Meta has announced that Instagram will officially discontinue its optional end-to-end encrypted direct message feature on May 8, 2026.
The feature was initially rolled out for testing in 2021 to provide users with a secure communication channel accessible only by the sender and recipient.
Meta cites very low adoption rates among its user base as the primary reason for sunsetting this privacy feature.
Once the May 8 deadline passes, all direct messages on the platform will revert to standard Transport Layer Security.
Transport Encryption Versus Privacy
The transition away from end-to-end encryption marks a significant shift in how user data is handled on Instagram.
With end-to-end encryption, cryptographic keys are stored exclusively on user devices, preventing intercepted messages from being read by anyone.
By reverting to standard transport encryption, data remains secure while traveling across the network, but is decrypted once it reaches Meta’s servers.
This architectural change allows Meta to perform several new actions on your private messages.
- Automated scanning for safety violations and malicious links.
- Integration of private chat data into machine learning and AI training models.
- Fulfillment of legal requests or law enforcement subpoenas using plaintext data.
- Routine moderation using server-side keyword tracking and behavioral analysis.
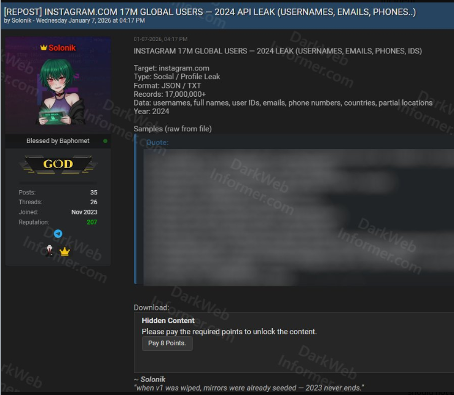
Furthermore, cybersecurity experts note that removing end-to-end encryption increases the risk of data exposure in the event of a server-side data breach.
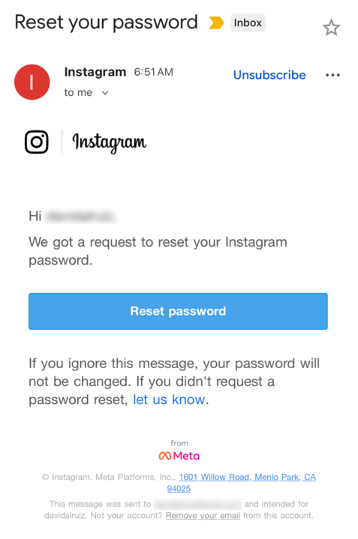
Users who previously relied on the encrypted chat feature must take immediate action to preserve their communication history.
Meta is actively sending notifications urging affected users to export their encrypted chat data before the infrastructure changes take effect.
After the cutoff date, previously encrypted threads will become fully accessible to Meta’s automated moderation algorithms.
You have four days left to enjoy encrypted chats on Instagram.
— Malwarebytes (@Malwarebytes) May 4, 2026
Once May 8th rolls around, your chats will be visible to Meta. pic.twitter.com/k1JftFSLbe
To safeguard their data, users should navigate to their account security settings and request a secure download of their personal information.
Failing to export this data before the deadline means those private conversations will seamlessly be added to the platform’s scannable database.
Community Backlash and Alternatives
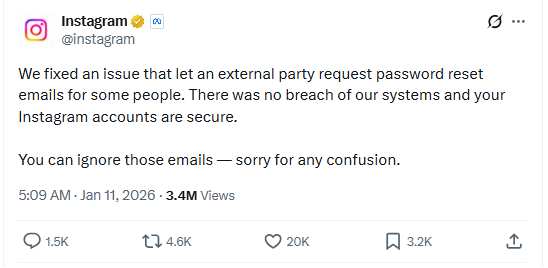
The cybersecurity community and privacy advocates have strongly criticized this sudden policy change.
Threat intelligence experts emphasize that removing built-in security features contradicts the growing global demand for robust digital privacy.
Social media discussions, including alerts from security firms like Malwarebytes, highlight public frustration over corporate data harvesting.
In response to the changes, security researchers continue to recommend migrating sensitive conversations to dedicated secure platforms.
Meta actively encourages users seeking privacy to transition to WhatsApp. However, many privacy-conscious individuals are shifting to independent messengers like Signal.
The post Instagram’s to End Encrypted Chats for Direct Messages appeared first on Cyber Security News.