A Chrome extension posing as an Amazon ad blocker was caught hijacking affiliate links in the background, redirecting commissions without user consent.
The post Chrome Add-On Caught Stealing Amazon Commissions appeared first on TechRepublic.
A Chrome extension posing as an Amazon ad blocker was caught hijacking affiliate links in the background, redirecting commissions without user consent.
The post Chrome Add-On Caught Stealing Amazon Commissions appeared first on TechRepublic.
A group of cybercriminals called DarkSpectre is believed to be behind three campaigns spread by malicious browser extensions: ShadyPanda, GhostPoster, and Zoom Stealer.
We wrote about the ShadyPanda campaign in December 2025, warning users that extensions which had behaved normally for years suddenly went rogue. After a malicious update, these extensions were able to track browsing behavior and run malicious code inside the browser.
Also in December, researchers uncovered a new campaign, GhostPoster, and identified 17 compromised Firefox extensions. The campaign was found to hide JavaScript code inside the image logo of malicious Firefox extensions with more than 50,000 downloads, allowing attackers to to monitor browser activity and plant a backdoor.
The use of malicious code in images is a technique called steganography. Earlier GhostPoster extensions hid JavaScript loader code inside PNG icons such as logo.png for Firefox extensions like “Free VPN Forever,” using a marker (for example, three equals signs) in the raw bytes to separate image data from payload.
Newer variants moved to embedding payloads in arbitrary images inside the extension bundle, then decoding and decrypting them at runtime. This makes the malicious code much harder for researchers to detect.
Based on that research, other researchers found an additional 17 extensions associated with the same group, beyond the original Firefox set. These were downloaded more than 840,000 times in total, with some remaining active in the wild for up to five years.
GhostPoster first targeted Microsoft Edge users and later expanded to Chrome and Firefox as the attackers built out their infrastructure. The attackers published the extensions in each browser’s web store as seemingly useful tools with names like “Google Translate in Right Click,” “Ads Block Ultimate,” “Translate Selected Text with Google,” “Instagram Downloader,” and “Youtube Download.”
The extensions can see visited sites, search queries, and shopping behavior, allowing attackers to create detailed profiles of users’ habits and interests.
Combined with other malicious code, this visibility could be extended to credential theft, session hijacking, or attacks targeting online banking workflows, even if those are not the primary goal today.
Although we always advise people to install extensions only from official web stores, this case proves once again that not all extensions available there are safe. That said, the risk involved in installing an extension from outside the web store is even greater.
Extensions listed in the web store undergo a review process before being approved. This process, which combines automated and manual checks, assesses the extension’s safety, policy compliance, and overall user experience. The goal is to protect users from scams, malware, and other malicious activity.
Mozilla and Microsoft have removed the identified add-ons from their stores, and Google has confirmed their removal from the Chrome Web Store. However, already installed extensions remain active in Chrome and Edge until users manually uninstall them. When Mozilla blocks an add-on it is also disabled, which prevents it from interacting with Firefox and accessing your browser and your data.
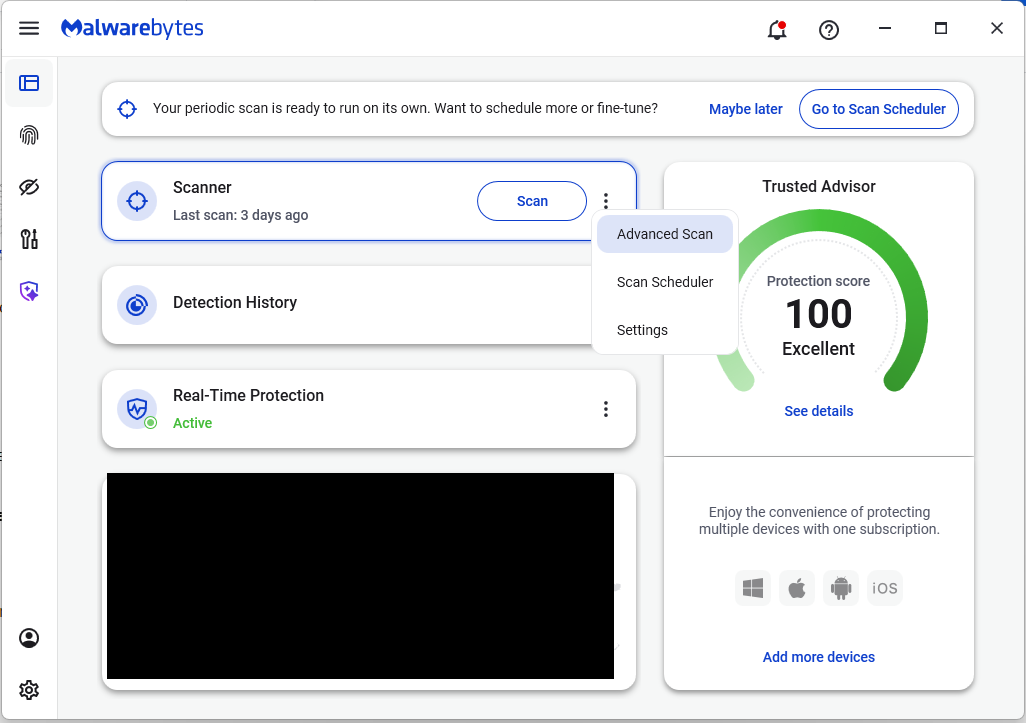
If you’re worried that you may have installed one of these extensions, Windows users can run a Malwarebytes Deep Scan with their browsers closed.
Manual check:
These are the names of the 17 additional extensions that were discovered:
Note: There may be extensions with the same names that are not malicious.
We don’t just report on threats—we help safeguard your entire digital identity
Cybersecurity risks should never spread beyond a headline. Protect your, and your family’s, personal information by using identity protection.
Researchers have unraveled a malware campaign that really did play the long game. After seven years of behaving normally, a set of browser extensions installed on roughly 4.3 million Chrome and Edge users’ devices suddenly went rogue. Now they can track what you browse and run malicious code inside your browser.
The researchers found five extensions that operated cleanly for years before being weaponized in mid-2024. The developers earned trust, built up millions of installs, and even collected “Featured” or “Verified” status in the Chrome and Edge stores. Then they pushed silent updates that turned these add-ons into spyware and malware.
The extensions turned into a remote code execution framework. They could download and run malicious JavaScript inside the browser and collect information about visited sites and the user’s browser, sending it all back to attackers believed to be based in China.
One of the most prevalent of these extensions is WeTab, with around three million installs on Edge. It acts as spyware by streaming visited URLs, search queries, and other data in real time. The researchers note that while Google has removed the extensions, the Edge store versions are still available.
Playing the long game is not something cybercriminals usually have the time or patience for.
The researchers attributed the campaign to the ShadyPanda group, which has been active since at least 2018 and launched their first campaign in 2023. That was a simpler case of affiliate fraud, inserting affiliate tracking codes into users’ shopping clicks.
What the group did learn from that campaign was that they could get away with deploying malicious updates to existing extensions. Google vets new extensions carefully, but updates don’t get the same attention.
It’s not the first time we’ve seen this behavior, but waiting for years is exceptional. When an extension has been available in the web store for a while, cybercriminals can insert malicious code through updates to the extension. Some researchers refer to the clean extensions as “sleeper agents” that sit quietly for years before switching to malicious behavior.
This new campaign is far more dangerous. Every infected browser runs a remote code execution framework. Every hour, it checks api.extensionplay[.]com for new instructions, downloads arbitrary JavaScript, and executes it with full browser API access.
The researchers at Koi shared a long list of Chrome and Edge extension IDs linked to this campaign. You can check if you have these extensions in your browser:
In Chrome
eagiakjmjnblliacokhcalebgnhellfi) into the search box.If the page scrolls to an extension and highlights the ID, it’s installed. If it says No results found, it isn’t in that Chrome profile.
If you see that ID under an extension, it means that particular add‑on is installed for the current Chrome profile.
To remove it, click Remove on that extension’s card on the same page.
In Edge
Since Edge is a Chromium browser the steps are the same, just go to edge://extensions/ instead.
We don’t just report on threats—we remove them
Cybersecurity risks should never spread beyond a headline. Keep threats off your devices by downloading Malwarebytes today.