
Visualização de leitura
North Carolina man pleads guilty to doxxing Supreme Court justices
European leaders unveil tentative deal for AI Act simplification, including a ban on nudification tools

The Canvas Hack Is a New Kind of Ransomware Debacle

How to Disable Google's Gemini in Chrome

Microsoft says Edge’s plaintext password behavior is “by design”
Some time ago, we discussed whether you should allow your browser to remember your passwords.
In that article we mentioned the importance of encryption.
“With a browser password manager, someone with access to your browser could see your passwords in clear text, although Windows can be set to ask for authentication (the same you use at startup of your device).”
The typical behavior of browser password managers is to store passwords encrypted on disk, tied to your user account, and protected by the operating system.
But recently, a security researcher systematically tested every major Chromium-based browser for how they handle credentials in memory. The researcher found that Edge was the only one loading the entire password vault into plaintext process memory at startup, where it remains for the duration of the session.
Chrome and other Chromium browsers were observed to only decrypt a password when needed (autofill or “show password”), not the whole vault, and to use mechanisms like app‑bound encryption for keys. Edge does not use those protections in this context.
So, the researcher decided to write a proof-of-concept (PoC) demonstrating that accessing that vault doesn’t rely on zero-days or complex exploitation. It relies on the relatively simple ability to read process memory, which does require elevated privileges.
But when the researcher reported the issue to Microsoft, the response was underwhelming. The company’s official response was that the behavior is “by design.” The reasoning most likely is that this behavior speeds up sign‑in and autofill, and attackers would already need a compromised machine or elevated access to read RAM, which Microsoft treats as out of scope for this design decision.
Which is basically true. An attacker already needs significant foothold: for example, code execution on the box and the ability to read Edge’s process memory, often requiring elevated privileges. This is not a remote, unauthenticated bug in the browser, but the design makes post‑compromise credential harvesting easier. And it’s a capability many infostealers already have.
It’s just another thing an attacker can do once they’ve compromised your machine. Combined with this academic study from 2024, which found many password managers leak plaintext passwords into memory under some conditions, it leads us to repeat our advice.
Should you allow your browser to remember your passwords?
Your browser password manager gives you ease of use, but that costs you some security. Of course, password managers aren’t foolproof either, so it’s important to decide for yourself where you store your passwords.
If you’re confident the website is safe, and anyone that can access it under your account won’t learn anything new, feel free to store the password in your browser, but disable autofill so you stay in control.
Use MFA where possible. It enormously reduces the risk should someone get hold of your password. And refrain from using the browser password manager to store your credit card details or other sensitive personally identifiable information, such as medical information.
But we’d add that, among the major browsers, Edge appears to be the weakest option if you still choose to use a built‑in password manager.
Stop threats before they can do any harm.
Malwarebytes Browser Guard blocks phishing pages and malicious sites automatically. Free, one click to install. Add it to your browser →
Researcher Shows Edge Browser Stores Saved Passwords in Plaintext
Smashing Security podcast #466: Meta sees everything, Copy Fail, and a deepfake gets hired
Thousands of Vibe-Coded Apps Expose Corporate and Personal Data on the Open Web

A Kid With a Fake Mustache Tricked an Online Age-Verification Tool

If a fake moustache can fool age checks, is the Online Safety Act working?
A report based on a survey by the UK’s Internet Matters shows that much of the responsibility for managing the online safety of children still falls on families.
The Online Safety Act came into effect in July, 2025, and the report explores what has changed in the online lives of UK families since then.
We discussed in December 2025 whether the privacy risks of age verification outweighed the enhanced child protection. While the report shows some progress, it mostly provides “an early view of how the online landscape is changing, and crucially, where it is not.”
Around half of children say they now see more age-appropriate content, and roughly four in ten parents and children feel the online world has become somewhat safer.
The online world is as much a part of a child’s environment as the physical world is. And blocking the view to parts of that world is not taken lightly. Almost half of children think age checks are easy to bypass. About a third admit to doing so recently, using tactics from fake birthdates and borrowed logins to spoofed faces and, less commonly, VPNs.
“I did catch my son [12] using an eyebrow pencil to draw a moustache on his face, and it verified him as 15 years old.”
Yet 90% of children who noticed improved blocking and reporting saw this as a good thing. Their support for these safety features is pragmatic. They point to:
- clearer rules
- restricted contact with strangers
- limits on high-risk functions
They also rate these features as helpful in reducing exposure to harmful content and interactions.
But the system is not perfect. In the month after the child protection codes came into force, almost half of children reported some online harm, including violent, hateful, and body image-related content that should be covered by the Act’s protections.
The survey also revealed that age checks are now commonplace. Over half of children said they were asked to verify their age within a recent two-month window, often on major platforms like TikTok, YouTube/Google, and Roblox, on both new and existing accounts.
The technology is improving. Platforms use facial age estimation, government ID, and third-party age assurance apps, and these are usually easy for children to complete.
However, gains in protection come with unresolved and, in some cases, growing concerns around privacy and data use, especially around age verification and AI.
Parents are worried not just about what data is collected for age checks, but whether it will be stored or reused by government or industry. This has fueled calls for central, privacy-protective solutions rather than fragmented data collection across platforms.
Because age assurance systems are both intrusive (in terms of data) and often ineffective (easy workarounds, weak enforcement), the report suggests they may not yet provide a good safety-to-privacy trade-off from a family perspective.
Obviously, the survey also didn’t capture input from adults pretending to be children to gain access to child-only spaces, a risk that parents link directly to predatory behavior.
The authors conclude that the Online Safety Act has started to reshape children’s online environments, making safety features more visible and enabling more age‑appropriate experiences in some areas.
However, the Act has not yet produced a “step change.” Harmful content remains widespread, age‑assurance is patchy and easy to circumvent, and key concerns such as time spent online, AI risks, and persuasive design remain under‑regulated.
Browse like no one’s watching.
Malwarebytes Privacy VPN encrypts your connection and never logs what you do, so the next story you read doesn’t have to feel personal. Try it free →
Google Chrome Accused of Silently Installing 4GB AI Model on User Devices
ShinyHunters’ Instructure Canvas LMS and Vimeo Breaches Impact Millions of Users
FTC bans data broker Kochava from selling sensitive location info

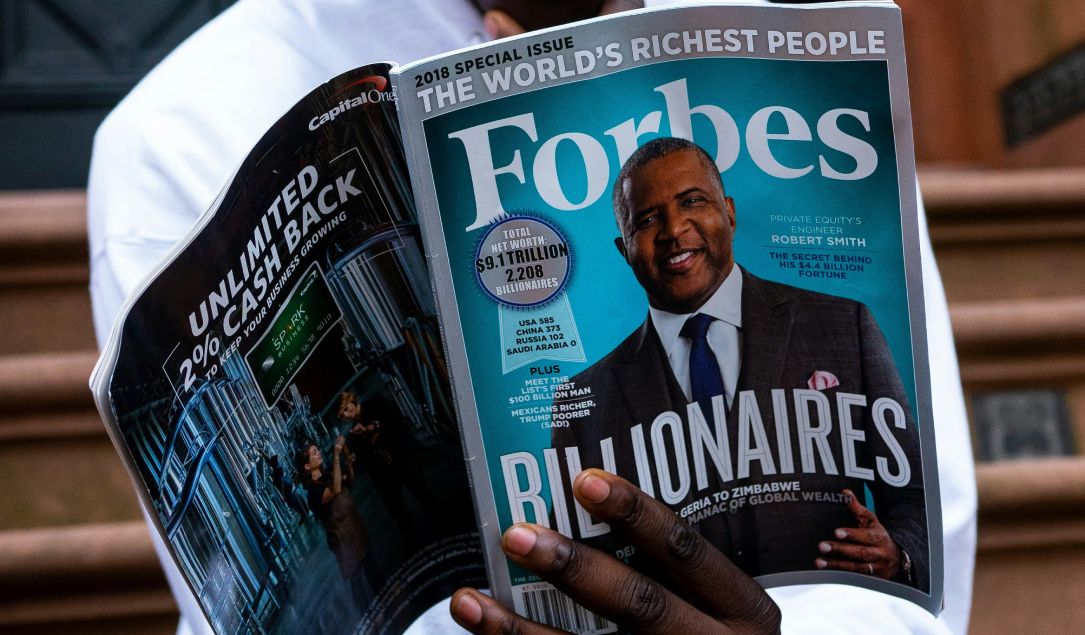
Forbes preliminarily agrees to pay $10 million to settle California wiretapping lawsuit
DHS Demanded Google Surrender Data on Canadian’s Activity, Location Over Anti-ICE Posts
