Threat Landscape March 2026: Ransomware Dominance, Access Brokers, Data Leaks, and Critical Exploitation Trends

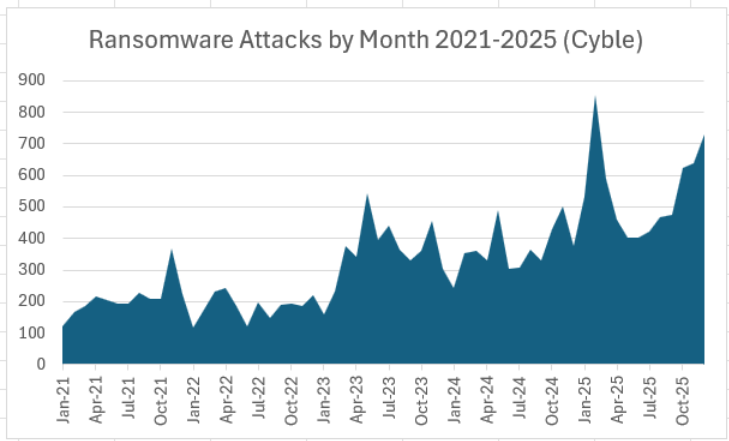
Cyble Research & Intelligence Labs (CRIL) in its monthly threat landscape analysis observed a highly active threat environment throughout March 2026, shaped by large-scale ransomware campaigns, persistent data breach activity, growing initial access brokerage markets, and exploitation of critical vulnerabilities affecting widely deployed enterprise systems.
Threat actors continued to prioritize financial extortion, credential access, and operational disruption, while increasingly targeting sectors rich in sensitive data or dependent on business continuity.
Quick Summary
Key threat trends identified during March 2026 include:
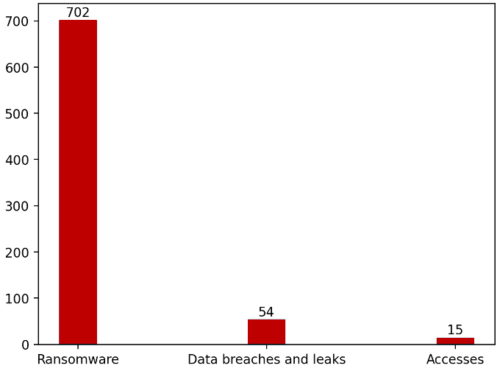
- 702 ransomware attacks recorded globally.
- 54 major data breach and leak incidents observed.
- 20 compromised access sale listings tracked across cybercrime forums.
- High concentration of attacks against Professional Services, Manufacturing, Retail, and Government sectors.
- Continued exploitation of vulnerabilities listed in CISA’s Known Exploited Vulnerabilities (KEV) catalog.
These trends indicate a mature cybercriminal ecosystem where access brokers, ransomware operators, and data leak actors increasingly operate in parallel.
Ransomware Activity Remained the Dominant Threat
CRIL recorded 702 ransomware attacks worldwide in March 2026, reflecting sustained aggression from both established groups and emerging operators.
Top Ransomware Groups
Qilin, Akira, The Gentlemen, Dragonforce, and INC Ransom were the top five most active ransomware actors in March 2026.
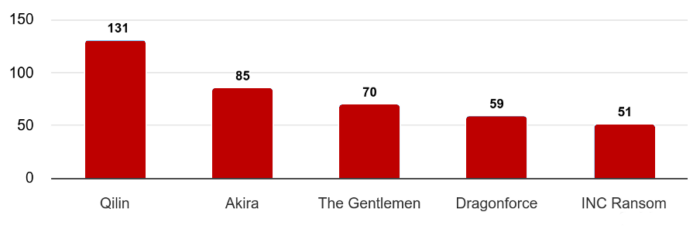
Together, the top five groups accounted for more than 56% of observed ransomware activity, highlighting strong operational scale and affiliate ecosystems.
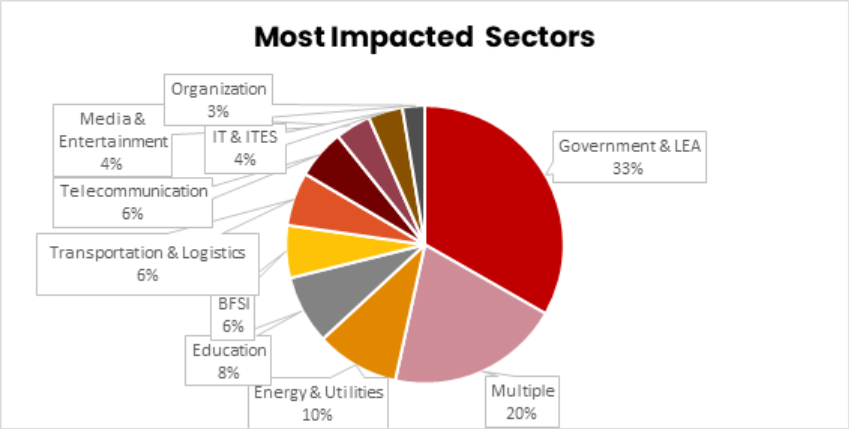
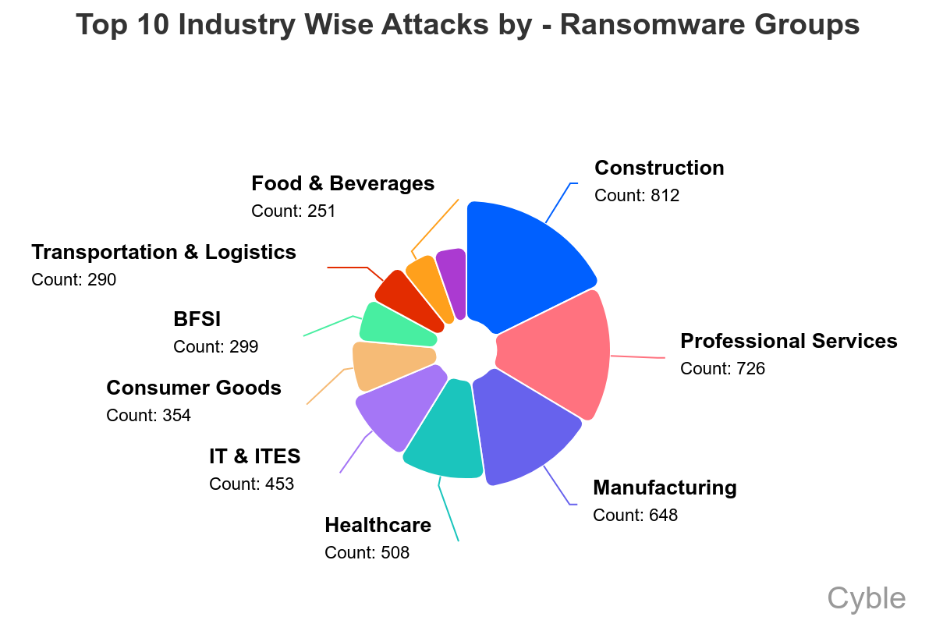
Most Targeted Industries
Construction, Professional Services, Manufacturing, Healthcare, and Energy & Utilities were the most targeted sectors by ransomware actors in March 2026.
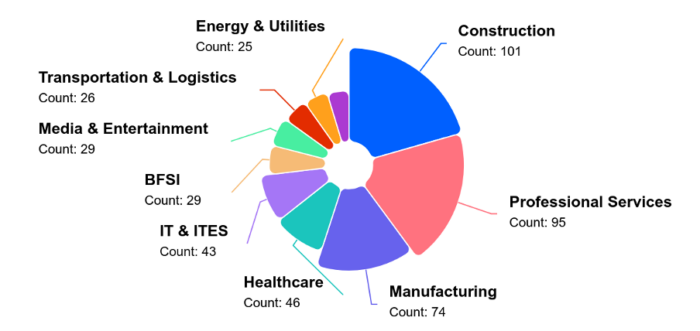
Threat actors continued using data theft + operational disruption as dual-extortion pressure tactics.
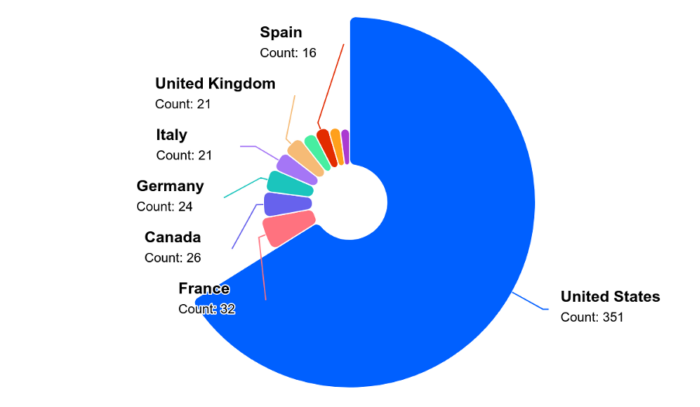
And when it came to country-wise split-up, the United States remained the focal point amid the ongoing geopolitical issues with Iran.
Compromised Access Market Expanded
CRIL tracked 20 distinct incidents involving the sale of unauthorized network access on underground forums.
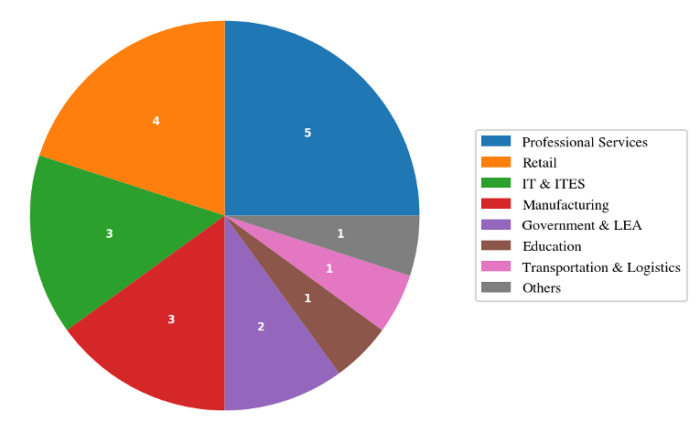
Most Targeted Sectors
- Professional Services – 25%
- Retail – 20%
- IT & ITES
- Manufacturing
Leading Access Sellers
A small group of actors dominated this market:
- vexin
- holyduxy
- algoyim
These three actors were responsible for over 55% of observed access listings.
This reinforces the role of access brokers as upstream enablers for ransomware, espionage, and fraud operations.
Data Breaches and Leak Markets Remained Active
CRIL observed 54 significant breach and leak incidents during the month.
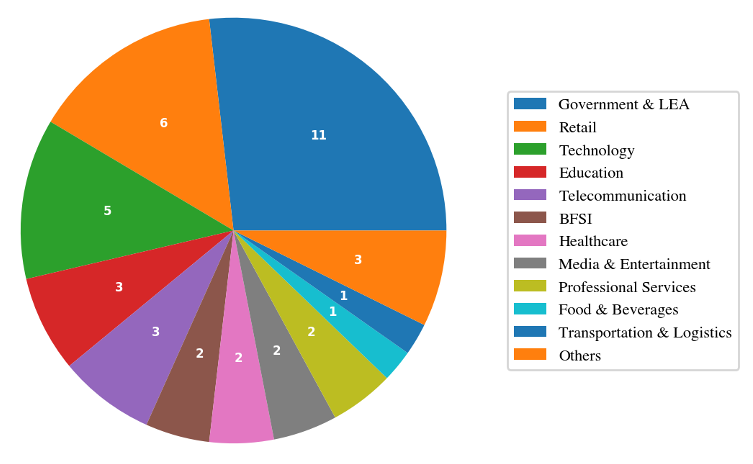
Most Targeted Sectors
- Government & Law Enforcement
- Retail
- Technology
Notable Incidents
Hospitality Holdings – TA Claimed 5TB Leak
Threat actor “nightly” claimed theft of over 5TB of data, including biometric records, CCTV footage, and financial documents.
South African Government Dataset for Sale
Threat actor XP95 advertised 3.8TB of allegedly stolen provincial government data.
Travel Data Leak
Over 95,000 travel-related records were reportedly exposed, including passports and payment data.
Exploited Vulnerabilities Accelerated Risk
March also saw active exploitation of critical vulnerabilities affecting enterprise technologies.
Notable KEV-listed vulnerabilities included:
- CVE-2026-20131 – Cisco Secure Firewall Management Center
- CVE-2025-53521 – F5 BIG-IP APM
- CVE-2026-20963 – Microsoft SharePoint Server
- CVE-2026-33017 – Langflow AI
- CVE-2021-22681 – Rockwell Automation ICS
Key Trend
Attackers exploited both:
- Newly disclosed zero-days
- Legacy vulnerabilities from prior years
This showcases widespread failures in patch management and exposure reduction.
Emerging Strategic Threat Developments
AI-Augmented Offensive Operations
Threat actors reportedly used CyberStrikeAI, an open-source AI-native security testing framework, in attacks against Fortinet FortiGate devices across 55 countries, compromising more than 600 appliances.
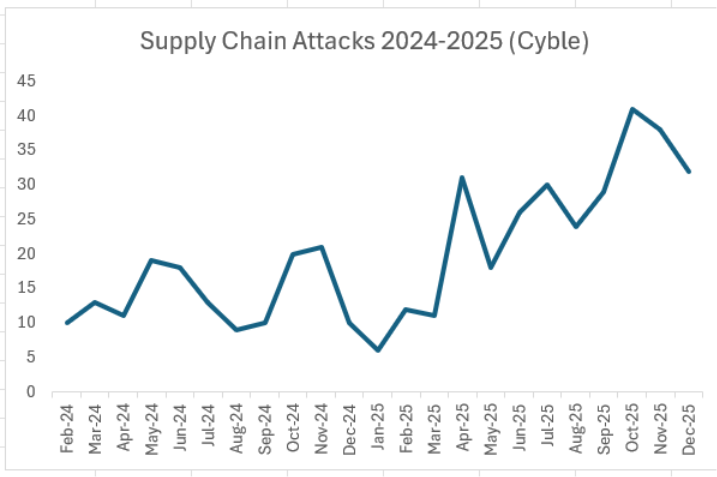
Supply Chain Malware via npm
North Korean actors were linked to 26 malicious npm packages distributing RAT malware through Pastebin/Vercel-based infrastructure.
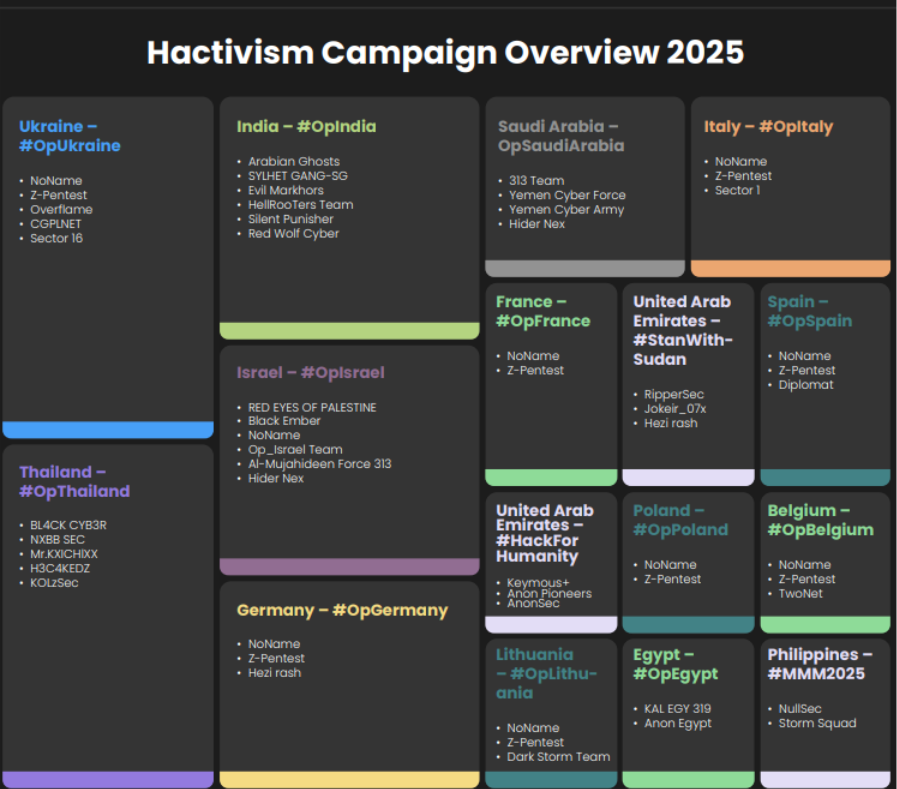
Geopolitical Cyber Risk
Iran-linked cyber operations were assessed as likely to increase following regional tensions, with potential ransomware and hacktivist targeting across the Middle East.
Industries Facing Highest Risk
Based on March activity, organizations in the following sectors faced elevated risk:
- Professional Services
- Government
- Manufacturing
- Retail
- Healthcare
- Critical Infrastructure
- Transportation & Logistics
These sectors combine valuable data, high uptime requirements, or complex supply chains.
Conclusion
The March 2026 threat landscape was defined by scale, specialization, and speed.
Threat actors increasingly leveraged:
- Access brokerage markets
- High-volume ransomware operations
- Large-scale data theft
- Rapid weaponization of critical vulnerabilities
- AI-enhanced offensive tooling
The combination of concentrated criminal ecosystems and widespread enterprise exposure creates a sustained high-risk environment for organizations globally.
Key Recommendations
- Prioritize remediation of KEV-listed vulnerabilities
- Strengthen identity security and MFA across remote access platforms
- Monitor for exposed credentials and access sale activity
- Segment critical networks to reduce lateral movement
- Conduct tabletop exercises for ransomware response
- Improve backup resilience and recovery testing
- Monitor software supply chain ecosystems
- Expand threat intelligence coverage across dark web and leak forums
Cyble’s threat intelligence, ransomware monitoring, vulnerability intelligence, and attack surface management solutions help organizations proactively identify risks, prioritize remediation, and defend against evolving global threats.
Book your demo now to see it in action!!!
The post Threat Landscape March 2026: Ransomware Dominance, Access Brokers, Data Leaks, and Critical Exploitation Trends appeared first on Cyble.