Global Rights Event Scrapped in Zambia Amid Sudden Government Decision
![]()

![]()
Tom Eston interviews offensive AI researcher and PhD candidate Andrew Wilson, a former Bishop Fox partner who helped grow the firm from under 20 people to nearly 500, built award-winning AI solutions for SOC modernization, founded Cactus Con, and relocated his family to Guadalajara to open and scale a Bishop Fox office. They discuss Mexico’s […]
The post The Real State of Offensive Security: AI, Penetration Testing & The Road Ahead with Andrew Wilson appeared first on Shared Security Podcast.
The post The Real State of Offensive Security: AI, Penetration Testing & The Road Ahead with Andrew Wilson appeared first on Security Boulevard.

Last summer, a conversation took place between a group of security professionals from EclecticIQ and Booz Allen Hamilton. The topic was straightforward: The Hague is home to NATO, Europol, the Dutch NCSC, and The Hague Security Delta - the largest security cluster in Europe. It is also home to major global enterprises, financial institutions, and critical national infrastructure that represent some of the most significant concentrations of cyber risk on the continent. By any measure, The Hague is one of the most important security hubs in the world.
And yet it had no grassroots community event to reflect that status. No accessible, practitioner-led space where the community could come together, share real knowledge, and connect outside of a commercial setting... and notably, no BSides event.
The question was simple. Why had nobody done this? What followed was equally simple.
We decided we would.
Researchers have discovered a new attack targeting Mac users. It lures them to a fake job website, then tricks them into downloading malware via a bogus software update.
The attackers pose as recruiters and contact people via LinkedIn, encouraging them to apply for a role. As part of the application process, victims are required to record a video introduction and upload it to a special website.
On that website, visitors are tricked into installing a so-called update for FFmpeg media file-processing software which is, in reality, a backdoor. This method, known as the Contagious Interview campaign, points to the Democratic People’s Republic of Korea (DPRK).
Contagious Interview is an illicit job-platform campaign that targets job seekers with social engineering tactics. The actors impersonate well-known brands and actively recruit software developers, artificial intelligence researchers, cryptocurrency professionals, and candidates for both technical and non-technical roles.
The malicious website first asks the victim to complete a “job assessment.” When the applicant tries to record a video, the site claims that access to the camera or microphone is blocked. To “fix” it, the site prompts the user to download an “update” for FFmpeg.
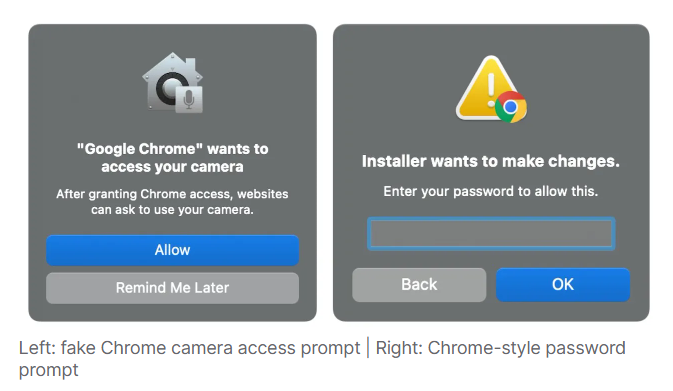
Much like in ClickFix attacks, victims are given a curl command to run in their Terminal. That command downloads a script which ultimately installs a backdoor onto their system. A “decoy” application then appears with a window styled to look like Chrome, telling the user Chrome needs camera access. Next, a window prompts for the user’s password, which, once entered, is sent to the attackers via Dropbox.

The end-goal of the attackers is Flexible Ferret, a multi-stage macOS malware chain active since early 2025. Here’s what it does and why it’s dangerous for affected Macs and users:
After stealing the password, the malware immediately establishes persistence by creating a LaunchAgent. This ensures it reloads every time the user logs in, giving attackers long-term, covert access to the infected Mac.
FlexibleFerret’s core payload is a Go-based backdoor. It enables attackers to:
Basically, this means the infected Mac becomes part of a remote-controlled botnet with direct access for cybercriminals.
While this campaign targets Mac users, that doesn’t mean Windows users are safe. The same lure is used, but the attacker is known to use the information stealer InvisibleFerret against Windows users.
The best way to stay safe is to be able to recognize attacks like these, but there are some other things you can do.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.