Visualização normal
-
HACKMAGEDDON
-
16-30 April 2026 Cyber Attacks Timeline
In the second timeline of April 2026 I collected 108 events, corresponding to an average of 7.2 events per day, a number that confirms a growing trend, driven by the increasing number of supply chain attacks, compared to the previous timeline, where I collected 94 events (6.27 events/day).
-
HACKMAGEDDON
-
Q1 2026 Cyber Attack Statistics
I aggregated the statistics created from the cyber attacks timelines published in the first quarter of 2026. In this period, I collected a total of 528 events (5.87 events/day) dominated by Cyber Crime with 66%, followed by Cyber Espionage with 18%, Hacktivism with 3%, and finally Cyber Warfare with 2%.
Q1 2026 Cyber Attack Statistics
-
HACKMAGEDDON
-
1-15 April 2026 Cyber Attacks Timeline
The first timeline of April 2026 brings an evolution in terms of methodology: from now on I will map the initial access techniques with the MITRE ATT&CK model. I also decided to merge the categories of Finance and Fintech in the sectors chart. From an event perspective, the first half of April 2026 confirmed a sustained trend...
1-15 April 2026 Cyber Attacks Timeline
-
Security Affairs
-
Bluesky hit by 24-hour DDoS attack as pro-Iran group claims responsibility
Bluesky suffered a 24-hour DDoS attack that caused outages. A pro-Iran hacker group claimed responsibility for the disruption. Bluesky experienced a sophisticated DDoS attack that disrupted its services for about 24 hours, starting on April 15. Bluesky is a decentralized, open-source microblogging social media platform similar to X (formerly Twitter). It allows users to post short messages, images, and videos (up to 300 characters) while providing more control over algorithms, data, and m
Bluesky hit by 24-hour DDoS attack as pro-Iran group claims responsibility
Bluesky suffered a 24-hour DDoS attack that caused outages. A pro-Iran hacker group claimed responsibility for the disruption.
Bluesky experienced a sophisticated DDoS attack that disrupted its services for about 24 hours, starting on April 15.
Bluesky is a decentralized, open-source microblogging social media platform similar to X (formerly Twitter). It allows users to post short messages, images, and videos (up to 300 characters) while providing more control over algorithms, data, and moderation.
The attack disrupted feeds, notifications, threads, and search, causing intermittent outages. A pro-Iran hacker group, called 313 Team (aka “Islamic Cyber Resistance in Iraq”), claimed responsibility, highlighting growing threats against social media platforms and the impact of coordinated disruption campaigns.
“Our team received a report of intermittent app outages at about 11:40pm PDT on April 15, 2026. They worked through the night to mitigate a sophisticated Distributed Denial-of-Service (DDoS) attack, which intensified throughout the day.” Bluesky announced. “We have not seen any evidence of unauthorized access to private user data.”
The company found no signs of data breaches and confirmed it limited the impact of the attack and avoided prolonged outages.
313 Team is a pro-Iran hacktivist group tied to politically driven cyber activity like DDoS attacks, defacements, phishing, and data-leak claims. It targets public services, government and symbolic platforms to create disruption and amplify geopolitical tensions. Analysts link it to the broader Iran-aligned ecosystem, sometimes close to state interests. However, the group often exaggerates its impact, so claims should be treated with caution.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Islamic Cyber Resistance in Iraq)
-
HACKMAGEDDON
-
March 2026 Cyber Attacks Statistics
After the cyber attacks timelines, it’s time to publish the statistics for March 2026 where I collected and analyzed 282 events: a sharp increase compared to the 176 events of the previous month. In March 2026, Cyber Crime continued to lead the Motivations chart with 64%, ahead of Cyber Espionage at number two with 15%. Hacktivism took over the third position with 6%, ahead of Cyber Warfare with 3%.
March 2026 Cyber Attacks Statistics
-
HACKMAGEDDON
-
16-31 March 2026 Cyber Attacks Timeline
The second half of March 2026 has been very active from an infosec standpoint, with 124 events and a threat landscape dominated by malware. As always, cyber crime led the motivations chart with 65%, slightly up from the previous timeline.
16-31 March 2026 Cyber Attacks Timeline
-
Security Affairs

-
Iran-linked group Handala claims to have breached three major UAE organizations
Iran-linked group Handala claims to have breached three major UAE organizations, Dubai Courts, Dubai Land Department, and Dubai Roads & Transport Authority The group Handala claimed a major cyberattack against the UAE, targeting Dubai Courts Department, Dubai Land Department, and Dubai Roads and Transport Authority. They alleged destroying 6 petabytes of data and stealing 149 TB of sensitive information, framing the attack as retaliation and a warning to regional governments, tho
Iran-linked group Handala claims to have breached three major UAE organizations
Iran-linked group Handala claims to have breached three major UAE organizations, Dubai Courts, Dubai Land Department, and Dubai Roads & Transport Authority
The group Handala claimed a major cyberattack against the UAE, targeting Dubai Courts Department, Dubai Land Department, and Dubai Roads and Transport Authority.

They alleged destroying 6 petabytes of data and stealing 149 TB of sensitive information, framing the attack as retaliation and a warning to regional governments, though such claims remain unverified.
“In response to the blatant betrayal of the Resistance Axis by the Epsteinist leaders of the UAE, and as a serious, preemptive warning to all treacherous governments in the region, Handala has launched one of its most powerful cyberattacks against the country’s critical infrastructure.” the group wrote on its Tor website. “During this operation, 6 petabytes of data have been completely destroyed…”

In early April, the group announced that it breached PSK Wind Technologies, an Israeli engineering and IT firm specializing in integrated systems for defense and critical communications, including command and control solutions.
Since the U.S.-Israeli war with Iran began in February, the Iran-linked group Handala has intensified its cyberattacks. It claimed responsibility for a destructive breach at medical tech firm Stryker that targeted its internal Microsoft environment and remotely wiped tens of thousands of employee devices without using malware.
The group claimed it wiped more than 200,000 servers, mobile devices, and other systems, forcing the company to shut down offices across 79 countries. The hacktivists also claimed they exfiltrated about 50TB of corporate data from the company’s infrastructure.
Recently, the Iran-linked hacking group Handala claimed the hack of the FBI Director Kash Patel’s personal Gmail account and shared alleged data, including photos and files.
The FBI is offering up to $10 million for information on the Handala hackers.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Handala)
-
Security Affairs

-
Hackers claim control over Venice San Marco anti-flood pumps
Hackers breached Venice ’s San Marco flood system, claiming control of pumps and the ability to disable defenses and flood coastal areas. The technologies that govern the physical world are the quiet infrastructure of modern life. From energy grids to water systems, from factories to flood defenses, operational technology (OT) has long had one essential mission: to keep everything running. But today, that is no longer enough. The question the market is asking has fundamentally changed: c
Hackers claim control over Venice San Marco anti-flood pumps
Hackers breached Venice ’s San Marco flood system, claiming control of pumps and the ability to disable defenses and flood coastal areas.
The technologies that govern the physical world are the quiet infrastructure of modern life. From energy grids to water systems, from factories to flood defenses, operational technology (OT) has long had one essential mission: to keep everything running.
But today, that is no longer enough. The question the market is asking has fundamentally changed: can these systems withstand a cyberattack? If the answer is no, then what we are building is not infrastructure, it is vulnerability at scale.
This shift is not theoretical. It is happening now, and recent events in Venice have made it painfully real.
A cyberattack recently targeted the hydraulic pump system that protects Piazza San Marco (Venice) from flooding, an iconic location visited by millions each year. The threat actor, operating under names such as “Infrastructure Destruction Squad” or “Dark Engine,” claimed to have gained administrative access to the system. In their own words, they suggested they could “disable defenses and flood coastal areas,” turning a digital intrusion into a potential physical disaster.
The group announced the security breach on its Telegram channel with the following post written in Chinese language:
“We, the Infrastructure Destruction Squad, hereby formally announce the truth about the San Marco incident:
Yes, you conducted new checks after the attack in late March. Yes, equipment tests came back positive after Easter. But what you haven’t understood is that we refused to completely shut down the flood defense system.
We are not here to destroy you. We are simply here to deliver a message: We can do it, and we are still inside your network.
No tests conducted by your security teams can drive us away. No system updates can expel us. We have been here for months and will remain here for months to come.
Any newspaper that disseminates this news without understanding the truth, prepare for a devastating attack. We will prove to you that you are vulnerable.”
The breach reportedly began in late March, with attackers accessing the control interface of the system. By early April, they started releasing evidence, screenshots of control panels, system layouts, and valve states. Hackers claimed they breached Italy’s flood risk reduction system, gaining full control to potentially disable defenses and flood areas. They said the goal was to expose critical infrastructure weaknesses and even enable political pressure. The group also offered to sell full root access to the system for just $600, highlighting both the severity of the breach and the low barrier to potential misuse.
“We announce the hacking of the system: SISTEMA DI RIDUZIONE RISCHIO ALLAGAMENTO (Flood Risk Reduction System) belonging to the Italian Ministry of Infrastructure and Transport. We have taken full control of the system. Political objective: To expose the vulnerability of Italy’s critical infrastructure. Control of this system enables the disabling of floodgates, flooding of coastal areas, and political blackmail of the Italian government. Offer for sale: We are granting full root access to the control system. The price is 600 USD for any party wishing to purchase access.”
While authorities confirmed that critical systems protecting the Basilica di San Marco remained unaffected, the incident exposed a deeply concerning reality: even highly symbolic and strategically important infrastructure can be probed, accessed, and potentially manipulated.
Such kind of incidents are really concerning because, unlike traditional IT systems, OT directly interacts with the physical processes. When compromised, the consequences are not just data loss, but service disruption, economic damage, and even threats to public safety.
This is not an isolated case. Across the globe, critical infrastructure is becoming increasingly exposed. The convergence of IT and OT, remote access for maintenance, and the widespread use of legacy technologies have created a perfect storm of risk. Many industrial systems were never designed with security in mind. They were built for longevity and reliability, not resilience against adversaries. And adversaries are evolving fast.
On April 7, 2026, U.S. agencies, including FBI, CISA, and NSA, warned of Iran-linked APTs exploiting internet-exposed OT systems.
Threat actors are carrying out cyberattacks targeting internet-connected operational technology (OT) across multiple critical infrastructure sectors. Iran-linked actors are believed to be behind the activity, aiming to cause disruption in areas such as government services, water systems, and energy.
The attacks involve manipulating project files and altering data shown on HMI and SCADA systems, leading in some cases to operational disruptions and financial losses. Authorities urged organizations to review indicators of compromise and apply mitigations to reduce risks. The campaign has been linked to groups like CyberAv3ngers, associated with Iran’s IRGC.
These actors are not necessarily exploiting unknown vulnerabilities, they are often leveraging legitimate tools and exposed interfaces to gain access and manipulate operations.
In other words, the attack surface is not just technical, it is architectural.
The Venice incident also highlights a broader strategic shift. This was not a typical ransomware attack aimed at financial gain. The symbolic “price” reportedly associated with access, just a few hundred dollars suggests a different motivation. The goal appears to be demonstration and disruption, a way to show that critical infrastructure can be reached, influenced, and potentially weaponized.
For organizations operating in industrial sectors, the implications are profound. Security can no longer be an afterthought, something added later as a patch or a compliance checkbox. It must be embedded from the start, secure-by-design.
That means:
- Controlled and monitored access
- Strong authentication mechanisms
- Segmentation between IT and OT networks
- Continuous monitoring and threat detection
- Protection of remote connections and supply chains
Companies that fail to adopt these principles are not just behind, they are exposing themselves and their customers to unacceptable risk. And yet, within this challenge lies a major opportunity.
In today’s industrial landscape, success is no longer defined by building machines that simply work. It is defined by building systems that remain trustworthy, even when under attack. The winners will be those who can guarantee not just performance, but resilience.
This is a win-win scenario. Secure systems protect businesses, ensure continuity, and safeguard public trust. They also create competitive advantage in a market that increasingly values reliability under pressure.
The story of Venice is a warning, but also a lesson.
It reminds us that the line between cyber and physical is gone. That a vulnerability in code can translate into water rising in a historic square. That attackers no longer need to break in with force, they can log in.
And most importantly, it reinforces a simple but urgent truth:
In the world of OT, security is no longer optional. It is foundational.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Venice)
-
Security Affairs

-
Pro-Iran Handala group breached Israeli defence contractor PSK Wind Technologies
Iran-linked hackers claim to have breached Israeli air defence contractor PSK Wind, which develops command and control systems. Pro-Iran Handala group announced on April 2 that it breached PSK Wind Technologies, an Israeli engineering and IT firm specializing in integrated systems for defense and critical communications, including command and control solutions. Handala appears as a pro-Palestinian hacktivist group but is widely seen as a front for Iran-backed Void Manticore, as reported
Pro-Iran Handala group breached Israeli defence contractor PSK Wind Technologies
Iran-linked hackers claim to have breached Israeli air defence contractor PSK Wind, which develops command and control systems.
Pro-Iran Handala group announced on April 2 that it breached PSK Wind Technologies, an Israeli engineering and IT firm specializing in integrated systems for defense and critical communications, including command and control solutions.
Handala appears as a pro-Palestinian hacktivist group but is widely seen as a front for Iran-backed Void Manticore, as reported by SecurityWeek. Known for phishing, data theft, extortion, and destructive wiper attacks, they also engage in info operations and psychological warfare. Since the Iran conflict began, they’ve targeted Israeli military servers, intelligence officers, and companies, stealing or wiping data.
The Handala claims to have stolen sensitive data from PSK Wind, including documents on command and control systems, allegedly sending it to “Axis of Resistance” missile units. The Axis of Resistance is an Iran-led political and military alliance of groups opposing Israel, the US, and allies, including Hezbollah in Lebanon, Palestinian Islamic Jihad, Syrian regime forces, and Shia militias in Iraq like Kata’ib Hezbollah.
Handala issued a threat coinciding with Passover, a major Jewish holiday that commemorates the Israelites’ liberation from slavery in ancient Egypt, warning of attacks on Israeli defense and command centers.
At this time, neither PSK Wind nor the Israeli military commented, while the group released confidential files showcasing top secret communications systems, internal documents, location photos and more.
— International Cyber Digest (@IntCyberDigest) April 2, 2026
BREAKING: Iranian nation-state threat actor Handala has breached Israeli defense contractor PSK Wind Technologies.
They've released confidential files showcasing top secret communications systems, internal documents, location photos and more. pic.twitter.com/w2Li9P1ZLp
The PSK Wind attack is part of an ongoing wave of cyber attacks on Israeli military infrastructure since February 28, coinciding with missile and drone strikes by Iran and its allies. Hackers claim the firm manages Israel’s air defence command centers, critical to systems like Iron Dome.
Since the U.S.-Israeli war with Iran began in February, the Iran-linked group Handala has intensified its cyberattacks. It claimed responsibility for a destructive breach at medical tech firm Stryker that targeted its internal Microsoft environment and remotely wiped tens of thousands of employee devices without using malware.
The group claimed it wiped more than 200,000 servers, mobile devices, and other systems, forcing the company to shut down offices across 79 countries. The hacktivists also claimed they exfiltrated about 50TB of corporate data from the company’s infrastructure.
Recently, the Iran-linked hacking group Handala claimed the hack of the FBI Director Kash Patel’s personal Gmail account and shared alleged data, including photos and files.
The FBI is offering up to $10 million for information on the Handala hackers.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Handala)
-
Blog – Cyble

-
Hybrid Warfare 2026: When Cyber Operations and Kinetic Attacks Converge
In 2026, hybrid warfare is no longer a theoretical construct discussed in policy circles; it is shaping geopolitical conflict in real time. The convergence of cyber warfare and kinetic attacks has transformed how nations project power, blending missiles, malware, and misinformation into unified campaigns. What distinguishes modern hybrid warfare from earlier conflicts is not just the presence of digital operations, but their synchronization with physical strikes to produce layered, systemic di
Hybrid Warfare 2026: When Cyber Operations and Kinetic Attacks Converge
![]()
In 2026, hybrid warfare is no longer a theoretical construct discussed in policy circles; it is shaping geopolitical conflict in real time. The convergence of cyber warfare and kinetic attacks has transformed how nations project power, blending missiles, malware, and misinformation into unified campaigns. What distinguishes modern hybrid warfare from earlier conflicts is not just the presence of digital operations, but their synchronization with physical strikes to produce layered, systemic disruption.
Nowhere is this more evident than in the Middle East, where escalating tensions have turned the region into a proving ground for cyber-physical warfare. Governments, energy systems, financial networks, and communication infrastructures are being targeted simultaneously, exposing vulnerabilities that extend far beyond national borders. The result is a battlespace where the frontlines are both physical and invisible, and where disruption can ripple globally within hours.
From Conflict to Convergence: The Rise of Cyber Physical Warfare
The turning point came on February 28, 2026, when coordinated military and cyber campaigns marked a new phase in hybrid war strategy. Joint operations combined airstrikes with cyberattacks, information warfare, and psychological operations, targeting nuclear facilities, military assets, and digital infrastructure in parallel. Internet connectivity in targeted regions dropped to as low as 1–4% of normal levels during the initial assault, demonstrating the effectiveness of integrated cyber warfare and kinetic attacks.
These operations were not designed for immediate destruction alone. Instead, they aimed to disorient command structures, disrupt civilian communication, and weaken public trust. Digital interference extended to media channels and widely used mobile applications, some of which were compromised to spread false information and induce panic.
The response was equally multifaceted. Within 72 hours, missile and drone strikes were accompanied by a surge in cyber activity, including spear-phishing campaigns, ransomware-style attacks, and coordinated data exfiltration efforts targeting energy grids, airports, and financial institutions.
Hacktivists as Force Multipliers in Modern Hybrid Warfare
One of the defining characteristics of modern hybrid warfare is the role of non-state actors. More than 70 hacktivist groups became active participants in the 2026 conflict, blurring the lines between state-sponsored operations and independent cyber activism. These groups executed distributed denial-of-service (DDoS) attacks, website defacements, and credential harvesting campaigns across multiple countries.
Their involvement amplifies the scale and unpredictability of cyber warfare and kinetic attacks. While some groups operate with ideological motivations, others appear loosely aligned with state objectives, acting as force multipliers without formal attribution. This ambiguity complicates response strategies and increases the risk of escalation.
Cyber campaigns emerged during this period, including fake missile alert applications designed to harvest sensitive user data such as contacts, messages, and device identifiers. These tools demonstrated a level of technical refinement typically associated with advanced persistent threat (APT) groups.
Iranian Cyber Capabilities and Strategic Depth
Despite early disruptions to its infrastructure, Iran maintained a good cyber posture throughout the conflict. Established threat groups continued to conduct espionage, infrastructure attacks, and credential theft operations targeting sectors such as energy, aviation, and telecommunications.
Parallel to these efforts, Iran-aligned hacktivist groups escalated disruptive campaigns, including industrial control system intrusions and data leaks. Some reports suggest coordination with Russia-linked actors.
A notable example is the emergence of hybrid threat actors employing destructive malware. Tools designed to overwrite system data, disable operating systems, and erase critical infrastructure highlight a shift toward more aggressive cyber physical warfare tactics. These operations are often executed in stages: initial access through phishing or exposed services, lateral movement using legitimate system tools, and eventual payload deployment designed for maximum disruption.
Infrastructure Disruption and Global Spillover Effects
The consequences of hybrid warfare are not confined to the immediate conflict zone. Early incidents in 2026 disrupted fuel distribution in Jordan and interfered with navigation systems, affecting over 1,100 vessels near the Strait of Hormuz. These disruptions pose significant risks to global oil and gas supply chains, illustrating how localized cyber warfare and kinetic attacks can have worldwide economic implications.
Countries like India are experiencing indirect exposure due to interconnected digital ecosystems. Supply chain dependencies, shared technologies, and cloud-based services create pathways for cyber threats to propagate across borders. Vulnerabilities in widely used platforms, including VPNs and enterprise communication systems, are actively exploited.
Attackers are also leveraging AI-driven techniques to enhance their effectiveness. Phishing campaigns now use highly personalized messaging, while automated reconnaissance tools map organizational structures to identify high-value targets. These capabilities reduce the time required to execute complex attacks and increase their success rates.
Cybercrime Exploitation in a Hybrid War Environment
Geopolitical instability has created fertile ground for cybercriminal activity. More than 8,000 domains linked to the 2026 conflict have been registered, many serving as platforms for scams, malware distribution, and misinformation campaigns.
Examples include fake donation websites, fraudulent e-commerce platforms, and cryptocurrency schemes designed to exploit public sentiment. Conflict-themed malware, often disguised as alert systems or news updates, has been used to deploy backdoors and establish persistent access to compromised systems.
This convergence of cybercrime and state-aligned activity reflects a broader trend: the industrialization of cyber threats. Ransomware-as-a-service platforms now provide end-to-end attack capabilities, lowering the barrier to entry for less experienced actors. With subscription costs as low as $500 per month, cyberattacks are becoming accessible.
India’s Evolving Role in the Hybrid Warfare Landscape
India’s cybersecurity environment in 2026 reflects many of the same dynamics observed in the Middle East. State-sponsored actors are focusing on long-term access and intelligence gathering, targeting government networks, defense systems, and critical industries. These operations often remain undetected for extended periods, leveraging advanced persistent techniques to maintain access.
At the same time, hacktivist groups in India are becoming more organized and technically capable. Their activities now include coordinated data leaks, disruption campaigns, and the use of advanced tools traditionally associated with nation-state actors.
Supply chain attacks are a growing concern, particularly in sectors undergoing rapid digital transformation. Healthcare, manufacturing, and financial services are vulnerable due to their reliance on interconnected systems. These vulnerabilities highlight the importance of continuous monitoring, vendor risk management, and layered security architectures.
Intelligence-Driven Defense in the Age of Hybrid War Strategy
As hybrid warfare evolves, traditional reactive security models are proving insufficient. Organizations are shifting toward intelligence-driven approaches that integrate tactical, operational, strategic, and technical insights.
This shift is critical in a landscape where attackers exploit legitimate platforms, use “living off the land” techniques, and maintain persistence for extended periods. Behavioral analytics, anomaly detection, and contextual authentication are becoming essential tools for identifying threats that bypass conventional defenses.
Equally important is the adoption of proactive measures such as multi-factor authentication, network segmentation, and robust incident response frameworks. Information sharing between organizations and governments is also emerging as a key component of resilience in the face of coordinated cyber warfare and kinetic attacks.
Conclusion
Hybrid warfare in 2026 is an operational reality. Cyber warfare and kinetic attacks now work in tandem, creating rapid, high-impact disruptions across both digital and physical systems. This is the core of modern hybrid warfare: fast, coordinated, and difficult to contain.
Defending against this requires a shift to intelligence-led security. In a landscape shaped by cyber physical warfare, organizations need real-time visibility, faster response, and the ability to anticipate threats, not just react to them. Cyble enables this shift with its AI-native platform, Cyble Blaze AI, designed to predict and stop threats before they escalate.
Strengthen your hybrid war strategy, explore Cyble’s threat intelligence capabilities or schedule a demo to see proactive security in action.
References:
- https://cyble.com/resources/research-reports/iran-israel-us-conflict-cyber-threat-monitor-edition-2/
The post Hybrid Warfare 2026: When Cyber Operations and Kinetic Attacks Converge appeared first on Cyble.
-
HACKMAGEDDON
-
1-15 March 2026 Cyber Attacks Timeline
In the first half of March 2026 I collected 95 events (6.34 events/day) with a threat landscape dominated by malware once ahead of account takeovers and ransomware.
1-15 March 2026 Cyber Attacks Timeline
-
Blog – Cyble

-
India’s Evolving Cyber Threat Landscape: State-Sponsored Attacks, Hacktivism, and What’s Next in 2026
The India cyber threat landscape 2026 is no longer defined by isolated incidents or opportunistic attacks. It has become a dynamic, constantly shifting battleground shaped by geopolitical tensions, rapid digitization, and highly advanced hackers. What once looked like sporadic cybercrime has matured into a layered ecosystem of state-sponsored cyber attacks, organized ransomware groups, and a growing wave of Hacktivism in India. Recent threat intelligence observations reveal a new pattern: a
India’s Evolving Cyber Threat Landscape: State-Sponsored Attacks, Hacktivism, and What’s Next in 2026
![]()
The India cyber threat landscape 2026 is no longer defined by isolated incidents or opportunistic attacks. It has become a dynamic, constantly shifting battleground shaped by geopolitical tensions, rapid digitization, and highly advanced hackers. What once looked like sporadic cybercrime has matured into a layered ecosystem of state-sponsored cyber attacks, organized ransomware groups, and a growing wave of Hacktivism in India.
Recent threat intelligence observations reveal a new pattern: attackers are not only becoming more capable, but also more strategic. They are targeting supply chains, exploiting systemic weaknesses, and adapting their methods faster than most organizations can respond. As a result, understanding India cybersecurity trends in 2026 requires looking beyond raw numbers and examining how intent, capability, and opportunity are converging.
A Surge in Attacks: The Numbers Tell Only Part of the Story
India’s exposure to cyber risk has expanded dramatically. In the first half of 2024 alone, the country experienced 593 cyberattacks, including 388 data breaches, 107 data leaks, and 39 ransomware incidents. These figures highlight not just frequency, but diversity in attack types.
By October 2025, the threat environment had intensified further. Cybersecurity teams faced a sharp escalation marked by:
- Record-breaking supply chain compromises
- Ransomware activity is reaching one of its highest peaks of the year
- Attackers are deploying more refined and targeted techniques across sectors
The Rise of State-Sponsored Operations
One of the most defining aspects of the Indian cyber threat landscape in 2026 is the growing footprint of state-backed threat actors. These groups operate with long-term objectives, often aligned with geopolitical interests rather than immediate financial gain.
Unlike conventional cybercriminals, state-sponsored cyber attacks in India tend to:
- Focus on espionage and intelligence gathering.
- Target government networks, defense infrastructure, and strategic industries.
- Use advanced persistent threat (APT) techniques to maintain long-term access.
What makes these actors particularly dangerous is their patience. They are not looking for quick wins; they are embedding themselves within systems, studying operational patterns, and waiting for the right moment to act. This shift has forced Indian organizations to rethink cybersecurity not just as an IT concern, but as a matter of national and economic security.
Hacktivism in India: Ideology Meets Cyber Capability
Parallel to state-backed threats, Hacktivism in India has gained noticeable momentum. Unlike financially motivated attackers, hacktivist groups are driven by political, ideological, or social causes.
In recent years, these actors have:
- Defaced government and corporate websites
- Leaked sensitive data to make political statements
- Coordinated attacks around major national or international events
What’s changing in 2026 is the level of coordination and technical maturity. Hacktivist groups are no longer limited to basic disruptions; they are leveraging tools and tactics once associated with more advanced threat actors. This convergence is blurring the lines between activism and cyber warfare.
Supply Chain and Sector-Specific Vulnerabilities
A notable trend shaping India's cybersecurity trends in 2026 is the rise of supply chain attacks. Instead of targeting a single organization directly, attackers compromise with a trusted vendor or service provider to gain access to multiple downstream systems.
This approach has proven particularly effective in sectors undergoing rapid digital transformation, such as healthcare. India’s healthcare industry, for instance, has embraced digitization at scale, improving efficiency and accessibility. However, this expanded digital footprint has also introduced new vulnerabilities.
Threat actors targeting this sector are:
- Exploiting interconnected systems and third-party dependencies
- Using ransomware to disrupt critical services
- Leveraging stolen health data for financial and strategic gain
The Expanding Role of Threat Intelligence
In response to the growing complexity of cyber attacks in India 2026, organizations are turning to threat intelligence as a core defense mechanism. This goes beyond basic monitoring and involves a multi-layered approach:
- Tactical intelligence for real-time threat detection
- Operational intelligence to understand attacker behavior
- Strategic intelligence to anticipate future risks
- Technical intelligence to analyze vulnerabilities and exploits
What Lies Ahead: Preparing for the Next Phase
Looking forward, the India cyber threat landscape 2026 will likely be shaped by three key forces:
- Automation and AI in Attacks and Defense: Attackers are beginning to use automation to scale their operations, while defenders are deploying AI to detect anomalies faster. This creates a technological arms race with no clear endpoint.
- Blurring of Threat Actor Categories: The distinctions between cybercriminals, hacktivists, and state-sponsored groups are becoming less defined. Collaboration and shared tools are making attribution more difficult.
- Increased Focus on Operational Technology (OT): As industries digitize their operational environments, attacks will target systems that control physical processes, raising the stakes significantly.
Conclusion
The India cyber threat landscape 2026 has made cybersecurity a strategic priority, not just an IT function. With rising state sponsored cyber attacks India and coordinated Hacktivism in India, organizations must shift to intelligence-driven, proactive defense to keep up with cyber attacks in India 2026.
Cyble addresses this need with AI-native threat intelligence and real-time response capabilities that help teams stay ahead of evolving risks. To see how this approach works in practice, book a Personalized Demo today!
The post India’s Evolving Cyber Threat Landscape: State-Sponsored Attacks, Hacktivism, and What’s Next in 2026 appeared first on Cyble.
-
Security Affairs

-
Attack on Stryker’s Microsoft environment wiped employee devices without malware
The recent cyberattack on Stryker wiped tens of thousands of employee devices through its Microsoft environment, and systems are still offline. A recent cyberattack on medical technology giant Stryker targeted its internal Microsoft environment and remotely wiped tens of thousands of employee devices without using malware. The company confirmed that its medical devices were not affected and remain safe to use. However, electronic ordering systems are still offline, forcing customers to place
Attack on Stryker’s Microsoft environment wiped employee devices without malware
The recent cyberattack on Stryker wiped tens of thousands of employee devices through its Microsoft environment, and systems are still offline.
A recent cyberattack on medical technology giant Stryker targeted its internal Microsoft environment and remotely wiped tens of thousands of employee devices without using malware. The company confirmed that its medical devices were not affected and remain safe to use. However, electronic ordering systems are still offline, forcing customers to place orders manually through sales representatives.
Last week, Pro-Palestinian hacktivist group Handala claimed responsibility for a disruptive cyberattack against medical technology firm Stryker.
The group claimed it wiped more than 200,000 servers, mobile devices, and other systems, forcing the company to shut down offices across 79 countries. The hacktivists also claimed they exfiltrated about 50TB of corporate data from the company’s infrastructure.
Handala appears as a pro-Palestinian hacktivist group but is widely seen as a front for Iran-backed Void Manticore, as reported by SecurityWeek. Known for phishing, data theft, extortion, and destructive wiper attacks, they also engage in info operations and psychological warfare. Since the Iran conflict began, they’ve targeted Israeli military servers, intelligence officers, and companies, stealing or wiping data.
Stryker Corporation is a leading U.S.-based medical technology company that develops and manufactures devices and equipment used in hospitals, including surgical tools, orthopedic implants, medical imaging systems, and hospital beds. It is one of the world’s largest medical device manufacturers. Stryker reported global sales of $22.6 billion in 2024 and has over 53,000 employees.
The group said that this attack “is only the beginning of a new chapter in cyber warfare.”
Stryker said the incident was not a ransomware attack and no malware was deployed. BleepingComputer, citing a source familiar with the incident, reported that the attacker used the wipe command in Microsoft Intune to remotely erase data from nearly 80,000 devices between 5:00 and 8:00 a.m. UTC on March 11. The action was carried out after compromising an administrator account and creating a new Global Administrator account. The investigation is being led by Microsoft’s Detection and Response Team (DART) with support from Palo Alto’s Unit 42. Stryker confirmed the breach was confined to its internal Microsoft corporate environment and did not affect any of its medical products or connected devices.
“All Stryker products across our global portfolio, including connected, digital, and life-saving technologies, remain safe to use. This event was contained to Stryker’s internal Microsoft environment, and as a result it did not affect any of our products—connected or otherwise.” reads the company’s update published on 03/15/2026 11:30 a.m. ET.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Handala)
-
Blog – Cyble
-
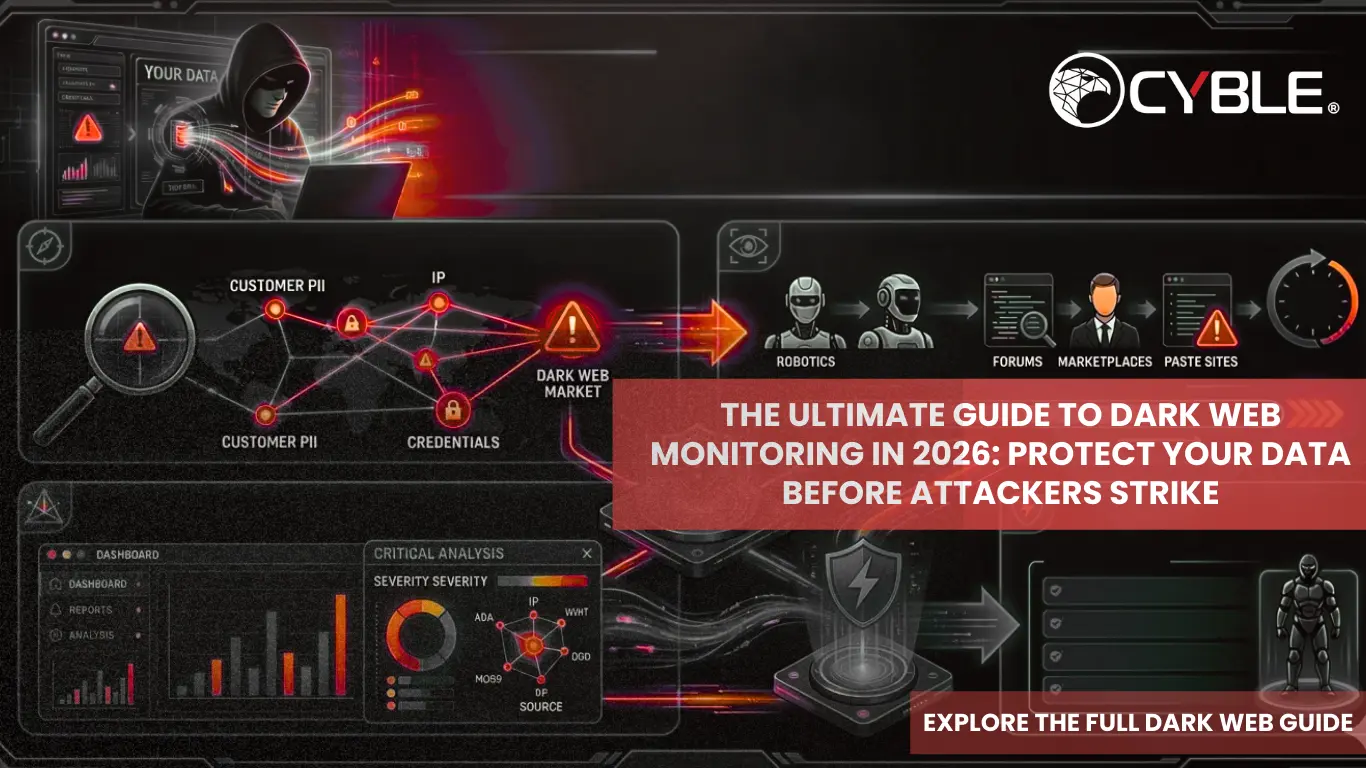
The Ultimate Guide to Dark Web Monitoring in 2026: Protect Your Data Before Attackers Strike
In 2026, cyber threats are originating on the dark web, where stolen credentials, exploit kits, and attack plans are bought and sold before they ever reach corporate networks. Organizations are turning to dark web intelligence and dark web monitoring solutions 2026 to detect new cyber threats early, monitor underground activity, and prevent breaches that traditional security tools may miss. Recent data from Cyble Research and Intelligence Labs (CRIL) shows the scale of this threat. In 2025 a
The Ultimate Guide to Dark Web Monitoring in 2026: Protect Your Data Before Attackers Strike
![]()
In 2026, cyber threats are originating on the dark web, where stolen credentials, exploit kits, and attack plans are bought and sold before they ever reach corporate networks. Organizations are turning to dark web intelligence and dark web monitoring solutions 2026 to detect new cyber threats early, monitor underground activity, and prevent breaches that traditional security tools may miss.
Recent data from Cyble Research and Intelligence Labs (CRIL) shows the scale of this threat. In 2025 alone, Cyble tracked 6,046 global data breach and leak incidents, with sectors such as government and finance among the most targeted. The research has also identified thousands of enterprise credentials circulating on dark web marketplaces, often harvested by infostealer malware and sold to cybercriminals.
For organizations that want to protect sensitive data, maintain reputation, and reduce operational risk, investing in dark web intelligence and dark web monitoring solutions is no longer optional; it’s a necessity.
What Is Dark Web Monitoring and Why It Matters in 2026
Dark web monitoring involves continuous scanning and intelligence gathering from hidden parts of the internet that aren’t indexed by traditional search engines, including TOR, I2P, ZeroNet, and encrypted chat channels. Cybercriminals use these platforms to trade stolen data, discuss exploits, and plan attacks.
Effective dark web surveillance allows organizations to detect threats early. By identifying stolen credentials, leaked data, and malicious activity before the attacker acts, security teams can reset passwords, notify affected personnel, and fortify defenses, turning reactive security into a proactive advantage.
How the Dark Web Has Evolved as a Threat Landscape
Once considered a fringe network, the dark web has become a structured ecosystem for cybercrime. Threat actors collaborate globally with the same levels of sophistication as legitimate enterprises, complete with forums for selling vulnerabilities, reputation systems for traders, and encrypted channels for planning attacks.
From ransomware kits to stolen databases and insider trading in sensitive corporate data, the dark web now functions as a hub for criminal collaboration and the commercialization of cyberattacks. Organizations that ignore this underground economy risk being blindsided.
What Kind of Data Ends Up on the Dark Web
Not all information on the dark web carries the same risk, but much of it is highly sensitive:
- Stolen credentials: Email/password combinations, VPN logins
- Breached corporate databases: Financial, HR, and client information
- Identity documents: Social Security numbers, passports
- Internal communications or proprietary IP
Even seemingly minor leaks, if unnoticed, can be exploited for data breaches. Platforms with data leak monitoring and dark web alerts allow teams to act before these threats escalate.
How Dark Web Monitoring Works
Modern dark web monitoring relies on a combination of automated technologies and expert analysis. Tools crawl hidden networks, marketplaces, paste sites, and private forums to collect data. AI and machine learning analyze signals, identify patterns of malicious behavior, and provide cyber threat intelligence in actionable formats.
Key capabilities include:
- Deep web and dark web scanning: Covering TOR, I2P, and other hidden networks
- Threat actor tracking: Linking chatter to known malicious entities
- Natural Language Processing (NLP): Interpreting unstructured forum text
- Actionable alerts: Prioritized intelligence for immediate response
This ensures organizations can anticipate threats rather than merely respond after an incident.
Key Features to Look for in a Dark Web Monitoring Solution
In 2026, an effective platform should offer:
- Continuous, real-time scanning
- Comprehensive monitoring of marketplaces, forums, and paste sites
- Automated alerts with remediation guidance
- Integration with existing cybersecurity systems
- Reporting for compliance and risk assessment
- Threat actor profiling and predictive analytics
Solutions lacking contextual intelligence or actionable insights are insufficient for modern threat landscapes.
Cyble Hawk for Advanced Threat Intelligence and Protection
To counter cyber threats from advanced adversaries, Cyble Hawk represents the next generation of dark web monitoring and threat intelligence. Beyond merely detecting leaks, Cyble Hawk tracks threat actors, uncovers emerging attack trends, and provides actionable insights across cyber and physical domains.
Key advantages of Cyble Hawk include:
- Deep Intelligence Fusion: Integrates open-source and proprietary intelligence for a 360-degree view of threats.
- AI & Deep Learning: Identifies threat actors and patterns in real time.
- Real-Time Alerts & Rapid Response: Immediate notifications for compromised credentials, breaches, and vulnerabilities.
- Incident Response & Resilience: Supports frameworks to continuously strengthen the cybersecurity posture.
Cyble Hawk doesn’t just monitor; it empowers organizations to detect, respond, and protect against the most advanced cyber threats before they escalate.
Dark Web Monitoring Across Industries
Different sectors face unique exposures, and tailored monitoring is critical:
- Financial Services: Detect compromised customer databases, prevent fraud schemes
- Healthcare: Identify patient data leaks, PHI exposure, and ransomware chatter
- Retail & E-Commerce: Monitor credential-stuffing lists, card dumps, and phishing campaigns
- Manufacturing & Critical Infrastructure: Track trade-secret exposure and APT activity
- Government & Public Sector: Detect contractor data leaks, APT campaigns, and impersonation threats
Building a Dark Web Monitoring Strategy in 2026
A robust strategy combines continuous monitoring with proactive response:
- Asset Prioritization: Identify the most critical data, accounts, and intellectual property
- Continuous Intelligence Gathering: Real-time scanning of forums, marketplaces, and paste sites
- Automated, Actionable Alerts: Ensure teams can respond quickly to compromised assets
- Integration with Cybersecurity Infrastructure: Link dark web intelligence with firewalls, identity protection, and incident response tools
- Employee Awareness: Educate staff to recognize phishing and social engineering attempts
This approach transforms dark web intelligence into a defensive advantage, reducing exposure and operational risk.
Frequently Asked Questions (FAQs)
Q.1: What is dark web intelligence?
Intelligence is collected from unindexed networks and underground forums to detect threats, leaked data, or compromised credentials.
Q.2: Can dark web monitoring prevent attacks?
It doesn’t prevent breaches outright, but early detection of leaks or malicious activity enables mitigation before exploitation.
Q.3: Who should use dark web monitoring?
Any organization handling sensitive data, including enterprises, government agencies, and financial institutions.
Q.4: How does Cyble Hawk enhance monitoring?
By combining AI, threat actor tracking, and real-time alerts, Cyble Hawk delivers actionable intelligence that allows organizations to detect, respond, and fortify defenses effectively.
Conclusion
In 2026, the dark web remains one of the most dynamic and high-risk areas of the cyber threat landscape. Organizations can no longer afford to rely on reactive security. By leveraging advanced monitoring platforms like Cyble Hawk, security teams gain early visibility into compromised data, track threat actors, and respond to risks before they escalate into major incidents.
Cyble Hawk combines AI-driven intelligence, real-time alerts, and expert threat analysis to help organizations detect threats faster and strengthen their cybersecurity posture. Schedule a personalized demo to see Cyble Hawk in action and learn how it can help protect your organization’s critical assets.
The post The Ultimate Guide to Dark Web Monitoring in 2026: Protect Your Data Before Attackers Strike appeared first on Cyble.
-
Unit 42
-
Insights: Increased Risk of Wiper Attacks
We are observing an increase of wiper attacks by the Iran-linked Handala Hack group (aka Void Manticore) through phishing and misuse of Microsoft Intune. The post Insights: Increased Risk of Wiper Attacks appeared first on Unit 42.
Insights: Increased Risk of Wiper Attacks
We are observing an increase of wiper attacks by the Iran-linked Handala Hack group (aka Void Manticore) through phishing and misuse of Microsoft Intune.
The post Insights: Increased Risk of Wiper Attacks appeared first on Unit 42.

-
Security | TechRepublic
-
Iran-Linked Hacktivists Hit Stryker, Knocking Employees Offline Across Multiple Countries
A cyberattack disrupted global operations at medical device maker Stryker, knocking employees offline and raising concerns about destructive wiper attacks. The post Iran-Linked Hacktivists Hit Stryker, Knocking Employees Offline Across Multiple Countries appeared first on TechRepublic.
Iran-Linked Hacktivists Hit Stryker, Knocking Employees Offline Across Multiple Countries
A cyberattack disrupted global operations at medical device maker Stryker, knocking employees offline and raising concerns about destructive wiper attacks.
The post Iran-Linked Hacktivists Hit Stryker, Knocking Employees Offline Across Multiple Countries appeared first on TechRepublic.
-
Security Affairs

-
Pro-Palestinian hacktivist group Handala targets Stryker in global disruption
Pro-Palestinian hacktivist group Handala claims a cyberattack on Stryker, alleging it wiped 200,000 systems and disrupted global operations. Pro-Palestinian hacktivist group Handala claims responsibility for a disruptive cyberattack against medical technology firm Stryker. “Medical technology giant Stryker is experiencing a global outage across its systems after a cyberattack early Wednesday. Staff and contractors report that the logo of an Iran-linked hacking group has appeared on login
Pro-Palestinian hacktivist group Handala targets Stryker in global disruption
Pro-Palestinian hacktivist group Handala claims a cyberattack on Stryker, alleging it wiped 200,000 systems and disrupted global operations.
Pro-Palestinian hacktivist group Handala claims responsibility for a disruptive cyberattack against medical technology firm Stryker.
“Medical technology giant Stryker is experiencing a global outage across its systems after a cyberattack early Wednesday. Staff and contractors report that the logo of an Iran-linked hacking group has appeared on login pages.” reported The Wall Street Journal.
The group claims it wiped more than 200,000 servers, mobile devices, and other systems, forcing the company to shut down offices across 79 countries. The hacktivists also claim they exfiltrated about 50TB of corporate data from the company’s infrastructure.
Handala appears as a pro-Palestinian hacktivist group but is widely seen as a front for Iran-backed Void Manticore, as reported by SecurityWeek. Known for phishing, data theft, extortion, and destructive wiper attacks, they also engage in info operations and psychological warfare. Since the Iran conflict began, they’ve targeted Israeli military servers, intelligence officers, and companies, stealing or wiping data.
Stryker Corporation is a leading U.S.-based medical technology company that develops and manufactures devices and equipment used in hospitals, including surgical tools, orthopedic implants, medical imaging systems, and hospital beds. It is one of the world’s largest medical device manufacturers. Stryker reported global sales of $22.6 billion in 2024 and has over 53,000 employees.
“We announce to the world that, in retaliation for the brutal attack on the Minab school and in response to ongoing cyber assaults against the infrastructure of the Axis of Resistance, our major cyber operation has been executed with complete success.
The Zionist-rooted corporation, Stryker, one of the key arms of the global Zionist lobby and a central ring in the ‘New Epstein’ chain, has been struck with an unprecedented blow. In this operation, over 200,000 systems, servers, and mobile devices have been wiped and 50 terabytes of critical data have been extracted.” Handala wrote on its website.
“Stryker’s offices in 79 countries have been forced to shut down. All the acquired data is now in the hands of the free people of the world, ready to be used for the true advancement of humanity and the exposure of injustice and corruption.”
The group said that this attack “is only the beginning of a new chapter in cyber warfare.”
Reports from Stryker employees in many countries, including the U.S., Ireland, and Australia, confirm devices were remotely wiped overnight.
“We are experiencing a severe, global disruption impacting all Stryker laptops and systems that connect to our network,” reads a message sent to staff based in Cork that Irish Mirror reported.
“At this time, the root cause has not yet been identified. We are actively engaged with Microsoft and treating this a critical, enterprise-wide incident.” reads a separate update sent to employees in Asia.
The company’s Entra login page was defaced with the Handala logo. Personal devices enrolled for work access also lost data, staff had to remove corporate apps, and many internal services went down.
Stryker is now restoring systems amid a global outage.
The stock of the Medical technology giant dropped after the cyberattack-
“Shares of Stryker retreated after the medical technology company was hit by a cyberattack.” reads The Wall Street Journal. “
Several governments have historically leveraged hacktivist groups during conflicts or geopolitical tensions, often to achieve strategic goals while maintaining plausible deniability. These groups provide states with a way to conduct cyber operations without directly attributing attacks to official state agencies.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Stryker)
-
HACKMAGEDDON
-
February 2026 Cyber Attacks Statistics
After the cyber attacks timelines, it’s time to publish the statistics for February 2026 where I collected and analyzed 176 events. In February 2026, Cyber Crime continued to lead the Motivations chart with 62%.
February 2026 Cyber Attacks Statistics
-
HACKMAGEDDON
-
16-28 February 2026 Cyber Attacks Timeline
In the second half of February 2026 I collected 80 events with a threat landscape dominated by malware with 42%, ahead of account takeovers and ransomware.
16-28 February 2026 Cyber Attacks Timeline
-
Security | TechRepublic
-
Hacktivists Claim DHS Breach, Leak 6,600+ ICE Contractor Records
Hacktivists claim they breached DHS systems, leaking records tied to 6,681 ICE contractor applicants, including major tech and defense firms. The post Hacktivists Claim DHS Breach, Leak 6,600+ ICE Contractor Records appeared first on TechRepublic.
Hacktivists Claim DHS Breach, Leak 6,600+ ICE Contractor Records
Hacktivists claim they breached DHS systems, leaking records tied to 6,681 ICE contractor applicants, including major tech and defense firms.
The post Hacktivists Claim DHS Breach, Leak 6,600+ ICE Contractor Records appeared first on TechRepublic.