IR Trends Q1 2026: Phishing reemerges as top initial access vector, as attacks targeting public administration persist
- Phishing reemerged as the most observed means of gaining initial access, accounting for over a third of the engagements where initial access could be determined. Phishing has not been the top vector for initial access since Q2 2025.
- Public administration and health care tied as the most targeted industry verticals, each accounting for 24 percent of all engagements. This is the third consecutive quarter where public administration has been the most targeted industry vertical.
- Pre-ransomware incidents made up just 18 percent of engagements this quarter, and we did not observe any ransomware deployment due to early and swift mitigation from Cisco Talos Incident Response (Talos IR). This is a slight increase from last quarter but overall very low compared to Q1 and Q2 2025, when we observed ransomware in 50 percent of engagements.

Watch this video to see Talos experts break down the trends and offer guidance for defenders.
AI tool leveraged in phishing campaign
Talos IR responded to a campaign that leveraged phishing, the most common means of initial access this quarter, to compromise the most targeted industry vertical this quarter: public administration. Notably, the actors leveraged the Softr AI-based web application development service, marking the first time we have documented the use of a specific AI tool by an adversary in a phishing campaign. Softr was used to generate a credential harvesting page targeting users’ Microsoft Exchange and Outlook Web Access (OWA) accounts.
State-sponsored and criminal actors have been observed abusing large language models (LLMs) to aid in the development of phishing lures, malicious scripts, and other tasks. DDoS-as-a-service actors have adopted AI algorithms for defense evasion and attack orchestration. While this is the first time we have documented the use of a specific AI tool in a Talos IR incident, we have moderate confidence that malicious actors have used Softr’s AI-powered web application creation platform since at May 2023, based on Cisco Umbrella data and other telemetry, and have done so with increasing frequency to date.
This incident demonstrates how AI tools can lower the barrier to entry for less sophisticated actors and/or accelerate the speed of phishing and credential-harvesting campaigns. Using a form template and the “vibe coding” feature, a phishing page like the one used in this attack could be quickly created with a few AI prompts and no code. Phishing pages built with Softr can direct data to a disposable external data store, such as Google Sheets, and send alerts for new captures via email — all without code.
Crimson Collective seen for the first time
Talos IR experienced its first case involving Crimson Collective, a cyber extortion group that appeared in September 2025. This attack highlighted the use of valid accounts for initial access, the second most commonly observed means of initial access this quarter. This attack also notably involved targeting exploit weaknesses, the second-most observed security weakness, accounting for 25 percent of all engagements. We attribute this activity to Crimson Collective based on IPs associated with the group that were used to scan the victim's ASA firewalls, as well as an overlap of observed tactics and techniques with publicly reported Crimson Collective attacks.
The incident began when a GitHub Personal Access Token (PAT) was inadvertently published on a public-facing website, exposing the organization to adversaries for several months. Upon obtaining access, the adversary used TruffleHog, an open-source tool commonly utilized by security professionals, to scan thousands of victim GitHub repositories for additional secrets and sensitive information. This approach allows attackers to perform reconnaissance without triggering suspicion, as they are leveraging standard, legitimate tools. The attacker’s discovery of client secrets through TruffleHog enabled further access to the victim’s Azure cloud storage, where they used Microsoft Graph API calls to authenticate, explore, and exfiltrate data. The abuse of legitimate cloud APIs demonstrates a growing trend where threat actors use native platform functionality to blend into normal user activity, making detection more challenging.
In addition to exfiltrating data, the adversary attempted to inject malicious code into multiple GitHub repositories. This code was designed to harvest any new secrets committed in the future, sending them to adversary-controlled infrastructure. Though these attempts were largely thwarted by the expiration of targeted secrets and effective security controls, the tactic reflects an emerging trend of supply chain and development environment attacks.
Ransomware trends
Ransomware experiences slight increase, remains low overall
Pre-ransomware incidents made up just 18 percent of engagements this quarter, and we did not observe any ransomware encryption due to early and swift mitigation from Talos IR. This is a slight increase from last quarter, when ransomware and pre-ransomware collectively comprised 13 percent of engagements, but overall very low compared to Q1 and Q2 2025, when we observed ransomware in 50 percent of engagements. Attribution is challenging in pre-ransomware events because there are no encryptors or ransom notes, but we assess that Rhysida ransomware and MoneyMessage ransomware accounted for two of the engagements.
While we did not observe many active and prolific ransomware-as-a-service (RaaS) operations, like Qilin or Akira, this likely does not indicate these major players are decreasing operations, as their data leak sites remain consistently active.
Rhysida ransomware actors use uncommon backdoor, Meowbackconn
Talos IR responded to a ransomware incident where the adversary attempted to deploy Rhysida ransomware. While the attack was mitigated in the pre-ransomware stage, we attribute this activity with moderate confidence to Rhysidabased on observed infrastructure that is associated with Rhysida activity and the use of Gootloader, which is commonly leveraged in Rhysida attacks during initial access. Notably, the actors deployed proxy-related DLLs (e.g., “meow_eu.dll”), which we assess were likely related to MeowBackConn, an uncommon backdoor that is closely associated with Gootloader, based on public reporting.
This attack represents several trends that we observed throughout Talos IR engagements in Q1 2026. The environmental weaknesses that enabled this intrusion — exposed WinRM management ports, over-privileged service accounts, and critical logging gaps — directly echo this quarter’s most prominent security weaknesses, including vulnerable or exposed infrastructure, accounting for 25 percent of engagements. Furthermore, the adversary’s use of Remote Desktop Protocol (RDP) for lateral movement is consistent with RDP being the top technique for lateral movement for the previous two quarters (Q3 and Q4 2025).
Targeting
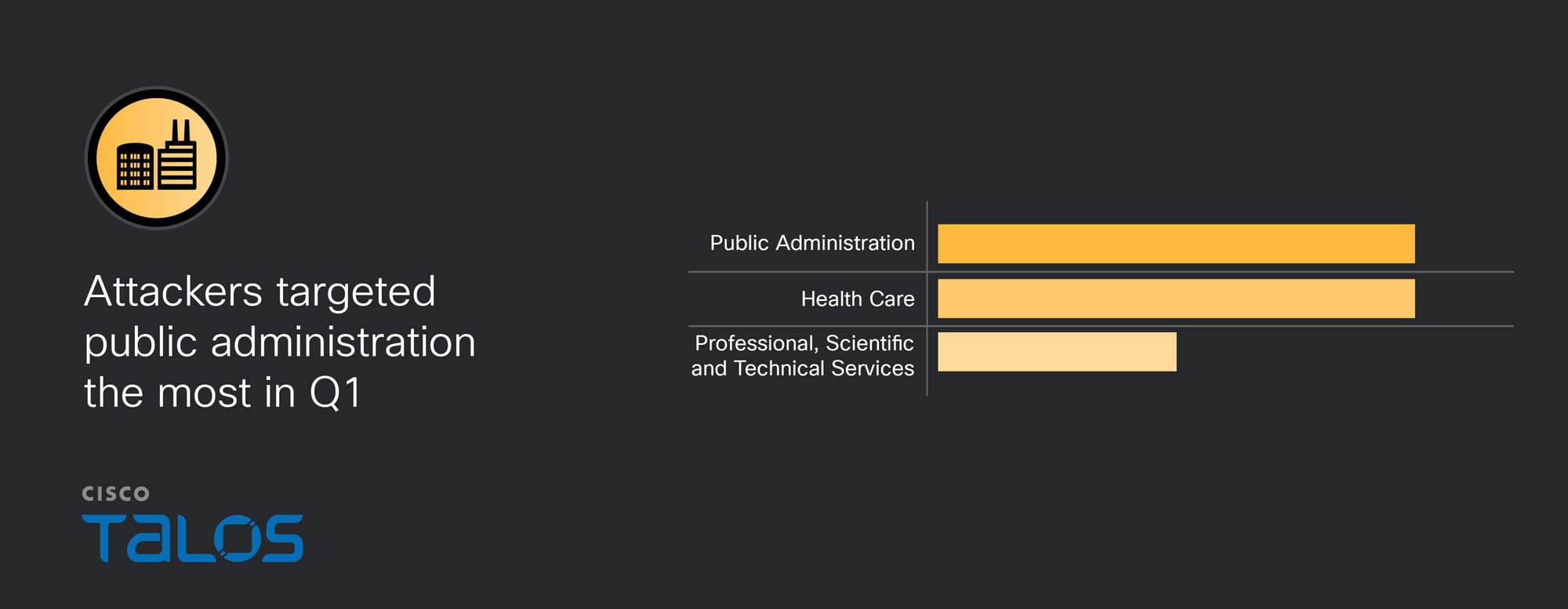
Public administration and health care were tied as the most targeted industry verticals. Notably, Q3 2025 marked the first time public administration emerged as the most targeted sector in Talos IR engagements, and it has retained that position since. Organizations within the public administration sector are attractive targets as they are often underfunded and use legacy equipment. These entities may have access to sensitive data as well as a low downtime tolerance, making them attractive to financially motivated and espionage-focused threat groups.
Initial access
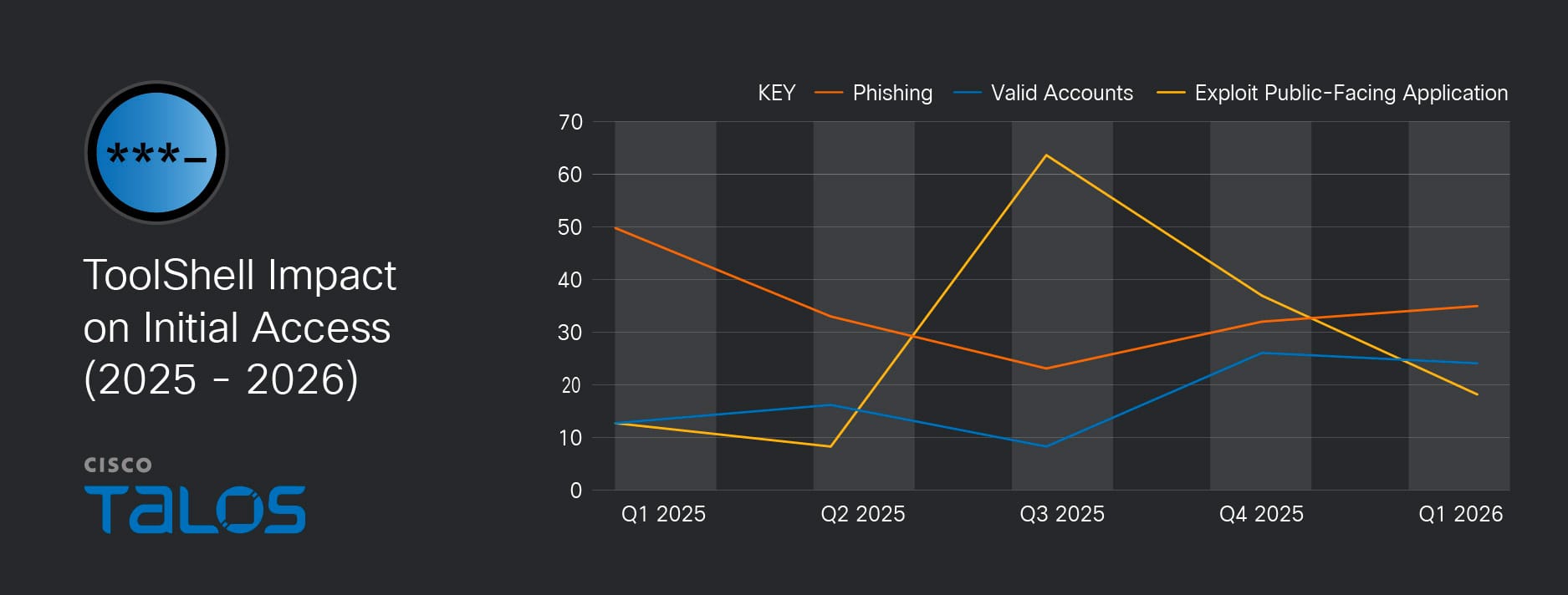
Phishing reemerged as the most observed means of gaining initial access, accounting for over a third of the engagements where initial access could be determined. Phishing was the top initial access vector in the first half of 2025, at which point it was surpassed by exploitation of public-facing applications, likely due to the widespread exploitation of vulnerabilities in on-premises Microsoft SharePoint servers, collectively referred to as ToolShell. Since then, we have observeda steady decrease in the exploitation of public-facing applications as an initial access vector from a high of 62 percent to only 18 percent in Q1 2026. Similarly, in this quarter, valid accounts returned to its pre-ToolShell baseline as the second most observed means of gaining initial access, comprising 24 percent of Talos IR engagements. We assess the decline in ToolShell exploitation is likely due to the widespread availability of emergency patches and enhanced security detections, highlighting the importance of timely patching.
Recommendations for addressing top security weaknesses
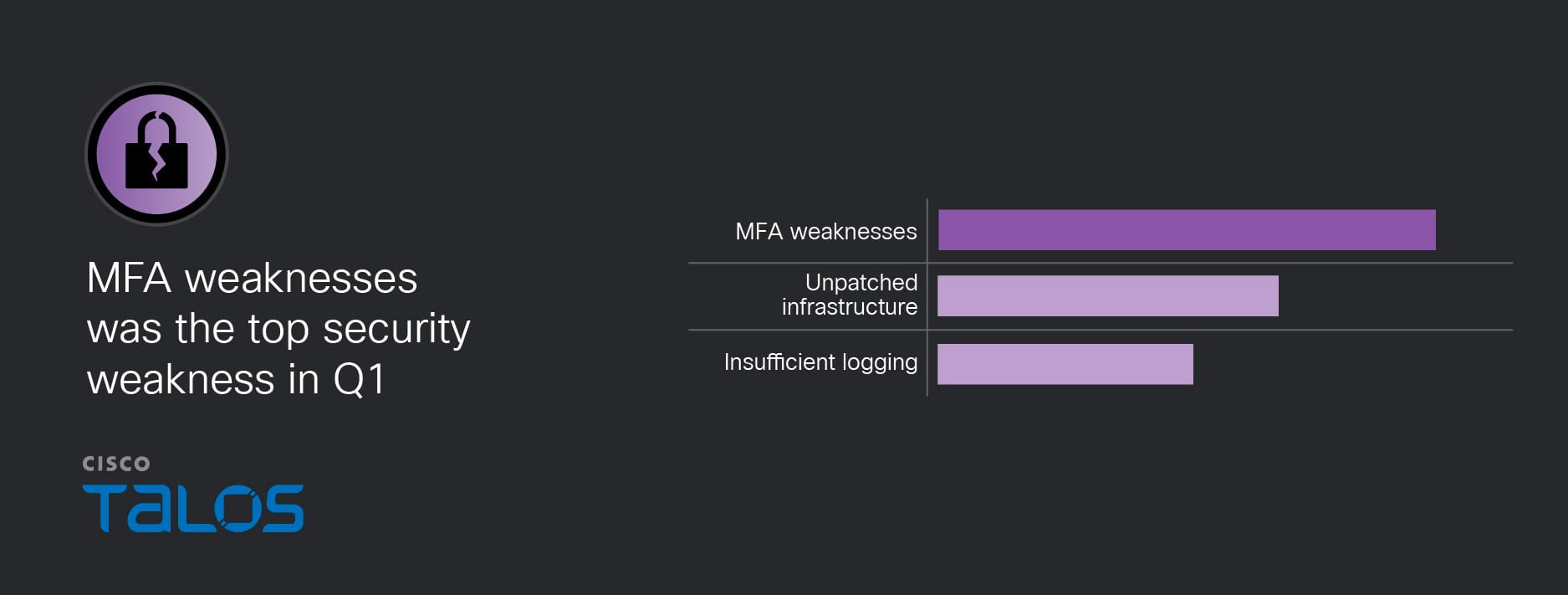
Implement properly configured MFA and other access control solutions
35 percent of engagements this quarter involved multi-factor authentication (MFA) weaknesses, an increase from last quarter. This includes incidents where threat actors bypassed MFA and where MFA was either missing or only partially enabled, particularly on remote access services. Adversaries were able to bypass MFA by registering new devices to previously compromised accounts, and in one instance, by configuring Outlook clients to connect directly to Exchange servers, circumventing MFA requirements. Addressing these weaknesses, especially by restricting self-service MFA enrollment and enforcing strong, centralized authentication policies, is essential to reducing risk and strengthening organizational resilience.
Conduct robust patch management
Vulnerable or exposed infrastructure was another top security weakness accounting for 25 percent of all engagements, a slight decrease from last quarter. This included exploiting a vulnerability (CVE-2025-20393) in the Spam Quarantine feature of Cisco AsyncOS Software for Cisco Secure Email Gateway and Cisco Secure Email and Web Manager, as well as a vulnerability (CVE-2023-20198) in the web UI feature in Cisco IOS XE Software. Talos also observed exposed management ports (such as WinRM open to the internet), which enabled rapid attacker movement and reconnaissance.
Configure centralized logging capabilities across the environment
Finally, 18 percent of engagements this quarter involved organizations with insufficient logging capabilities, which hindered investigative efforts. Understanding the full context and chain of events performed by an adversary on a targeted host is vital not only for remediation but also for enhancing defenses and addressing any system vulnerabilities for the future. To address this issue, Talos IR recommends organizations implement a security information and event management (SIEM) solution for centralized logging. In the event an adversary deletes or modifies logs on the host, the SIEM will contain the original logs to support a forensics investigation. Additionally, Talos IR offers a Log Architecture Assessment service, which provides a focused review of an organization’s logs and overall log strategy to identify gaps and offer recommendations that give a complete view of the security environment and strengthen incident response readiness
MITRE ATT&CK appendix
The tables below represent the MITRE ATT&CK techniques observed in this quarter’s IR engagements and includes relevant examples and the number of times seen. Given that some techniques can fall under multiple tactics, we grouped them under the most relevant tactic based on the way they were leveraged. Please note that this is not an exhaustive list.
Key findings from the MITRE ATT&CK framework include:
- Phishing was the top method of initial access, replacing exploitation of public-facing applications which was dominant in the prior two quarters.
- Web-based C2 was the most common C2 pattern. Application Layer Protocol over web protocols was observed most often, indicating adversaries frequently blended C2 into normal-looking traffic.
- Lateral movement primarily relied on common remote administration channels. SMB/Windows Admin Shares was the top lateral movement technique, with WMI and RDP also heavily used, suggesting attackers repeatedly leveragedstandard enterprise remote management paths once inside. RDP was the top technique for lateral movement in the prior two quarters.
- Defense evasion frequently focused on weakening visibility and endpoint protections. Impair defenses by disabling/modifying tools appeared multiple times, alongside log/trace reduction behaviors (e.g., clear command history and file deletion), indicating a recurring emphasis on reducing detection and forensic evidence.
Tactic | Technique | Example | Estimated times observed |
Reconnaissance | T1589.002: Gather Victim Identity Information: Email Addresses | The adversary enumeratedinternal processes and identifiedvendor emails to facilitate their fraudulent ordering scheme. | 1 |
| T1595: Active Scanning
| The adversary scanned public-facing websites to understand the target environment. | 2 |
| T1593: Search Open Websites/Domains | The adversary scanned the web to obtain Github PATs. | 1 |
Initial access | T1566: Phishing | The adversary used malicious emails and social engineering to compromise user accounts and facilitate fraudulent purchase orders. | 5 |
| T1189: Drive-by compromise | The adversary registered several domains that masquerade as being related to VMware, and manipulated the SEO to show them at the top when searching for keywords such as VMware | 3 |
| T1078: Valid Accounts | The adversary successfully gained access to the environment by using compromised user credentials | 4 |
| T1190: Exploit public-facing applications | Two internet facing Linux servers running Apache and an LMS application were targeted. | 3 |
Execution | T1204.002: User Execution: Malicious File | The victim downloaded a malicious installer on their personal host, connected the host to their company’s network, transferred the malware to their primary domain controller, then executed the malware. | 3 |
| T1204.001: User Execution: Malicious link | The victim clicked on a link that led to a fake DocuSign document hosted on adobe[.]com | 5 |
| T1059.001: Command and Scripting Interpreter: PowerShell | The adversary used PowerShell commands and scripts for execution. | 4 |
| T1059.006: Command and Scripting Interpreter: Python | The adversary used automated Python scripts to interact with the environment. | 1 |
| T1059.005: Command and Scripting Interpreter: MSHTA | The adversary attempted to use mshta.exe to retrieve and execute a remote malicious payload from an external URL. | 1 |
Persistence | T1556.006: ModifyAuthentication Process: Multi-Factor Authentication | The adversary registered their own malicious MFA devices to maintain access to compromised accounts. | 2 |
| T1219: Remote Access Software | The adversary installed and used AnyDesk for unauthorized remote access. | 1 |
| T1053.005: Scheduled Task/Job: Scheduled Task | The adversary configured tasks to run on a schedule or at system startup. | 1 |
| T1505: Server Software Component | The adversary installed malware on breached devices to facilitateremote command execution via HTTP. | 1 |
Privilege escalation | T1068: Exploitation for Privilege Escalation | The adversary escalated to SYSTEM level privileges, which may have provided access to cached credentials in memory or registry hive. | 1 |
| T1548: Abuse Elevation Control Mechanism | The adversary used ExecutionPolicy Bypass in PowerShell and attempted to add users to the local Administrators group. | 1 |
| T1078 Valid Accounts | The adversary bypassed standard access controls by using compromised accounts with existing high-level privileges. | 1 |
Defense evasion | T1070.003: Indicator Removal on Host: Clear Command History | The adversary used the terminal emulator "ConEmu" to run commands, intentionally avoiding log generation. | 2 |
| T1070.001: Indicator Removal: Clear Windows Event Logs | The adversary deleted logs on compromised devices to limit forensic findings. | 1 |
| T1556: ModifyAuthentication Process | The adversary set up an Outlook client Outlook client to connect to the Exchange Server and was able to send messages via that path which bypasses the requirement for MFA via Duo. | 1 |
| T1562.001: Impair Defenses: Disable or Modify Tools | The adversary was able to uninstall EDR agents from hosts and attempted to delete Windows Defender policies. | 4 |
Credential access
| T1003.002: OS Credential Dumping: Security Account Manager | The adversary saved SAM and SYSTEM registry hives to extract local account hashes. | 2 |
| T1003.003: OS Credential Dumping: NTDS | The adversary dumped the ntds.dit file from Domain Controllers to obtain domain-wide credential hashes. | 1 |
| T1003.005: Cached Domain Credentials | The adversary gained NT hashes for multiple domain accounts from cached logon information. | 1 |
| T1557: Adversary-in-the-Middle | The adversary used an AiTMproxy to capture credentials and session tokens. | 1 |
Discovery | T1087.003: Account Discovery: Email Account | The adversary used Graph API calls to verify long lists of email addresses and retrieve associated user GUIDs. | 1 |
| T1580: Cloud Infrastructure Discovery | The adversary performed enumeration of the environment, including gathering OneDrive metadata (drive IDs and child item counts) and user roles. | 1 |
| T1069.002: Permission Groups Discovery: Domain Groups | The adversary used commands like net group "domain admins" /domain to find high-privilege accounts.
| 1 |
| T1526: Cloud Service Discovery | The adversary ran the legitimate cybersecurity tool TruffleHog to discover repositories containingclient secrets and personal information. | 1 |
Lateral movement | T1021.002: Remote Services: SMB/Windows Admin Shares | The adversary used PsExec(communicated over SMB) to move laterally from the compromised domain controller to other servers. | 4 |
| T1047: Windows Management Instrumentation | The adversary used PowerShell scripts to leverage WMI (Get-WmiObject) to query remote computers. | 3 |
| T1021.001: Remote Services: Remote Desktop Protocol | The adversary used RDP connections between hosts. | 3 |
Collection | T1530: Data from Cloud Storage Object | The analysis of M365 Audit Logs showed multiple FileAccessedand FileDownloaded events for documents stored in SharePoint and OneDrive. | 1 |
| T1040 Network Sniffing | The adversary executed monitor capture commands on specific interfaces to intercept and capture network traffic. | 1 |
Command and control | T1071.001: Application Layer Protocol: Web Protocols | The adversary used MeshAgentto communicate with the C2 server over WebSockets. | 5 |
| T1102: Web Service | The adversary leveraged a Telegram URL to issue instructions and download links. | 1 |
| T1572: Protocol Tunneling | The adversary used a second-stage script to create an HTTPS tunnel directly to the C2 system. | 1 |
| T1201: Traffic Signaling | The adversary communicated with external infrastructure using regular beaconing or other signaling patterns to maintain C2 or check in with their C2 server. | 1 |
Exfiltration | T1567.002: Exfiltration Over Web Service | The adversary accessed and exfiltrated internal data, specifically SharePoint files, via web-based channels. | 1 |
| T1041: Exfiltration Over C2 Channel | The adversary exfiltrated approximately 2,500 client secrets and personal information. | 2 |
Impact | T1657: Financial Theft | The adversary used company resources to place orders totaling hundreds of thousands of US dollars for various products which were successfully delivered. | 1 |
| T1486 Data Encrypted for Impact | The adversary encrypted victim data. | 1 |
| T1531 Account Access Removal | The adversary disabled admin accounts and deleted service accounts in the Active Directory (AD) and Azure | 1 |
Software | Rhysida | A RaaS, known for posing as a cybersecurity team that “helps” its victims identify security weaknesses in their networks. | Pre-ransomware engagement |
| SocGholish | A JavaScript-based loader malware that has been used since at least 2017, primarily for initial access. | 1 |
| Money Message | A ransomware that emerged in March 2023, and is capable of targeting Windows and Linux systems (including VMware ESXiservers). | Pre-ransomware engagement |



