New Quasar Linux (QLNX) RAT Hijacks Cloud Keys and NPM Tokens
The post New Quasar Linux (QLNX) RAT Hijacks Cloud Keys and NPM Tokens appeared first on Daily CyberSecurity.

Phishing still hooks users around the world and coaxes them to hand over credentials. But on occasion the good guys take them down, like the FBI in collaboration with Indonesian law enforcement did with W3LLStore marketplace.
The post FBI, Indonesian Authorities Team to Take Down Site Ripping Off Users for Millions appeared first on Security Boulevard.

Washington’s push to ban foreign-made Wi-Fi routers may sound tough on cybersecurity, but like earlier bans on foreign drones and telecom gear it risks becoming security theater that ignores the real problem: Millions of unpatched devices already sitting on American networks.
The post Banning Routers Won’t Secure the Internet appeared first on Security Boulevard.

While companies use "perp walks" for terminated employees, 48% of manufacturers fail to revoke digital access within 24 hours. Explore the growing risk of dormant accounts, the 74% automation gap in provisioning, and why experts like Darren Guccione and James Maude call overprivileged identities a "frictionless path" for modern cyberattacks.
The post Dormant Accounts Leave Manufacturing Orgs Open to Attack appeared first on Security Boulevard.

![]()
Before you can securely sign software or automate code signing in your Windows environment, you will need to configure your credentials for DigiCert® KeyLocker and the Signing Manager Command-Line Tool (SMCTL). Your credentials create a trusted connection between your local signing tools and DigiCert ONE to ensure that only authorized users are able to access… Read More How to Setup Credentials for Windows to Use DigiCert KeyLocker & SMCTL?
The post How to Setup Credentials for Windows to Use DigiCert KeyLocker & SMCTL? appeared first on SignMyCode - Resources.
The post How to Setup Credentials for Windows to Use DigiCert KeyLocker & SMCTL? appeared first on Security Boulevard.
A massive unsecured database exposed 149 million logins, raising concerns over infostealer malware and credential theft.
The post Data Leak Exposes 149M Logins, Including Gmail, Facebook appeared first on TechRepublic.
Google has released an update for its Chrome browser that includes 13 security fixes, four of which are classified as high severity. One of these was found in Chrome’s Digital Credentials feature–a tool that lets you share verified information from your digital wallet with websites so you can prove who you are across devices.
Chrome is by far the world’s most popular browser, with an estimated 3.4 billion users. That scale means when Chrome has a security flaw, billions of users are potentially exposed until they update.
That’s why it’s important to install these patches promptly. Staying unpatched means you could be at risk just by browsing the web, and attackers often exploit these kinds of flaws before most users have a chance to update. Always let your browser update itself, and don’t delay restarting the browser as updates usually fix exactly this kind of risk.
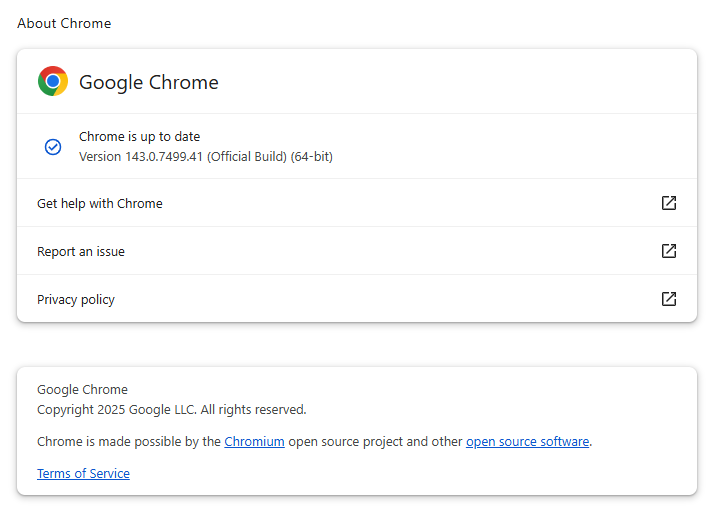
The latest version number is 143.0.7499.40/.41 for Windows and macOS, and 143.0.7499.40 for Linux. So, if your Chrome is on version 143.0.7499.40 or later, it’s protected from these vulnerabilities.
The easiest way to update is to allow Chrome to update automatically, but you can end up lagging behind if you never close your browser or if something goes wrong—such as an extension stopping you from updating the browser.
To update manually, click the More menu (three dots), then go to Settings > About Chrome. If an update is available, Chrome will start downloading it. Restart Chrome to complete the update, and you’ll be protected against these vulnerabilities.
You can also find step-by-step instructions in our guide to how to update Chrome on every operating system.

One of the vulnerabilities was found in the Digital Credentials feature and is tracked as CVE-2025-13633. As usual Google is keeping the details sparse until most users have updated. The description says:
Use after free in Digital Credentials in Google Chrome prior to 143.0.7499.41 allowed a remote attacker who had compromised the renderer process to potentially exploit heap corruption via a crafted HTML page.
That sounds complicated so let’s break it down.
Use after free (UAF) is a specific type of software vulnerability where a program attempts to access a memory location after it has been freed. That can lead to crashes or, in some cases, let an attackers run their own code.
The renderer process is the part of modern browsers like Chrome that turns HTML, CSS, and JavaScript into the visible webpage you see in a tab. It’s sandboxed for safety, separate from the browser’s main “browser process” that manages tabs, URLs, and network requests. So, for HTML pages, this is essentially the browser’s webpage display engine.
The heap is an area of memory made available for use by the program. The program can request blocks of memory for its use within the heap. In order to allocate a block of some size, the program makes an explicit request by calling the heap allocation operation.
A “remote attacker who had compromised the renderer” means the attacker would already need a foothold (for example, via a malicious browser extension) and then lure you to a site containing specially crafted HTML code.
So, my guess is that this vulnerability could be abused by a malicious extension to steal the information handled through Digital Credentials. The attacker could access information normally requiring a passkey, making it a tempting target for anyone trying to steal sensitive information.
Some of the fixes also apply to other Chromium browsers, so if you use Brave, Edge, or Opera, for example, you should keep an eye out for updates there too.
We don’t just report on threats—we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your, and your family’s, personal information by using identity protection.