ANZ Organizations Are in the Ransomware Crosshairs— What the Dark Web Is Telling Us
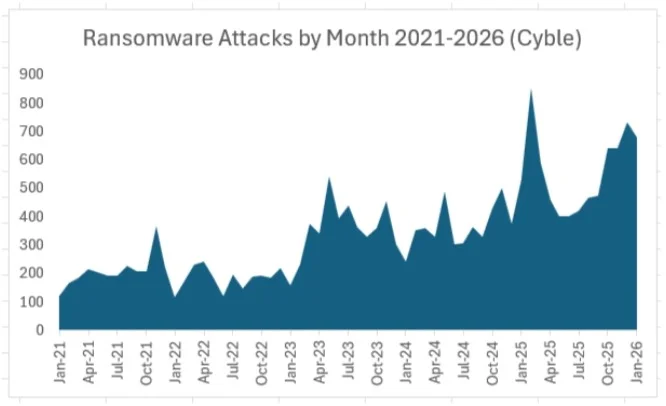
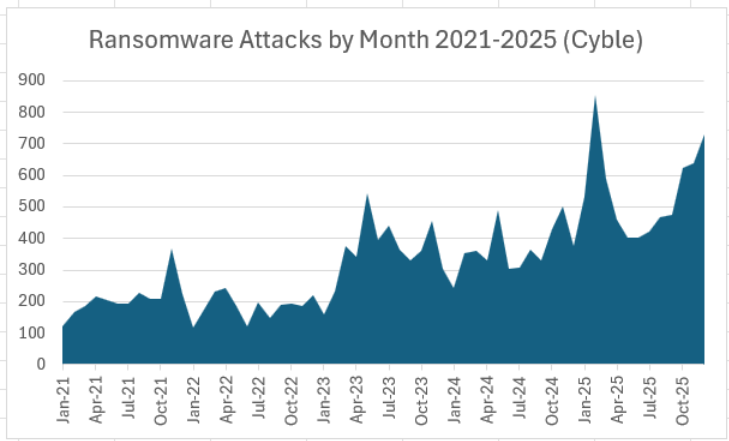
The conversation around ANZ ransomware threats has shifted noticeably over the past year. What once looked like sporadic, high-profile incidents has evolved into a sustained and structured campaign against organizations across Australia and New Zealand. Signals emerging from underground forums and marketplaces reveal a sobering reality: ransomware is no longer just a technical problem; it is an economic strategy driven by efficiency, specialization, and scale.
At the center of this shift is ransomware dark web intelligence, which paints a clear picture of attacker intent. Threat actors are not simply increasing volume; they are refining their focus. The ANZ region, with its high-value economy and deeply digitized infrastructure, has become a preferred hunting ground.
Why High-Value Economies Attract ANZ Ransomware Threats
Australia’s economic profile plays directly into the hands of ransomware operators. A strong GDP, combined with a relatively small population, creates a high-return environment. Attackers don’t need to cast a wide net; each successful breach can yield significant payouts.
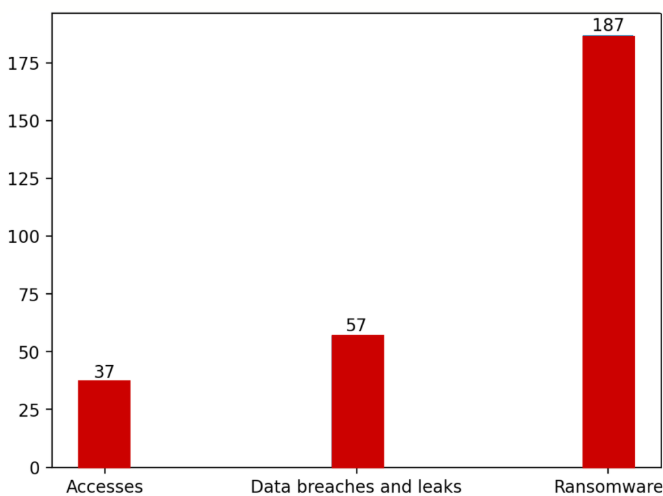
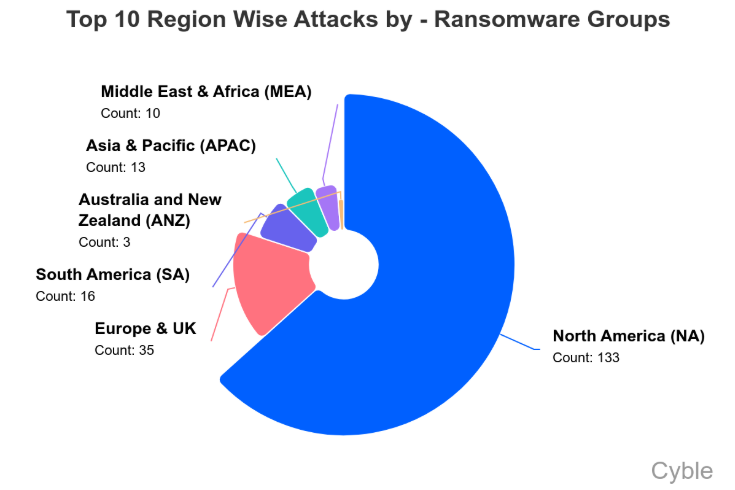
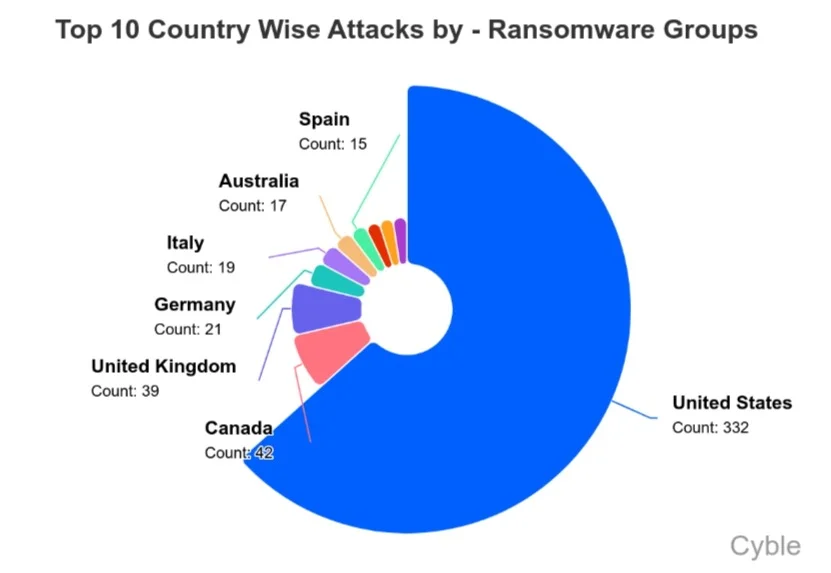
By mid-2025, 71 ransomware incidents had been publicly claimed in Australia, compared to nine in New Zealand. On the surface, those figures may seem moderate. However, when adjusted for population, the rate of ransomware attacks in Australia and New Zealand stands out globally. Even larger economies have not experienced the same intensity relative to their size.
This imbalance reflects a fundamental principle driving ANZ organizations cybersecurity risks: attackers prioritize value over volume. In practical terms, fewer victims can still mean higher profits.
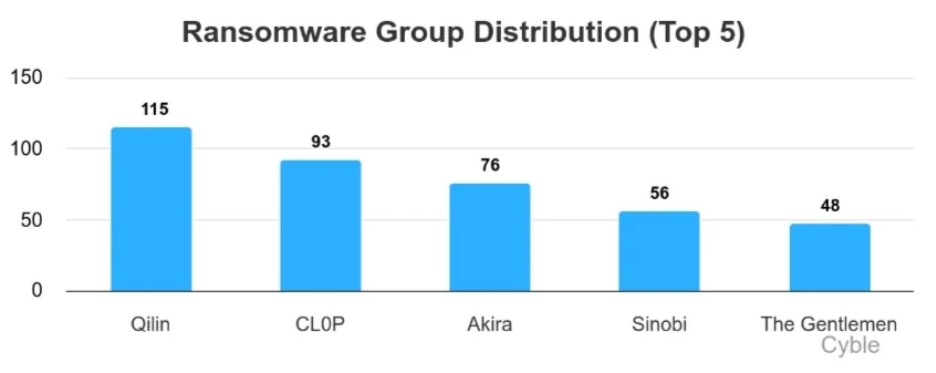
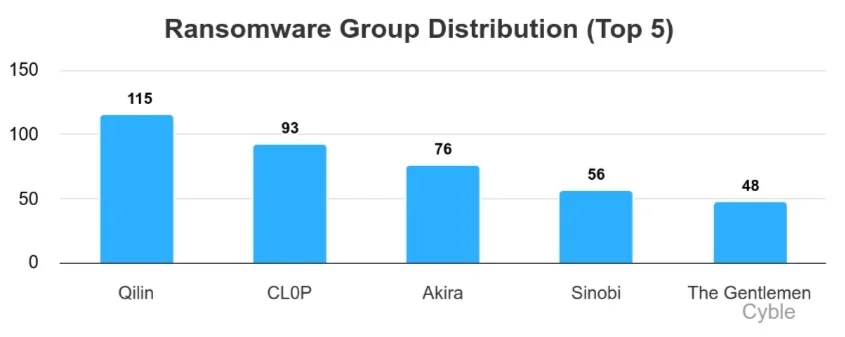
A Fragmented Threat Landscape with No Single Dominant Actor
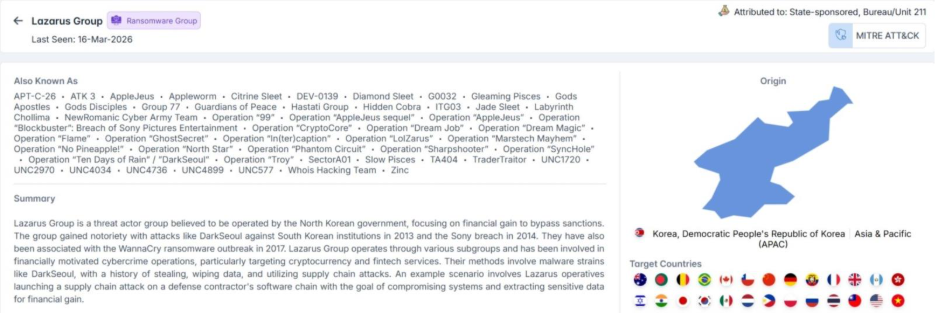
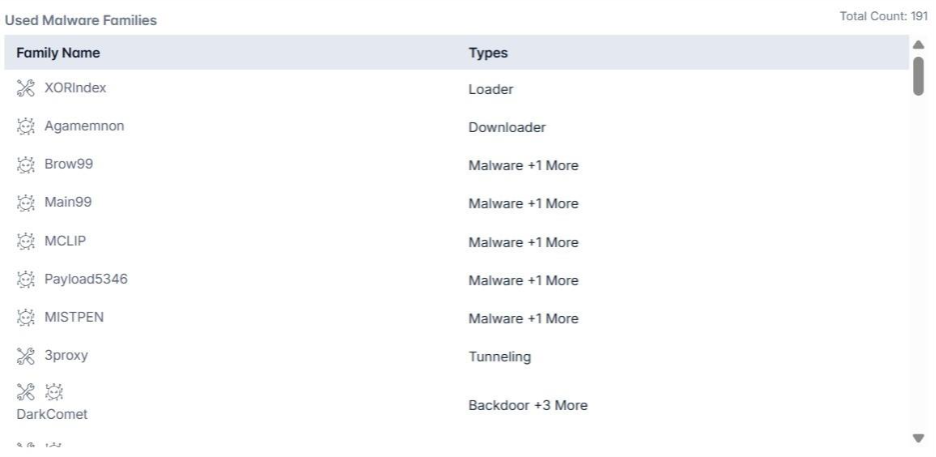
Unlike regions where one ransomware group dominates headlines, the dark web ANZ cyber threats ecosystem is notably fragmented. Multiple groups, including Qilin, Akira, INC, Lynx, and Dragonforce, operate concurrently, each claiming a similar share of attacks.
This decentralization complicates defense strategies. Organizations are not facing a predictable adversary with a consistent playbook. Instead, they must prepare for a rotating cast of threat actors, each bringing different techniques, timelines, and negotiation tactics.
From a ransomware dark web intelligence perspective, this fragmentation signals a competitive market. Threat actors are actively testing sectors, probing defenses, and adapting quickly based on what works.
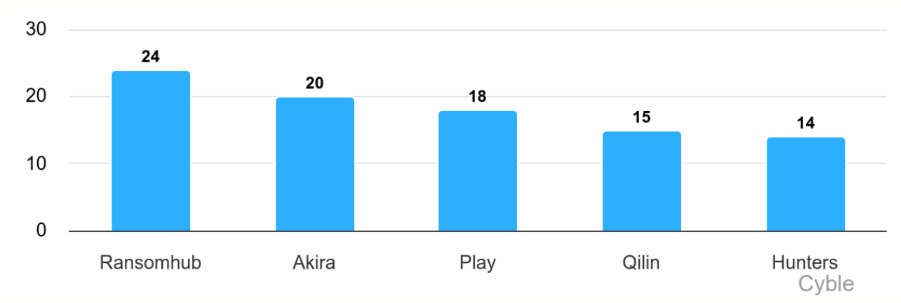
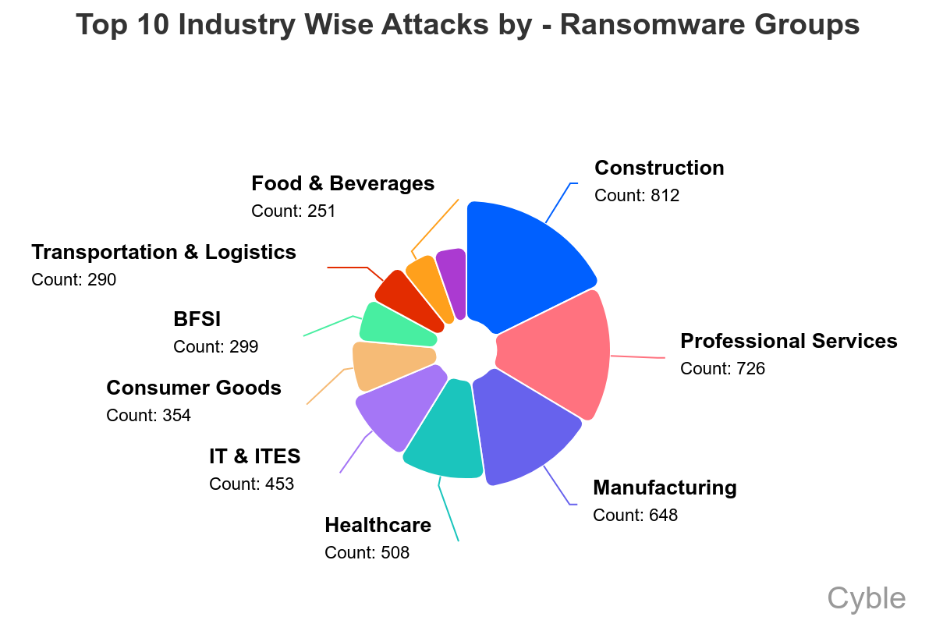
Industries Under Sustained Pressure
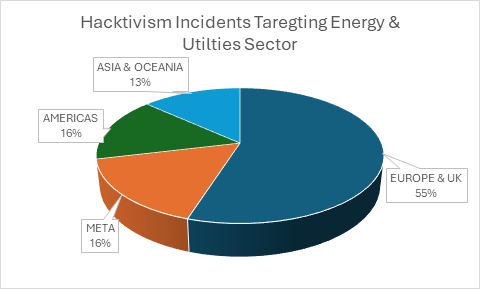
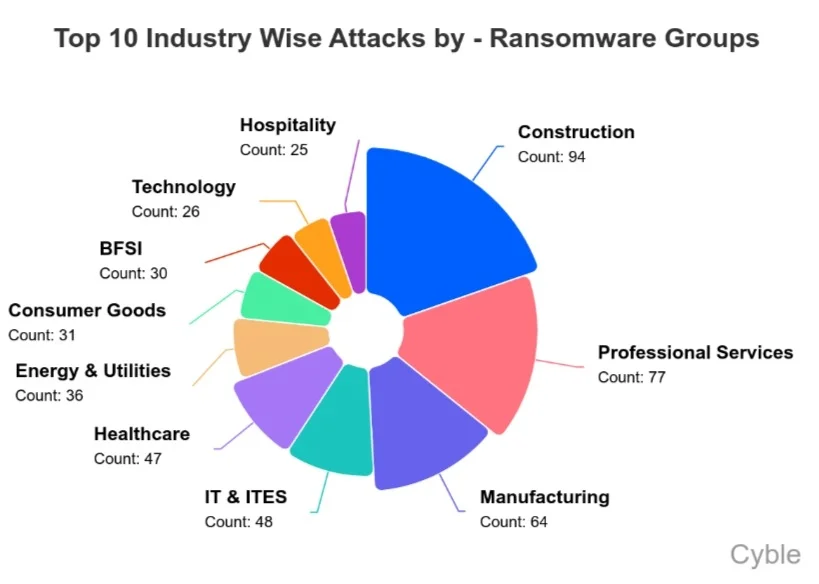
The distribution of ANZ ransomware threats is far from uniform. Certain sectors continue to absorb the majority of attacks due to the nature of their operations.
Healthcare and professional services sit at the top of the list. In healthcare, the urgency of patient care creates a near-zero tolerance for downtime, increasing the likelihood of ransom payments. Professional services firms, on the other hand, hold large volumes of sensitive client data, making them lucrative targets.
However, the scope is broader than these two sectors alone. Aviation software providers, pharmaceutical companies, engineering firms, and even steel manufacturers have all been affected. This pattern reinforces a key insight: ransomware attacks in Australia and New Zealand are opportunistic but calculated, targeting environments where disruption carries tangible consequences.
Notable Incidents Reveal Tactical Evolution
Several incidents in 2025 highlight how attackers are evolving their methods.
The Akira group compromised an Australian industrial technology provider, exfiltrating approximately 10GB of sensitive data, including financial records and employee identification documents. This case highlights the growing overlap between ransomware and critical infrastructure risk.
In another breach, a political organization suffered exposure to communications, identity records, and financial data, highlighting that ANZ organizations' cybersecurity risks extend beyond the private sector.
Meanwhile, Dragonforce leaked over 100GB of data from an engineering firm, including technical drawings and internal reports. The long-term implications of such intellectual property theft often exceed immediate financial damage.
These cases share a common thread: encryption is no longer the sole objective. Data exfiltration and double extortion have become standard practices.
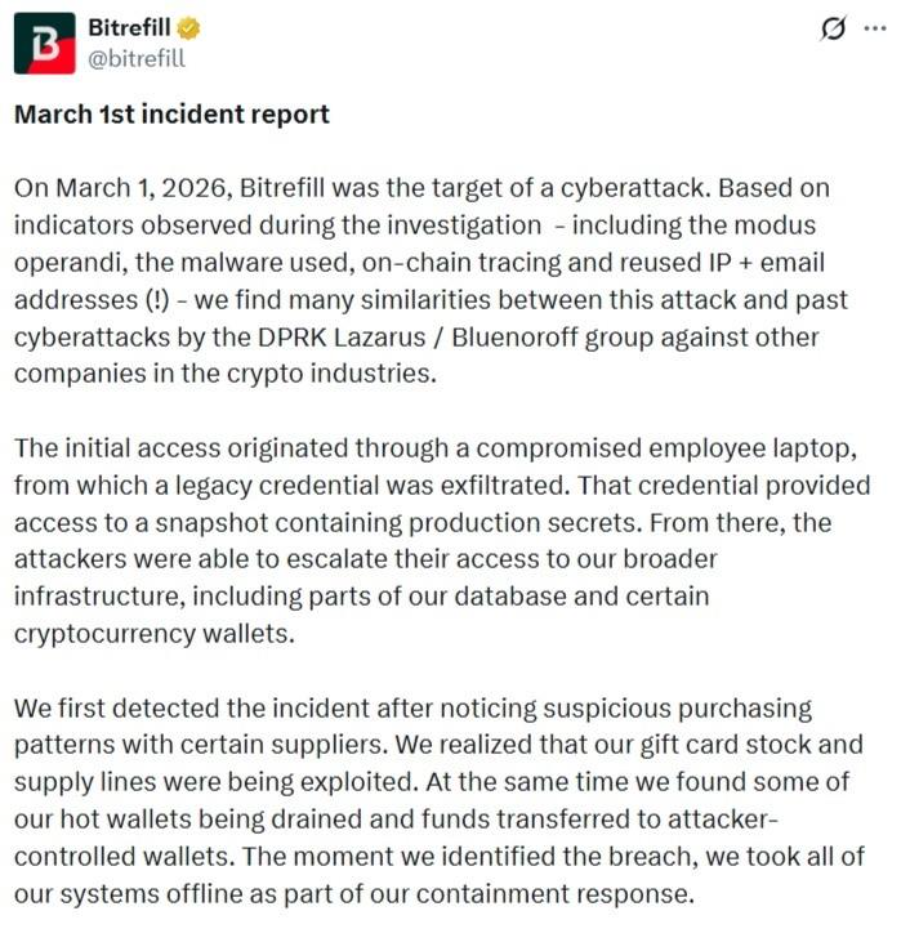
The Rise of Initial Access Brokers
One of the most important developments in shaping dark web ANZ cyber threats is the growth of the initial access market. In 2025 alone, 92 instances of compromised access sales were observed across Australia and New Zealand.
Retail organizations accounted for roughly 34% of these cases, followed by BFSI and professional services. The implications are significant. Attackers no longer need to breach networks themselves; they can simply purchase access.
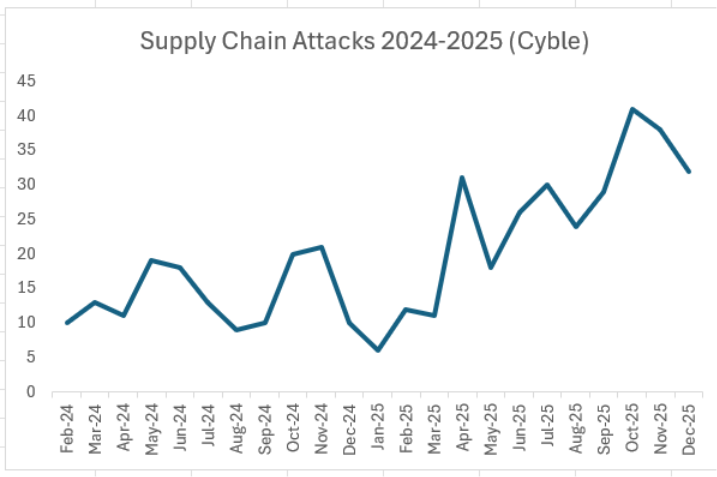
This shift has redefined how ANZ ransomware threats materialize. The most complex phase of an attack—initial intrusion—is now outsourced, accelerating timelines and increasing overall attack volume.
It also introduces indirect risk. Organizations may be compromised through vendors, partners, or shared platforms, expanding the attack surface beyond traditional boundaries.
Ransomware-as-a-Service and the Scaling Problem
The emergence of affiliate-driven models, particularly groups like INC Ransom, has further amplified ransomware attacks in Australia and New Zealand. Operating under a Ransomware-as-a-Service structure, these groups separate responsibilities: affiliates handle intrusions, while core operators manage ransom negotiations.
This model enables rapid scaling. Multiple attacks can be executed simultaneously, each leveraging shared infrastructure and tooling.
INC Ransom’s activity across healthcare and professional services highlights how effective this approach has become. Their operations often involve credential compromise, privilege escalation, lateral movement, and eventual deployment of ransomware—frequently paired with data exfiltration.
From a ransomware dark web intelligence standpoint, this reflects a mature ecosystem where roles are specialized, and efficiency is maximized.
A Regional Problem with Cross-Border Impact
Although Australia is the primary target, the broader region is not immune. A ransomware attack on Tonga’s Ministry of Health disrupted national healthcare services, while a major breach in New Zealand’s healthcare sector involved both data theft and system encryption.
These incidents reinforce the interconnected nature of ANZ organizations' cybersecurity risks. Threat actors operate without regard for national boundaries, shifting focus wherever defenses appear weakest.
Common Entry Points and Techniques
Despite the evolving ecosystem, many attack methods remain consistent. Spear-phishing campaigns, exploitation of unpatched systems, and the use of stolen credentials continue to dominate.
Once inside, attackers often rely on legitimate tools—file compression utilities, remote management software, and standard data transfer mechanisms—to blend into normal operations. This “living off the land” approach makes detection significantly more difficult.
From Defense to Resilience
The steady rise of ANZ ransomware threats signals a need for strategic change. Perimeter-based defenses are no longer sufficient in an environment where access can be purchased, and attacks can be outsourced.
As access is bought and attacks are outsourced, organizations must shift toward stronger identity controls, continuous monitoring, rapid patching, and tighter third-party risk management.
Cybersecurity is no longer just about prevention—it’s about resilience. Attacks are inevitable, but their impact doesn’t have to be. Cyble helps organizations stay ahead with AI-powered threat intelligence, dark web monitoring, and predictive defense through its AI-native platform, Cyble Blaze.
Stay ahead of ransomware threats—book a free demo and build a more resilient security posture.
The post ANZ Organizations Are in the Ransomware Crosshairs— What the Dark Web Is Telling Us appeared first on Cyble.