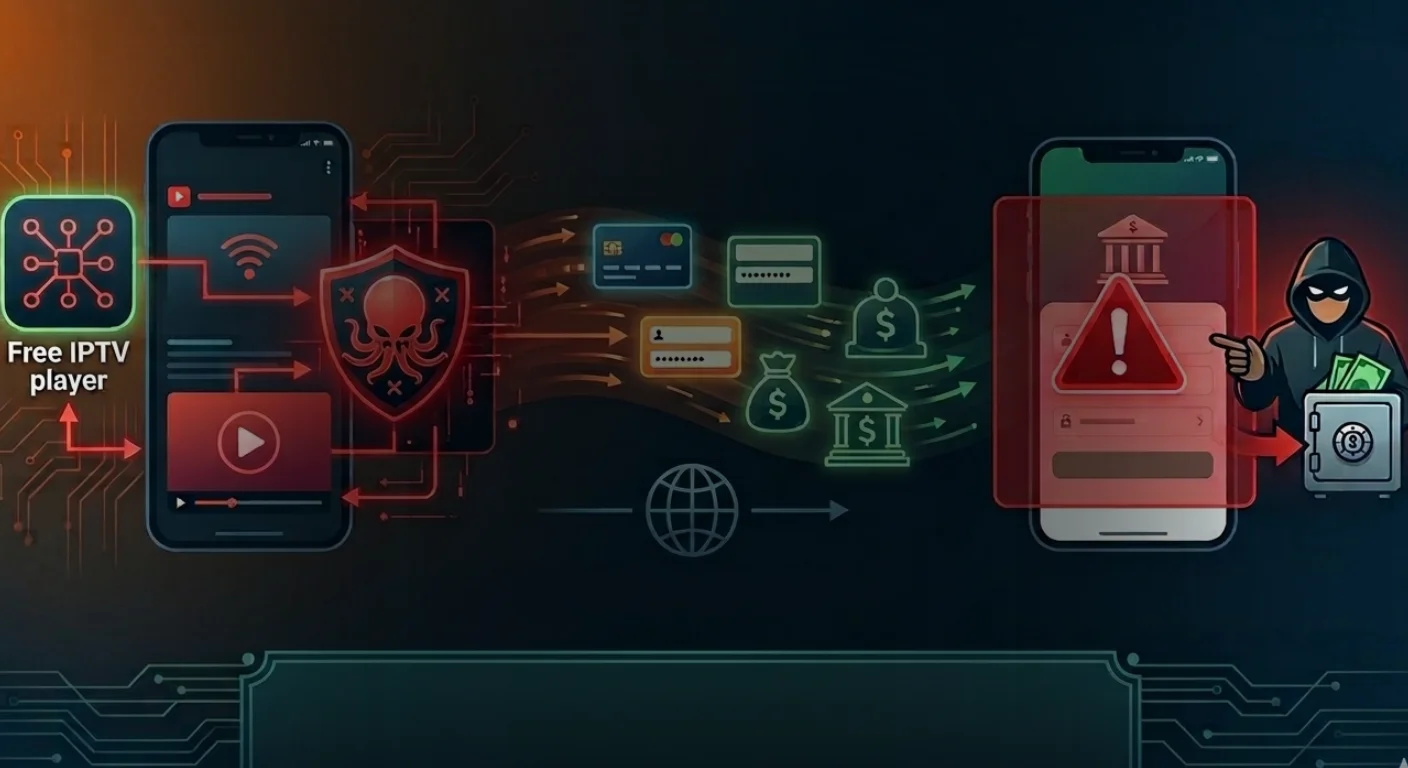
Perseus Android Malware Targets Mobile Banking Users via Fake IPTV Apps
20 de Março de 2026, 02:49
![]()
Perseus Android Malware Shows Evolution of Mobile Threats
The Perseus Android malware builds on older malware families like Cerberus and Phoenix, but it doesn’t simply replicate them, it refines them. This is part of a broader trend in Android malware, where attackers reuse proven codebases and add targeted enhancements rather than reinventing the wheel. This evolution matters. Instead of noisy, easily detectable attacks, modern mobile security threats are becoming quieter and more efficient. Perseus, for instance, leverages legitimate Android features like Accessibility Services to maintain control over infected devices. This allows it to operate in ways that mimic normal user behavior, making detection significantly harder. The result? A malware strain that blends in rather than stands out.IPTV Apps Malware: A Familiar Trap with Higher Stakes
One of the most notable aspects of the Perseus Android malware is its distribution method. It hides inside IPTV apps, streaming applications that users often download outside official app stores. This is not accidental. IPTV apps are widely used and frequently sideloaded, especially in regions like Turkey and Italy, which are the primary targets of this campaign. Users are already conditioned to install these apps manually, lowering their guard in the process. This tactic reflects a growing pattern in IPTV apps malware campaigns. Instead of exploiting technical vulnerabilities, attackers exploit user behavior. It’s a subtle but effective shift—from hacking systems to manipulating habits.Targeting Notes and Personal Data
What sets the Perseus Android malware apart from typical Android malware is its focus on personal notes. While most malware targets login credentials or banking data, Perseus goes a step further by scanning note-taking applications. This is a significant escalation. Notes often contain highly sensitive information, passwords, recovery phrases, financial details, and even private thoughts. By accessing this data, attackers gain context, not just credentials. The malware uses a command called “scan_notes” to systematically open note-taking apps and extract their contents without user interaction. This isn’t just data theft—it’s surveillance.Full Device Takeover Through Advanced Remote Control
The Perseus Android malware also enables full device takeover using remote control capabilities. Through Accessibility-based sessions, attackers can monitor screens in near real time, capture user inputs, and even overlay fake interfaces to steal sensitive information. This combination of keylogging and overlay attacks makes it particularly dangerous for mobile banking data theft. Users may believe they are interacting with legitimate banking apps, while in reality, their inputs are being intercepted. In practical terms, this means attackers can not only access accounts but also initiate and authorize fraudulent transactions.Strong Evasion Tactics Make Detection Harder
Another reason the Perseus Android malware is concerning is its ability to evade detection. It performs extensive environment checks to determine whether it is running on a real device or within an analysis environment. It looks for signs like:- Presence of debugging tools
- Emulator characteristics
- Root access indicators
- Unrealistic hardware or battery data