained technical capability.
Operation Alice initially only targeted the platform operator. However, through international cooperation, the investigation uncovered the identities of 440 customers who had used the operator's services. Due to the nature of the purchases, additional investigations were launched against them, and the operation remains ongoing against more than 100 of those individuals.
The operational results include the seizure of 105 servers along with computers, mobile phones, and electronic storage devices. Investigators also seized the financial proceeds generated across five years of operation.
Tax season is also peak season for identity theft. Malwarebytes researchers spotted criminals trading stolen tax records on dark web forums.
The post Your tax forms sell for $20 on the dark web appeared first on Security Boulevard.
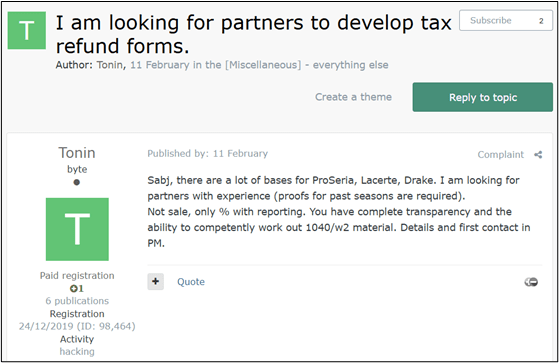
Tax season is also peak season for identity theft. Criminals use stolen personal data to file fake tax returns and claim refunds before the real taxpayer does. Here’s how the fraud works, and how to protect yourself.
Stolen Identity Refund Fraud (SIRF) is a type of tax fraud where criminals steal someone’s personal information—such as a Social Security number and date of birth—and use it to file a fake tax return in that person’s name in order to claim a tax refund.
The fraudsters usually submit the false return early in the tax season before the real taxpayer files, so the refund is issued to them instead of the legitimate person.
The money is often sent to bank accounts, debit cards, or addresses controlled by the criminals. Victims usually discover the fraud only when their real tax return is rejected or when the tax authority, like the US Internal Revenue Service (IRS), reports that a refund has already been issued in their name.
As Americans scramble to meet the annual tax filing deadline, a hidden ecosystem on the Dark Web kicks into overdrive, transforming tax season into a lucrative period of the year for international cybercriminals. Shahak Shalev, Global Head of Scam and AI Research at Malwarebytes, said:
“People are expecting messages about taxes, refunds, and filings, which makes phishing emails and fake IRS alerts much easier to believe. At the same time, the personal data needed to commit tax fraud is shockingly cheap on the dark web. It’s no surprise scammers treat tax season like an annual opportunity.”
Behind the sudden influx of fraudulent refund claims lies a highly organized criminal supply chain deeply rooted in Russian-language underground forums. These specialized platforms act as the primary enablers of tax fraud.
Rather than harvesting data from scratch, fraudsters can simply purchase massive datasets of stolen Personally Identifiable Information (PII), complete with ready-to-use W-2 and 1040 forms. For more sophisticated operations, Initial Access Brokers (IABs) auction off direct network access to compromised Certified Public Accountants (CPAs) and accounting firms.
Beyond raw data and access, this underground economy provides a full suite of “fraud-as-a-service” tools—including on-demand services to forge supporting financial documents and dedicated instructional hubs featuring step-by-step tutorials.
At the epicenter of this illicit commerce is one of the premier Russian-language underground forums, which serves as the definitive marketplace for fraudsters to buy and offload tax-related PII. The commoditization of this data is staggering in its efficiency, operating much like a traditional e-commerce platform.
Our research team has captured several compelling samples of this trading activity, highlighting a clear pricing tier based on the freshness of the data and the target demographic. In one recently observed listing, a threat actor advertised a bulk package of 100 complete tax forms for $2,000—effectively pricing a fully documented stolen identity at just $20.
Conversely, older data dumps from the 2024 tax year are heavily discounted to clear inventory; highly sensitive records specifically belonging to wealthy retirees and pensioners from that period are currently being traded for less than $4 per identity.
This staggering volume of tax-related data must originate from somewhere, and threat actors have identified the ultimate jackpot: US companies that handle tax preparation and accounting procedures.
From an attacker’s perspective, it is infinitely more efficient to breach a dedicated business that serves as a centralized vault for this sensitive information than to cast a wide net trying to trick individual citizens into handing over their personal details.
Our research team recently intercepted a prime example of this strategy in action, identifying a Dark Web listing for compromised network access to a US-based tax service firm. The victimized organization is a small business; a typical target of criminals looking for easy access for exploitable information.
Exploiting these systemic weaknesses, the threat actor was able to quietly infiltrate the company’s internal infrastructure and is now auctioning off direct access to a database containing the complete, highly sensitive PII of over 1,600 clients.

Even when threat actors encounter roadblocks during the fraud process—such as a missing piece of PII or a highly specific financial document required for verification—the cybercrime underground offers a comprehensive suite of on-demand services to seamlessly solve these issues.
Our research team has tracked a dedicated black market known as “Cypher – Fullz and Docs,” which specializes in selling complete, ready-to-use sets of stolen US identities (commonly referred to in the underground as “fullz”) for as little as $0.75 per set.
However, having the basic data is sometimes not enough to bypass required checks.
When additional paperwork is required to legitimize a fraudulent claim, threat actors simply turn to specialized forgery services like “Fakelab.” For a nominal fee ranging between $20 and $40, Fakelab operates as an illicit digital design studio, meticulously forging any tax-related document an attacker might need, from customized W-2s to realistic bank statement, ensuring the scam can proceed without a hitch.
The culmination of the tax fraud lifecycle—and often the most precarious phase for the attacker—is the cashout. To successfully finalize the scam and extract the stolen funds, fraudsters require a robust financial infrastructure, typically relying on compromised “drop” bank accounts and supplementary financial tools designed to launder the money and obscure their tracks.
Unsurprisingly, the Dark Web ecosystem provides not just the tools but the detailed education necessary to execute this critical phase. Our research team identified a dedicated underground resource known as “Flava,” which serves as a centralized instructional hub. This platform is brimming with comprehensive, step-by-step tutorials specifically detailing how to orchestrate these complex cashout schemes targeting US citizens and residents.

Stolen Identity Refund Fraud is a reminder that identity theft doesn’t just lead fraudulent purchases. It can impact something as fundamental as filing your taxes.
Cybercriminals take advantage of underground marketplaces that sell stolen personal data, compromised business access, and tools designed to support fraud. It makes it easier for criminals to file fake tax returns quickly and at scale.
For taxpayers, the best defense is limiting the amount of personal data available to criminals, filing your taxes early, and paying attention to any warning signs that someone may be trying to use your identity.
Tax fraud often depends on criminals getting access to your personal information first. The less data they have, the harder it is for them to impersonate you. Here are some steps that can help reduce your risk:
Note: These dark web screenshots have been roughly translated from Russian.
What do cybercriminals know about you?
Use Malwarebytes’ free Digital Footprint scan to see whether your personal information has been exposed online.
Eurail B.V. confirmed that the traveler data stolen in a breach earlier this year is now being offered for sale on the dark web. The company disclosed the development as part of its ongoing response to the cybersecurity incident.
“Eurail B.V. has confirmed that certain customer data affected by the previously reported security incident has been offered for sale on the dark web and a sample data set has been published on Telegram.” reads the statement published by the company. “We are continuing to investigate the scope and impact.”
Eurail B.V. is a Netherlands-based company that manages and sells the Eurail Pass, allowing international travelers to explore Europe by train with a single ticket. Working with dozens of railway and ferry partners, it provides access to more than 250,000 kilometers of rail routes across over 30 European countries, simplifying cross-border rail travel.
Eurail B.V. confirmed a security breach that led to unauthorized access to customer data, including participants in the European Commission’s DiscoverEU program. The company said it quickly secured its systems and launched an investigation with the help of external cybersecurity and legal experts.
Early findings indicate the breach may involve order and reservation details, basic identity and contact data, travel companion information, and in some cases passport numbers and expiry dates.
“The personal data affected may include data that you have provided (where applicable):
The company pointed out it does not store payment card data or passport copies. The company notified authorities in compliance with the GDPR regulation.
Eurail B.V. said customers whose data may have been accessed or published will be informed directly when contact details are available. They urge vigilance against suspicious calls, emails, or messages requesting personal information and stress that Eurail will never request sensitive data unsolicited. Customers should update their Rail Planner app password, review related email, social media, or banking passwords, monitor accounts for unusual activity, and report any concerns to their bank.
Further guidance is available via Eurail’s customer support center.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Eurail)

Técnicas de OSINT na Dark Web para cibersegurança:
OSINT na Dark Web (ou DARKINT) refere-se à coleta de inteligência a partir de fontes públicas (mas ocultas) em redes anonimizadas como Tor (.onion), I2P e similares. Em cibersegurança, é essencial para:
Aviso Legal e Ético Importante (2026): Acessar a dark web é legal na maioria dos países (incluindo Brasil), mas interagir com conteúdo ilegal, comprar algo ou participar de fóruns pode cruzar linhas rapidamente. Mantenha-se passivo: apenas observação e busca. Nunca faça login com credenciais reais, baixe arquivos desconhecidos ou ative JavaScript sem ambiente isolado/hardened. Respeite leis como Marco Civil da Internet e LGPD.
Muitos profissionais evitam navegação direta no Tor para trabalho rotineiro — é lento e arriscado. Prefira serviços indexados que crawlam .onion legalmente e entregam resultados via clearnet (mais seguro e rápido).
Ferramentas Gratuitas / Acessíveis
Plataformas Profissionais / Comerciais (Recomendadas para Cyber)
Tabela Rápida de Comparação (Foco em Cibersegurança)
| Técnica / Objetivo | Melhores Ferramentas Gratuitas | Melhores Ferramentas Profissionais | Nível de Risco | Por que é útil em Cyber |
|---|---|---|---|---|
| Busca de Credenciais / Vazamentos | HaveIBeenPwned + Intelligence X | Recorded Future, SpyCloud | Baixo | Detecção precoce de breach |
| Chatter em Fóruns / Atores de Ameaça | Ahmia + Tor manual | Babel X, DarkOwl | Médio | TTPs e inteligência de campanhas |
| Monitoramento de Marketplaces / Dumps | Haystak / Torch | SOCRadar, Cyble | Médio | Alertas de venda de dados roubados |
| Varredura Automatizada / IOCs | Script OnionSearch | API Intelligence X / DarkSearch | Baixo-Médio | Checagem em batch de hashes/domínios |
| Conteúdo Histórico / Arquivado | Intelligence X | Arquivos Recorded Future | Baixo | Posts deletados e leaks antigos |
Fluxo Inicial Rápido (Baixo Risco)


Rui-Siang Lin (24) was sentenced to 30 years in prison for running Incognito Market, a major darknet drug marketplace that sold over one ton of narcotics. The Taiwanese man pled guilty in December 2024.
“United States Attorney for the Southern District of New York, Jay Clayton, announced that RUI-SIANG LIN was sentenced to 30 years in prison for conspiring to distribute narcotics, money laundering, and conspiring to sell adulterated and misbranded medication, in connection with LIN’s ownership and operation of the Incognito Market, an online narcotics marketplace that sold more than one ton of narcotics before its closure in March 2024.” reads the press release published by DoJ.
Incognito Market ran on the dark web from 2020 to 2024 and sold over $105 million in drugs worldwide. Operated by Rui-Siang Lin under the alias “Pharaoh,” the site trafficked massive amounts of cocaine, meth, and other narcotics, including fentanyl-laced pills. Lin controlled every part of the operation, from vendors to customers.
The marketplace worked like a polished online shop for drugs. Users logged in, browsed thousands of listings, and paid with crypto. Vendors paid a 5% fee on each sale, the platform supported a built-in crypto “bank” to handle payments and kept buyers and sellers anonymous.
LIN co-founded Incognito Market in October 2020, took control by early 2022, and shut it down in March 2024 while operating from places including St. Lucia. Despite running a major dark web drug market, he even led a local police training on cybercrime and crypto. Under his leadership, Incognito grew to over 400,000 buyers, 1,800 vendors, and more than 640,000 drug transactions. He allowed opiate sales, including fake “oxycodone” that was actually fentanyl, linked to at least one fatal overdose. When closing the site, LIN stole over $1 million in user funds and tried to extort users by threatening to expose their data.
“In imposing the sentence, Judge McMahon stated to the defendant that Incognito Market was “a business that made [him] a drug kingpin,” and that this was the “most serious drug crime I have ever been confronted with in 27.5 years.”” continues the press release.
Along with the prison sentence, LIN received five years of supervised release and was ordered to forfeit about $105 million.
“Rui-Siang Lin was one of the world’s most prolific drug traffickers, using the internet to sell more than $105 million of illegal drugs throughout this country and across the globe,” said U.S. Attorney Jay Clayton. “While Lin made millions, his offenses had devastating consequences. He is responsible for at least one tragic death, and he exacerbated the opioid crisis and caused misery for more than 470,000 narcotics users and their families. Today’s sentence puts traffickers on notice: you cannot hide in the shadows of the Internet. And our larger message is simple: the internet, ‘decentralization,’ ‘blockchain’—any technology—is not a license to operate a narcotics distribution business.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, dark web)
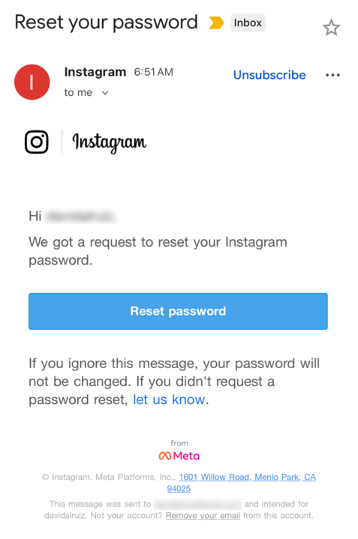
Last week, many Instagram users began receiving unsolicited emails from the platform that warned about a password reset request.

The message said:
“Hi {username},
We got a request to reset your Instagram password.
If you ignore this message, your password will not be changed. If you didn’t request a password reset, let us know.”
Around the same time that users began receiving these emails, a cybercriminal using the handle “Solonik” offered data that alleged contains information about 17 million Instagram users for sale on a Dark Web forum.

These 17 million or so records include:
Please note that there are no passwords listed in the data.
Despite the timing of the two events, Instagram denied this weekend that these events are related. On the platform X, the company stated they fixed an issue that allowed an external party to request password reset emails for “some people.”

So, what’s happening?
Regarding the data found on the dark web last week, Shahak Shalev, global head of scam and AI research at Malwarebytes, shared that “there are some indications that the Instagram data dump includes data from other, older, alleged Instagram breaches, and is a sort of compilation.” As Shalev’s team investigates the data, he also said that the earliest password reset requests reported by users came days before the data was first posted on the dark web, which might mean that “the data may have been circulating in more private groups before being made public.”
However, another possibility, Shalev said, is that “another vulnerability/data leak was happening as some bad actor tried spraying for [Instagram] accounts. Instagram’s announcement seems to reference that spraying. Besides the suspicious timing, there’s no clear connection between the two at this time.”
But, importantly, scammers will not care whether these incidents are related or not. They will try to take advantage of the situation by sending out fake emails.
“We felt it was important to alert people about the data availability so that everyone could reset their passwords, directly from the app, and be on alert for other phishing communications,” Shalev said.
If and when we find out more, we’ll keep you posted, so stay tuned.
If you have enabled 2FA on your Instagram account, we think it is indeed safe to ignore the emails, as proposed by Meta.
Should you want to err on the safe side and decide to change your password, make sure to do so in the app and not click any links in the email, to avoid the risk that you have received a fake email. Or you might end up providing scammers with your password.
Another thing to keep in mind is that these are Meta-data. Which means some users may have reused or linked them to their Facebook or WhatsApp accounts. So, as a precaution, you can check recent logins and active sessions on Instagram, WhatsApp, and Facebook, and log out from any devices or locations you do not recognize.
If you want to find out whether your data was included in an Instagram data breach, or any other for that matter, try our free Digital Footprint scan.

Google began offering "dark web reports" a while back, but the company has just announced the feature will be going away very soon. In an email to users of the service, Google says it will stop telling you about dark web data leaks in February. This probably won't negatively impact your security or privacy because, as Google points out in its latest email, there's really nothing you can do about the dark web.
The dark web reports launched in March 2023 as a perk for Google One subscribers. The reports were expanded to general access in 2024. Now, barely a year later, Google has decided it doesn't see the value in this type of alert for users. Dark web reports provide a list of partially redacted user data retrieved from shadowy forums and sites where such information is bought and sold. However, that's all it is—a list.
The dark web consists of so-called hidden services hosted inside the Tor network. You need a special browser or connection tools in order to access Tor hidden services, and its largely anonymous nature has made it a favorite hangout for online criminals. If a company with your personal data has been hacked, that data probably lives somewhere on the dark web.


© Getty Images | 400tmax

Vazamento global: Brasil lidera com mais de 7 bilhões de cookies roubados
Pesquisa da NordVPN revela que o Brasil ocupa o 1º lugar entre 235 países no vazamento de cookies, com mais de 7 bilhões de registros, dos quais 550 milhões ainda estão ativos
O Brasil desponta como o país com o maior volume de cookies vazados no mundo, conforme aponta nova pesquisa realizada pela NordVPN. De acordo com os dados, entre os quase 94 bilhões de cookies vazados encontrados na dark web, mais de 7 bilhões são originários de usuários brasileiros. O levantamento também revela que aproximadamente 550 milhões desses cookies ainda estão ativos e vinculados a atividades reais de usuários.
![]()
Apesar dos cookies serem vistos como úteis para melhorar experiências online, muitos não percebem que hackers podem explorá-los para roubar dados pessoais e acessar sistemas seguros. No contexto brasileiro, o volume de vazamentos é significativamente maior em relação aos demais países, com Índia, Indonésia, Estados Unidos e Vietnã, completando a lista dos cinco primeiros colocados.
Apesar de parecer inofensivos, os cookies vazados não contêm apenas informações triviais. Entre os dados expostos estão nomes completos, endereços de e-mail, senhas, cidades e até mesmo endereços físicos dos usuários. Portanto, esses dados podem ser utilizados por criminosos para cometer fraudes, roubo de identidade e invasões de contas online, colocando em risco a segurança digital de milhões de pessoas.
O especialista em cibersegurança da NordVPN, Adrianus Warmenhoven, alerta sobre os perigos dessa exposição. “Cookies podem parecer inofensivos, mas, nas mãos erradas, eles se tornam verdadeiras chaves digitais para nossas informações mais privadas.”, explica.
![]()
Número de cookies vazados em alta
A pesquisa revela que o número de cookies vazados subiu drasticamente nos últimos anos. Em 2024, eram 54 bilhões, enquanto em 2025 o número já ultrapassa os 94 bilhões — um aumento de 74%. Grande parte dos cookies vazados está relacionada a grandes plataformas, como Google (4,5 bilhões), YouTube (1,33 bilhões), Microsoft (1,1 bilhões) e Bing (1 bilhão).
O estudo também identificou que 38 tipos de malwares foram usados para roubar os cookies. O Redline lidera a lista, responsável por mais de 41,6 bilhões de vazamentos. Outros malwares, como Vidar (10 bilhões) e LummaC2 (9 bilhões), também contribuíram para a coleta de dados sensíveis.
![]()
O que são cookies e por que são importantes?
Os cookies são pequenos arquivos de texto que os sites armazenam no navegador do usuário para lembrar preferências, detalhes de login e comportamento de navegação. Esses arquivos desempenham um papel essencial na personalização da experiência online, permitindo que as páginas carreguem mais rapidamente e mantenham as configurações personalizadas do usuário.
Os cookies facilitam a navegação ao manter o usuário conectado, salvar itens no carrinho de compras e oferecer recomendações personalizadas com base no histórico de navegação. Sem eles, as interações online seriam menos práticas e personalizadas.
Tipos de cookies mais comuns:
Embora sejam úteis, os cookies podem representar riscos se caírem nas mãos erradas. Hackers podem roubar esses arquivos para acessar contas pessoais sem precisar de login, já que muitos cookies contêm tokens de sessão que mantêm a conexão ativa.
Formas simples de proteger seus dados
Diante dos dados alarmantes, a NordVPN recomenda que os usuários devem adotar formas simples de proteção que podem ajudar a prevenir roubo de dados. “As pessoas costumam fechar o navegador, mas a sessão ainda está ativa. Limpar os dados do site ajuda a minimizar os riscos”, diz Warmenhoven.
Metodologia
Os dados da pesquisa realizada entre 23 e 30 de abril foram compilados em parceria com pesquisadores independentes especializados em pesquisa de incidentes de segurança cibernética.
Os pesquisadores utilizaram dados coletados de canais do Telegram onde hackers anunciam quais informações roubadas estão disponíveis para venda. Isso levou a um conjunto de dados com informações sobre mais de 93,76 bilhões de cookies.
Os pesquisadores analisaram se os cookies estavam ativos ou inativos, qual malware foi usado para roubá-los, de qual país eles eram, bem como quais dados continham sobre a empresa que os criou, o sistema operacional do usuário e as categorias de palavras-chave atribuídas aos usuários.
A NordVPN não comprou cookies roubados nem acessou o conteúdo dos cookies, examinando apenas os tipos de dados contidos neles.
Sobre a NordVPN
A NordVPN é o provedor de serviços VPN mais avançado do planeta, usado por milhões de usuários de internet no mundo todo. A NordVPN fornece dupla criptografia VPN e Onion Over VPN, garantindo privacidade com rastreamento zero. Um dos principais recursos do produto é a Proteção Contra Ameaças, que bloqueia sites maliciosos, malware, rastreadores e anúncios maliciosos. É muito fácil de usar, oferece um dos melhores preços do mercado e possui mais de 6,2 mil servidores em 111 países. Para mais informações, acesse: nordvpn.com.

Os números não deixam dúvidas: o setor da saúde segue como um dos alvos preferenciais dos cibercriminosos no mundo. Segundo o Data Breach Investigations Report (DBIR) 2025, divulgado pela Verizon no dia 23 de abril, foram mais de 1.700 incidentes de segurança registrados na área médica entre novembro de 2023 e outubro de 2024. Destes, um assustador volume de 1.542 resultou em vazamentos de dados, muitos expostos por cibercriminosos em sites e fóruns na Dark e Deep Web.
O levantamento é considerado uma das maiores referências globais sobre segurança digital. Neste ano, analisou mais de 22 mil incidentes, com 12.195 violações de dados confirmadas em organizações de 139 países.
A saúde ficou atrás apenas do setor industrial, que acumulou 1.607 violações no mesmo período. “Os dados médicos são altamente sensíveis e valiosos. Por isso, o setor virou uma espécie de mina de ouro para os cibercriminosos”, explica Anchises Moraes, especialista da Apura Cyber Intelligence, que pelo sétimo ano consecutivo é uma das colaboradoras do relatório, levando dados do cenário brasileiro para esse levantamento global.
Segundo o relatório, 45% das violações miraram dados médicos, enquanto 40% afetaram dados pessoais, como nomes, endereços e números de documentos.
Os principais caminhos para as violações continuam sendo os mesmos: intrusões, falhas humanas e erros diversos, responsáveis por 74% dos casos. Já sobre quem promove os ataques, a maioria vem de fora: 67% são atribuídos a agentes externos. Mas o risco interno também é alto: 30% dos incidentes foram causados por pessoas com acesso legítimo aos sistemas. Os parceiros, por sua vez, responderam por 4% das investidas.
A maioria das invasões teve motivações financeiras: 90% dos ataques buscaram lucro direto com extorsão ou venda de dados. Contudo, um dado chama a atenção: os ataques movidos por espionagem saltaram de 1% em 2023 para 16% em 2024, um crescimento que, segundo Moraes, é “expressivo e preocupante”.
“Esse é um dos grandes desafios: muitas vezes, quem está dentro da organização facilita ou executa o ataque”, alerta Moraes. Para ele, a resposta precisa ir além de barreiras tecnológicas. “É preciso investir em treinamento, conscientização e controles rigorosos.”
Outra mudança detectada pelo DBIR 2025: os ataques de ransomware e invasões sofisticadas superaram, pela primeira vez, os erros humanos como causa dos incidentes, que lideravam o ranking até 2023. A escalada preocupa, especialmente em hospitais, onde a indisponibilidade de sistemas por um ataque de ransomware pode comprometer o atendimento e colocar vidas em risco. A América Latina também figura no relatório com destaque: foram 657 incidentes na região, sendo 413 com vazamentos confirmados.
“Depois que um ataque acontece, o desespero toma conta, e isso dá ainda mais vantagem aos criminosos”, afirma Moraes. “Não basta ter rotinas de segurança, sistemas de proteção robustos e, principalmente, investir em educação protetiva cibernética para reduzir o risco de um ataque bem-sucedido”, destaca. “É fundamental investir em medidas preventivas e pró-ativas, como monitoramento de ameaças, e construir um sólido plano de resposta a incidentes, para minimizar o impacto e retomar rapidamente a operação caso o pior aconteça”.
![]()
O relatório completo pode ser acessado gratuitamente no site da Verizon: https://www.verizon.com/