eBay Struggles with Widespread Outage, Disrupting Transactions and API Access
![]()

![]()

![]()
![]()
Law enforcement agencies across Europe, the United States, and other partner nations cracked down on the commercial DDoS-for-hire ecosystem, targeting both operators and customers of services used to knock websites offline.
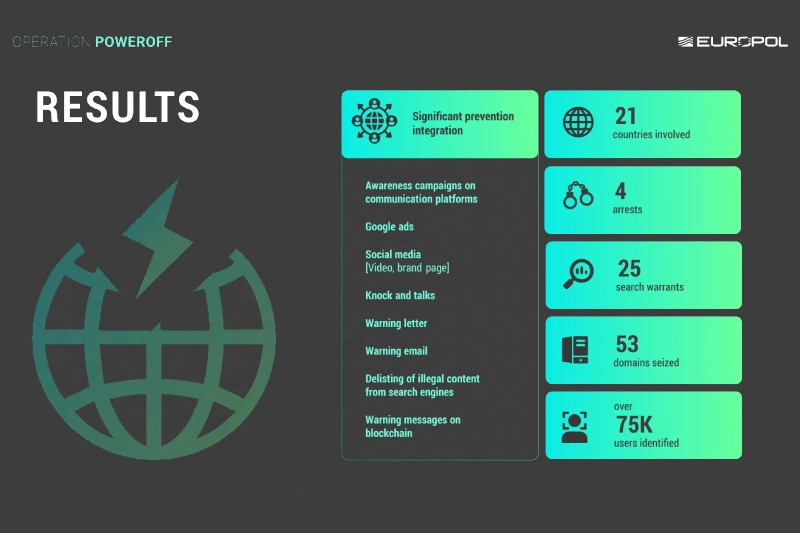
The coordinated effort led to the seizure of 53 domains, four arrests, 25 search warrants, and warning notices sent to more than 75,000 people suspected of using so-called “booter” or “stresser” platforms.
DDoS-for-hire platforms allow customers to pay relatively small fees to launch distributed denial-of-service attacks against websites, gaming services, businesses, and public infrastructure. In fact, AI-driven threat intelligence company Cyble, in a new research report released today said, DDoS was the primary mode of attack during the ongoing Iran-Israel and U.S. conflict. Cyble recorded a 140% increase in DDoS attacks targeting Israeli entities after September 2025, and at the height of the conflict, saw 40 DDoS attacks per day.
These DDoS-for-hire services often market themselves as legitimate stress-testing tools, but authorities say they are widely abused for harassment, extortion, and disruption.
The latest enforcement wave is part of the long-running international initiative known as "Operation PowerOFF," which has previously dismantled multiple booter services and disrupted related infrastructure.
The U.S. Department of Justice said investigators in Alaska seized infrastructure linked to eight DDoS-for-hire domains, including services branded as Vac Stresser and Mythical Stress, both of which allegedly advertised the ability to launch tens of thousands of attacks per day. Investigators also searched backend servers tied to the platforms.
Officials did not immediately identify those behind the services, but said the action was intended to disrupt the technical backbone used to power attacks globally.
In one of the more unusual aspects of the operation, authorities contacted more than 75,000 suspected users directly through warning emails and letters.
Law enforcement agencies appear to be using deterrence alongside takedowns—sending a message that paying for DDoS attacks leaves a trail and may bring legal consequences.
Security experts say the tactic could be particularly effective against younger or low-level offenders who use these platforms for gaming disputes, personal retaliation, or vandalism without fully understanding the legal risks.
Investigators said they identified around three million criminal accounts connected to the wider DDoS-for-hire ecosystem. The sheer number of accounts shows how industrialized cybercrime services have become. Instead of building botnets or malware, users can simply rent attack capability on demand.
DDoS attacks overwhelm a target with traffic, often causing websites, applications, or networks to crash. While sometimes dismissed as nuisance attacks, they can disrupt hospitals, financial institutions, government portals, and emergency services.
Recent years have also seen DDoS attacks used as smokescreens to distract security teams while other intrusions unfold.
Despite repeated takedowns, booter services often reappear quickly under new names, new domains, or relocated hosting providers. Researchers have found that while seizures can significantly reduce traffic in the short term, the market has proven resilient over time.
That means operations like PowerOFF may need to combine arrests, infrastructure seizures, financial disruption, and user deterrence to have lasting impact.