The Week in Vulnerabilities: GitHub Enterprise, Argo CD, Oracle Identity Manager, and Mozilla Security Flaws
The latest weekly vulnerability Insights report to clients by Cyble provides a detailed view of vulnerabilities tracked between April 15, 2026, and April 21, 2026. The findings highlight a slight dip in overall disclosures compared to the previous week, but the persistence of active exploitation and evidence of real-world attacks continues to target enterprise, cloud, and open-source ecosystems.
During this reporting period, Cyble’s Vulnerability Intelligence module tracked 1,095 vulnerabilities, reflecting a decrease in volume after last week’s spike. However, the reduced number does not indicate lower risk. In fact, the presence of over 91 vulnerabilities with publicly available Proof-of-Concept (PoC) exploits increases the likelihood of rapid weaponization and exploitation in real-world environments.
Additionally, Cyble observed 2 vulnerabilities actively discussed in underground forums, reinforcing that threat actors continue to prioritize high-impact flaws and accelerate their use in real-world attacks.
Real-World Attacks and Threat Intelligence Observations
As part of its weekly vulnerability Insights, CRIL leveraged its Threat Hunting capabilities to capture real-time attack data using distributed honeypot sensors. These systems recorded multiple instances of:
- Exploit attempts
- Malware intrusions
- Financial fraud campaigns
- Brute-force attacks
The Sensor Intelligence data further revealed targeted campaigns involving malware families such as:
- CoinMiner Linux
- WannaCry
- Linux Mirai Coin Miner
- Linux IRCBot
- Android Coin Hive Miner
In addition to malware activity, phishing emails and brute-force attempts were also observed, demonstrating the breadth of real-world attacks targeting both users and infrastructure.
The report also provides deeper visibility into attacker behavior, including:
- Top targeted countries
- Frequently abused ports
- Source IP intelligence
- Network operator attribution
These insights reinforce how active exploitation is not limited to isolated vulnerabilities but is part of coordinated attack campaigns.
Weekly Vulnerability Disclosure Overview
Analysis of the weekly vulnerability Insights reveals several important patterns in vendor exposure and severity distribution.
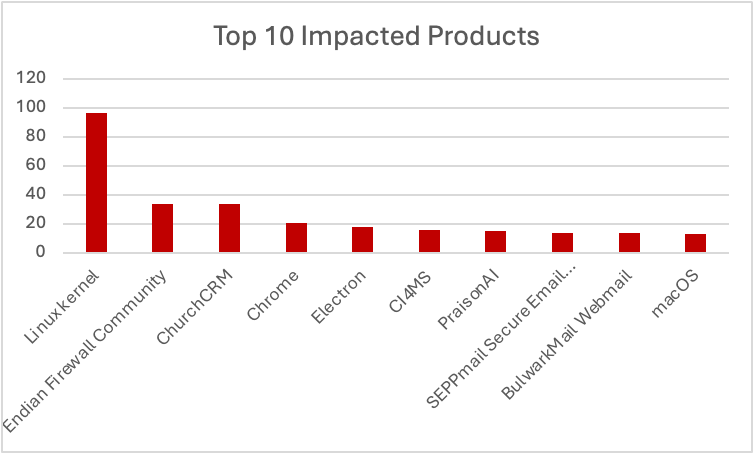
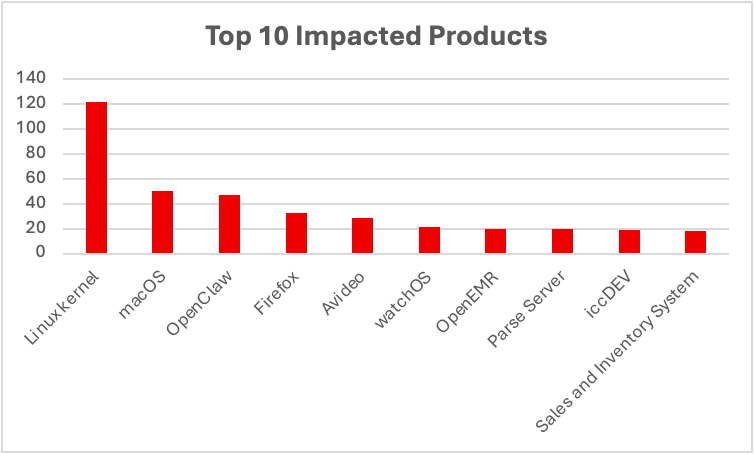
Top Vendors Impacted
The highest number of reported vulnerabilities was associated with:
- Oracle
- Mozilla
- Dell
- FreeScout Help Desk
This distribution highlights how both enterprise-grade platforms and open-source tools remain attractive targets for adversaries.
Severity Breakdown
- 96 vulnerabilities were rated critical under CVSS v3.1
- 43 vulnerabilities were rated critical under CVSS v4.0
Key Vulnerabilities Driving Real-World Attacks
Several critical vulnerabilities stood out due to their potential for exploitation:
- CVE-2026-5921: A flaw in GitHub Enterprise Server involving Server-Side Request Forgery (SSRF) and a timing side-channel attack
- CVE-2026-6388: A critical issue in Argo CD Image Updater, widely used in Kubernetes environments
- CVE-2026-34287: A vulnerability in Oracle Identity Manager (OIM) Connector
- CVE-2026-6771: A flaw in Mozilla Firefox and Thunderbird DOM security
These vulnerabilities are particularly dangerous because they target trusted development and identity systems, allowing attackers to:
- Execute arbitrary code
- Steal credentials
- Compromise entire servers
Such weaknesses directly contribute to real-world attacks, as they enable adversaries to infiltrate core enterprise workflows with minimal resistance.
CISA KEV Catalog: Evidence of Active Exploitation
Between April 15 and April 21, 2026, the Cybersecurity and Infrastructure Security Agency (CISA) added 9 vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalog, confirming active exploitation in the wild.
Notable KEV Additions
- CVE-2023-27351 (PaperCut MF/NG): This vulnerability allows unauthenticated remote code execution with SYSTEM privileges. It has been widely exploited by ransomware groups such as Clop and LockBit.
- CVE-2025-48700 (Zimbra Collaboration Suite): A Cross-Site Scripting (XSS) flaw that can be leveraged for session hijacking and data theft.
- CVE-2026-20133 (Cisco Catalyst SD-WAN Manager): An information disclosure vulnerability exposing sensitive network data.
As of April 2026, CISA has added 23 vulnerabilities to the KEV catalog, further emphasizing the scale of active exploitation across industries.
Trending Vulnerabilities and Resurgence of Real-World Attacks
Among the most notable cases in this week’s weekly vulnerability Insights is the resurgence of older vulnerabilities being reused in new campaigns.
CVE-2024-3721 (TBK DVR Devices)
A critical OS command injection flaw affecting TBK Digital Video Recorders has re-emerged due to a new Mirai-based botnet variant called “Nexcorium.”
This botnet is actively scanning for vulnerable DVR models (DVR-4104 and DVR-4216) to recruit them into a distributed denial-of-service (DDoS) network. Its inclusion in the KEV catalog confirms ongoing active exploitation and highlights how legacy devices continue to fuel real-world attacks.
CVE-2025-0520 (ShowDoc)
A remote code execution vulnerability allows attackers to upload malicious PHP files to publicly accessible directories. Once uploaded, these files can be executed to gain control over the server.
This simple yet effective attack vector has made ShowDoc a frequent target in real-world attacks.
Underground Activity and Exploit Development
CRIL’s monitoring of underground forums revealed continued interest in weaponizing vulnerabilities for active exploitation.
Notable Vulnerabilities Discussed
- CVE-2026-33825 (Microsoft Defender): A privilege escalation flaw linked to the “BlueHammer” exploit family, allowing attackers to gain SYSTEM-level access and extract sensitive data such as NTLM hashes.
- CVE-2025-8941 (Linux-PAM): A path traversal vulnerability enabling privilege escalation through symlink attacks.
- CVE-2026-38526 (Krayin CRM): An authenticated file upload vulnerability leading to remote code execution.
- CVE-2026-26980 (Ghost CMS): A SQL injection flaw allowing unauthorized database access and data exfiltration.
The timeline analysis shows rapid transitions from disclosure to exploit availability, reinforcing the speed at which real-world attacks can materialize.
Persistent Risk Despite Lower Volume
This week’s vulnerability Insights show that even with fewer disclosures, the risk of active exploitation and real-world attacks remains significant. With 91+ PoC-backed vulnerabilities, new KEV additions, and ongoing underground activity, attackers continue to move quickly from discovery to exploitation. In this environment, organizations need proactive, intelligence-driven defenses.
Cyble’s AI-powered threat intelligence platform provides real-time visibility, predictive insights, and automated security operations to help teams stay ahead of evolving threats. Organizations can explore these capabilities further by scheduling a demo with Cyble.
The post The Week in Vulnerabilities: GitHub Enterprise, Argo CD, Oracle Identity Manager, and Mozilla Security Flaws appeared first on Cyble.