The post Goodbye ViveTool: Microsoft Unveils Native “Feature Flags” to Unlock Hidden Windows 11 Powers appeared first on Daily CyberSecurity.
Visualização de leitura
Gmail Finally Lets You Change Your Email Address Without Losing Anything
Gmail users in the US can now change their email address without losing data. Here’s how the long-awaited Google feature works and its key limits.
The post Gmail Finally Lets You Change Your Email Address Without Losing Anything appeared first on TechRepublic.
Cybersecurity Is a Calling, Not Just a Career — Dr. Priyanka Sunder (PD) on Women Leading the Charge

Dr Priyanka Sunder (PD) Interview on Cybersecurity, GRC & Leadership
TCE: On the occasion of International Women's Day, how do you see the role of women evolving in cybersecurity leadership and governance?
Dr. Priyanka Sunder (PD): Women bring unique perspectives that enrich strategy and problem-solving — empathy, patience, determination, and attention to detail are not just soft skills but critical enablers of effective cybersecurity. These qualities help uncover root causes, ensure logical closures of risk remediations, and strengthen decision-making. By turning challenges into opportunities and stepping beyond comfort zones, we build cross-functional skills, foster a One Team culture, and position cybersecurity as a true business enabler. Women leaders excel at servant and situational leadership, building the trust and collaboration that unite teams around common organizational goals — inspiring the next generation to see cybersecurity not just as a career, but as a calling.TCE: How have you seen GRC evolve in helping organizations manage today's complex threat landscape?
Dr. Priyanka Sunder (PD): When I started as an Information Security Analyst 20 years ago, organizations treated compliance as a "check in the box" exercise. It took over a decade for the shift toward recognizing that cyber hygiene is a fundamental pillar of enterprise resilience. Today, companies understand that compliance is not a one-time effort — it's a moving target. The question is no longer "have you been compromised?" but "how prepared are we, and how fast can we recover?" GRC now plays a critical role through periodic maturity assessments, Information Security scorecards, integrated business continuity testing, and third-party risk management. A strong cybersecurity training and awareness framework — which can reduce 90% of risks from human error — is equally central to that mission.TCE: How can organizations align multiple compliance frameworks like NIST, ISO 27001, RBI, MAS TRM, and GDPR without impacting operational agility?
Dr. Priyanka Sunder (PD): Throughout my career, I've emphasized secure code development, secure configurations, and hardening baselines as foundational drivers for safely adopting emerging technologies like AI, OT, and cloud. These form the pillars of Security by Design — driving operational excellence while keeping Information Security agile and enabling collective transformation.TCE: What are the most critical controls organizations should prioritize when securing cloud environments?
Dr. Priyanka Sunder (PD): In the shared responsibility model, organizations must prioritize mitigating vendor dependency, ensuring data localization for jurisdictional compliance, maintaining robust backup strategies, preventing security misconfigurations across containers and storage, and implementing strong key management practices. A phased migration approach, combined with proactively addressing these challenges, helps organizations strengthen cloud security while ensuring smoother transitions.TCE: What practical strategies can organizations adopt to build a stronger security culture?
Dr. Priyanka Sunder (PD): Strong leadership commitment is the foundation. When management consistently models secure behaviour — using multi-factor authentication, reporting suspicious activity — it signals that cybersecurity is a shared responsibility, not just an IT function. Training must be continuous, engaging, and role-tailored: bite-sized learning, phishing simulations, secure coding workshops, and fraud prevention sessions help employees internalize security practically. Appointing "security champions" within departments fosters collective influence, and employees should feel safe reporting mistakes without fear of blame. Together, leadership buy-in, engaging training, and employee empowerment transform staff into the organization's strongest line of defence.
TCE: What are the most common risk management gaps you observe across enterprises today?
Dr. Priyanka Sunder (PD): Drawing from five years in Big 4 IT Advisory and over a decade in financial services, the most critical gaps I've observed are: absence of robust GRC solutions for effective risk and compliance management, lack of integrated patch management for real-time visibility and timely remediation, and inadequate cybersecurity awareness among employees, vendors, and customers. Other recurring gaps include weak change management, cloud security, access controls, and endpoint security.TCE: How can cybersecurity leaders better communicate risk posture and investment priorities to executive stakeholders?
Dr. Priyanka Sunder (PD): Business leaders understand numbers and focus on the big picture, so it's imperative to speak their language. Present risk mitigations, GRC benefits, and cybersecurity impacts — financial losses, reputational damage, customer attrition, service disruptions — in quantifiable terms. Quantitative risk assessment models and GRC solutions can articulate the financial impact of control gaps, measurable ROIs, and periodic KRIs and KPIs, giving senior management clear assurance of cybersecurity's true value and supporting informed decision-making.TCE: What advice would you give aspiring women professionals building careers in GRC and cybersecurity?
Dr. Priyanka Sunder (PD): Turning challenges into opportunities has been a defining theme for me — overcoming bias in the early years, managing burnout during peak career phases, and achieving breakthroughs in recent years. These experiences reinforced my belief that growth can be both intrinsic and extrinsic, lateral and linear. Stepping outside comfort zones fosters cross-functional skill development and cultivates a strong One Team culture. Continuous learning has been central to my own journey, and I encourage women professionals to leverage that same mindset to build resilient, long-term careers in cybersecurity.Why Cybersecurity Still Fails at the Basics: Hackmanac CEO Sofia Scozzari

Here’s what she shared:
Sofia Scozzari Interview: Why Cybersecurity Must Move Beyond Technology
TCE: If you had to explain today’s cyber threat landscape using a real-world analogy (outside of technology), what would it be—and why?
Sofia Scozzari: I often describe the current cyber threat landscape as being like walking inside a beehive. If we haven’t been stung yet, we will be in the future. Threat actors constantly evolve, adapting to technological innovations, geopolitical shifts, and trending topics. They collaborate, specialize, and operate with “as-a-service” models that make offensive capabilities scalable and accessible. In contrast, defenders often act in isolation and hesitate to openly share incidents, which unintentionally preserves the attacker’s advantage. The result is a structural asymmetry between offense and defence, with offense taking advantage of collaboration. Even with the perfect defence strategy, we should assume exposure and breach are inevitable. The real strategic question is not "if," but rather how prepared we are when it happens. Just as biological systems develop resilience through collective immunity, cybersecurity requires structured information sharing and awareness to rebalance the attack–defence equation.TCE: You’ve spent years analyzing cyberattacks globally through Hackmanac. What is one common assumption about cyber threats that you believe is completely misunderstood?
Sofia Scozzari: In my opinion, the most misunderstood assumption is that cybersecurity is exclusively a technical issue, a subset of IT, often resulting in a fraction of a company’s IT budget. Today, cyberattacks can disrupt far more than technological systems, affecting core business assets, operations, reputation, and even endanger human lives, as in healthcare, connected medical devices, or electric vehicles. Cyber risk extends beyond technology and has evolved into a strategic business risk. Therefore, it should be governed accordingly.TCE: Looking back at your career journey, was there a single moment or decision that quietly changed your direction in cybersecurity? What did it teach you?
Sofia Scozzari: Looking back, the turning point in my career was my decision to leave traditional consulting and corporate roles to build my own company. This choice gave me the flexibility to determine how to intervene and effect change in the consideration and management of cybersecurity. After studying the problem more deeply, I realized that most cybersecurity decisions are mistakenly based on the volume of attacks (and not always the ones that really matter) rather than their impact. For this reason, we focus specifically on successful cyberattacks (an indication of where defences failed) and impacts (operational, financial, reputational consequences), providing executives and managers with precise, actionable strategic insight to guide cyber risk management.
TCE: In threat intelligence, patterns often repeat. Have you noticed any “cyber déjà vu” moments where organizations keep making the same mistakes despite better tools?
Sofia Scozzari: One recurring pattern in cybersecurity is the continued exploitation of known vulnerabilities. While it may be easy to interpret this as simple organizational negligence, the reality is that many companies operate highly complex environments built on legacy systems or mission-critical software certified only for specific versions. Updating these systems can introduce operational risk, making patch management far more challenging than it appears from the outside. The root cause, however, goes deeper: security by design is still not consistently embedded in the development process of systems, software, and applications. Instead, security is often treated as an additional layer applied after deployment rather than integrated from the outset. Moreover, unlike manufacturers of physical products, software vendors rarely face direct legal consequences when vulnerabilities in their products are exploited. The burden of mitigation largely falls on the end user, resulting in frequent preventable breaches.TCE: Cybersecurity is often seen as highly technical, yet much of it is about human behavior. What human factor do you think organizations still underestimate the most?
Sofia Scozzari: Cybersecurity is often framed as a technological issue, which naturally drives attention toward software, infrastructure, and technical controls, underestimating the human factor. Consequently, a significant portion of compromises still originate from human interaction: credential misuse, poor security hygiene, insider risk, or simple misjudgement under pressure. Attackers understand this very well, which is why phishing and social engineering remain effective entry points. On the other hand, cybersecurity awareness among collaborators, including employees, consultants, and suppliers— is often overlooked as a key component of an effective cybersecurity defence strategy.TCE: As a founder and leader, how do you personally stay ahead of constant change without getting overwhelmed by the speed of the cybersecurity industry?
Sofia Scozzari: I genuinely love cybersecurity because it evolves constantly: in this field, boredom is impossible. Continuous change forces you to think out of the box and to focus on the bigger picture rather than isolated details. In my role especially, understanding how technology, geopolitics, business dynamics, and human behaviour intersect is far more important than concentrating on a single technical dimension. I also don’t believe that stepping away, even temporarily, means falling behind permanently. Throughout my career, I’ve taken pauses — sometimes by choice, sometimes not — and each time I returned with broader perspective and stronger judgment. Soft skills such as adaptability, critical thinking, and strategic vision are just as important as technical expertise in cybersecurity field. Equally important is maintaining a healthy balance between professional and personal life. For this reason, at Hackmanac we have chosen to work fully remotely, enabling flexibility and trust within the team.Also Read: Top 50 Women Leaders in Cybersecurity to Watch in 2026
TCE: On International Women’s Day, many conversations focus on representation. From your experience, what truly helps women stay and grow in cybersecurity—not just enter the field?
Sofia Scozzari: I strongly believe that cybersecurity, as a profession, has no gender. The perception that it is male-dominated field is largely rooted in cultural conditioning. Many young women grow up internalizing the idea that they are less suited for technical subjects and are not always encouraged to pursue STEM paths. In reality, there are no inherent barriers. I personally know several extraordinary women in cybersecurity who bring passion, creativity, expertise, and talent to the field. Three factors truly help women grow in cybersecurity: early encouragement, inclusive environments (not only related to gender), and a strong focus on competence. First, early encouragement is important for students to choose their academic and future career paths. They should consider cybersecurity because it is a fast-growing industry with huge global demand, a meaningful impact, and strong long-term career prospects. Second, we must highlight the diversity of roles within cybersecurity. The field is not limited to highly technical positions. Legal, compliance, risk management, communications, strategy, and business roles are also essential. This makes the industry accessible to professionals from varied backgrounds who may wish to pursue a change in their careers. Finally, my advice for women already in the field is simple: focus on competence and results. Although challenges and biases may exist, sustained professionalism, expertise, and consistency build credibility over time. Cybersecurity needs diversity, not just for representation, but because complex global challenges require diverse perspectives.TCE: The theme of our initiative is “Give to Gain.” What is one piece of knowledge or opportunity you received in your career that you now consciously pass forward?
Sofia Scozzari: One of the most valuable gifts I received in my career was trust. I was just a curious young girl looking into computers and learning how to assemble them. I was supported and encouraged to pursue that curiosity. Much of what I learned came more from hands-on experience rather than from formal education. I was fortunate to study in inclusive environments focused on preparing capable IT professionals, and equally fortunate to move across diverse roles — from system administrator to IT consultant, project manager, presales, and cybersecurity manager. Each transition expanded my perspective and forced me out of my comfort zone. What I consciously pass forward is that same encouragement: do not fear stepping beyond what feels familiar. Growth rarely happens inside comfort. I encourage professionals — especially younger ones — to focus less on self-doubt and more on how they can create value in any context, leveraging both technical expertise and soft skills, expertise and passion.TCE: If you could redesign how organizations approach cybersecurity from scratch—without legacy systems or old processes—what would you do differently first?
Sofia Scozzari: If I could redesign how organizations approach cybersecurity from scratch, I would start by rethinking their decision-making structures. Currently, cybersecurity is often evaluated based on compliance checklists, budget constraints, or emergencies. Rarely is it fully integrated into strategic planning, performance metrics, or executive accountability. I would embed cyber risk directly into core business KPIs, forcing a reevaluation of budget allocation. This would enable security to influence product design, supply chain selection, partnerships, and investment decisions. Finally, I would ensure that security intelligence is continuously translated into board-level language. Leaders who don't usually receive technical alerts should at least receive strategic insights related to business exposure and impact to fully understand and manage their company's specific threat scenario.Women Shaping the Future of Mobile Cybersecurity in a Digital-First Era

Saloni Nanwate, AVP – Security Engineering, Protectt.ai Labs Pvt Ltd
India’s digital economy now lives on the smartphone. Banking, investing, healthcare consultations, shopping, even government services all sit inside mobile applications that people use dozens of times a day. For businesses this shift has unlocked enormous reach and convenience. It has also created a new reality for cybersecurity. Attackers are no longer trying only to break into enterprise networks or data centres. Increasingly they are going after the mobile applications where transactions actually happen. That is where money moves, identities are verified, and sensitive customer data lives. For industries such as banking, fintech and digital commerce, the mobile application has quietly become the most exposed point in the entire technology stack.The Growing Cyber Risk in Mobile First Platforms
Mobile apps run on devices that companies do not control. Each user’s phone can have a different operating system version, different security posture and sometimes even malicious software already present. From a security perspective, this makes the mobile environment unpredictable. Cybercriminals are taking advantage of this reality. Instead of attacking infrastructure directly, they manipulate how apps behave once they are running on the device. Techniques such as reverse engineering, runtime tampering, session hijacking and overlay attacks allow attackers to interfere with legitimate app behaviour without triggering traditional security systems. Many organisations still rely heavily on perimeter defences that protect networks and backend infrastructure. But once an application is operating on a user’s device, that perimeter no longer exists. This is why mobile security strategies are gradually shifting toward protection mechanisms that are embedded directly within the application itself. Technologies such as runtime application self protection are becoming essential in this model. By monitoring application behaviour during execution, these systems allow apps to detect tampering, malicious tools or suspicious environments and respond immediately. In simple terms, the app becomes capable of defending itself while it is running.Women Leaders Are Helping Redefine Cybersecurity Thinking
While the cyber threat landscape is evolving quickly, the cybersecurity industry itself is also changing. One of the most encouraging shifts has been the growing presence of women in leadership roles across cybersecurity and digital risk management. Cybersecurity is often viewed purely as a technical discipline. In reality it is equally about strategy, foresight and understanding human behaviour. Women leaders are increasingly shaping how organisations think about these dimensions of security. In the context of mobile platforms this perspective becomes particularly important. Securing digital ecosystems is not just about deploying tools. It requires understanding how users interact with applications, how fraudsters exploit human behaviour and how security can be built into digital experiences without frustrating legitimate users. Across the industry many women leaders are pushing organisations to adopt a security by design mindset. Instead of treating security as something that is added later, they advocate integrating protection throughout the application lifecycle. Security considerations begin during development, continue through testing and remain active even after the application reaches users. This approach reflects a broader shift in cybersecurity thinking. Prevention is no longer enough. Detection and response must happen continuously and in real time.Building a Stronger Cybersecurity Ecosystem
Another area where women leaders are making a significant impact is collaboration. Cyber threats rarely respect industry boundaries. Attackers share tools and techniques across regions and sectors, which means defenders must do the same. Many women leaders are actively encouraging stronger collaboration between enterprises, security researchers, regulators and technology providers. Knowledge sharing and cross industry dialogue are becoming increasingly important in identifying emerging threats before they spread widely. At the same time the industry faces a growing shortage of cybersecurity professionals. Encouraging more women to enter the field is not only about diversity. It is about strengthening the talent pool needed to defend an increasingly complex digital ecosystem. As India continues its transition toward a mobile driven digital economy, trust will remain the foundation of every digital interaction. Every secure transaction, every protected user session and every resilient mobile application contributes to maintaining that trust. It’s a moment to truly appreciate and recognise the incredible women shaping the future of cybersecurity. Through leadership, innovation and collaboration they are strengthening the defenses that protect millions of digital users every day. The next phase of digital growth will depend not only on new technologies but also on the people guiding how those technologies are secured. Women leaders are playing a vital role in ensuring that the mobile ecosystems powering today’s digital economy remain safe, resilient and trustworthy.Android 17 Leaks Reveal Major Redesign, AI Features, and Privacy Upgrades
Android 17 beta is here. Here’s what is confirmed so far, what leaks suggest, and which rumored features may arrive later in 2026.
The post Android 17 Leaks Reveal Major Redesign, AI Features, and Privacy Upgrades appeared first on TechRepublic.
The Privacy Problem With Meta’s Ray-Ban Smart Glasses
This episode discusses Meta Ray-Ban Smart Glasses, which blend a camera, microphone, AI features, and social media integration into sunglasses that look like normal fashion eyewear, raising major privacy concerns. It highlights reports that footage captured by the glasses may be reviewed by human contractors to help train Meta’s AI systems, and notes critics’ concerns […]
The post The Privacy Problem With Meta’s Ray-Ban Smart Glasses appeared first on Shared Security Podcast.
The post The Privacy Problem With Meta’s Ray-Ban Smart Glasses appeared first on Security Boulevard.
Cyber Risk Management Starts with Understanding the Business: CISO Hannah Suarez Explains Why

Cyber Risk Management Insights from CISO Hannah Suarez
TCE: You have led cybersecurity and compliance programs across multiple industries, including telecommunications, aviation, and software startups. How does the approach to cyber risk management differ between fast-growing startups and more established enterprises?
Hannah: One of the key, obvious, differentiators is the approach to risk. Startups willing to absorb or delay risk treatment in favor of risk acceptance to grow is one example. Also, even if this is the approach for a startup that has to show itself as secure to enterprise, you can still wrap it in an ISO framework and have it in the ISMS so there is an actual approach.TCE: With organizations increasingly adopting cloud-first strategies, what are the most common cloud security gaps you observe today, and how can CISOs address them proactively?
Hannah: First is to differentiate exactly what model is this when it comes to ownership and operations. For example, you onboard a new application which is on cloud (such as Salesforce) and from there determine if there is compliance responsibility by the operator or if it is entirely on the company. Or, we could be referencing to operating a software that is managed by an operator on cloud (AWS, GCP, Azure). Or we could be talking about private cloud hosted instead. From there on, the layers become complex as you try to determine responsibility and ownership. Which components are going to be shared responsibility to operate, which components are not, and so on. Therefore, I find that a lot of time gets invested in trying to understand the solution first and why the business is heading into that direction by talking to the relevant stakeholders. I could really go on in more detail about cloud security in third party management, but the overall basis is who owns and who is responsible.
TCE: You have worked extensively with frameworks such as ISO, NIST, CIS, SOC, and SOX. How should organizations prioritize these frameworks without creating compliance fatigue?
Hannah: The problem is being framework-only. For example, why would one cite a NIST guideline from their cybersecurity framework if this isn’t relevant in the ISMS? So the challenge is to try to come back to the business first and then from there determine what should be prioritized. Coming back to the business involves applying risk management, since you also have to understand the responsibility of implementing and owning the risk. It doesn’t mean that you are limited to just one framework only – i.e only follow ISO, or only follow NIST, etc. I did an exercise of going through multiple guidelines and frameworks to see what the information is on supply chain management lifecycle on a holistic view, then went into the detailed for specific components of it (onboarding, offloading, etc) that is more suitable to the current business process.TCE: From your experience presenting to boards and executive teams, how can cybersecurity leaders better translate technical risks into business impact?
Hannah: You differentiate who is responsible, is it the business owner, the system owner, the risk owner, the contract owner. And adjust.TCE: Having worked across diverse global markets, how do regional regulatory environments influence cybersecurity strategy and risk governance?
Hannah: It is dependent on recognising ownership of what applicable laws and regulations apply within the entire data flow or process flow. Therefore I start on the contractual component and work my way to how it is impacting the ISMS and then applying the ISMS.TCE: As cyber threats continue to evolve, which emerging risk areas—such as AI-driven attacks or supply chain vulnerabilities—do you believe organizations should prepare for most urgently?
Hannah: Something that is a thorn for organizations that has undergone massive digital transformation is supply chain vulnerabilities. Addressing this is going to be at the core of addressing the more specialized topics, like AI-driven attacks. For example, you onboard new suppliers for a process that is required to use and store highly regulated commercial data, or highly sensitive data (such as, biometrics like voice analysis). This new system then announces their intention to use data for their AI models. What next?TCE: You have a strong background in building security maturity for organizations. What are the first three practical steps companies should take to strengthen their security posture in 2026?
Hannah: Have executive management involvement across the business. Understand the business and why it is going in a certain direction like my answer previously on frameworks. Understand the components (vendors, suppliers, operators) that make up the business (like my answer previously on cloud).TCE: As someone with an entrepreneurial mindset and experience across startups, how can cybersecurity enable business growth rather than being seen only as a compliance requirement?
Hannah: For startups, one of the issues that they face is building trust with enterprises. And compliance programs (be it ISO 27001, data protection management programs, etc) are important to establish this. Not just for the objective third party view from an auditor, but also for the day to day running of the business. A lot of the enablement, without things devolving into some compliance checkbox, is for the startup to learn more about risk management – not just thje TARA framework (Transfer, Accept, Reduce, Avoid) but to also get to ways that they don’t seek permission to do risk analysis, all the time. For this, it is risk exploitation which is to be able to seize opportunities first, then working on the TARA method later. It is more like the saying “ask for forgiveness later” in which the later part is to conduct the risk analysis later. Or the other way of saying is to accept first, then analyse later.TCE: On the occasion of International Women’s Day, what key actions can organizations take to create more inclusive and supportive environments for women in cybersecurity?
Hannah: Community is very important. As someone who has moved in several countries (with the UAE as my seventh), one of the things that you do is to find ways to try to ground yourself in a new community. This was very much evident in the UAE through initiatives for women in cyber security, and also being in other groups for women in technology that I am a part of for the wider GCC area. Organizations can choose to take part in more of these initiatives, or at least encourage and empower their employees to participate.TCE: What advice would you offer to young women aspiring to build leadership careers in cybersecurity, particularly in areas like risk management and compliance?
Hannah: In the beginning, I was working as a system administrator for a software company. We had customers that needed to configure specific components to make it compliant (such as, using FIPS cryptographic modules). In the end, I ended up learning more about these frameworks. When I pivoted more towards auditing and implementing ISMS for enterprises and organizations, the focus was less on the technical and being super specialized in it, and more on the business side and finding ways to get the business to reach and maintain compliance. Having background in the two, I find, has been a valuable perspective to work in this area.Conclusion
Hannah Suarez’s perspective is a reminder that cyber risk management is not just about frameworks or compliance checklists. At its core, it is about understanding how a business operates, who owns the risk, and how security decisions affect the organization as a whole. From navigating cloud security responsibilities to addressing growing supply chain vulnerabilities, Hannah emphasizes that security leaders must first understand the direction of the business before building controls around it. Only then can cybersecurity move beyond enforcement and become part of how organizations operate and grow. Her journey also highlights the importance of community and mentorship, particularly for women in cybersecurity who are building leadership roles across the industry. As organizations continue to evolve digitally, the challenge for CISOs will be balancing innovation with responsible cyber risk management. As Hannah suggests throughout this conversation, the starting point remains simple: understand the business, understand the risk, and build security programs that support both.Women in Cybersecurity Reveal the Skills That Built Their Confidence

As International Women’s Day is marked on 8 March, conversations around representation, leadership, and opportunity across industries take renewed focus. In cybersecurity — a field that continues to evolve at remarkable speed — women in cybersecurity are playing a growing role in strengthening digital resilience, shaping security strategies, and mentoring the next generation of professionals.
Their journeys often involve navigating complex challenges while continuously adapting to new technologies, emerging threats, and changing security landscapes.
As part of its Women in Cybersecurity initiative, The Cyber Express asked cybersecurity leaders a simple but important question:
“Which skill or mindset has played the biggest role in building your confidence and growth in cybersecurity?”
From curiosity and continuous learning to calm decision-making and structured problem-solving, their responses highlight the perspectives that have helped them grow and succeed in the cybersecurity industry.
Here’s what they shared.
Women’s Day 2026: Voices of Women in Cybersecurity
Carmen Marsh
President & CEO at United Cybersecurity Alliance (Europe, US, Middle East & Japan) Curiosity. Disciplined, courageous curiosity. Cybersecurity is not a static profession. It is an evolving battlefield of technology, psychology, geopolitics, and human behavior. The moment you believe you know enough, you become obsolete. I have always believed in expanding beyond what is required of me. Not just mastering the tools of today, but understanding the patterns shaping tomorrow. Reading outside your lane. Engaging with peers. Asking uncomfortable questions. Challenging assumptions. Just as important is stepping out of isolation. Cybersecurity can feel technical and solitary, but the community is extraordinary. When you connect with mentors, peers, and diverse voices, you realize you are not alone in navigating complexity. That shared learning builds both competence and confidence. Growth in cybersecurity is not about ego. It is about intellectual humility and relentless evolution. That mindset changes everything.Lisa Fitzgerald
Partner, Norton Rose Fulbright Staying ‘cyber-calm’ is critical. Cyber-attacks are generally times of crisis for organisations. As a legal adviser, our role is to ensure certain steps are taken in a timely, methodical and strategic manner. It can seem like a clinical role – ensuring the information needed is gathered, mitigation obligations are in place and notification deadlines are met – but interacting with various stakeholders who are under great stress requires a very human and calm approach.Hannah Suarez
CISO, Loyalty Status Co I find that knowing when to specialize and when to generalize is a great asset. Specialization enables you to build and explore new and deeper threads of knowledge in a given area, and generalization allows you to build those threads into something more and to connect these threads into other areas. I don't believe in the dichotomy that you can only be one or the other.Dr Sheeba Armoogum
Associate Professor in Cybersecurity, University of Mauritius My personal focus has been on ongoing learning. I make sure to stay up to date daily on new cybercrime trends, threat intelligence, and policy changes. Since cybersecurity evolves quickly, keeping informed helps me stay competent and confident.Sofia Scozzari
CEO & Founder, Hackmanac Curiosity has always been my primary driver and the strongest catalyst for my growth. Another key mindset for me has been embracing constant innovation, anticipating change, rather than just react to it. Finally, I strongly believe that dedicating time to education and awareness is essential. Cybersecurity is often perceived as overly technical and complex, confined to specialists. In reality, however, it is also a business issue. Managers and C-level executives make strategic decisions about budgets and asset protection. Therefore, it is crucial that they understand the real impact of cyber risk and threats on their organization.Bonnie Butlin
Co-Founder and Executive Director, Security Partners' Forum I did not come into security and cybersecurity as a technical or cybersecurity expert, and had to accept that understanding and addressing cybersecurity in my work is unavoidable. Over time, understanding cybersecurity, particularly as the field continues to develop and mature, has become a true asset for my work. It allows me to enhance my work with additional perspectives and understanding, for example, on threats and operations in the cybersecurity space, which directly or indirectly cross over into other areas of security and society.Dr. Priyanka Sunder
CHRIO and Co-founder Secure Mojo Personally, continuous learning and moving out of your comfort zone has benefitted me in building my confidence, credibility, professional brand and network. It has also helped me solve real life problems and align my career aspirations with my IKIGAI – my purpose or calling. I don’t look as growth as linear or hierarchical for me growth is measured in terms of knowledge across multiple domains (related or un-related), improving soft skills and solving deep-seated problems be it people, process, technology or data security. Every aspect of growth be it intrinsic or extrinsic, linear or vertical, regional role or bigger portfolio is a way to showcase your strengths and bring value additions to your team and organisation and communities at large. Follow you calling, make your career your calling instead of trading time and health for money.Sabitha Sriram
Security and Risk Consultant I think working for passion, strategic thinking, learning orientation and soft skills help a lot to excel in this domain.Bree Kagwe
Ethical Hacker | Simplifying Cybersecurity For Women In Offensive Security Structured problem-solving. Instead of getting overwhelmed by a big challenge, I focus on the next logical step. Being okay with not knowing everything, as long as you know how to find the next step, has been the biggest boost to my confidence.Top 50 Women Leaders in Cybersecurity to Watch in 2026

Women in Cybersecurity: Progress and Persistent Challenges
Within cybersecurity, women continue to expand their presence in a field that has historically been male dominated. According to the latest available data, women currently make up about 22% of the global cybersecurity workforce, a significant increase from just 11% in 2017. Today, one in four cybersecurity professionals is a woman, and projections suggest that by 2031, women could represent nearly one-third of the cybersecurity workforce. Despite this progress, challenges remain. In the United States, women still hold less than 20% of cybersecurity roles, and a gender pay gap of around 5% persists in the sector. Career growth also continues to present obstacles, with nearly half of women in cybersecurity reporting challenges in professional advancement, while almost one-third say they have experienced workplace discrimination at some point in their careers. Even so, women across the cybersecurity ecosystem are making remarkable contributions — from leading security operations and shaping national cyber policies to advancing threat intelligence, digital forensics, and cyber resilience strategies. Their work is not only protecting organizations and critical infrastructure but also inspiring the next generation of security professionals. Keeping this in mind, The Cyber Express’ “Top 50 Women Leaders in Cybersecurity to Watch in 2026” recognizes professionals whose leadership, expertise, and impact are helping redefine the cybersecurity landscape. Their journeys reflect the spirit of International Women’s Day on 8 March — demonstrating that when we support and empower women in cybersecurity, the entire digital ecosystem stands to gain.Top 50 Women Leader in Cybersecurity | IWD Special by The Cyber Express
| Name | Designation | Company Name |
| Celia Mantshiyane | Group Chief Information Security Officer | FirstRand |
| Radhika Bajpai | CISO | Russell Investments |
| Holly Foxcroft | Cyber Security Business Partner - BISO | OneAdvanced |
| Dr Sheeba Armoogum | Associate Professor in Cybersecurity | University of Mauritius |
| Irene Corpuz | Founding Partner, Head of Governance & Communications | Women in Cyber Security Middle East |
| Patricia "Patty" Voight | Executive Managing Director; CISO and Tech Risk Management | Webster Bank |
| Alya Al Marzooqi | Group Digital Risk Management and Compliance Manager | ADNOC Group |
| Sakshi Porwal | Global Chief Information Security Officer & Cybersecurity Consulting Practice Head | Compunnel Inc. |
| Rona Michele Spiegel, CISSP | Senior Manager, Security and Trust, Mergers and Acquisitions | Autodesk |
| Dr Priyanka Sunder | Co-Founder & Chief Human Risk Intelligence Officer | Secure Mojo |
| Lauren Dana Rosenblatt | Vice President, Chief Information Security Officer (CISO) | PSEG |
| Sheeba Sultan Hasnain | Chairwoman & CIO | SENTIENTE |
| Dr. Meetali Sharma | Director - Risk, Compliance and Information Security | SDG Corporation |
| Kylie Watson | Head of Cyber Security, ANZ/ASEAN/Japan/India/GC/Middle East/Africa | DXC Technology |
| Catherine Rowe | Chief Information Security Officer | Reserve Bank of Australia |
| Maryam Bechtel | General Manager, Chief Information Security Officer (CISO) | TAL Australia |
| Sofia Scozzari | CEO (Chief Executive Officer) and Founder | Hackmanac |
| Archana Venugopal | Senior Vice President & Chief Information Secuirty Officer National aCommodity& Derivates Exchange | National Commodity & Derivative Exchange Of India Limited |
| Shivani Arni | Enterprise CISO | Mahindra Group |
| Cindy (Monceaux) Hoots | Chief Digital Officer & CIO | AstraZeneca |
| Jae Evans | EVP, Oracle Cloud Infrastructure and Global CIO | Oracle |
| Sheila Jordan | Chief Digital Technology Officer | Honeywell |
| Maria Demaree | Senior Vice President, Enterprise Business and Digital Transformation & CIO | Lockheed Martin |
| Heide Young | Manager Cyber Strategy & Engagement | NEOM |
| Eman Al Awadhi | Vice President – Network and Cyber Security | Expo City Dubai |
| Julia Dudenko | Group CISO | Haniel |
| Anne Neuberger | Deputy National Security Advisor, Cyber & Emerging Tech | National Security Council, The White House |
| Kris Lovejoy | Global Head of Strategy | Kyndryl |
| Ramya Ganesh | Cybersecurity XDR Leader | Cisco |
| Jane Teh | Founder and CEO | VortiQ[x] |
| Nasrin Rezai | SVP, Chief Information Security Officer | Verizon |
| Laura Deaner | Chief Information Security Officer | The Depository Trust & Clearing Corporation (DTCC) |
| Mignona Coté | SVP Chief Information Security Officer | Infor |
| Noopur Davis | Global CISO. Chief Product Privacy Officer. Corporate EVP. | Comcast |
| Teresa Zielinski | Vice President, CISO | GE Vernova |
| Andrea Abell | Chief Information Security Officer | Eli Lilly and Company |
| Deneen DeFiore | Vice President & Chief Information Security Officer | United Airlines |
| Elizabeth Joyce | EVP & Global CISO | State Street |
| Mary Rose Martinez | Chief Information Security Officer and Vice President of Infrastructure | Marathon Petroleum Corporation |
| Marnie (Huss) Wilking | VP Chief Security Officer | Booking.com |
| Hannah Suarez 🇵🇸 | CISO | Loyalty Status Co |
| Annie (Anne) Haggar | Deputy Chief of Staff | Australian Government |
| Sujata Misra | GM - Network Infra and Security Leader | Brigade Group |
| Bonnie Butlin | Co-Founder and Executive Director | Security Partners' Forum |
| Gurdeep Kaur | Chief Operating Officer | Suraksha Catalyst |
| Vandana Verma | President | InfoSec Girls |
| Mansi Thapar | Global Head – Cyber Security & Infra | Apollo Tyres |
| Rosalia Hajek | CISO | Topgolf Callaway Brands |
| Carmen Marsh | President & CEO | United Cybersecurity Alliance (Europe, US, Middle East & Japan) |
| Lisa Fitzgerald | Partner | Norton Rose Fulbright |
Okta vs Microsoft Entra ID: Which Enterprise SSO Platform Is Better?
Compare Okta vs Microsoft Entra ID for enterprise SSO. Learn differences in authentication, security, and identity management for SaaS and enterprise platforms.
The post Okta vs Microsoft Entra ID: Which Enterprise SSO Platform Is Better? appeared first on Security Boulevard.
With developer verification, Google's Apple envy threatens to dismantle Android's open legacy
It's been nearly 20 years since Google revealed Android, which the company described as the first "truly open" mobile operating system, setting Google-powered phones apart from the iPhone's aggressively managed experience. Over time, though, Android has become more aligned with Apple's approach. For the moment, users still have the final say in what software runs on their increasingly locked-down smartphones. Later this year, though, Google plans to seriously curtail that freedom in the name of security.
In the coming weeks, Google will officially debut Android developer verification, which will require app makers outside the Play Store to register with their real names and pay a fee to Google. Failure to do so will block their apps from installation (sometimes called sideloading) on virtually all Android devices. Google says this is a necessary evolution of the platform's security model, but upending the status quo could push developers away from Android and risk the privacy of those that remain.
This might make your phone a little safer, sure, but it won't stop people from getting scammed. At the same time, it could rob the Android ecosystem of what made it special in the first place.
© Aurich Lawson | Getty Images
New AirSnitch attack bypasses Wi-Fi encryption in homes, offices, and enterprises
It’s hard to overstate the role that Wi-Fi plays in virtually every facet of life. The organization that shepherds the wireless protocol says that more than 48 billion Wi-Fi-enabled devices have shipped since it debuted in the late 1990s. One estimate pegs the number of individual users at 6 billion, roughly 70 percent of the world’s population.
Despite the dependence and the immeasurable amount of sensitive data flowing through Wi-Fi transmissions, the history of the protocol has been littered with security landmines stemming both from the inherited confidentiality weaknesses of its networking predecessor, Ethernet (it was once possible for anyone on a network to read and modify the traffic sent to anyone else), and the ability for anyone nearby to receive the radio signals Wi-Fi relies on.
Ghost in the machine
In the early days, public Wi-Fi networks often resembled the Wild West, where ARP spoofing attacks that allowed renegade users to read other users' traffic were common. The solution was to build cryptographic protections that prevented nearby parties—whether an authorized user on the network or someone near the AP (access point)—from reading or tampering with the traffic of any other user.


© Getty Image | BlackJack3D
Firefox is giving users the AI off switch
Some software providers have decided to lead by example and offer users a choice about the Artificial Intelligence (AI) features built into their products.
The latest example is Mozilla, which now offers users a one-click option to disable generative AI features in the Firefox browser.
Audiences are divided about the use of AI, or as Mozilla put it on their blog:
“AI is changing the web, and people want very different things from it. We’ve heard from many who want nothing to do with AI. We’ve also heard from others who want AI tools that are genuinely useful. Listening to our community, alongside our ongoing commitment to offer choice, led us to build AI controls.”
Mozilla is adding an AI Controls area to Firefox settings that centralizes the management of all generative AI features. This consists mainly of a master switch, “Block AI enhancements,” which lets users effectively run Firefox “without AI.” It blocks existing and future generative AI features and hides pop‑ups or prompts advertising them.
Once you set your AI preferences in Firefox, they stay in place across updates. You can also change them whenever you want.
Starting with Firefox 148, which rolls out on February 24, you’ll find a new AI controls section within the desktop browser settings.
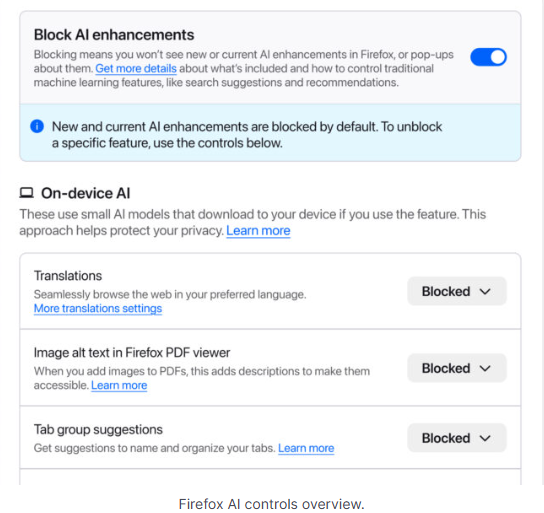
You can turn everything off with one click or take a more granular approach. At launch, these features can be controlled individually:
- Translations, which help you browse the web in your preferred language.
- Alt text in PDFs, which add accessibility descriptions to images in PDF pages.
- AI-enhanced tab grouping, which suggests related tabs and group names.
- Link previews, which show key points before you open a link.
- An AI chatbot in the sidebar, which lets you use your chosen chatbot as you browse, including options like Anthropic Claude, ChatGPT, Microsoft Copilot, Google Gemini and Le Chat Mistral.
We applaud this move to give more control to the users. Other companies have done the same, including Mozilla’s competitor DuckDuckGo, which made AI optional after putting the decision to a user vote. Earlier, browser developer Vivaldi took a stand against incorporating AI altogether.
Open-source email service Tuta also decided not to integrate AI features. After only 3% of Tuta users requested them, Tuta removed an AI copilot from its development roadmap.
Even Microsoft seems to have recoiled from pushing AI to everyone, although so far it has focused on walking back defaults and tightening per‑feature controls rather than offering a single, global off switch.
Choices
Many people are happy to use AI features, and as long as you’re aware of the risks and the pitfalls, that’s fine. But pushing these features on users who don’t want them is likely to backfire on software publishers.
Which is only right. After all, you’re paying the bill, so you should have a choice. Before installing a new browser, inform yourself not only about its privacy policy, but also about what control you’ll have over AI features.
Looking at recent voting results, I think it’s safe to say that in the AI gold rush, the real premium feature isn’t a chatbot button—it’s the off switch.
We don’t just report on privacy—we offer you the option to use it.
Privacy risks should never spread beyond a headline. Keep your online privacy yours by using Malwarebytes Privacy VPN.
Meta confirms it’s working on premium subscription for its apps
Meta plans to test exclusive features that will be incorporated in paid versions of Facebook, Instagram, and WhatsApp. It confirmed these plans to TechCrunch.
But these plans are not to be confused with the ad-free subscription options that Meta introduced for Facebook and Instagram in the EU, the European Economic Area, and Switzerland in late 2023 and framed as a way to comply with General Data Protection Regulation (GDPR) and Digital Markets Act requirements.
From November 2023, users in those regions could either keep using the services for free with personalized ads or pay a monthly fee for an ad‑free experience. European rules require Meta to get users’ consent in order to show them targeted ads, so this was an obvious attempt to recoup advertising revenue when users declined to give that consent.
This year, users in the UK were given the same choice: use Meta’s products for free or subscribe to use them without ads. But only grudgingly, judging by the tone in the offer… “As part of laws in your region, you have a choice.”
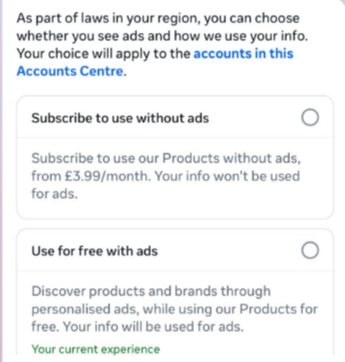
That ad-free option, however, is not what Meta is talking about now.
The newly announced plans are not about ads, and they are also separate from Meta Verified, which starts at around $15 a month and focuses on creators and businesses, offering a verification badge, better support, and anti‑impersonation protection.
Instead, these new subscriptions are likely to focus on additional features—more control over how users share and connect, and possibly tools such as expanded AI capabilities, unlimited audience lists, seeing who you follow that doesn’t follow you back, or viewing stories without the poster knowing it was you.
These examples are unconfirmed. All we know for sure is that Meta plans to test new paid features to see which ones users are willing to pay for and how much they can charge.
Meta has said these features will focus on productivity, creativity, and expanded AI.
My opinion
Unfortunately, this feels like another refusal to listen.
Most of us aren’t asking for more AI in our feeds. We’re asking for a basic sense of control: control over who sees us, what’s tracked about us, and how our data is used to feed an algorithm designed to keep us scrolling.
Users shouldn’t have to choose between being mined for behavioral data or paying a monthly fee just to be left alone. The message baked into “pay or be profiled” is that privacy is now a luxury good, not a default right. But while regulators keep saying the model is unlawful, the experience on the ground still nudges people toward the path of least resistance: accept the tracking and move on.
Even then, this level of choice is only available to users in Europe.
Why not offer the same option to users in the US? Or will it take stronger US privacy regulation to make that happen?
We don’t just report on threats – we help protect your social media
Cybersecurity risks should never spread beyond a headline. Protect your social media accounts by using Malwarebytes Identity Theft Protection.
[Correction] Gmail can read your emails and attachments to power “smart features”
Update November 22. We’ve updated this article after realising we contributed to a perfect storm of misunderstanding around a recent change in the wording and placement of Gmail’s smart features. The settings themselves aren’t new, but the way Google recently rewrote and surfaced them led a lot of people (including us) to believe Gmail content might be used to train Google’s AI models, and that users were being opted in automatically. After taking a closer look at Google’s documentation and reviewing other reporting, that doesn’t appear to be the case.
Gmail does scan email content to power its own “smart features,” such as spam filtering, categorisation, and writing suggestions. But this is part of how Gmail normally works and isn’t the same as training Google’s generative AI models. Google also maintains that these feature settings are opt-in rather than opt-out, although users’ experiences seem to vary depending on when and how the new wording appeared.
It’s easy to see where the confusion came from. Google’s updated language around “smart features” is vague, and the term “smart” often implies AI—especially at a time when Gemini is being integrated into other parts of Google’s products. When the new wording started appearing for some users without much explanation, many assumed it signalled a broader shift. It’s also come around the same time as a proposed class-action lawsuit in the state of California, which, according to Bloomberg, alleges that Google gave Gemini AI access to Gmail, Chat, and Meet without proper user consent.
We’ve revised this article to reflect what we can confirm from Google’s documentation, as it’s always been our aim to give readers accurate, helpful guidance.
Google has updated some Gmail settings around how its “smart features” work, which control how Gmail analyses your messages to power built-in functions.
According to reports we’ve seen, Google has started automatically opting users in to allow Gmail to access all private messages and attachments for its smart features. This means your emails are analyzed to improve your experience with Chat, Meet, Drive, Email and Calendar products. However, some users are now reporting that these settings are switched on by default instead of asking for explicit opt-in—although Google’s help page states that users are opted-out for default.
How to check your settings
Opting in or out requires you to change settings in two places, so I’ve tried to make it as easy to follow as possible. Feel free to let me know in the comments if I missed anything.
To fully opt out, you must turn off Gmail’s smart features in two separate locations in your settings. Don’t miss one, or AI training may continue.
Step 1: Turn off Smart features in Gmail, Chat, and Meet settings
- Open Gmail on your desktop or mobile app.
- Click the gear icon → See all settings (desktop) or Menu → Settings (mobile).
- Find the section called smart features in Gmail, Chat, and Meet. You’ll need to scroll down quite a bit.
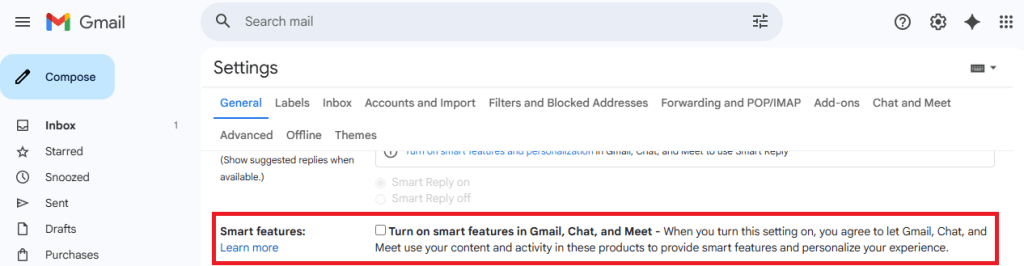
- Uncheck this option.
- Scroll down and hit Save changes if on desktop.
Step 2: Turn off Google Workspace smart features
- Still in Settings, locate Google Workspace smart features.
- Click on Manage Workspace smart feature settings.
- You’ll see two options: Smart features in Google Workspace and Smart features in other Google products.
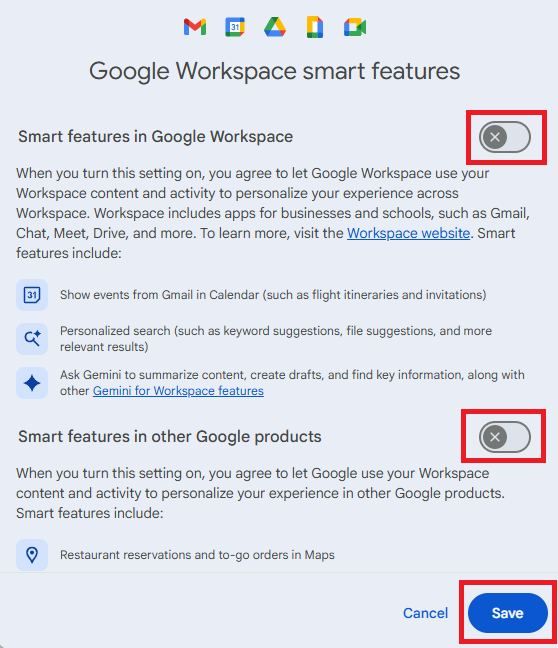
- Toggle both off.
- Save again in this screen.
Step 3: Verify if both are off
- Make sure both toggles remain off.
- Refresh your Gmail app or sign out and back in to confirm changes.
We don’t just report on privacy—we offer you the option to use it.
Privacy risks should never spread beyond a headline. Keep your online privacy yours by using Malwarebytes Privacy VPN.
iOS and Android juice jacking defenses have been trivial to bypass for years
About a decade ago, Apple and Google started updating iOS and Android, respectively, to make them less susceptible to “juice jacking,” a form of attack that could surreptitiously steal data or execute malicious code when users plug their phones into special-purpose charging hardware. Now, researchers are revealing that, for years, the mitigations have suffered from a fundamental defect that has made them trivial to bypass.
“Juice jacking” was coined in a 2011 article on KrebsOnSecurity detailing an attack demonstrated at a Defcon security conference at the time. Juice jacking works by equipping a charger with hidden hardware that can access files and other internal resources of phones, in much the same way that a computer can when a user connects it to the phone.
An attacker would then make the chargers available in airports, shopping malls, or other public venues for use by people looking to recharge depleted batteries. While the charger was ostensibly only providing electricity to the phone, it was also secretly downloading files or running malicious code on the device behind the scenes. Starting in 2012, both Apple and Google tried to mitigate the threat by requiring users to click a confirmation button on their phones before a computer—or a computer masquerading as a charger—could access files or execute code on the phone.


© Aurich Lawson | Getty Images