The post Cisco CNC and NSO Flaw Allows Remote Attackers to Lock Down Network Management appeared first on Daily CyberSecurity.
Visualização de leitura
Massive “Low and Slow” DDoS Attack Hits Platform With 2.45 Billion in 5 Hours
Hackers Use Jenkins Access to Deploy DDoS Botnet Against Gaming Servers
Anti-DDoS Firm Heaped Attacks on Brazilian ISPs
A Brazilian tech firm that specializes in protecting networks from distributed denial-of-service (DDoS) attacks has been enabling a botnet responsible for an extended campaign of massive DDoS attacks against other network operators in Brazil, KrebsOnSecurity has learned. The firm’s chief executive says the malicious activity resulted from a security breach and was likely the work of a competitor trying to tarnish his company’s public image.

An Archer AX21 router from TP-Link. Image: tp-link.com.
For the past several years, security experts have tracked a series of massive DDoS attacks originating from Brazil and solely targeting Brazilian ISPs. Until recently, it was less than clear who or what was behind these digital sieges. That changed earlier this month when a trusted source who asked to remain anonymous shared a curious file archive that was exposed in an open directory online.
The exposed archive contained several Portuguese-language malicious programs written in Python. It also included the private SSH authentication keys belonging to the CEO of Huge Networks, a Brazilian ISP that primarily offers DDoS protection to other Brazilian network operators.
Founded in Miami, Fla. in 2014, Huge Networks’s operations are centered in Brazil. The company originated from protecting game servers against DDoS attacks and evolved into an ISP-focused DDoS mitigation provider. It does not appear in any public abuse complaints and is not associated with any known DDoS-for-hire services.
Nevertheless, the exposed archive shows that a Brazil-based threat actor maintained root access to Huge Networks infrastructure and built a powerful DDoS botnet by routinely mass-scanning the Internet for insecure Internet routers and unmanaged domain name system (DNS) servers on the Web that could be enlisted in attacks.
DNS is what allows Internet users to reach websites by typing familiar domain names instead of the associated IP addresses. Ideally, DNS servers only provide answers to machines within a trusted domain. But so-called “DNS reflection” attacks rely on DNS servers that are (mis)configured to accept queries from anywhere on the Web. Attackers can send spoofed DNS queries to these servers so that the request appears to come from the target’s network. That way, when the DNS servers respond, they reply to the spoofed (targeted) address.
By taking advantage of an extension to the DNS protocol that enables large DNS messages, botmasters can dramatically boost the size and impact of a reflection attack — crafting DNS queries so that the responses are much bigger than the requests. For example, an attacker could compose a DNS request of less than 100 bytes, prompting a response that is 60-70 times as large. This amplification effect is especially pronounced when the perpetrators can query many DNS servers with these spoofed requests from tens of thousands of compromised devices simultaneously.
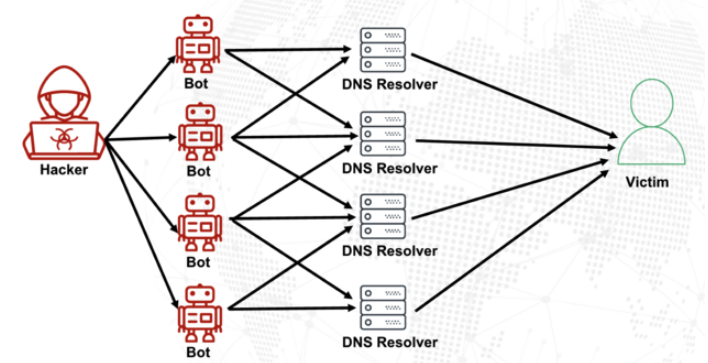
A DNS amplification and reflection attack, illustrated. Image: veracara.digicert.com.
The exposed file archive includes a command-line history showing exactly how this attacker built and maintained a powerful botnet by scouring the Internet for TP-Link Archer AX21 routers. Specifically, the botnet seeks out TP-Link devices that remain vulnerable to CVE-2023-1389, an unauthenticated command injection vulnerability that was patched back in April 2023.
Malicious domains in the exposed Python attack scripts included DNS lookups for hikylover[.]st, and c.loyaltyservices[.]lol, both domains that have been flagged in the past year as control servers for an Internet of Things (IoT) botnet powered by a Mirai malware variant.
The leaked archive shows the botmaster coordinated their scanning from a Digital Ocean server that has been flagged for abusive activity hundreds of times in the past year. The Python scripts invoke multiple Internet addresses assigned to Huge Networks that were used to identify targets and execute DDoS campaigns. The attacks were strictly limited to Brazilian IP address ranges, and the scripts show that each selected IP address prefix was attacked for 10-60 seconds with four parallel processes per host before the botnet moved on to the next target.
The archive also shows these malicious Python scripts relied on private SSH keys belonging to Huge Networks’s CEO, Erick Nascimento. Reached for comment about the files, Mr. Nascimento said he did not write the attack programs and that he didn’t realize the extent of the DDoS campaigns until contacted by KrebsOnSecurity.
“We received and notified many Tier 1 upstreams regarding very very large DDoS attacks against small ISPs,” Nascimento said. “We didn’t dig deep enough at the time, and what you sent makes that clear.”
Nascimento said the unauthorized activity is likely related to a digital intrusion first detected in January 2026 that compromised two of the company’s development servers, as well as his personal SSH keys. But he said there’s no evidence those keys were used after January.
“We notified the team in writing the same day, wiped the boxes, and rotated keys,” Nascimento said, sharing a screenshot of a January 11 notification from Digital Ocean. “All documented internally.”
Mr. Nascimento said Huge Networks has since engaged a third-party network forensics firm to investigate further.
“Our working assessment so far is that this all started with a single internal compromise — one pivot point that gave the attacker downstream access to some resources, including a legacy personal droplet of mine,” he wrote.
“The compromise happened through a bastion/jump server that several people had access to,” Nascimento continued. “Digital Ocean flagged the droplet on January 11 — compromised due to a leaked SSH key, in their wording — I was traveling at the time and addressed it on return. That droplet was deprecated and destroyed, and it was never part of Huge Networks infrastructure.”
The malicious software that powers the botnet of TP-Link devices used in the DDoS attacks on Brazilian ISPs is based on Mirai, a malware strain that made its public debut in September 2016 by launching a then record-smashing DDoS attack that kept this website offline for four days. In January 2017, KrebsOnSecurity identified the Mirai authors as the co-owners of a DDoS mitigation firm that was using the botnet to attack gaming servers and scare up new clients.
In May 2025, KrebsOnSecurity was hit by another Mirai-based DDoS that Google called the largest attack it had ever mitigated. That report implicated a 20-something Brazilian man who was running a DDoS mitigation company as well as several DDoS-for-hire services that have since been seized by the FBI.
Nascimento flatly denied being involved in DDoS attacks against Brazilian operators to generate business for his company’s services.
“We don’t run DDoS attacks against Brazilian operators to sell protection,” Nascimento wrote in response to questions. “Our sales model is mostly inbound and through channel integrator, distributors, partners — not active prospecting based on market incidents. The targets in the scripts you received are small regional providers, the vast majority of which are neither in our customer base nor in our commercial pipeline — a fact verifiable through public sources like QRator.”
Nascimento maintains he has “strong evidence stored on the blockchain” that this was all done by a competitor. As for who that competitor might be, the CEO wouldn’t say.
“I would love to share this with you, but it could not be published as it would lose the surprise factor against my dishonest competitor,” he explained. “Coincidentally or not, your contact happened a week before an important event – one that this competitor has NEVER participated in (and it’s a traditional event in the sector). And this year, they will be participating. Strange, isn’t it?”
Strange indeed.
Litecoin Hit by Zero-Day Vulnerability, Triggers 13-Block Reorganization

The Zero-Day Bug and Its Impact on the Litecoin Network
A zero-day vulnerability refers to a flaw that is unknown to the developers at the time of its exploitation. In this case, the bug targeted the handling of MimbleWimble Extension Block (MWEB) transactions, a privacy feature on the Litecoin network. The vulnerability allowed an attacker to exploit the network by triggering a Denial-of-Service (DoS) attack, flooding the network with invalid MWEB transactions. MWEB transactions are designed to offer enhanced privacy for Litecoin users by obscuring transaction details. However, due to the zero-day bug, some Litecoin nodes that had not updated their software accepted invalid MWEB transactions, violating the network’s consensus rules. As a result, a block reorganization (or “reorg”) took place when a competing chain of blocks replaced the existing chain, causing 13 blocks to be reorganized. A block reorg of this magnitude is a rare event and presents significant challenges, including the potential for double-spending and undermined user confidence.Understanding the Denial-of-Service Attack and Its Impact on Miners
The core target of the attack was the mining pools, which play a critical role in securing the Litecoin network. Mining pools are groups of miners who pool their computational power to increase their chances of successfully finding a block. By launching a DoS attack, the attacker aimed to disrupt the mining process by overwhelming the network with invalid transactions. The impact on miners was particularly severe. Mining pools that failed to update their nodes were unable to process valid blocks during the attack. This resulted in temporary downtime for these pools, contributing to a short-term drop in the network’s hashrate. While the Litecoin network quickly recovered, the event highlighted the vulnerability of mining operations when software updates are delayed or ignored.Quick Response and Deployment of the Patch
Despite the severity of the incident, the Litecoin team responded promptly. Within hours, the development team confirmed the bug and rolled out a patch that effectively closed the attack vector. The patch prevented nodes from accepting invalid MWEB transactions, thus stabilizing the network and mitigating further risks. The team urged all node operators to update their software immediately to ensure the security of their operations. Importantly, the Litecoin team confirmed that no funds were lost as a result of the reorganization. While users’ transactions that were part of the reorganized blocks were reversed, the overall integrity of the network remained intact. The incident, although disruptive, demonstrated the resilience and quick action of the Litecoin team.The Role of MWEB and Zero-Day Bugs
Launched in 2011, Litecoin has earned a reputation as one of the oldest and most stable cryptocurrencies. As a fork of Bitcoin, it relies on a proof-of-work consensus mechanism to validate transactions. Over the years, Litecoin has faced relatively few security incidents, but the April 25 event serves as a stark reminder that even established networks are susceptible to vulnerabilities. The introduction of MWEB in 2022 marked a significant upgrade for Litecoin, providing users with enhanced privacy features. However, as seen with this recent zero-day vulnerability, new features can also introduce unforeseen risks.eBay Struggles with Widespread Outage, Disrupting Transactions and API Access

The Scope of the eBay Outage
The eBay outage first began to affect eBay users on the afternoon of April 26, when they began reporting issues with the platform’s functionality. According to Downdetector, a popular service that tracks online outages, the spike in complaints reached around 3:30 PM ET, with the situation worsening the evening. As of 10:30 PM ET, more than 1,300 outage reports were logged, although the number eventually decreased to about 600 by 11:50 PM ET. Users complained that essential functions like search were malfunctioning, and pages were loading extremely slowly. "I can't even search for anything or complete a purchase," one frustrated user posted on social media. Others echoed similar concerns, noting that critical transactions were unable to be completed, with error messages preventing them from checking out. Sellers also voiced their frustrations, noting that they could not access the API, which is crucial for the functioning of third-party tools used to manage listings, inventory, and sales. "It’s been nearly 6 hours since the API went down, and we have no word from support," one seller wrote, emphasizing the financial impact of the outage.Social Media Users Complain About the Outage
While eBay has not officially confirmed the cause of the outage, rumors quickly began circulating on social media that the hacktivist group 313 Team was responsible for a DDoS attack targeting the platform. DDoS attacks, which flood a website with traffic to overwhelm its servers and take it offline, have become a frequent tactic for hacktivist groups in recent years. The group, which has previously targeted high-profile organizations, allegedly posted a claim on various forums, taking credit for the disruption. However, this attribution has not been independently verified, and eBay has not provided details about the nature of the attack. The company’s official status page displayed no alerts of a cyberattack, showing only minor updates on the system’s functionality. Despite these official updates, the community’s response has been vocal, with many users continuing to report issues well into the night. One individual posted, "It’s not just down for me, it’s down for everyone. Is this part of a bigger attack targeting e-commerce sites?" With eBay’s customer support channels largely silent or offering only generic responses, users took to social media to express their frustration. The company’s Instagram account, where many users had previously reached out for help, quickly became a forum for complaints. One commenter wrote, “Brooo you’re down—come on, get up! I need to pay for an auction.” Others left similar messages, questioning the reliability of the platform and demanding answers.O iPhone não é tão invencível assim: uma análise do DarkSword e do Coruna | Blog oficial da Kaspersky
O DarkSword e o Coruna são novas ferramentas utilizadas em ataques invisíveis a dispositivos iOS. Esses ataques não exigem interação do usuário e já estão sendo usados em larga escala por agentes mal-intencionados. Antes do surgimento dessas ameaças, a maioria dos usuários do iPhone não precisava se preocupar com a segurança de dados. Poucos grupos realmente se preocupavam com isso, como políticos, ativistas, diplomatas, executivos de negócios de alto nível e pessoas que lidam com dados extremamente confidenciais, já que eles poderiam vir a ser alvos de agências de inteligência estrangeiras. Já discutimos spywares avançados usados contra esses grupos anteriormente, e observamos como era raro encontrá-los.
No entanto, o DarkSword e o Coruna, descobertos por pesquisadores no início deste ano, são revolucionários. Esses malwares estão sendo usados em infecções em massa de usuários comuns. Nesta postagem, explicamos por que essa mudança ocorreu, os riscos dessas ferramentas e como se proteger.
O que sabemos sobre o DarkSword e como ele pode infectar o seu iPhone
Em meados de março de 2026, três equipes de pesquisa diferentes coordenaram a divulgação das suas descobertas sobre um novo spyware chamado de DarkSword. Essa ferramenta é capaz de invadir silenciosamente dispositivos com o iOS 18, sem que o usuário perceba que algo está errado.
Primeiro, devemos esclarecer uma coisa: o iOS 18 não é tão antigo quanto parece. Embora a versão mais recente seja o iOS 26, a Apple revisou recentemente o sistema de versões, surpreendendo a todos. A empresa decidiu avançar oito versões (da 18 diretamente para a 26) para que o número do sistema operacional correspondesse ao ano atual. Apesar disso, a Apple estima que cerca de um quarto de todos os dispositivos ativos ainda executam o iOS 18 ou uma versão anterior.
Agora que isso já foi esclarecido, vamos voltar a falar sobre o DarkSword. A pesquisa mostra que esse malware infecta as vítimas quando elas visitam sites perfeitamente legítimos que contêm códigos maliciosos. O spyware se instala sem qualquer interação do usuário: basta acessar uma página comprometida. Isso é conhecido como técnica de infecção zero clique. Os pesquisadores relatam que milhares de dispositivos já foram infectados desta forma.
Para comprometer um dispositivo, o DarkSword usa uma cadeia de exploits com seis vulnerabilidades para evitar o sandbox, aumentar privilégios e executar código. Assim que o dispositivo é infectado, o malware consegue coletar dados, incluindo:
- Senhas
- Fotos
- Conversas e dados do iMessage, WhatsApp e Telegram
- Histórico do navegador
- Informações dos aplicativos Calendário, Notas e Saúde da Apple
Além disso, o DarkSword coleta dados de carteiras de criptomoedas, atuando como malware de dupla finalidade para espionagem e roubo de criptoativos.
A única boa notícia é que o spyware não sobrevive a uma reinicialização. O DarkSword é um malware sem arquivo, o que significa que ele vive na RAM do dispositivo e nunca se incorpora ao sistema de arquivos.
Coruna: direcionado às versões mais antigas do iOS
Apenas duas semanas antes da descoberta do DarkSword se tornar pública, os pesquisadores revelaram outra ameaça que tinha o iOS como alvo, chamada de Coruna. Esse malware consegue comprometer dispositivos que executam softwares mais antigos, especificamente as versões 13 a 17.2.1 do iOS. O método utilizado pelo Coruna é exatamente igual ao do DarkSword: as vítimas visitam um site legítimo injetado com código malicioso que, em seguida, infecta o dispositivo delas com o malware. Todo o processo é completamente invisível e não requer interação do usuário.
Uma análise detalhada do código do Coruna revelou que ele explora 23 vulnerabilidades distintas do iOS, várias delas localizadas no WebKit da Apple. Vale lembrar que, de um modo geral (fora da UE), todos os navegadores iOS precisam usar o mecanismo WebKit. Isso significa que essas vulnerabilidades não afetam apenas os usuários do Safari, mas também qualquer pessoa que use outros navegadores no iPhone.
A versão mais recente do Coruna, assim como o DarkSword, inclui modificações projetadas para drenar carteiras de criptomoedas. Ele também coleta fotos e, em alguns casos, informações de e-mails. Ao que tudo indica, roubar criptomoedas parece ser o principal motivo da implementação generalizada do Coruna.
Quem criou o Coruna e o DarkSword, e como eles foram disseminados?
A análise do código de ambas as ferramentas sugere que o Coruna e o DarkSword provavelmente foram desenvolvidos por grupos diferentes. No entanto, ambos são softwares criados por empresas patrocinadas pelo governo, possivelmente dos EUA. Isso se reflete na alta qualidade do código: não são kits montados com partes aleatórias, mas exploits projetados de forma uniforme. Em algum momento, essas ferramentas vazaram e foram parar nas mãos de gangues de cibercriminosos.
Os especialistas da GReAT, da Kaspersky, analisaram todos os componentes do Coruna e confirmaram que o kit de exploração é uma versão atualizada da estrutura usada na Operação Triangulação. Esse ataque anterior tinha como alvo os funcionários da Kaspersky, uma história que abordamos em detalhes neste blog.
Uma teoria sugere que um funcionário da empresa que desenvolveu o Coruna vendeu o malware para hackers. Desde então, ele tem sido usado para drenar carteiras de criptomoedas de usuários na China. Alguns especialistas estimam que pelo menos 42 mil dispositivos foram infectados somente neste país.
Quanto ao DarkSword, os cibercriminosos já o usaram para infectar dispositivos de usuários na Arábia Saudita, Turquia e Malásia. O problema se agrava pelo fato de que os invasores que implementaram o DarkSword deixaram o código-fonte completo nos sites infectados, facilitando a detecção dele por outros grupos criminosos.
O código também inclui comentários detalhados explicado exatamente o que faz cada componente, reforçando a hipótese de que ele surgiu no Ocidente. Essas instruções detalhadas tornam mais fácil para outros hackers adaptarem a ferramenta para interesses próprios.
Como se proteger do Coruna e do DarkSword
Dois malwares poderosos que permitem a infecção em massa de iPhones sem exigir qualquer interação do usuário caíram nas mãos de um grupo essencialmente ilimitado de cibercriminosos. Para ser infectado pelo Coruna ou pelo DarkSword, basta que você visite o site errado na hora errada. Portanto, este é um daqueles casos em que todos os usuários precisam levar a sério a segurança do iOS, não apenas aqueles que pertencem a grupos de alto risco.
A melhor coisa a fazer para se proteger do Coruna e do DarkSword é atualizar assim que possível os dispositivos para a versão mais recente do iOS ou do iPadOS 26. Se isso não for possível (por exemplo, se o dispositivo for mais antigo e não compatível com o iOS 26), ainda assim é recomendado baixar a versão mais recente disponível. Especificamente, procure as versões 15.8.7, 16.7.15 ou 18.7.7. A Apple aplicou correções em vários sistemas operacionais mais antigos, o que é raro.
Para proteger os dispositivos Apple contra malwares semelhantes que provavelmente aparecerão no futuro, recomendamos fazer o seguinte:
- Instale as atualizações em todos os dispositivos da Apple o quanto antes. A empresa lança regularmente versões do SO que corrigem vulnerabilidades conhecidas. Não as ignore.
- Ative a opção Otimização de segurança em segundo plano. Esse recurso permite que o dispositivo receba correções de segurança críticas além das atualizações completas do iOS, reduzindo o risco de exploração de vulnerabilidades pelos hackers. Para ativá-lo, vá para Configurações → Privacidade e segurança → Otimização de segurança em segundo plano e ative a opção Instalar automaticamente.
- Considere usar o Modo de bloqueio. Essa é uma configuração de segurança reforçada que, apesar de limitar alguns recursos do dispositivo, bloqueia ou restringe ataques de forma significativa. Para ativá-lo, vá para Configurações → Privacidade e segurança → Modo de bloqueio → Ativar o Modo de bloqueio.
- Reinicie o dispositivo uma vez por dia (ou mais). Isso interrompe a atuação de malwares sem arquivo, pois essas ameaças não são incorporadas ao sistema e desaparecem após a reinicialização.
- Use o armazenamento criptografado para dados confidenciais. Mantenha chaves de carteiras de criptomoedas, fotos de documentos e dados confidenciais em um local seguro. Kaspersky Password Manager é uma ótima opção para isso, pois gerencia suas senhas, tokens de autenticação de dois fatores e chaves de acesso em todos os dispositivos, mantendo notas, fotos e documentos sincronizados e criptografados.
A ideia de que os dispositivos da Apple são à prova de balas é um mito. Eles são vulneráveis a ataques de zero clique, cavalos de Troia e técnicas de infecção ClickFix. Além disso, aplicativos maliciosos já foram encontrados na App Store mais de uma vez. Leia mais aqui:
- Predador vs. iPhone: a arte da vigilância invisível
- AirBorne: Ataques a dispositivos da Apple através de vulnerabilidades no AirPlay
- Os seus fones de ouvido Bluetooth estão espionando você?
- O trojan para roubo de dados SparkCat penetra na App Store e no Google Play para roubar dados de fotos
- Banshee: um malware de roubo de dados que persegue usuários do macOS




DDoS wave continues as Mastodon hit after Bluesky incident
Mastodon suffered a major DDoS attack shortly after a similar incident hit Bluesky. The outage was significant but resolved within a few hours.
Mastodon was hit by a major DDoS attack just days after a similar disruption affected Bluesky. Mastodon is a free and open-source software platform for decentralized social networking with microblogging features similar to X.
The attack caused a major outage, impacting users across the decentralized platform. However, Mastodon’s team responded quickly and mitigated the issue within a few hours, restoring normal service.
Below is the timeline of the attack:
- April 20, 2026 at 12:58 PM – We are currently experiencing a DDoS attack. We are actively investigating the issue.
- April 20, 2026 at 3:05 PM – We have implemented countermeasure against the DDoS attack, and the site is accessible. We are continuing to monitor the situation.
- April 20, 2026 at 12:58 PM – We are currently experiencing a DDoS attack. We are actively investigating the issue.
A group called 313 Team claimed responsibility for the attack on Bluesky, but no threat actor has publicly taken credit for the Mastodon attack.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, DDOS)
Bluesky Back Online After DDoS Attack, as Iran-Linked 313 Team Takes Credit
Bluesky hit by 24-hour DDoS attack as pro-Iran group claims responsibility
Bluesky suffered a 24-hour DDoS attack that caused outages. A pro-Iran hacker group claimed responsibility for the disruption.
Bluesky experienced a sophisticated DDoS attack that disrupted its services for about 24 hours, starting on April 15.
Bluesky is a decentralized, open-source microblogging social media platform similar to X (formerly Twitter). It allows users to post short messages, images, and videos (up to 300 characters) while providing more control over algorithms, data, and moderation.
The attack disrupted feeds, notifications, threads, and search, causing intermittent outages. A pro-Iran hacker group, called 313 Team (aka “Islamic Cyber Resistance in Iraq”), claimed responsibility, highlighting growing threats against social media platforms and the impact of coordinated disruption campaigns.
“Our team received a report of intermittent app outages at about 11:40pm PDT on April 15, 2026. They worked through the night to mitigate a sophisticated Distributed Denial-of-Service (DDoS) attack, which intensified throughout the day.” Bluesky announced. “We have not seen any evidence of unauthorized access to private user data.”
The company found no signs of data breaches and confirmed it limited the impact of the attack and avoided prolonged outages.
313 Team is a pro-Iran hacktivist group tied to politically driven cyber activity like DDoS attacks, defacements, phishing, and data-leak claims. It targets public services, government and symbolic platforms to create disruption and amplify geopolitical tensions. Analysts link it to the broader Iran-aligned ecosystem, sometimes close to state interests. However, the group often exaggerates its impact, so claims should be treated with caution.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Islamic Cyber Resistance in Iraq)
Bluesky, Fast-Growing X Alternative, Hit by Sophisticated DDoS Attack

Bluesky Cyberattack Disrupts Core Platform Functions
The disruption began at approximately 11:40 PM PDT on April 15, when Bluesky received initial reports of intermittent outages. Engineers responded immediately, working overnight to contain what was later described as a “sophisticated” DDoS attack. As the attack intensified over the next several hours, it began to impact the platform’s functionality. In an early update, Bluesky stated: “We are experiencing some service interruptions, and our team is working on the issue. You can find the latest updates at status.bsky.app or follow @status.bsky.app.” As more users reported issues, the company clarified the extent of the disruption: “The attack is impacting our application, with users experiencing intermittent interruptions in service for their feeds, notifications, threads and search.” DDoS attacks function by overwhelming servers with massive volumes of traffic, effectively preventing legitimate users from accessing services. In this case, the cyberattack on Bluesky followed that pattern, focusing on disrupting availability rather than infiltrating systems or extracting sensitive data.Platform Stabilizes While Attack Continues
By around 9 PM PDT on April 16, Bluesky reported that the platform had stabilized despite the continued presence of DDoS traffic. The company noted: “The application has remained stable since approximately 9 PM PDT, April 16 despite ongoing Distributed Denial-of-Service (DDoS) attacks. We have not seen any evidence of unauthorized access to private user data.” This message was reiterated in subsequent updates, reinforcing the company’s position that user data remained secure. In its final communication on the incident, Bluesky stated: “The application has remained stable since the evening of April 16 and we have seen no evidence of unauthorized access to private user data. Given the ongoing stability, this will be our final update.”Attribution Remains Unclear as Platform Continues to Grow
The company has not officially attributed the attack to any specific group or actor. However, a group identifying itself as “313 Team,” reportedly claimed responsibility through a Telegram message, stating that it had carried out a “massive cyberattack” targeting Bluesky’s application programming interface (API). The incident comes amid a period of significant growth for the platform. Since its inception, Bluesky has expanded to approximately 43.7 million users, driven in part by users migrating from X following political developments in the United States.Relatório de Ameaça: STX RAT
Motivação
O STX RAT representa mais um representante relevante da evolução contínua dos Remote Access Trojans (RATs) baseados em .NET, operando em um ecossistema onde acessibilidade, modularidade e baixo custo de entrada favorecem sua rápida disseminação entre atores de ameaça com diferentes níveis de sofisticação. Para a tomada de decisão de CISOs, o risco não reside apenas nas capacidades técnicas do malware, mas na combinação de três fatores críticos:
- Facilidade de aquisição e operação (commodity malware)
- Capacidade de persistência silenciosa em endpoints corporativos
- Integração com cadeias de ataque maiores (stealers, loaders, ransomware)
O STX RAT não é, isoladamente, uma ferramenta de alta sofisticação. No entanto, seu uso em campanhas oportunistas e sua capacidade de fornecer acesso contínuo ao ambiente comprometido o tornam um multiplicador de risco, frequentemente atuando como estágio intermediário para ataques mais destrutivos. Do ponto de vista de negócio, os principais impactos incluem:
- Exfiltração de dados sensíveis (credenciais, documentos, sessões)
- Comprometimento prolongado sem detecção
- Uso como ponto de apoio para ransomware
- Exposição regulatória (LGPD) e dano reputacional
A Evolução
O STX RAT se insere no ecossistema consolidado de RATs baseados em .NET, ao lado de famílias como AsyncRAT e QuasarRAT. Essas ferramentas compartilham características comuns:
- Código relativamente acessível
- Facilidade de customização
- Interfaces de controle amigáveis
- Distribuição via fóruns underground e canais fechados
Em 2025, cabe destacar que houve uma convergência entre três categorias de malware:
- RATs tradicionais (controle remoto)
- Infostealers (exfiltração rápida de dados)
- Loaders (entrega de payloads adicionais)
O STX RAT acompanha essa tendência ao oferecer:
- Capacidades de coleta de dados
- Execução remota de comandos
- Flexibilidade para integração com outros payloads
O STX segue a tend6encia de Malware-as-a-Service (MaaS), um modelo de negocio criminoso onde deliquentes menos experientes conseguem conduzir campanhas eficazes com baixo investimento técnico.
3. Análise de Kill Chain
3.1 Vetores de entrada
O STX RAT é tipicamente distribuído por meio de vetores amplamente conhecidos, porém ainda eficazes:
- Campanhas de phishing com anexos maliciosos
- Arquivos compactados contendo executáveis disfarçados
- Arquivos ISO, LNK e loaders
- Software pirata, cracks e keygens
- Malvertising
A eficácia desses vetores depende fortemente de engenharia social, frequentemente adaptada ao idioma e contexto regional, além de ser cada vez mais efetiva graças ao uso intensivo de IA.
3.2 Execução inicial
Após o acesso inicial:
- O usuário executa um loader ou dropper
- O payload é descompactado ou injetado em memória
- Pode haver uso de LOLBins (ex.: PowerShell) para execução indireta
3.3 Persistência
O STX RAT estabelece persistência utilizando:
- Chaves de registro (Run/RunOnce)
- Tarefas agendadas
- Cópias em diretórios persistentes do sistema
Essa persistência é projetada para se manter a reinicializações e ofuscar as ações de ferramentas, analistas e .
3.4 Expansão e pós-exploração
Embora não seja um framework completo, que inclua o movimento lateral, o acesso fornecido permite:
- Execução de ferramentas adicionais
- Download de payloads secundários
- Movimentação manual por operadores
4. Arquitetura Técnica do STX RAT
O STX RAT, por suas características de desenvolvimento, possui:
- Portabilidade
- Ofuscação
- Rápido desenvolvimento
4.1. Capacidades principais:
- Keylogging
- Captura de tela
- Gerenciamento de arquivos
- Execução remota de comandos
- Monitoramento do sistema
A comunicação entre cliente e servidor permite controle quase em tempo real.
5. Evasão
O STX RAT emprega técnicas comuns, porém eficazes:
5.1. Ofuscação
- Proteção de strings
- Packing do binário
5.2. Evasão de análise
- Detecção de ambiente virtual
- Delay de execução
- Verificação de sandbox
5.3. Evasão de defesa
- Uso de LOLBins
- Execução em memória (parcial)
- Possível bypass de mecanismos como AMSI
O objetivo não é invisibilidade total, mas reduzir a probabilidade de detecção automática.
6. Comando e Controle (C2)
A comunicação C2 geralmente utiliza:
- HTTP/HTTPS
- Portas customizadas
- Comunicação periódica (beaconing)
6.1. Características:
- Uso de VPS de baixo custo
- Rotação de IPs/domínios
- Infraestrutura descartável
Essa arquitetura favorece:
- Resiliência operacional
- Dificuldade de bloqueio completo
7. Impacto na América Latina
A América Latina apresenta condições favoráveis para disseminação do malware:
- Alta taxa de uso de software não licenciado
- Menor maturidade em segurança em PMEs
- Forte uso e eficácia de engenharia social
Setores frequentemente impactados:
- Financeiro
- Governo
- Pequenas e médias empresas
Campanhas costumam explorar:
- Idioma local (português ou espanhol)
- Temas como boletos, impostos, entregas e serviços bancários são os mais frequentes.
8. Técnicas, Táticas e procedimentos (TTPs)
O comportamento do STX RAT pode ser mapeado em diversas táticas:
a) Initial Access
- Phishing (T1566)
b) Execution
- User Execution (T1204)
- PowerShell (T1059.001)
c) Persistence
- Registry Run Keys (T1547.001)
- Scheduled Tasks (T1053)
d) Defense Evasion
- Obfuscated Files (T1027)
- Virtualization/Sandbox Evasion (T1497)
e) Command & Control
- Application Layer Protocol (T1071)
f) Exfiltration
- Exfiltration Over C2 Channel (T1041)
9. Estratégias de Detecção e Defesa
9.1. Controles técnicos
- EDR/XDR com análise comportamental
- Monitoramento de rede
- Detecção de anomalias
9.2. Hardening
- Bloqueio de macros
- Controle de execução de scripts
- Princípio do menor privilégio
9.3. Conscientização dos Usuários
- Treinamento contínuo contra phishing
10. Recomendações e Conclusões
O STX RAT não representa uma ruptura tecnológica, mas sim a continuidade de uma tendência perigosa, onde o modelo MaaS facilita o acesso de ferramentas de acesso remoto malicioso de alta eficácia. As principais recomendações de alto nível apontam para:
- Investir em visibilidade de endpoint
- Integrar threat intelligence ao SOC
- Melhorar capacidade de resposta a incidentes
- Reduzir superfície de ataque
Sua relevância está na escala, acessibilidade e integração com cadeias de ataque maiores, tornando-o um risco significativo para usuários finais e PMEs. Para Gestores e C-Levels, a prioridade deve ser:
- Detecção precoce
- Resposta rápida
- Redução de exposição humana
O maior risco não está na sofisticação do malware, mas na combinação entre acessibilidade, engenharia social e falhas de visibilidade defensiva.
Fiquem seguros e atenção nos detalhes! Um informe de inteligência pode fazer toda a diferença.
Operation PowerOFF: 53 DDoS domains seized and 3 Million criminal accounts uncovered
Operation PowerOFF shut down 53 DDoS-for-hire domains, arrested four suspects, and exposed data on over 3 million criminal user accounts.
Operation PowerOFF is an international law enforcement action that dismantled 53 domains linked to DDoS-for-hire services used by over 75,000 cybercriminals. Authorities arrested four suspects, seized infrastructure, and gained access to databases containing more than 3 million user accounts. They are now warning identified users, while continuing investigations with multiple search warrants.
DDoS-for-hire services, or “booters,” are illegal platforms that let users pay to launch DDoS attacks that flood websites or servers with traffic, causing outages. They are used for harassment, extortion, or disruption and can lead to serious legal consequences for users.
“On 13 April 2026, 21 countries joined forces in a coordinated action week that focused on enforcement and prevention measures against over 75 000 criminal users engaging in distributed denial-of-service (DDoS)-for-hire services.” reads the press release published by EUROPOL. “With over 75 000 warning emails and letters being sent to identified criminal users and 4 arrests, the action week also led to the takedown of 53 domains and the issuing of 25 search warrants.”

Authorities disrupted booter services by seizing servers and infrastructure used to launch attacks, limiting further harm. Access to seized databases with over 3 million user accounts enabled coordinated global actions against cybercriminals and raised awareness about the illegality of these services.
Operation PowerOFF continues with a strong prevention phase to stop future DDoS attacks. Authorities launched campaigns targeting users, including ads warning young people searching for attack tools, removal of over 100 malicious URLs, and warning messages sent via blockchains used for payments. They also updated the official website to highlight ongoing actions and raise awareness about the risks and illegality of DDoS-for-hire services.

Authorities continue dismantling global DDoS-for-hire networks under Operation PowerOFF. In August 2025, the U.S. also took down the RapperBot botnet, used for large-scale attacks across more than 80 countries since 2021.
In December 2024, law enforcement agencies operating under Operation PowerOFF disrupted 27 of the most popular platforms (including zdstresser.net, orbitalstress.net, and starkstresser.net) to launch Distributed Denial-of-Service (DDoS) attacks. The authorities also arrested three administrators of these platforms in France and Germany, and identified over 300 users.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Operation PowerOFF)
Operation PowerOFF: 75K Users of DDoS-for-Hire Services Identified and Warned
New Mirai Variant Nexcorium Hijacks DVR Devices for DDoS Attacks
Operation PowerOFF Knocks Out 75,000 DDoS Attackers and Over 50 Service Domains
A major international law enforcement campaign has hit the DDoS-for-hire ecosystem, warning more than 75,000 suspected users and disrupting the infrastructure that helped power online attacks around the world. Backed by Europol, Operation PowerOFF brought together authorities from 21 countries in a coordinated action week on 13 April 2026. The operation resulted in four arrests, […]
The post Operation PowerOFF Knocks Out 75,000 DDoS Attackers and Over 50 Service Domains appeared first on GBHackers Security | #1 Globally Trusted Cyber Security News Platform.
