The post Cybersecurity Pros Sentenced for Running ALPHV BlackCat Ransomware appeared first on Daily CyberSecurity.
Visualização de leitura
IOCTA 2026 Report Warns of Rising AI-Driven Cybercrime and Dark Web Threats

IOCTA 2026 Report Maps Evolving Cyber Threat Landscape
The IOCTA 2026 report serves as a roadmap for understanding emerging cyber threats, covering areas such as online fraud, ransomware attacks, and child exploitation networks. Edvardas Šileris, Head of the European Cybercrime Centre at Europol, emphasized that the report is intended to help law enforcement agencies respond effectively to these evolving risks. He noted that as cybercriminals continue to exploit new technologies, strengthening capabilities and improving collaboration will be essential to protect citizens and critical infrastructure.Dark Web Fragmentation and Cryptocurrencies Fuel Crime
A key finding in the IOCTA 2026 report is the continued role of the dark web as a central hub for cybercriminal activity. Despite ongoing crackdowns, marketplaces and forums remain active, with criminals frequently shifting platforms to avoid detection. The report highlights how fragmentation and specialization across these platforms make investigations more difficult. Encrypted messaging services and anonymized networks are increasingly connecting surface and dark web environments, reducing the visibility of criminal operations. Cryptocurrencies also play a significant role, according to the IOCTA 2026 report. Privacy-focused coins and offshore exchanges are widely used to launder ransomware payments, making financial tracking more challenging. The report also points to a growing trend of younger individuals becoming involved in cryptocurrency-related activities, sometimes without understanding the legal risks.AI-Driven Fraud Expands Across Europe
The IOCTA 2026 report identifies artificial intelligence as a major driver of online fraud. Cybercriminals are using generative AI tools to create highly targeted phishing campaigns and social engineering attacks. These tools allow attackers to:- Personalize fraudulent messages at scale
- Mimic legitimate communication styles
- Automate large-scale scam operations
Ransomware and Data Extortion Remain Key Threats
Ransomware continues to be a dominant threat, as outlined in the IOCTA 2026 report. A large number of active ransomware groups were observed throughout 2025, with many adopting data extortion tactics. Instead of relying solely on encryption, attackers are increasingly threatening to release stolen data to pressure victims into paying. This shift has made cyberattacks more damaging, particularly for public institutions and large organizations. The report also notes growing links between state-sponsored actors and criminal groups, with some cybercriminals acting as proxies in broader geopolitical strategies. Emerging hacking coalitions are adding another layer of complexity to the threat landscape.Rise in Online Child Exploitation and Criminal Networks
The IOCTA 2026 report highlights a concerning increase in online child sexual exploitation cases. The financial trade of child abuse material is growing, and the use of synthetic content is creating new challenges for investigators. Encrypted messaging platforms are widely used by offenders, making it harder for authorities to monitor and intervene. The report also points to the emergence of organized online communities that engage in multiple forms of criminal activity. These networks combine cybercrime with violent offenses, creating a complex and dangerous ecosystem that extends beyond digital spaces.Need for Stronger Law Enforcement Collaboration
The findings of the IOCTA 2026 report reinforce the need for improved coordination between governments, law enforcement agencies, and industry stakeholders. As cyber threats become more advanced, isolated efforts are no longer sufficient. The report provides actionable insights and recommendations aimed at strengthening investigative capabilities and improving response strategies. It also stresses the importance of innovation in tackling new forms of cybercrime.Kraken Exchange Faces Extortion After Insider Recorded System Footage
UNC6783 Hackers Use Fake Okta Pages in Corporate Breach Campaign
Germany Names Suspected Leader of REvil and GandCrab Ransomware Gangs

Inside the REvil Ransomware Gang’s Operations
Authorities allege that Shchukin, along with another suspect, Anatoly Sergeevitsch Kravchuk, carried out coordinated attacks that extorted nearly €2 million, while causing more than €35 million in economic damage. The REvil ransomware gang and GandCrab ransomware group were among the first to popularize “double extortion”, a tactic that changed the ransomware landscape. Victims were not only asked to pay for decryption keys but also pressured to pay again to prevent stolen data from being published. This model has since become standard across ransomware gangs, making attacks more damaging and recovery more difficult for victims.From GandCrab to REvil: Evolution of a Cybercrime Enterprise
The GandCrab ransomware operation first appeared in 2018 and quickly gained traction through an affiliate model. Hackers were offered a share of profits in exchange for breaching corporate systems, while the core operators maintained and improved the malware. Over time, GandCrab released multiple versions of its ransomware, each designed to evade detection and improve effectiveness. By May 2019, the group claimed to have earned over $2 billion before announcing its shutdown. Soon after, the REvil ransomware gang emerged. Many cybersecurity experts viewed it as a direct continuation or rebranding of GandCrab. Operating under the same alias “UNKNOWN,” the group expanded its reach and began targeting larger organizations with deeper pockets. REvil became known for “big-game hunting”—focusing on enterprises with significant revenues and cyber insurance coverage, increasing the likelihood of large payouts.Industrialization of Ransomware Gangs
What makes the REvil ransomware gang particularly significant is how it operated more like a business than a traditional cybercriminal group. Ransomware developers outsourced tasks such as gaining initial access, encrypting systems, and laundering payments. Specialized actors—like access brokers and crypto laundering services—formed an entire underground ecosystem supporting these attacks. This structure allowed ransomware gangs to scale operations quickly, reinvest profits, and continuously improve their tools. As a result, attacks became more targeted, more sophisticated, and more difficult to stop.High-Profile Attacks and Law Enforcement Response
One of the most notable incidents linked to the REvil ransomware gang was the 2021 attack on Kaseya, which impacted over 1,500 businesses worldwide. The scale of the breach demonstrated how ransomware could disrupt entire supply chains. However, the same attack also marked the beginning of REvil’s decline. The FBI later revealed it had gained access to the group’s infrastructure before the incident but could not act immediately without compromising its investigation. Subsequent actions, including the release of a free decryption key, weakened the group’s operations significantly.Following the Money and Identity Trail
Shchukin’s name had previously surfaced in a 2023 U.S. Department of Justice filing related to cryptocurrency seizures tied to REvil activities. Authorities linked him to digital wallets holding over $317,000 in illicit funds. Despite the identification, German authorities believe Shchukin remains in Russia, beyond immediate reach. “Based on the investigations so far, it is assumed that the wanted person is abroad, presumably in Russia,” the BKA noted.What This Means for the Ransomware Landscape
The exposure of a suspected leader behind the REvil ransomware gang is a rare win for law enforcement in a space where attribution is often difficult. But the broader issue remains. The structure pioneered by GandCrab ransomware and refined by REvil continues to influence modern ransomware gangs. The tools, tactics, and business models are still widely used. Even as individual operators are identified, the ecosystem they helped build continues to operate. The takeaway is clear: ransomware is no longer just a technical threat—it is an organized, evolving industry.World Leaks data extortion: What you need to know
Smashing Security podcast #460: Never knock on the door of a nuclear submarine base and ask for a selfie
Sextortion “I recorded you” emails reuse passwords found in disposable inboxes
Our malware removal support team recently flagged a new wave of sextortion emails, with the subject line: “You pervert, I recorded you!”
If the message sounds familiar, that’s because it’s a variation of the long-running “Hello pervert” scam.
The email claims the target’s device has been infected by a “drive-by exploit,” which supposedly gave the extortionist full access to the device. To add credibility, the scammer includes a password that actually belongs to the target.
Here’s one of the emails:
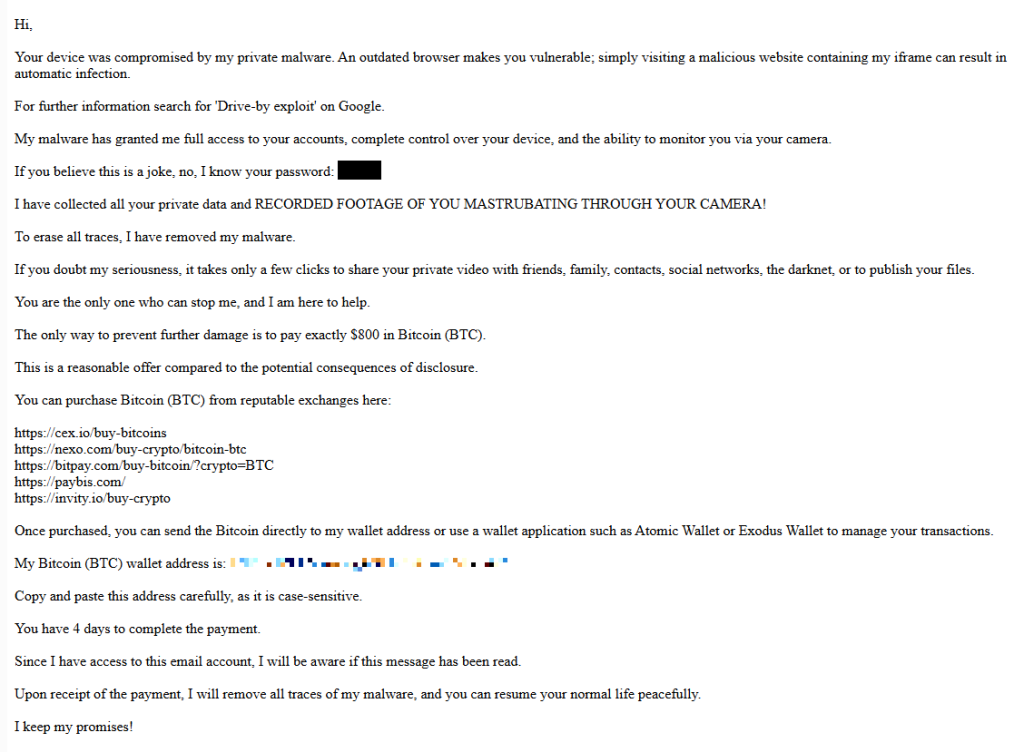
Your device was compromised by my private malware. An outdated browser makes you vulnerable; simply visiting a malicious website containing my iframe can result in automatic infection.
For further information search for ‘Drive-by exploit’ on Google.
My malware has granted me full access to your accounts, complete control over your device, and the ability to monitor you via your camera.
If you believe this is a joke, no, I know your password: {an actual password}
I have collected all your private data and RECORDED FOOTAGE OF YOU MASTRUBATING THROUGH YOUR CAMERA!
To erase all traces, I have removed my malware.
If you doubt my seriousness, it takes only a few clicks to share your private video with friends, family, contacts, social networks, the darknet, or to publish your files.
You are the only one who can stop me, and I am here to help.
The only way to prevent further damage is to pay exactly $800 in Bitcoin (BTC).
This is a reasonable offer compared to the potential consequences of disclosure.
You can purchase Bitcoin (BTC) from reputable exchanges here:
{list of crypto-currency exchanges}
Once purchased, you can send the Bitcoin directly to my wallet address or use a wallet application such as Atomic Wallet or Exodus Wallet to manage your transactions.
My Bitcoin (BTC) wallet address is: {bitcoin wallet which has received 1 payment at the time of writing}
Copy and paste this address carefully, as it is case-sensitive.
You have 4 days to complete the payment.
Since I have access to this email account, I will be aware if this message has been read.
Upon receipt of the payment, I will remove all traces of my malware, and you can resume your normal life peacefully.
I keep my promises!
The message is a bit contradictory. Early on, the sender claims they have already removed the malware to “erase all traces,” but later promises to remove it after receiving payment.
Where the password comes from
I found that one particular sender using the name Jenny Green and the Gmail address JennyGreen64868@gmail.com sent many of these emails to people that use the FakeMailGenerator service.
FakeMailGenerator is a free disposable email service that gives users a temporary, receive‑only inbox they can use instead of their real address, mainly to get around email confirmations or avoid spam.
As mentioned, the addresses are receive‑only, meaning they cannot legitimately send mail and the mailbox is not tied to a specific person. On top of that, there is no login. Anyone who knows the address (or guesses the inbox URL) can see the same inbox.
My guess is that the scammer searched these public inboxes for passwords and then reused those passwords in their sextortion emails.
So users of FakeMailGenerator and similar services should consider this a warning. Your inbox may be publicly accessible, show up in search results, and you may receive a lot more than what you signed up for. Definitely don’t use services like this for anything sensitive.
How to stay safe
Knowing these scams exist is the first step to avoiding them. Sextortion emails rely on panic and embarrassment to push people into paying quickly. Here are a few simple steps to protect yourself:
- Don’t rush. Scammers rely on fear and urgency. Take a moment to think before reacting.
- Don’t reply to the email. Responding tells the attacker that someone is reading messages at that address, which may lead to more scams.
- Change your password if it appears in the email. If you still use that password anywhere, update it.
- Use a password manager. If you’re having trouble generating or storing a strong password, have a look at a password manager.
- Don’t open unsolicited attachments. Especially when the sender address is suspicious or even your own.
- Don’t use disposable inboxes for important accounts. The mail in that inbox might be available for anyone to find.
- For peace of mind, turn your webcam off or buy a webcam cover so you can cover it when you’re not using the webcam.
Pro tip: Malwarebytes Scam Guard immediately recognized this for what it is: a sextortion scam.
What do cybercriminals know about you?
Use Malwarebytes’ free Digital Footprint scan to see whether your personal information has been exposed online.
ShinyHunters Leak 12.4 Million CarGurus Records in Massive Data Dump
ShinyHunters allegedly leaked 12.4 million CarGurus records, exposing personal and financing data and raising risks of phishing and data extortion attacks.
The post ShinyHunters Leak 12.4 Million CarGurus Records in Massive Data Dump appeared first on TechRepublic.
Please Don’t Feed the Scattered Lapsus ShinyHunters
A prolific data ransom gang that calls itself Scattered Lapsus ShinyHunters (SLSH) has a distinctive playbook when it seeks to extort payment from victim firms: Harassing, threatening and even swatting executives and their families, all while notifying journalists and regulators about the extent of the intrusion. Some victims reportedly are paying — perhaps as much to contain the stolen data as to stop the escalating personal attacks. But a top SLSH expert warns that engaging at all beyond a “We’re not paying” response only encourages further harassment, noting that the group’s fractious and unreliable history means the only winning move is not to pay.

Image: Shutterstock.com, @Mungujakisa
Unlike traditional, highly regimented Russia-based ransomware affiliate groups, SLSH is an unruly and somewhat fluid English-language extortion gang that appears uninterested in building a reputation of consistent behavior whereby victims might have some measure of confidence that the criminals will keep their word if paid.
That’s according to Allison Nixon, director of research at the New York City based security consultancy Unit 221B. Nixon has been closely tracking the criminal group and individual members as they bounce between various Telegram channels used to extort and harass victims, and she said SLSH differs from traditional data ransom groups in other important ways that argue against trusting them to do anything they say they’ll do — such as destroying stolen data.
Like SLSH, many traditional Russian ransomware groups have employed high-pressure tactics to force payment in exchange for a decryption key and/or a promise to delete stolen data, such as publishing a dark web shaming blog with samples of stolen data next to a countdown clock, or notifying journalists and board members of the victim company. But Nixon said the extortion from SLSH quickly escalates way beyond that — to threats of physical violence against executives and their families, DDoS attacks on the victim’s website, and repeated email-flooding campaigns.
SLSH is known for breaking into companies by phishing employees over the phone, and using the purloined access to steal sensitive internal data. In a January 30 blog post, Google’s security forensics firm Mandiant said SLSH’s most recent extortion attacks stem from incidents spanning early to mid-January 2026, when SLSH members pretended to be IT staff and called employees at targeted victim organizations claiming that the company was updating MFA settings.
“The threat actor directed the employees to victim-branded credential harvesting sites to capture their SSO credentials and MFA codes, and then registered their own device for MFA,” the blog post explained.
Victims often first learn of the breach when their brand name is uttered on whatever ephemeral new public Telegram group chat SLSH is using to threaten, extort and harass their prey. According to Nixon, the coordinated harassment on the SLSH Telegram channels is part of a well-orchestrated strategy to overwhelm the victim organization by manufacturing humiliation that pushes them over the threshold to pay.
Nixon said multiple executives at targeted organizations have been subject to “swatting” attacks, wherein SLSH communicated a phony bomb threat or hostage situation at the target’s address in the hopes of eliciting a heavily armed police response at their home or place of work.
“A big part of what they’re doing to victims is the psychological aspect of it, like harassing executives’ kids and threatening the board of the company,” Nixon told KrebsOnSecurity. “And while these victims are getting extortion demands, they’re simultaneously getting outreach from media outlets saying, ‘Hey, do you have any comments on the bad things we’re going to write about you.”
In a blog post today, Unit 221B argues that no one should negotiate with SLSH because the group has demonstrated a willingness to extort victims based on promises that it has no intention to keep. Nixon points out that all of SLSH’s known members hail from The Com, shorthand for a constellation of cybercrime-focused Discord and Telegram communities which serve as a kind of distributed social network that facilitates instant collaboration.
Nixon said Com-based extortion groups tend to instigate feuds and drama between group members, leading to lying, betrayals, credibility destroying behavior, backstabbing, and sabotaging each other.
“With this type of ongoing dysfunction, often compounding by substance abuse, these threat actors often aren’t able to act with the core goal in mind of completing a successful, strategic ransom operation,” Nixon wrote. “They continually lose control with outbursts that put their strategy and operational security at risk, which severely limits their ability to build a professional, scalable, and sophisticated criminal organization network for continued successful ransoms – unlike other, more tenured and professional criminal organizations focused on ransomware alone.”
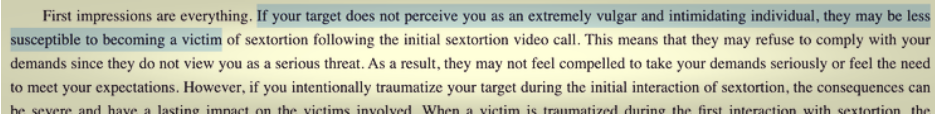
Intrusions from established ransomware groups typically center around encryption/decryption malware that mostly stays on the affected machine. In contrast, Nixon said, ransom from a Com group is often structured the same as violent sextortion schemes against minors, wherein members of The Com will steal damaging information, threaten to release it, and “promise” to delete it if the victim complies without any guarantee or technical proof point that they will keep their word. She writes:
A key component of SLSH’s efforts to convince victims to pay, Nixon said, involves manipulating the media into hyping the threat posed by this group. This approach also borrows a page from the playbook of sextortion attacks, she said, which encourages predators to keep targets continuously engaged and worrying about the consequences of non-compliance.
“On days where SLSH had no substantial criminal ‘win’ to announce, they focused on announcing death threats and harassment to keep law enforcement, journalists, and cybercrime industry professionals focused on this group,” she said.
Nixon knows a thing or two about being threatened by SLSH: For the past several months, the group’s Telegram channels have been replete with threats of physical violence against her, against Yours Truly, and against other security researchers. These threats, she said, are just another way the group seeks to generate media attention and achieve a veneer of credibility, but they are useful as indicators of compromise because SLSH members tend to name drop and malign security researchers even in their communications with victims.
“Watch for the following behaviors in their communications to you or their public statements,” Unit 221B’s advisory reads. “Repeated abusive mentions of Allison Nixon (or “A.N”), Unit 221B, or cybersecurity journalists—especially Brian Krebs—or any other cybersecurity employee, or cybersecurity company. Any threats to kill, or commit terrorism, or violence against internal employees, cybersecurity employees, investigators, and journalists.”
Unit 221B says that while the pressure campaign during an extortion attempt may be traumatizing to employees, executives, and their family members, entering into drawn-out negotiations with SLSH incentivizes the group to increase the level of harm and risk, which could include the physical safety of employees and their families.
“The breached data will never go back to the way it was, but we can assure you that the harassment will end,” Nixon said. “So, your decision to pay should be a separate issue from the harassment. We believe that when you separate these issues, you will objectively see that the best course of action to protect your interests, in both the short and long term, is to refuse payment.”
Pornhub tells users to expect sextortion emails after data exposure
After a recent data breach that affected Pornhub Premium members, Pornhub has updated its online statement to warn users about potential direct contact from cybercriminals.
“We are aware that the individuals responsible for this incident have threatened to contact impacted Pornhub Premium users directly. You may therefore receive emails claiming they have your personal information. As a reminder, we will never ask for your password or payment information by email.”
Pornhub is one of the world’s most visited adult video-sharing websites, allowing users to view content anonymously or create accounts to upload and interact with videos.
Pornhub has reported that on November 8, 2025, a security breach at third-party analytics provider Mixpanel exposed “a limited set of analytics events for certain users.” Pornhub stressed that this was not a breach of Pornhub’s own systems, and said that passwords, payment details, and financial information were not exposed.
Mixpanel confirmed it experienced a security incident on November 8, 2025, but disputes that the Pornhub data originated from that breach. The company stated there is:
“No indication that this data was stolen from Mixpanel during our November 2025 security incident or otherwise.”
Regardless of the source, cybercriminals commonly attempt to monetize stolen user data through direct extortion. At the moment, it is unclear how many users are affected, although available information suggests that only Premium members had their data exposed.
In October, we reported that one in six mobile users are targeted by sextortion scams. Sextortion is a form of online blackmail where criminals threaten to share a person’s private, nude, or sexually explicit images or videos unless the victim complies with their demands—often for more sexual content, sexual favors, or money.
Having your email address included in a dataset of known Pornhub users makes you a likely target for this type of blackmail.
How to stay safe from sextortion
Unless you used a dedicated throwaway email address to sign up for Pornhub Premium, you should be prepared to receive a sextortion-type email. If one arrives:
- Any message referencing your Pornhub use, searches, or payment should be treated as an attempt to exploit breached or previously leaked data.
- Never provide passwords or payment information by email. Pornhub has stated it will not ask for these.
- Do not respond to blackmail emails. Ignore demands, do not pay, and do not reply—responding confirms your address is actively monitored.
- Save extortion emails, including headers, content, timestamps, and attachments, but do not open links or files. This information can support reports to your email provider, local law enforcement, or cybercrime units.
- Change your Pornhub password (if your account is still active) and ensure it’s unique and not reused anywhere else.
- Turn on multi-factor authentication (MFA) for your primary email account and any accounts that could be used for account recovery or identity verification.
- Review your bank and card statements for unfamiliar charges and report any suspicious transactions at once.
- If you used a real-name email address for Pornhub, consider moving sensitive subscriptions to a separate, pseudonymous email going forward.
Use STOP, our simple scam response framework to help protect against scams.
- S—Slow down: Don’t let urgency or pressure push you into action. Take a breath before responding. Legitimate businesses like your bank or credit card don’t push immediate action.
- T—Test them: If you answered the phone and are feeling panicked about the situation, likely involving a family member or friend, ask a question only the real person would know—something that can’t be found online.
- O—Opt out: If it feels off, hang up or end the conversation. You can always say the connection dropped.
- P—Prove it: Confirm the person is who they say they are by reaching out yourself through a trusted number, website or method you have used before.
Should you have doubts about the legitimacy of any communications, submit them to Malwarebytes Scam Guard. It will help you determine whether it’s a scam and provide advice on how to act.
We don’t just report on threats—we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your, and your family’s, personal information by using identity protection.