The Tadashi Files: Inside the xlabs_v1 Botnet Targeting 4 Million Android Devices
The post The Tadashi Files: Inside the xlabs_v1 Botnet Targeting 4 Million Android Devices appeared first on Daily CyberSecurity.
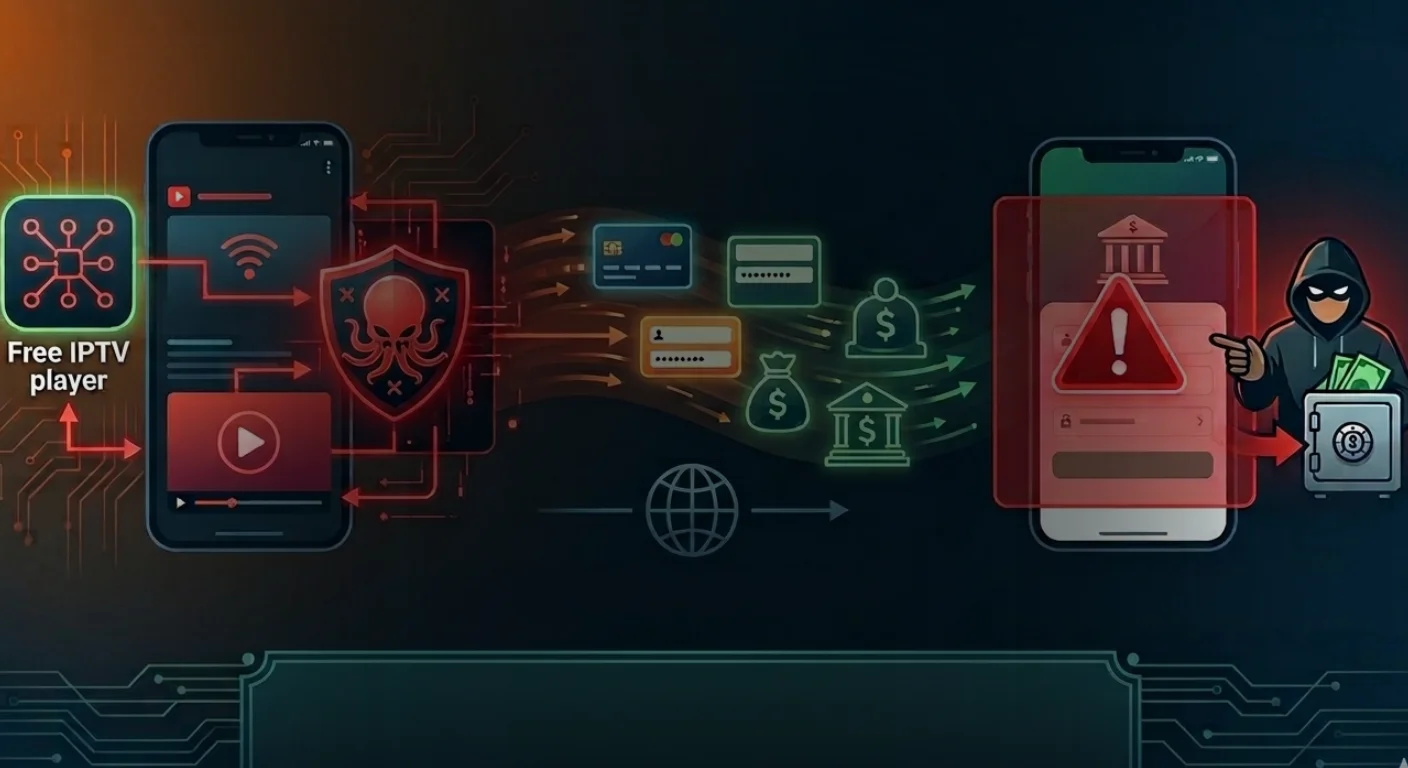
Four Android banking malware campaigns are targeting more than 800 apps by abusing overlays, Accessibility permissions, and sideloaded fake apps to steal PINs.
The post Over 800 Android Apps Targeted in PIN-Stealing Trojan Campaign appeared first on TechRepublic.

![]()
A flaw in the EngageLab SDK exposed 50 million Android users, allowing malicious apps to exploit trusted permissions and access sensitive data.
The post Microsoft: Third-Party Android Vulnerability Leaves Over 50M Users Exposed appeared first on TechRepublic.
NoVoice malware was found in 50 Android apps on Google Play, with 2.3 million downloads, by bypassing detection and targeting outdated devices.
The post Android Alert: 50 Google Play Apps Linked to ‘NoVoice’ Malware Reached 2.3M Downloads appeared first on TechRepublic.
![]()

A new Android malware called BeatBanker spreads through fake Starlink apps distributed on websites posing as the Google Play Store. Once installed, it hijacks devices, steals login credentials, tampers with cryptocurrency transactions, and secretly mines Monero, combining banking trojan capabilities with crypto-mining.
The campaign mainly targets users in Brazil, spreading through phishing pages and sometimes via WhatsApp, allowing attackers to maintain long-term surveillance and remote control of compromised phones.
In newer attacks, operators replaced the banker component with a RAT and maintain persistence while communicating with mining pools.
The campaign starts with a phishing site that mimics the Google Play Store and distributes a fake “INSS Reembolso” app.
The malware impersonates the official service of Instituto Nacional do Seguro Social, tricking users into installing a trojanized APK disguised as a trusted government app.
“At various stages of the attack, BeatBanker disguises itself as a legitimate application on the Google Play Store and as the Play Store itself.” states the report published by Kaspersky.

The packed APK uses a native library to decrypt and load hidden malware directly in memory, helping it evade mobile antivirus detection. It also checks device details and blocks execution in analysis environments. The app then shows a fake update page resembling the Google Play Store to trick victims into installing additional malicious payloads and maintain persistence.
After victims tap Update on a fake Google Play Store screen, the malware downloads a cryptominer based on XMRig and connects to attacker-controlled mining pools. It uses Firebase Cloud Messaging as a as its command-and-control channel. Each message triggers checks on battery level, temperature, installation date, and user activity, allowing attackers to start or stop the hidden crypto miner and keep infected devices responsive to remote commands while monitoring key device conditions.
BeatBanker maintains persistence by running a foreground service that plays a silent audio loop to avoid shutdown. It also installs a banking trojan that abuses accessibility permissions to control the device, monitor browsers, and target crypto apps such as Binance and Trust Wallet.
“BeatBanker compromises the machine with a cryptocurrency miner and introduces another malicious APK that acts as a banking Trojan. This Trojan uses previously obtained permission to install an additional APK called INSS Reebolso, which is associated with the package com.destination.cosmetics.” continues the report.
When users attempt Tether transfers, the malware overlays fake screens and silently replaces the destination wallet address with one controlled by the attackers.
Kaspersky detected new BeatBanker samples spreading through a fake Starlink app. The malware keeps earlier persistence tricks such as looped audio and fixed notifications and still deploys a crypto miner. Instead of a banking trojan, however, it now installs BTMOB RAT, a highly obfuscated remote access tool.
BTMOB, linked to malware families like CraxsRAT and CypherRAT, operates as Malware-as-a-Service and provides full control over infected devices. It can grant permissions automatically, run persistently in the background, hide notifications, capture screen-lock credentials, log keystrokes, track GPS location, and access cameras.
“BeatBanker is an excellent example of how mobile threats are becoming more sophisticated and multi-layered. Initially focused in Brazil, this Trojan operates a dual campaign, acting as a Monero cryptocurrency miner, discreetly draining your device’s battery life while also stealing banking credentials and tampering with cryptocurrency transactions.” concludes the report that includes Indicators of Compromise (IoCs). “Moreover, the most recent version goes even further, substituting the banking module with a full-fledged BTMOB RAT.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, BeatBanker Android malware)
A fake Android antivirus app called TrustBastion is spreading malware and stealing banking credentials. Here’s how it works and how to stay protected.
The post Fake ‘Antivirus’ App Spreads Android Malware, Steals Banking Credentials appeared first on TechRepublic.
Attackers exploited Hugging Face’s trusted infrastructure to spread an Android RAT, using fake security apps and thousands of malware variants.
The post Hugging Face Repositories Abused in New Android Malware Campaign appeared first on TechRepublic.
The Polish Computer Emergency Response Team (CERT Polska) analyzed a new Android-based malware that uses NFC technology to perform unauthorized ATM cash withdrawals and drain victims’ bank accounts.
Researchers found that the malware, called NGate, lets attackers withdraw cash from ATMs (Automated Teller Machines, or cash machines) using banking data exfiltrated from victims’ phones—without ever physically stealing the cards.
NFC is a wireless technology that allows devices such as smartphones, payment cards, and terminals to communicate when they’re very close together. So, instead of stealing your bank card, the attackers capture NFC (Near Field Communication) activity on a mobile phone infected with the NGate malware and forward that transaction data to devices at ATMs. In NGate’s case the stolen data is sent over the network to the attackers’ servers rather than being relayed purely by radio.
NFC comes in a few “flavors.” Some produce a static code—for example, the card that opens my apartment building door. That kind of signal can easily be copied to a device like my “Flipper Zero” so I can use that to open the door. But sophisticated contactless payment cards (like your Visa or Mastercard debit and credit cards) use dynamic codes. Each time you use the NFC, your card’s chip generates a unique, one-time code (often called a cryptogram or token) that cannot be reused and is different every time.
So, that’s what makes the NGate malware more sophisticated. It doesn’t simply grab a signal from your card. The phone must be infected, and the victim must be tricked into performing a tap-to-pay or card-verification action and entering their PIN. When that happens, the app captures all the necessary NFC transaction data exchanged — not just the card number, but the fresh one-time codes and other details generated in that moment.
The malware then instantly sends all that NFC data, including the PIN, to the attacker’s device. Because the codes are freshly generated and valid only for a short time, the attacker uses them immediately to imitate your card at an ATM; the accomplice at the ATM presents the captured data using a card-emulating device such as a phone, smartwatch, or custom hardware.
But, as you can imagine, being ready at an ATM when the data comes in takes planning—and social engineering.
First, attackers need to plant the malware on the victim’s device. Typically, they send phishing emails or SMS messages to potential victims. These often claim there is a security or technical issue with their bank account, trying to induce worry or urgency. Sometimes, they follow up with a phone call, pretending to be from the bank. These messages or calls direct victims to download a fake “banking” app from a non-official source, such as a direct link instead of Google Play.
Once installed, the app app asks for permissions and leads victims through fake “card verification” steps. The goal is to get victims to act quickly and trustingly—while an accomplice waits at an ATM to cash out.
NGate only works if your phone is infected and you’re tricked into initiating a tap-to-pay action on the fake banking app and entering your PIN. So the best way to stay safe from this malware is keep your phone protected and stay vigilant to social engineering:
Malwarebytes for Android detects these banking Trojans as Android/Trojan.Spy.NGate.C; Android/Trojan.Agent.SIB01022b454eH140; Android/Trojan.Agent.SIB01c84b1237H62; Android/Trojan.Spy.Generic.AUR9552b53bH2756 and Android/Trojan.Banker.AURf26adb59C19.
We don’t just report on phone security—we provide it
Cybersecurity risks should never spread beyond a headline. Keep threats off your mobile devices by downloading Malwarebytes for iOS, and Malwarebytes for Android today.