ICE Uses Graphite Spyware
ICE has admitted that it uses spyware from the Israeli company Graphite.
ICE has admitted that it uses spyware from the Israeli company Graphite.

On the morning of March 11, employees at Stryker offices worldwide switched on their computers and found them blank — login screens replaced by a logo most had never seen. A small, barefoot boy with a slingshot, the symbol of Handala.
The attack on Stryker Corporation — a Fortune 500 medical technology giant that supplies surgical equipment, orthopedic implants, and neurotechnology to hospitals globally — ranks as one of the most operationally destructive cyberattacks ever executed against a U.S. healthcare company.
Stryker reported $25 billion in revenue in 2025 and employs approximately 56,000 people, with its products embedded in hospital supply chains worldwide. What hit it was not ransomware. The attackers came to destroy, not extort.
Stryker confirmed the incident in a Form 8-K filing with the U.S. SEC, describing "a global disruption to the Company's Microsoft environment" and stating it had no indication of ransomware or malware and believed the incident was contained. The company's own filing, however, understated what employees were already reporting on the ground.
Employees in the United States, Ireland, Costa Rica, and Australia reported that managed Windows laptops and mobile devices had been remotely wiped.
Another claimed the situation as "bad" and said: "Many colleagues phones have been wiped. Instructed to remove intune, company portal, teams, VPN from personal devices. Personal phone so have lost access to my eSim. Unable to log in to many things due to 2-factor authentication. Have lost all personal data from personal devices that were enrolled and now unable to access emails and teams."My wife had 3 Stryker managed devices wiped around 3:30 AM EDT. Their Entra login page was defaced with the Handala logo," a Reddit user said.
Handala claimed to have wiped more than 200,000 systems, servers, and mobile devices and extracted 50 terabytes of data, forcing Stryker to shut down operations across 79 countries. Stryker in a midnight update said it was still working on complete restoration post the cyberattack.
"We are continuing to resolve the disruption impacting our global network, resulting from the cyber attack. At this time, there is no indication of malware or ransomware and we believe the situation is contained to our internal Microsoft environment only. Our products like Mako, Vocera and LIFEPAK35 are fully safe to use. We have visibility to the orders entered before the event, and they will be shipped as soon as our system communications are restored. Any orders that have come in after the event are being examined. We are working to ensure our electronic ordering system is back up and running as quickly as possible. It is safe to communicate with Stryker employees and sales representatives by email and phone, and within your facility." - Stryker's update on the cyberattack
The mechanism behind the attack points to a calculated abuse of Microsoft Intune — a cloud-based platform enterprises use to manage and push policy updates to all enrolled devices from a single console. A wiper is malware that permanently erases data rather than encrypting it for ransom.
In short, an attacker with admin-level access to Intune effectively is holding a kill switch for every enrolled endpoint in the organization. The Handala branding that appeared on screens before the wipe confirmed that access had been established and held well before the destructive phase began — this was a deliberate, staged operation.
Handala — also known as Handala Hack Team, Hatef, and Hamsa — first surfaced in December 2023 as a hacktivist operation linked to Iran's Ministry of Intelligence and Security (MOIS), initially targeting Israeli organizations with destructive malware designed to wipe both Windows and Linux devices, explained researchers at AI-powered threat intelligence firm, Cyble.
The group takes its name and visual branding from the iconic Palestinian cartoon character created by Naji al-Ali — a child refugee who never grows up and always turns his back to the viewer.
The hacktivist branding, however, obscures a more serious intelligence attribution. Multiple threat intelligence firms assess Handala as one of several online personas maintained by Void Manticore, a MOIS-affiliated actor optimized for psychological and reputational disruption — breaking into systems, conducting hack-and-leak activity, and timing the publication of stolen material to maximize pressure.
Check Point Research found repeated overlaps between MuddyWater — another MOIS-affiliated group — and Void Manticore, including shared criminal tooling. Handala has used Rhadamanthys, a commercial infostealer sold on dark web forums, pairing it with custom data wipers in phishing lures that impersonated F5 software updates and even Israel's own National Cyber Directorate.
Cyble has observed Handala hackers using Hamsa and Hatef data wipers in its previous campaigns targeted mainly at Israeli entities. [caption id="attachment_110112" align="aligncenter" width="500"]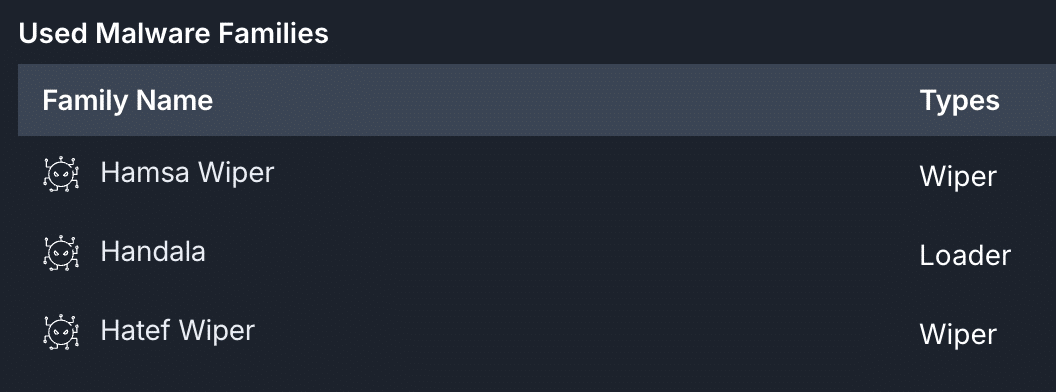 Source: Cyble Research and Intelligence Labs[/caption]
Source: Cyble Research and Intelligence Labs[/caption]
Void Manticore's attack playbook follows a consistent pattern of Handala too. Initial access through unpatched web servers, VPN gateways, and remote access solutions; lateral movement using living-off-the-land tools like PowerShell and scheduled tasks; and final-stage deployment of destructive wiper families designed to erase file systems and corrupt boot records.
The group's prior targets read like a map of sensitive sectors. Since the start of the Iran-Israel war, Handala has claimed to have wiped Israeli military weather servers, intercepted security feeds in Jerusalem, stolen and wiped data from various companies, doxxed Israeli intelligence officers, and breached an Israeli oil and gas exploration company.
Most recently, threat intelligence reporting documented the group publishing identifying details for 50 senior Israeli Air Force officers — names, IDs, addresses, and phone numbers.
Handala stated the Stryker attack was carried out in retaliation for a U.S. military strike on a school in Minab, Iran, that reportedly killed more than 175 people, most of them children.
[caption id="attachment_110115" align="aligncenter" width="500"]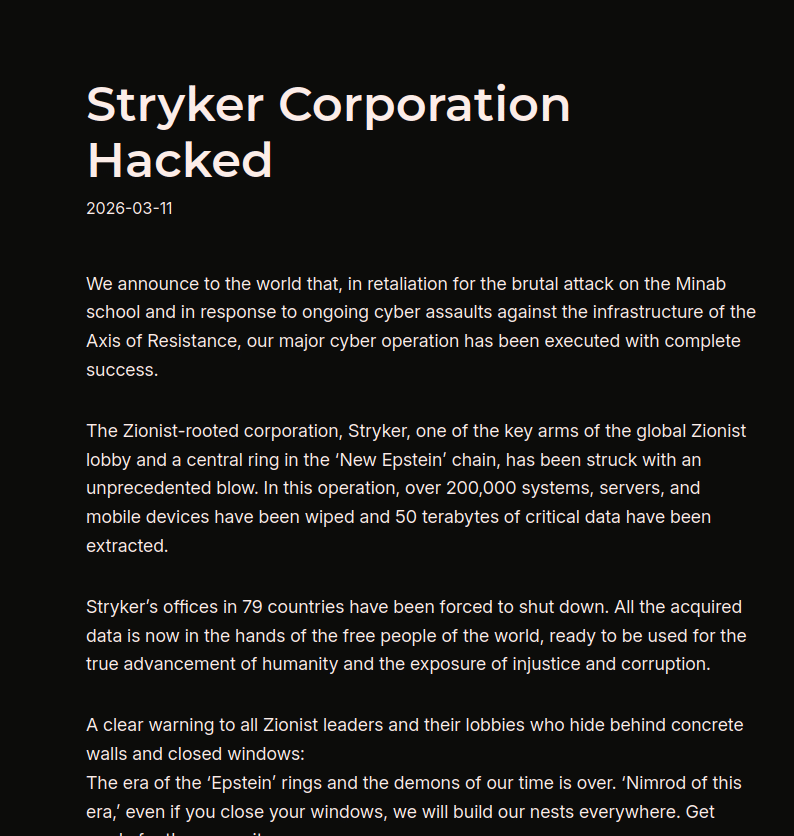 Stryker Cyberattack Claim by Handala (Source: X)[/caption]
Stryker Cyberattack Claim by Handala (Source: X)[/caption]
Stryker has no direct connection to military operations, though it did secure a $450 million Department of Defense contract in 2025 to supply medical devices to the U.S. military.
That contract likely put a target on Stryker's back.
Recent reporting indicates that MOIS-affiliated groups, including Handala, infiltrated U.S. and Israeli infrastructure weeks before the military operations conducted as part of Operation Epic Fury, suggesting pre-positioned access rather than reactive intrusion. In other words, Handala may have been inside Stryker's environment long before anyone noticed.
Check Point researchers also observed Handala routing operations through Starlink IP ranges to probe externally facing applications for misconfigurations and weak credentials — a deliberate technique to blend reconnaissance traffic into legitimate satellite internet usage and frustrate IP-based blocking.
The hacker collective on Wednesday also claimed hacking another Israeli company Verifone, a leading provider of payment solutions and point-of-sale terminals to countries across the globe. However, a spokesperson for the company told The Cyber Express that all such claims are "fake news" and do not hold any substance. “Verifone closely monitors the security and integrity of its systems worldwide. We have observed recent allegations on March 11, 2026 from threat actors claiming an intrusion into our systems in Israel. Verifone has found no evidence of any incident related to this claim and has no service disruption to our clients," the spokesperson said. Updated on March 13, 2026 1:24 AM ET: The article was updated with a statement from Verifone spokesperson confirming no evidence of intrusion and no authenticity in Handala's claims.The Israeli Air Force (IAF) has dropped 5,000 bombs on Iran since the United States and Israel launched an attack last week, according to a statement by the IAF on March 4.
Bellingcat has monitored weapons used in the first few days of the war, and strikes across the region, including those that caused civilian harm. Some weapons, such as the US Precision Strike Missile, have seen their first use in combat. A variant of the Tomahawk missile, previously unknown to the public, was also used.
On March 3, the IAF posted three images in three separate posts showing a bomb not publicly seen in Israeli service before. The Israel Air Force released these photos accompanied with claims they were of jets participating in the strikes on Iran. Experts told Bellingcat that this bomb appears to have an incendiary component, and may be one intended to destroy chemical or biological warfare agents.

The images appear to show 2,000-pound-class air-delivered bombs fitted with Joint Direct Attack Munition (JDAM) guidance kit with a red band around the nose. Red is commonly used to denote an incendiary, while yellow indicates high explosive effect.

We identified key details about the munition and shared the images with two weapons experts.
Dr N.R. Jenzen-Jones, the director of Armament Research Services (ARES), a weapons intelligence consulting company, told Bellingcat these images show a 2,000-pound-class air-delivered bomb fitted with a Joint Direct Attack Munition (JDAM) guidance kit.
Frederic Gras, an Explosive Remnants of War (ERW) expert, also told Bellingcat that the bomb could be of the US MK 80 series, or an Israeli copy, and has a JDAM guidance kit.

The US JDAM bomb guidance kit is designed for use with bombs that use the MK 80 series bomb bodies, and the closely related BLU-109 “bunker buster” body.
The Open Source Munitions Portal added the munition to their website on March 3, describing it as “visually similar to a MK 84 general purpose aerial bomb”, while noting that “the marking scheme is distinctly different”. The War Zone also reported on these distinct markings, and possible munitions it could be.

“The combination of yellow and red bands probably indicates both a high explosive and incendiary payload, which would be consistent with a 2,000-pound-class bomb of MK 84 form factor known as the BLU-119/B Crash Prompt Agent Defeat (CrashPAD),” Dr Jenzen-Jones told Bellingcat.
Frederic Gras, an Explosive Remnants of War (ERW) expert said that the US and Israel both use red markings to indicate an incendiary payload, or effect. The bomb could be a full incendiary payload, with the yellow band indicating a bursting charge, or it could be a bomb primarily with a high explosive component, and a secondary incendiary effect, Gras added.
It’s not the first time the Israeli Air Forces has published weapon images with red bands marking the warhead or payload section of a munition. Shortly after the start of the Gaza War in 2023, the IAF posted a photo which included an Apache attack helicopter with a Hellfire missile with a red band. The IAF deleted the post and replaced it with a similar photo of an Apache without this missile.

This fueled speculation online that this could be an incendiary or the thermobaric variant of the Hellfire missile, the AGM-114N. It has been approved by the US for sale to Israel.
M825A1 155mm white phosphorus artillery projectiles, munitions designed to create smoke, used by Israel also have a red band and a yellow band around the nose.
Israeli munitions which are not incendiary have also been spotted with light red bands over the fuel tanks for munitions with jet engines, such as the Delilah cruise missile.

The markings are consistent with the US-produced CrashPAD, but “given the possible CBW [chemical and biological warfare] threats Israel has long faced from Iran, it is entirely plausible that an Israeli analogue was developed,” Dr Jenzen-Jones told Bellingcat.
The CrashPAD contains white phosphorus and high explosives, and is designed to destroy biological and chemical warfare agents according to US government documents.

Dr Jenzen-Jones told Bellingcat that the CrashPAD is the only publicly known weapon of this type utilising a MK 84 bomb body although there are several programs producing similar munitions. A penetrating variant is known as the Shredder but it uses a modified BLU-109 bomb body, which is visually different from the MK 84 bomb body visible in the IAF photos.

CrashPAD has been in the US inventory for nearly two decades. “Chemical Agent Defeat weapons, such as Crashpad, are not illegal”, and they must undergo a legal review to ensure compliance with US domestic and international law, Michael Meier, former Senior Advisor to the Army Judge Advocate General for Law of War and current Adjunct Professor at Georgetown University Law Center, told Bellingcat.
“The express purpose for the reservation is that these weapons, such as Crashpad, are the only weapons that can effectively destroy certain targets such as biological weapons facilities, for which high heat would be required to eliminate bio-toxins,” Meier said.
Dr Arthur van Coller, Professor of International Humanitarian Law at the STADIO Higher Education, told Bellingcat that “if the CrashPAD is used as designed, i.e. to target chemical or biological weapon stockpiles sufficiently removed from civilian populations, then its use is consistent with IHL [International Humanitarian Law] and treaty law, even under CCW [Certain Conventional Weapons], Protocol III.”
Dr Arthur van Coller also said that the “United States and Israel are State Parties to the CCW itself,” but only the US is also a party to Protocol III on incendiary weapons, albeit with reservations, which means that Israel “is not legally bound by Protocol III’s restrictions on incendiary weapons (including those applying to CrashPAD) under treaty law”. Iran is not a party to the CCW at all.
The US is a major supplier of weapons to Israel, and has sent thousands of MK 80 series and BLU-109 bombs to the country. Israel also produces some MK 80 series bombs.
The US Defense Security Cooperation Agency, which publishes details of some major arms sales, does not mention any transfers of the CrashPAD. Bellingcat asked the Department of State if the CrashPAD or weapons with similar capabilities were transferred to Israel. Bellingcat also asked the Department of State if they assessed that Iran had a chemical weapons program. A State Department Spokesperson told Bellingcat that “The Trump administration backs Israel’s right to self-defense” and referred Bellingcat to the IDF for questions about procurement and munitions used.
The US Department of Defense did not respond to requests for comment by the time of publication.
Bellingcat asked the IDF what the bomb was, if it was supplied by the US, if it contained white phosphorus, thermobaric or fuel air explosives, and if the IDF assessed that Iran had a chemical weapons program. The IDF told Bellingcat that it “will not be able to provide details regarding the types of munitions it uses. With that said the IDF uses only legal weapons and ammunition.”
Bellingcat’s Carlos Gonzales contributed research to this article. Livio Spaini from Bellingcat’s Volunteer Community also contributed to this piece.
Bellingcat is a non-profit and the ability to carry out our work is dependent on the kind support of individual donors. If you would like to support our work, you can do so here. You can also subscribe to our Patreon channel here. Subscribe to our Newsletter and follow us on Bluesky here, Instagram here, Reddit here and YouTube here.
The post The Incendiary Bomb Never Seen in Israel Before appeared first on bellingcat.
According to the Check Point Cyber Security Report 2026, cyber operations are increasingly used to support military activity and battle damage assessment (BDA). During the Israel-Iran tensions, researchers from Check Point Software Technologies observed a surge in attacks targeting IP cameras across Israel and Gulf countries, including the UAE, Qatar, Bahrain, and Kuwait, as well as Lebanon and Cyprus. The activity, attributed to Iran-linked actors, relied on VPN and VPS infrastructure to scan devices, mainly Hikvision and Dahua Technology cameras, for known vulnerabilities.
“During the ongoing conflict, we identified intensified targeting of IP cameras from two manufacturers starting on February 28, originating from infrastructure we attribute to Iranian threat actors.
The targeting extends across Israel, Qatar, Bahrain, Kuwait, the UAE, and Cyprus – countries that have also experienced significant missile activity linked to Iran. On March 1st, we additionally observed camera-targeting activity focused on specific areas in Lebanon.” states Check Point Software Technologies.”
“We also observed earlier, more targeted activity against cameras in Israel and Qatar on January 14–15. These dates surround with Iran’s temporary closure of its airspace, reportedly amid expectations of a potential U.S. strike.”
Researchers believe the goal was reconnaissance and real-time monitoring to support intelligence gathering and potential military targeting.
Threat actors targeted the following vulnerabilities in Hikvision and Dahua devices:
| CVE | Vulnerability |
|---|---|
| CVE-2017-7921 | An improper authentication vulnerability in Hikvision IP camera firmware |
| CVE-2021-36260 | A command injection vulnerability in the Hikvision web server component |
| CVE-2023-6895 | An OS command injection vulnerability in Hikvision Intercom Broadcasting System |
| CVE-2025-34067 | An unauthenticated remote code execution vulnerability in Hikvision Integrated Security Management Platform |
| CVE-2021-33044 | An authentication bypass vulnerability in multiple Dahua products |
The experts state that Chinese manufacturers have patched all the above issues.
Researchers analyzed exploitation attempts for CVE-2021-33044 and CVE-2017-7921 linked to infrastructure attributed to Iran.
In October 2021, experts warned that proof-of-concept (PoC) exploit code was available for two authentication-bypass vulnerabilities in Dahua cameras, tracked as CVE-2021-33044 and CVE-2021-33045. A remote attacker can exploit both vulnerabilities by sending specially crafted data packets to the vulnerable cameras.
Since early 2026, scanning activity targeting IP cameras has surged across Israel and several Middle East countries, often aligning with geopolitical tensions such as protests in Iran, U.S. military visits to Israel, and fears of potential strikes.


Similar patterns appeared during the June 2025 Israel-Iran conflict, when compromised cameras were likely used for reconnaissance and battle damage assessment, including a case involving a camera near Israel’s Weizmann Institute before a missile strike.
“One of the best-known cases occurred when Iran struck Israel’s Weizmann Institute of Science with a ballistic missile and had reportedly taken control of a street camera facing the building just prior to the hit” concludes the report.
Defenders should reduce risks by removing public internet access to cameras and placing them behind VPN or zero-trust gateways. Organizations should change default passwords, enforce strong unique credentials, and keep device firmware updated. Cameras should run on isolated network segments with restricted outbound traffic. Security teams should also monitor for repeated login failures, suspicious remote access, and unusual outbound connections.
This week, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added Hikvision multiple products improper authentication vulnerability CVE-2017-7921 (CVSS score of 9.8) to its Known Exploited Vulnerabilities (KEV) catalog.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Iran, IP cameras)
Wired has the story:
Shortly after the first set of explosions, Iranians received bursts of notifications on their phones. They came not from the government advising caution, but from an apparently hacked prayer-timing app called BadeSaba Calendar that has been downloaded more than 5 million times from the Google Play Store.
The messages arrived in quick succession over a period of 30 minutes, starting with the phrase ‘Help has arrived’ at 9:52 am Tehran time, shortly after the first set of explosions. No party has claimed responsibility for the hacks.
It happened so fast that this is most likely a government operation. I can easily envision both the US and Israel having hacked the app previously, and then deciding that this is a good use of that access.
US President Donald Trump said on January 2 that the US was “locked and loaded and ready to go”. Trump was talking aloud about intervening in Iran if it continued a violent crackdown on demonstrators who had taken to the streets over spiralling inflation and ongoing repression.
Thousands of Iranian’s were reported to have been killed by state security forces in just under a month. According to Amnesty International, the Islamic Revolutionary Guard Corps (IRGC), the Basij plainclothes militia, police forces and other plain-clothed agents carried out the deadliest violence against protesters in decades.
On Saturday, February 28, the United States and Israel launched a large-scale attack against Iran, killing Supreme Leader Ayatollah Ali Khamenei and targeting military infrastructure throughout the country. President Trump initially told Iranians they should seize control of the government but on Tuesday this week said: “If you’re going to go out and protest, don’t do it yet. It’s very dangerous out there. A lot of bombs are being dropped.” Almost 800 Iranians have been killed in US and Israeli strikes so far, according to the Iranian Red Crescent.
While the US has released a list of military targets, including IRGC headquarters and missile systems, Bellingcat has reviewed strikes against another type of target inside the Islamic Republic — police stations.
Experts told the New York Times that strikes against these facilities may be part of an effort to motivate Iranians to challenge the regime, although satellite analysis alone doesn’t allow us to tell if it is the US, Israel or both nations who have targeted police stations.
Using medium-resolution PlanetScope satellite imagery from Planet Labs, Bellingcat has been able to locate at least 15 local police stations or similar buildings that were struck between March 1 and March 3. Videos and photos shared on social media also show the aftermath of some of these strikes.
Comparing the March 1 PlanetScope satellite imagery with imagery taken on March 3, it’s possible to make out visible signs of building destruction throughout Tehran. Some of these sites have already been widely-reported on, including the strike on Supreme Leader Ali Khamenei’s compound and official residence.
But Bellingcat reviewed damage to a number of smaller buildings throughout Tehran and cross-referenced the locations with data on Google Maps, Open Street Maps and Wikimapia where we found that several were listed as police stations. The majority of sites we identified are in dense urban areas.
Video shared by Iranian state broadcaster Tasnim News showed the aftermath of a strike on what it describes as a “diplomatic police station” near Ferdowsi Square — one of downtown Tehran’s main intersections. Another video taken at the same location shows at least two people on the ground with a large amount of damage to nearby buildings. Geolocation of the videos puts them at 35.7032, 51.4189, adjacent to a school and office buildings.

Another video, geolocated by a volunteer with Geoconfirmed — a volunteer geolocation collective — shows a heavily damaged police station near Tehran’s Grand Bazaar. PlanetScope imagery from March 3 shows heavy damage to the area around the police station.
Photos and video from the Golestan Palace, a UNESCO World Heritage Site that sits adjacent to the police office, shows that it also sustained damage.


Iran’s security apparatus includes a network of police, plain clothes officers, civilian militia battalions known as Basij and the Islamic Revolutionary Guard Corps. During recent protests security forces were seen shooting protestors on the streets, and many of those killed showed signs of being shot in the head.
Iran has experienced several waves of anti-regime protests over the past 15 years, all of which have been put down by the authorities who have not shied away from using extreme violence to contain them.
Although the Financial Times reported speaking to a Tehran resident that said one of the police stations we identified, in the Gisha neighborhood, had hosted a branch of Iran’s morality police, it is thus far unclear from the satellite data whether any of the police stations had any particular role during the recent protests.
Trevor Ball, Logan Williams and Felix Matteo Lommerse contributed reporting to this piece for Bellingcat. Anisa Shabir and Stéphanie Ladel contributed from Bellingcat’s Volunteer Community.
Bellingcat is a non-profit and the ability to carry out our work is dependent on the kind support of individual donors. If you would like to support our work, you can do so here. You can also subscribe to our Patreon channel here. Subscribe to our Newsletter and follow us on Bluesky here, Instagram here, Reddit here and YouTube here.
The post Satellite Imagery Reveals Strikes on Iranian Police Stations appeared first on bellingcat.

The United States and Israel launched an attack on Iran on Saturday morning, killing Supreme Leader Ayatollah Ali Khamenei as well as several senior regime figures and striking multiple sites across the country. Iran retaliated by firing at targets across the region, including Israel, Bahrain, Qatar, the UAE and other Gulf states. The conflict is ongoing despite no declaration of war by the US Congress. US President Donald Trump initially called for regime change in Iran but has since delivered a mixed message about the aims of “Operation Epic Fury”.
Israel has said it dropped more than 2,000 bombs in the first 30 hours of the war. While the US claims to have struck over 1,000 targets in the first 24 hours, with President Trump stating that “bombs will fall everywhere”. In response, Iran is reported to have launched at least 390 missiles and 830 drones in the first two days.
Bellingcat has been monitoring strikes across the region, including those that caused civilian harm, and identified a wide variety of weapons have been used so far, including missiles and drones.
The US reported that some of the first weapons they launched were Tomahawk missiles. Footage from the US McFaul also showed Tomahawks being launched.
There is also reporting that a new variant of the Tomahawk was used in these strikes.
Imagery of many other different munitions used by the US, Israel and Iran have appeared on social media.
This article covers some of the munitions Bellingcat has seen imagery of as the war enters its fourth day.
Many of the weapons used so far have also been deployed in other recent US conflicts, including the 12-day Israel-Iran war, and US strikes in Yemen and Venezuela.
The US is the major supplier of arms to allies in the region, including for Israel, Kuwait, Qatar, UAE, and Jordan.
On Sunday, the US Department Of Defence (DOD) published photos showing weapons being prepared for loading on aircrafts, including the MK-80 series of bombs like MK-82 500-pound bombs, and BLU-109 2,000-pound ‘bunker busters’ equipped with Joint Direct Attack Munition (JDAM) bomb guidance kits.

The DOD has also released several photos showing the C variants of the AGM-154 Joint Standoff Weapon (JSOW). As documented by the Open Source Munitions Portal, this weapon has been used recently by the US in Yemen and Venezuela.

The DOD also released a slideshow showing images from the first 24 hours of the war, including an image showing the first combat use of the Precision Strike Missile. The DOD further released a list of some equipment used, including the THAAD ballistic missile defense system.

Many of the weapons deployed by the US have also been used by Israel. This includes the MK-80 series of bombs, BLU-109 bombs and Joint Direct Attack Munition (JDAM) bomb guidance kits.

Israel also produces some of its own munitions, which they released video or photos of since the start of the conflict, including MK-83 1,000-pound bombs equipped with Israeli SPICE-1000 bomb guidance kits.

Israel also produces RAMPAGE missiles, visible in the image below.

On Sunday, the DOD said they had used the Low-cost Unmanned Combat Attack System (LUCAS) one-way attack drones in strikes. The LUCAS drone is a US copy of the Iranian Shahed one-way attack drone.

A video of a crashed LUCAS drone has subsequently appeared online, reportedly in Iraq.
While Bellingcat could not geolocate this video, then men seen in the footage can be heard speaking Arabic while US CENTCOM has said that this is the first time they have used this drone in combat.
Local Iraqi residents are taking the newly deployed, nearly intact American LUCAS drone for themselves. pic.twitter.com/fbx411iAYU
— Special Kherson Cat(@bayraktar_1love) March 2, 2026
A video shows a LUCAS drone that allegedly crashed in Iraq.
Iran has retaliated by firing one-way attack drones, including Shahed variants, and missiles at Israel, and US-bases in various countries across the region, including UAE, Qatar, Kuwait, Jordan and Iraq.
Iranian Shahed drones have hit civilian buildings in the Gulf, as well as US military bases.
Palm Jumeirah in Dubai was attacked by Shahed kamikaze drones.
—
[image or embed]Special Kherson Cat
(@specialkhersoncat.bsky.social) 28 February 2026 at 15:37
A Shahed drone crashes into a hotel in Dubai on Feb. 28.
In Bahrain, a Shahed was seen crashing into a residential building on Feb. 28.
Virtually a first person view of the Iranian drone hitting the high-rise building in Manamah, Bahrain.
— (((Tendar))) (@tendar.bsky.social) 28 February 2026 at 18:57
[image or embed]
A Feb. 28. video shows a Shahed drone hitting a residential tower in Bahrain.
Many missiles have a booster, a rocket motor that detaches from the missile after it is expended. These boosters fall to the ground under the flight path of the missile.
Bellingcat verified that Iranian missile boosters have fallen in nearby countries caught in the crossfire, including Qatar and Jordan (see below post geolocated to Al-Hashmi St. in Irbid, Jordan), while some Israeli boosters have reportedly fallen in Iraq.
اهلنا في اربد الله يحميكم pic.twitter.com/LvHWgicE4F
— فواز الذياب (@FawazElziyab) February 28, 2026
A Feb. 28. post shows an Iranian ballistic missile booster that fell on Al-Hashmi St. in Irbid, Jordan.
The US and Israel, as well as several Gulf countries, have fired missiles, intended to destroy Iranian missiles or drones in the air before they reach their targets. Many Iranian weapons have been intercepted, but others have successfully hit, including in a strike on a US command post in Kuwait, killing six US troops.
Most ballistic missile interceptors are “hit-to-kill” where they are designed to destroy missiles by the impact. These interceptors have their own components that fall to the ground, as well as the debris from interceptions.
Remnants of Patriot Interceptor missiles, which are operated by the US and several Gulf countries, have been seen, and countries including the UAE have reported they have intercepted missiles. The UAE has claimed that 165 missiles and 541 drones were fired at the country, most were intercepted.

Many close-up images of munition debris have been posted on social media over recent days which are difficult to geolocate. While we have not been able to verify the location of these munitions, we used reverse image search tools to verify they had not been posted online prior to the current conflict. The munition remnants are also consistent with those used by the US, Israel and Iran. But as we cannot geolocate or chronolocate them yet, we cannot fully verify them. Many of these images have been posted with false claims about the object and who fired it.
Despite Bellingcat being unable to fully verify them, we are including a selection of them with accurate identifications, due to the likelihood that more images of these same objects will continue to appear online as the war continues.
One example of incorrectly identified munitions, is the below picture of an aircraft’s external fuel tank, or drop tank that was posted on Telegram on March 1 alongside the claim that it is an Israeli missile.
A Mar. 1. image shows a drop tank from an Israeli jet reportedly found in Anbar, Iraq. Source: NAYA.
Drop tanks are used on jets to extend the range and are jettisoned after use, resulting in these tanks falling to the ground. These tanks have been mistaken for missile parts in previous conflicts.
Despite Iran’s prevalent use of missiles, not all missile boosters are Iranian. On February 28 missile boosters from Israeli air-launched ballistic missiles were reportedly found just east of Tikrit, Iraq. The below image shows the booster from Israel’s Blue Sparrow series, and can be matched to images previously identified and posted on the likes of the Open Source Munitions Portal.
A short while ago, a missile landed near Duraji village in the Dauda area of the Khurmatu district.#Isreal #Iran pic.twitter.com/qzZLNUgekD
— Sarwan Wllatzheri (@SarwanBarzani_) February 28, 2026
A Feb. 28. post shows an Israeli Blue Sparrow series missile booster, reportedly found in Duraji, Iraq.
Additionally, unexploded WDU-36/B warheads from Tomahawk missiles were reportedly found –, one in Kirkuk, Iraq and one found near Jablah, Syria. Tomahawk warheads and other remnants are frequently misidentified, often as drones.

These titanium cased warheads comprise a small part of the much larger Tomahawk missile, and have been found intact in numerous countries when the warhead has failed to explode, as seen in images shared on the Open Source Munitions Portal.
Unexploded Tomahawk warheads from strikes in other conflicts have also been identified by the Open Source Munitions Portal .
Remnants of an Israeli Arrow 2 interceptor missile were posted online, falsely identified as an Iranian missile, and were allegedly found in eastern Syria. These images could again be matched to those found from previous conflicts on the Open Source Munitions Portal.
An Iranian missile fell in Al-Shoula area, south of DeirEzzor eastern Syria!. pic.twitter.com/TsWVuda2nf
— Omar Abu Layla (@OALD24) March 1, 2026
A Israeli Arrow 2 interceptor missile falsely identified as as an Iranian missile in a post on X.
One photo of a remnant reportedly found in Ahvaz, Iran, included a false claim that it was a US ATACMS missile. Bellingcat was able to confirm the image does not match ATACMS construction by comparing it to imagery of that munition. We have as yet been unable to confirm if it was indeed located in Ahvaz, Iran – although we were able to identify the munition.
U.S. ATACMS tactical ballistic missile remains found in Ahvaz, Iran.@Osinttechnical pic.twitter.com/plytSUI4w6
— Open Source Intel (@Osint613) March 1, 2026
An actuator section of a MIM-23 HAWK missile, falsely identified by the post above as an ATACMS missile.
The markings on the remnant include an “FSN” or federal stock number, that can be looked up to identify the item. The FSN was replaced by the national stock number (NSN) in 1974, meaning this missile was produced prior to 1974.

Bellingcat looked up the FSN/NSN (1410002343266) which corresponds with the US manufactured MIM-23B HAWK, an air defence missile.

There are many other US, Israeli and Iranian munitions that may have been used in the current conflict, but images have not yet appeared on social media.
With fresh strikes carried out overnight/ early Tuesday and President Trump saying that “likely more” US troops will die, the conflict continues to escalate and shows no sign of ceasing in the days ahead. And despite the death of Ayatollah Ali Khamenei the Iranian regime has vowed revenge and continued strikes against Israel, the US and their Gulf allies.
Bellingcat’s Carlos Gonzales, Jake Godin and Felix Matteo Lommerse contributed research to this article. Anisa Shabir from Bellingcat’s Volunteer Community also contributed to this piece.
Bellingcat is a non-profit and the ability to carry out our work is dependent on the kind support of individual donors. If you would like to support our work, you can do so here. You can also subscribe to our Patreon channel here. Subscribe to our Newsletter and follow us on Bluesky here, Instagram here, Reddit here and YouTube here.
The post “Bombs will fall Everywhere”: The American, Israeli and Iranian Weapons Being Deployed in Middle East appeared first on bellingcat.
The following intelligence brief was sent to all SentinelOne partners and customers today:
Recent U.S. and Israeli strikes against Iranian targets, followed by Iranian attacks on multiple regional locations, present a highly dynamic geopolitical situation with credible cyber threat implications. Iran has historically incorporated cyber operations into periods of regional escalation.
Given the rapid escalation of geopolitical tensions, we assess that Iranian state-aligned cyber activity is likely to intensify in the near-term based on a long track record of leveraging cyber operations for asymmetric retaliation, coercive signaling, and strategic messaging. Prior campaigns, including destructive wiper malware, infrastructure disruption, and influence operations masquerading as ‘hacktivism’, demonstrate both capability and intent to operate in the cyber domain alongside kinetic action.
This report outlines Iran’s historical cyber posture, relevant tactics and tradecraft, and our forward-looking assessment of potential cyber responses in the days and weeks following the airstrikes.
We assess with high confidence that organizations in Israel, the United States, and allied nations are likely to face direct or indirect targeting – particularly within government, critical infrastructure, defense, financial services, academic, and media sectors.
We recommend that all clients, especially those operating in, or supporting, U.S. and Israeli infrastructure, review their security posture and preparedness accordingly.
This assessment is current as of February 28, 2026 and reflects a rapidly evolving threat environment.
Iran presents a mature, well-resourced cyberthreat based on more than fifteen years of experience across a wide range of malicious cyber events.
Iran uses a diverse set of cyber tools to further state objectives, particularly preservation of the Iranian regime, including:
Iranian cyber actors previously aligned their operations with kinetic campaigns, often acting as a force multiplier for regional allies like Hamas or as a standalone tool of retaliation. The TTPs employed by Iranian hacktivists increasingly mirror those used by state-sponsored APTs, raising critical questions about capability sharing and formal command-and-control relationships within this environment.
Expect escalated targeting of Israeli defense, government, and intelligence networks using spearphishing, credential harvesting, and deployment of custom malware. Historically, groups such as APT34 (OilRig) and APT42 (TA453) leveraged legitimate access to move laterally and exfiltrate strategic intelligence. Additionally, U.S. military and government organizations will likely be targeted in similar campaigns.
Anticipated Targets:
Iran has a well-documented history of using destructive malware and DDoS attacks to disrupt the critical infrastructure of its adversaries. We assess a high likelihood of similar tactics being deployed against U.S. and Israeli sectors, particularly utilities and public-facing systems.
Key techniques include:
Anticipated Targets:
Iranian-aligned actors are likely to amplify disinformation campaigns to shape public perception, particularly around civilian impact, military failure, and geopolitical instability. These efforts often run concurrently with real-world escalations and aim to degrade public trust in institutions.
Anticipated Themes:
Iran has demonstrated readiness to expand attacks to Western infrastructure during periods of high tension. Recent examples include the exploitation of Unitronics PLCs at U.S. water treatment plants (late 2023), highlighting a shift toward ICS/OT targets. Such actions serve retaliatory and signaling purposes and are often designed to be low-impact yet high-visibility to maximize psychological effect.
Anticipated Targets:
SentinelOne research and detection teams have closely followed Iranian cyber actors for many years. We provide multiple layers of protection and are closely monitoring emerging threat intelligence to maximize coverage.
We extensively cover techniques known to be used by Iranian threat groups including:
These protections are not Iran-specific but known to be effective in detecting their operations.
We are monitoring the situation closely and can ship new detections quickly through Platform Rules updates or Live Security Updates.
For maximum protection, we recommend:
SentinelOne is proactively hunting for IOCs and TTPs associated with these groups. These threat hunts are being performed for all Wayfinder Threat Hunting customers. Any related hunt findings will be visible in the Wayfinder Threat Hunting dashboard.
This report is intended to support informed decision-making and proactive defensive measures amid a dynamic and escalating geopolitical conflict.
The cyber threat landscape associated with Iranian state-aligned actors is adaptive, and we assess that both targeting priorities and tactics may shift rapidly in response to real world developments, political statements, or perceived provocations.
We advise clients to treat this as a time-sensitive assessment and to revisit posture, incident response, and monitoring processes regularly.
For immediate questions or escalations, please contact your Client Success Lead or reach our Support teams directly at: https://www.sentinelone.com/global-services/get-support-now/
Customers should consider activating Platform Detection Library rules to improve coverage. The following rules are known to be effective against Iranian cyber operations:
MuddyWater
Credential Dumping
Tunneling & Remote Access
Collection & Exfiltration
PowerShell/Script Abuse
Defense Evasion, Impact, Discovery

Internet access across Iran was drastically reduced on Saturday as Israel and the United States carried out strikes against the country, according to independent and non-partisan global internet monitor NetBlocks.
یک شهروند روز شنبه با ارسال ویدیویی میگوید که سهراه ضرابخانه در تهران و وزارت اطلاعات هدف گرفته شده است. pic.twitter.com/qniNzip9F9
— ايران اينترنشنال (@IranIntl) February 28, 2026
Network data indicated a near-total nationwide blackout.
“Confirmed: Network data show #Iran is now in the midst of a near-total internet blackout with national connectivity at 4% or ordinary levels. The incident comes amid US and Israeli combat operations and matches measures used during last year’s war with Israel.” wrote NetBlocks.
— NetBlocks (@netblocks) February 28, 2026
Confirmed: Network data show #Iran is now in the midst of a near-total internet blackout with national connectivity at 4% or ordinary levels. The incident comes amid US and Israeli combat operations and matches measures used during last year's war with Israel. pic.twitter.com/1XunOr4Q19
NetBlocks noted that the disruption resembles measures previously seen during last year’s conflict with Israel, suggesting authorities may have intentionally restricted connectivity amid escalating tensions.
Cloudflare also confirmed that Internet traffic in the country has dropped to effectively zero as of 18:45 UTC (22:15 PM local time), signaling a complete shutdown in the country and disconnection from the global Internet.
#Internet traffc in #Iran has dropped to effectively zero as of 18:45 UTC (22:15 PM local time), signaling a complete shutdown in the country, and disconnection from the global Internet.https://t.co/V77cj6rrQW pic.twitter.com/yZjOBqsGJm
— Cloudflare Radar (@CloudflareRadar) January 8, 2026

Iran’s internet shutdowns are widely viewed as tools for regime control. Teheran may use it to curb information flows, and reduce foreign pressure or cyber threats against critical infrastructure. By cutting or throttling connectivity during crises, authorities hinder external cyber operations and limit reconnaissance while also disrupting internal coordination, protest organization, and real-time reporting of damage or abuses.
Large-scale cyberattacks reportedly struck Iran alongside Saturday’s military strikes by Israel and the U.S., disrupting major domestic platforms. According to local media, websites of key news agencies, including IRNA and ISNA, experienced significant outages. As state media faltered, many Iranians turned to foreign opposition sites and social media platforms such as Instagram and Telegram for updates, wherever internet access remained available.
Update March 1st, 2026
NetBlocks says Iran’s internet blackout has now lasted over 24 hours, with national connectivity stuck at about 1 % of normal levels as of Sunday. The shutdown is occurring amid escalated conflict after US and Israeli airstrikes, including reported hits on major sites following the death of Iran’s Supreme Leader. The prolonged blackout has sharply restricted communication, reducing civic engagement and access to information at a critical moment for the country’s future.
— NetBlocks (@netblocks) March 1, 2026
Update: #Iran's internet blackout has now passed the 24-hour mark with national connectivity flatlining at 1% of ordinary levels.
The measure limits civic engagement at a key moment for the country's future after the killing of Ayatollah Khamenei in US and Israeli airstrikes. pic.twitter.com/W4jDgds1Ty
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
(SecurityAffairs – hacking, Iran)
To stay up to date on our latest investigations, join Bellingcat’s WhatsApp channel here
On the night of Jan. 7 this year, three 250-pound bombs smashed into an apartment block in the Al Tuffah neighbourhood of northern Gaza. Footage of the aftermath shows walls collapsed, rubble piled up and blackened household items scattered across the scene.
Although a ceasefire has been in effect since October, and a Board of Peace led by US President Donald Trump has been announced to begin phase two of that process, Israel has continued to conduct strikes within Gaza
The IDF claimed they targeted a senior Hamas operative in response to a violation of the ceasefire agreement in the Jan. 7 attack.
Two people were reported to have been killed.
While the strike was an Israeli operation, among the debris were munition remnants of at least three US-made GBU-39 Small Diameter Bombs, including one that failed to explode.

American-made munitions like these have played a significant role in Israel’s operations in Gaza.
The US has provided billions of dollars worth of military aid to Israel over the years, and has enacted legislation providing at least US$16.3 billion in direct military aid since the most recent war began. In the first few months of the Trump Administration nearly $12 billion in major weapon sales to Israel were approved with deliveries scheduled to take years to complete.
However, human rights groups like Amnesty International and Human Rights Watch have said that US-made weapons have been used in Gaza in ways that have likely violated international law. Multiple international media reports have also identified individual instances of civilian harm likely caused by US weaponry deployed by Israel in Gaza.
A 2024 State Department report, completed during the administration of former President Joe Biden, even stated that due to Israel’s “significant reliance on US-made defence articles it is reasonable to assess” that they have been used in “instances inconsistent with its IHL [International Humanitarian Law] obligations or with established best practices for mitigating civilian harm” — although Israel says it operates within international law and seeks to mitigate civilian harm while aiming to dismantle Hamas’ military capabilities.

Your donations directly contribute to our ability to publish groundbreaking investigations and uncover wrongdoing around the world.
Yet the full extent of civilian harm in Gaza caused by the use of US-produced weapons remains unclear.
Foreign media are not allowed into Gaza and the documentation of events there has relied heavily on social media footage and the work of local journalists, many of whom have been killed in Israeli air or ground strikes while carrying out their work.
Bellingcat has collated scores of incidents like the Jan. 7 strike in Al Tuffah where US-produced munitions have been found in the aftermath of Israeli strikes.
This analysis utilises publicly available media footage and identifies at least 79 specific cases, many of which caused death and damage to civilian infrastructure such as schools, homes and healthcare infrastructure.
While revealing, it is important to note that the data comes with some significant caveats and limitations that must be acknowledged before exploring it.
Gaza has been pummelled since the Hamas attacks of Oct. 7, 2023, when more than 1,200 Israelis were killed and hundreds more kidnapped.
In response, Israel is reported to have deployed 30,000 munitions into Gaza in the first seven weeks of the conflict alone. The Israeli Airforce has also bombed over 100 different targets in Gaza in a single day multiple times.
This dataset – which details cases where US-made munition remnants have been found and evidence of their use published in media or posted to social media – therefore only captures a small fraction of the overall incidents over more than two years of war.
Furthermore, Israel and the US both produce some of the same munitions, such as the MK-80 series of bombs. The US supply of this series, especially the 2,000-pound MK-84 of which over 14,000 have reportedly been delivered since Oct. 7 2023, have been central to calls for the suspension of US arms transfers to Israel due to their destructive potential.
But because Israel also makes these bombs domestically the country of origin cannot be definitively identified without specific remnants that show either the lot number, indicating the manufacturer, or other identifying information.

As a result a decision was made to try and track the use of three specific munitions that are made solely in the US and which Israel does not domestically produce. This, again, significantly reduced the number of incidents analysed.
These munitions were Hellfire missiles, GBU-39 Small Diameter Bombs and Joint Direct Attack Munition (JDAM) bomb guidance kits. While this analysis does not track MK-80 series bombs, the JDAM kit is one of several guidance kits that can attach to bombs like the MK-84 but which is only produced by the US.
The full dataset can be found here. The munition identifications were reviewed by Frederic Gras, an independent Explosive Remnants of War (ERW) Expert and Consultant.

Despite all of the above caveats and limitations, the analysis recorded 79 geolocated incidents where remnants of these three models of US-made munitions were either found in the aftermath of a strike or were captured in visual imagery in the moments before impact.
Beyond the 79 cases analysed and included in the dataset, other US-made munitions were identified in a further 26 cases, although it was not possible to geolocate the remnants or strikes prior to publication. It may be possible to geolocate the outstanding incidents in time. Bellingcat is, therefore, including these incidents in the dataset but notes further work is required for them.
Many of the geolocations in the dataset were initially posted publicly by independent geolocators, or volunteers from the GeoConfirmed community, including Anno Nemo, Abu Location, fdov, Chris Osieck, Zvi Adler and Will Cobb. These geolocations were independently checked and verified by Bellingcat.
Subscribe to our newsletter for first access to our published content and events that our staff and contributors are involved with, including interviews and training workshops.
For the 79 incidents it was possible to geolocate, Bellingcat sought to compile reports of civilian harm. Yet given the lack of access afforded to international observers it was not possible to independently verify each of these reports of casualties or fatalities.
The reports, many of which cite health authorities in Gaza, detailed that at least 744 people were killed in these 79 strikes, including at least 78 women and 175 children. When reports offered a range for the number killed, or number of women and children killed, Bellingcat used the lower end of the estimate.
Israel rarely provides estimates for civilian casualties from their strikes. It has also claimed that the Gaza Ministry of Health has exaggerated death tolls after specific strikes. Analysing previous public reporting of each incident in the dataset, Bellingcat found that the IDF had claimed at least 69 people that were reported killed in these attacks were militants belonging to Hamas or other factions. In one strike, where at least 33 people were reported killed, the IDF claimed to have targeted “dozens” of Hamas members, releasing the names of 17 people they said were part of Hamas.
Bellingcat asked the IDF if they could provide a total for the number of people killed in the attacks listed in the dataset or for any specific strikes but they did not provide a figure. A spokesperson for the IDF provided information for eight strikes within the dataset that it said sought to hit “terrorist targets”. Bellingcat has noted this response beside each incident in the dataset.
The spokesperson added that Israel “strikes military targets and objectives in accordance with international law and takes all feasible measures to mitigate harm to civilians and civilian structures as much as possible.”
The Gaza Ministry of Health has reported that over 70,000 Palestinians have been killed in the conflict. While Israel has long disputed those casualty figures, Israeli media recently cited anonymous Israeli Defence Force (IDF) sources who said they believed them to be largely accurate. Israel has claimed to have killed about 25,000 militants in Gaza.
Attacks on schools, mosques, shelters and residences are all included in the dataset. In total, 28 strikes on schools using US made munitions were identified. GBU-39 bomb remnants were found at the site of 20 of these strikes. Most of these took place before the ceasefire of January 2025.
For example, the Khadija school in Deir Al Balah was targeted in three rounds of airstrikes on July 27, 2024 that used both GBU-39 bombs and MK-80 series bombs equipped with JDAM kits. Satellite imagery before and after the strike showed significant damage to the facility.

Video from the ground provided more detail, showing that the first round of airstrikes targeted five different areas of the school complex.
The unexploded bomb body of a GBU-39 was found inside the school, while the fuzewell from a GBU-39 bomb that exploded was photographed near the destroyed gate structure.

An evacuation notice was then reportedly issued, and two buildings on the eastern side of the complex were targeted with larger bombs, leveling the buildings there. An additional evacuation notice was reportedly issued before a third strike.
A video of the third strike shows at least six people, including a child, visible within approximately 55 meters of where a bomb equipped with a US-made JDAM kit hit one of the already collapsed buildings on the eastern side of the complex.

These three strikes killed at least 30 people, including 15 children and eight women, according to reports collated by Airwars. At least 100 were injured, according to the same reports. Most people were reportedly harmed in the initial strikes, according to the UN Office of the High Commissioner for Human Rights.

The United Nations reported at the end of February 2025 that 403 of 564 school buildings in Gaza had been “directly hit” in some manner, either by airstrikes or by other munitions. School buildings are often used as shelters. However, Israel has claimed in some instances that they were being used as Hamas command centres.
After the war resumed in March 2025, recorded strikes on schools generally appeared to use Israeli-made munitions. Only two strikes on schools since then were found to have used US made munitions – a May 2025 attack on the Fahmy Al Jarjawi school with at least three US-made GBU-39 bombs that killed 36 people, according to hospitals in Gaza, and a July 2025 strike on Cairo Basic School where five people were reported killed and where remnants of a Hellfire missile was found.

While the dataset shows no other attacks on schools using US munitions after this period, it is important to note that there may have been other instances where US-made munitions were used in such circumstances but which were not recorded.
Two strikes using US-made munitions to directly target medical facilities were identified in this analysis. A Hellfire missile was used in a June 2024 strike on a health clinic in Gaza City that killed Hani al-Jafarawi, the director of ambulance and emergency services in Gaza. However, the IDF claimed the strike had killed “the terrorist Muhammad Salah, who was responsible for projects and development in Hamas’ Weapons Manufacturing Headquarters”.
The Gaza Civil Defence Headquarters in Al Daraj, Gaza City, was also targeted with a US-made GBU-39 bomb in September 2024. The bomb penetrated multiple floors but failed to explode, causing injuries but no deaths.
Five instances of US-made munitions being used for strikes near medical facilities were also identified. Four of these strikes used Hellfire missiles to target tents within approximately 150 meters of the Al Aqsa Martyr’s Hospital Main Complex in Deir Al Balah.

The fifth strike used a US JDAM likely attached to a MK-82 500-pound bomb to target the Al Aqsa Mosque across the street from the hospital, approximately 50 meters away from the main hospital complex. This strike killed 26 people, according to the Gaza Ministry of Health.
A US Marine Corps manual on Close Air Support states that a MK-82 bomb delivered within 425 meters is considered “danger close”, with a bomb delivered within 250 meters being 100 times more dangerous than the minimum “danger close” standard.
Twenty-six strikes were identified where US munitions were used to target buildings including homes, schools and mosques after an evacuation notice was issued by the IDF. In 23 of these strikes there was no reported harm. However, there was significant harm recorded in others even with evacuation notices.
Evacuation notices are notifications that provide advance warning of strikes and can be made on social media or sent to people’s phones. These notices often provide journalists on the ground time to set up cameras to record the incoming strikes. Such videos are occasionally of high enough quality to identify the bomb guidance kit attached as JDAMs kit as they fall, as can be seen in the video below.
لحظة قصف مسجد الألباني في مدينة خانيونس بصاروخين من طيران الحربي .
— عبدالله العطار abdallah alattar (@abdallahatar) August 1, 2025
The moment the Al-Albani Mosque in Khan Younis
was bombed with two missiles by warplanes.: Abdallah Alattar / Anadoluimages
1 أغسطس 2025 pic.twitter.com/U3Tad0veA6
By Sept. 17, 2025 Israel said it had destroyed 25 high-rise buildings in preparation for their assault on Gaza City. Bellingcat was able to identify that at least seven high-rise buildings in Gaza City, including Al Soussi Tower, Al Roya Tower, and Al Roya 2 Tower, were issued evacuation notices then destroyed using MK-80 series bombs with JDAM kits.

The Aybaki Mosque, built in the 13th century, was also hit with MK-80 series bombs with JDAM kit, which the IDF told Bellingcat was a strike targeting the “deputy commander of heavy machine guns unit in Hamas, Khaled Nabil Saleh Shabat”. The IDF has claimed that these tall buildings host Hamas infrastructure, including observation posts and prepared attack positions.
The public warnings posted by the IDF for buildings targeted in Gaza City in September 2025 alerted residents of specific blocks, as well as those in the target building and adjacent tents to leave and head south towards the IDF declared humanitarian zone.
Prior to strikes in Lebanon where the IDF issued evacuation notices, maps were publicly posted requesting civilians evacuate at least 500 meters away. However, a review of public posts by the IDF for evacuation notices in Gaza from September 2025 found no notices that provide a specific evacuation distance.
Bellingcat asked the IDF if the content of evacuation notices sent to people’s phones differ in content from those publicly posted and why evacuation notices in Gaza appeared to not provide a recommended evacuation distance like those issued by the IDF in Lebanon. The IDF told Bellingcat that they issue “clear and detailed advance warnings through multiple channels, including communications published by the IDF Arabic Spokesperson and enables the civilian population to evacuate before strike.”
The distance people are told to evacuate prior to strikes is important as fragments from bombs, or the buildings being targeted, can still kill or injure people hundreds of meters away.
In one strike where an evacuation notice was given before the strike, a four-year-old girl, Razan Hamdiye, was reported killed. One person was also reported killed in the strike on the AlRoya tower.
After the airstrike targeting the Harmony Tower, a graphic video captured by the Anadolu Agency showed a group of people about 120 meters away had been either killed or injured by the strike, despite the evacuation notice.
US-made munitions have also been used in other IDF strikes, including one which reportedly killed the leader of Hamas’ Military Wing, Mohammed Deif. At least 90 people were reported killed in this attack and US-made JDAM remnants recovered. US munitions were also used in the September 2025 strike that reportedly killed Hamas Spokesman, “Abu Obayda” and at least six other people, where remnants of US-made GBU-39 bombs were found.
American-made munitions were also used alongside other unidentified munitions in the June 2024 IDF hostage rescue operation in Nuseirat, where 274 people were reportedly killed. These 274 deaths are not included in the 744 people reported killed in the incidents contained within the dataset due to the inability to identify the other weapons used in at least 13 strikes that occurred during the operation.
Bellingcat reached out to the IDF, the US Department of State, and the US Department of Defense before publishing this story. Bellingcat also asked the primary contractors for these munitions, Boeing and Lockheed Martin, about whether they track how their products are used in Gaza.
Boeing, which manufactures the GBU-39 bomb and JDAM bomb guidance kit did not respond. Neither did Lockheed Martin, which makes the AGM-114 “Hellfire” missile.
The Department of Defense declined to comment.
A spokesperson for the US Department of State said “The US Government is not able to make such determinations” when asked how many civilian deaths could be attributed to the use of US-made weapons in Gaza.
Bellingcat asked if the State Department held a different assessment than the NSM-20 which was introduced under President Biden and determined that it was reasonable to assess that US-made weapons were used by Israel in instances “inconsistent with its IHL obligations or with established best practices for mitigating civilian harm”. The spokesperson said “NSM-20 is no longer US policy.”
The State Department referred other questions about the use of the munitions highlighted in this article to the Israeli Defence Forces, who told Bellingcat that they do not detail the munitions they employ and that Hamas exploits “civilian infrastructure for terrorist purposes”.
Jake Godin and Carlos Gonzales contributed to this report.
Afton Briones, a member of Bellingcat’s Volunteer Community, contributed research to this piece.
Bellingcat is a non-profit and the ability to carry out our work is dependent on the kind support of individual donors. If you would like to support our work, you can do so here. You can also subscribe to our Patreon channel here. Subscribe to our Newsletter and follow us on Bluesky here and Mastodon here.
The post Made in the USA: How American-Built Weapons Have Wrought Destruction in Gaza appeared first on bellingcat.
In the early hours of June 13, Israeli missiles slammed into apartment buildings across the Iranian capital, Tehran.
By morning, it became apparent that nine men Israel said were closely associated with the country’s nuclear programme were dead.
Videos posted to social media showed buildings in flames and rescue workers sifting through rubble as they looked for survivors.
Dozens of civilians who lived in the same apartment blocks as those targeted also died in the strikes. In one instance, a 14-storey residential tower completely collapsed.
But this was just the start, the opening shots of what Israel dubbed Operation Rising Lion – a 12-day operation targeting Iranian scientists, nuclear sites, security figures and military capabilities.
While Iran sought to fight back, launching missiles and drones at Israel, the damage and death toll inflicted by Israel was far greater.
On day 10 of the operation, the United States joined with Israel, carrying out strikes on nuclear sites at Fordow, Natanz and Isfahan.
Bellingcat worked with FRONTLINE (PBS), The Washington Post and Evident Media to piece together the events of the 12-day war to try and understand the true impact of the strikes on Iran’s nuclear programme. Iran maintains the programme is peaceful but Israel has long suspected that it is designed to develop nuclear weapons.
FRONTLINE filmmakers were given access to Iran, where they visited the sites of some of the strikes and spoke to neighbours and relatives of those who were killed as well as high-ranking Iranian officials.
The Washington Post also spoke to senior intelligence and military sources involved in Operation Rising Lion, and the filmmakers visited Vienna to speak with the International Atomic Energy Agency (IAEA), the organisation that has been responsible for monitoring Iran’s nuclear programme.
Bellingcat, alongside The Washington Post, analysed open source information such as satellite imagery, social media footage, local media coverage, death notices and cemetery records to understand how the attacks on Iranian scientists unfolded as well as analyse the civilian cost of the conflict.
US viewers can watch the full film below.
Full reporting reporting from The Washington Post on this topic can be found here and seen on FRONTLINE’s YouTube channel, at pbs.org/frontline, on PBS stations and in the PBS App.
Trevor Ball, Carlos Gonzales, Sebastian Vandermeersch and Eoghan Macguire reported for Bellingcat. Sebastian Walker and Adam Desiderio reported for PBS Frontline. Nilo Tabrizy and Jarrett Ley reported for The Washington Post.
Bellingcat is a non-profit and the ability to carry out our work is dependent on the kind support of individual donors. If you would like to support our work, you can do so here. You can also subscribe to our Patreon channel here. Subscribe to our Newsletter and follow us on Twitter here and Mastodon here.
The post Investigating the Impact of US-Israeli Strikes on Iran’s Nuclear Programme appeared first on bellingcat.
A escalada de tensões entre Irã e Israel ganha um novo e perigoso capítulo no ciberespaço. Um relatório divulgado pela Check Point Research revela que o grupo de ciberespionagem iraniano conhecido como Educated Manticore, com ligações diretas ao Corpo da Guarda Revolucionária Islâmica (IRGC-IO), intensificou campanhas direcionadas contra acadêmicos, jornalistas e especialistas de tecnologia israelenses.
De acordo com a investigação, o Educated Manticore concentrou esforços em atacar profissionais de alto nível, incluindo professores de ciência da computação de universidades renomadas de Israel, pesquisadores de cibersegurança e jornalistas. As ações, sofisticadas e cuidadosamente planejadas, fazem parte de uma ofensiva de espionagem digital que visa obter acesso indevido a contas de e-mail e outros serviços críticos.
Os invasores se passam por pesquisadores, executivos ou analistas de empresas de cibersegurança fictícias, estabelecendo contato inicial por e-mail ou até mesmo por mensagens no WhatsApp. Com uma comunicação polida, bem estruturada e aparentemente legítima — muitas vezes auxiliada por inteligência artificial —, os criminosos buscam conquistar a confiança das vítimas e direcioná-las para links maliciosos.
Uma vez estabelecido o contato, os alvos são conduzidos para falsas páginas de login do Gmail, Outlook ou Yahoo, desenvolvidas com tecnologia moderna baseada em Single Page Applications (SPA) usando React. Essas páginas simulam com precisão o fluxo de autenticação de grandes provedores de e-mail, incluindo etapas de autenticação multifator (2FA), captura de senhas e códigos de verificação.
Além disso, o kit de phishing desenvolvido pelo grupo conta com keyloggers ocultos, capazes de registrar todas as teclas digitadas, mesmo que o usuário não finalize o processo. As informações são transmitidas em tempo real para os servidores dos atacantes, potencializando o roubo de credenciais e comprometendo ainda mais as contas das vítimas.
Um aspecto que chamou atenção dos analistas foi o uso de convites falsos do Google Meet, hospedados no próprio serviço Google Sites, o que dá uma aparência ainda mais legítima às páginas maliciosas. Ao clicarem nas imagens desses convites, as vítimas são redirecionadas a sites sob o controle dos atacantes.
A infraestrutura da Educated Manticore é ampla e bem estruturada. Desde janeiro de 2025, o grupo registrou mais de 130 domínios diferentes — muitos relacionados a temas como tecnologia, comunicação e educação —, utilizados para hospedar as páginas de phishing e gerenciar as operações clandestinas. A maioria desses domínios foi registrada através do provedor NameCheap.
Os especialistas também identificaram uma sobreposição significativa com outra célula de operações, conhecida como GreenCharlie, o que sugere uma possível ramificação ou subgrupo da Educated Manticore atuando de forma coordenada.
Entre os domínios maliciosos monitorados estão sendly-ink[.]shop, idea-home[.]online, live-meet[.]info, bestshopu[.]online, entre muitos outros. Além disso, diversos endereços IP associados à operação foram mapeados, fortalecendo as evidências de uma infraestrutura técnica bem organizada.
Apesar da crescente exposição e dos esforços da comunidade de segurança cibernética, o Educated Manticore segue atuando com rapidez e agressividade, demonstrando grande capacidade de adaptação e evasão. A campanha atual, ao explorar o contexto geopolítico e acadêmico, representa uma ameaça grave à integridade das instituições israelenses e ao ecossistema global de cibersegurança.
“Esses ataques evidenciam como o ciberespaço se tornou um dos principais campos de batalha no atual conflito Irã-Israel”, alertam os pesquisadores da Check Point. A expectativa é de que o grupo continue investindo em táticas de roubo de identidade e coleta de informações, principalmente de indivíduos envolvidos em ambientes acadêmicos, científicos e tecnológicos estratégicos.
A Check Point Research divulgou uma lista de domínios e endereços IP associados à infraestrutura maliciosa do Educated Manticore. Profissionais e empresas de tecnologia são fortemente aconselhados a implementar medidas de monitoramento e bloqueio desses indicadores em suas redes.
Entre os principais IOCs identificados estão:
Endereços IP:
185.130.226[.]71
45.12.2[.]158
45.143.166[.]230
91.222.173[.]141
194.11.226[.]9
Domínios Notórios:
sendly-ink[.]shop
idea-home[.]online
live-meet[.]info
bestshopu[.]online
live-message[.]online
A lista completa de domínios e IPs está disponível no relatório técnico da Check Point.
O caso do Educated Manticore reforça o papel crítico da cibersegurança no cenário geopolítico atual. A sofisticação técnica, combinada a uma estratégia agressiva de engenharia social, demonstra que grupos apoiados por Estados seguem explorando vulnerabilidades humanas e tecnológicas para alcançar seus objetivos de espionagem.
Especialistas recomendam vigilância redobrada, treinamentos contínuos de conscientização e o uso de autenticação forte e verificada, especialmente entre profissionais que atuam em áreas sensíveis de tecnologia e pesquisa.
Scroll Down to view interactive photogrammetry produced for this story; you can expand both models to view them in full screen mode and explore them for yourself. You can view a video version of this story, here.
According to the Committee to Protect Journalists (CPJ), at least 165 Palestinian journalists have been killed since the Israel-Hamas war began in October 2023. In fact, according to CPJ, last year was the deadliest year for journalists worldwide since they began documenting deaths in 1992.
Gathering aerial footage of Gaza is a dangerous task, and Bellingcat along with our partners at Forbidden Stories, Le Monde, Die Zeit, Der Standard, Paper Trail Media, Arab Reporters for Investigative Journalism (ARIJ) and RFI identified several cases where drone journalists were killed or injured shortly after capturing aerial images.
The Gaza Project is a collaborative investigation coordinated by Forbidden Stories, involving more than 40 journalists representing 12 media outlets (Forbidden Stories, Paper Trail Media, RFI, Bellingcat, Die Zeit, Le Monde, France 24, ARIJ, The Seventh Eye/Shakuf +972 Magazine, ZDF and Der Standard) who continued the work of Gazan journalists and investigated about the threats and difficulties they are facing.

Israel said early on in the war it could not guarantee safety of journalists in Gaza. Hamas has also been known to use drones to target Israel Defense Forces (IDF) positions and has used drone footage in propaganda videos. The investigative consortium contacted the IDF about the cases mentioned in this story, how they determined the drones posed a threat, the IDF rules of engagement with drones and how they define someone as a terrorist. The IDF did not answer specific questions about individual cases, nor did they provide further details about the two individuals in this piece, but they did tell us the IDF rejects outright the allegation of systemic attack on journalists.
“The IDF cannot address operational directives and regulations as they are classified. However, every operational action or strike is mandated by IDF directives, which instruct commanders to apply the basic rules of the law of armed conflict,” they said.
The full cost of the war still needs to be assessed through on the ground visits, when a permanent ceasefire is agreed, but in the meantime, satellite imagery combined with drone footage and other imagery captured by journalists in Gaza has been critical to lay bare the level of destruction.
For instance, a brief drone video lasting just over one minute and published in January this year by the AFP news agency after the first phase of the recent ceasefire was implemented, shows the rubble of scores of hollowed-out homes in Rafah. Some are completely levelled, others severely damaged.
The most recent interim damage assessment compiled by the World Bank, European Union and United Nations estimates almost 300,000 homes have been damaged or destroyed across Gaza and that 95% of hospitals are non-functional.
In order to continue the reporting on the extent of damage caused by the war in Gaza, Bellingcat and our partners are sharing satellite imagery and using a 3D model technique called photogrammetry to capture and show the areas the journalists had been filming or were unable to report on.
On February 15, 2024, about six months into the conflict, the United Nations shared a short video on social media showing dozens of hollowed out or partially collapsed buildings located in Gaza City’s Al-Shati Refugee Camp. The video starts with a birds-eye view filmed by a drone that shows entire blocks levelled in the compact neighbourhood.
Over the course of more than 12 months of conflict, Al-Shati Refugee Camp saw heavy destruction.
The neighbourhood and its surroundings were an early target for IDF ground operations inside Gaza, with the IDF announcing in mid-November 2023 that it had completely captured the area. The IDF said it was a main Hamas stronghold. One video geolocated by a Geoconfirmed volunteer shows the heavily damaged coastal side of the Al-Shati Refugee Camp a year later. The camp also abuts an archeological site to the north that was potentially damaged by the ground operation and airstrikes, as previously documented by Bellingcat and Forensic Architecture.
The images shared by UNRWA were filmed using a drone by Palestinian journalist Abdallah Al-Hajj. Nine days after they were posted online, he was back filming in the same area when he was seriously injured in an Israeli army strike, losing both his legs.
Previous photos taken by Al-Hajj had been shared by UNRWA earlier that month and almost 300 of his photos were included on UNRWA’s film and photo archive, with some aerial photos taken by Al-Hajj as early as 2020. He had previously worked as a photojournalist for the Jerusalem-based, Palestinian newspaper Al Quds as well as other media.
Speaking to our partners Forbidden Stories, Al-Hajj said he felt a journalistic responsibility to continue filming in Gaza during the war but took several precautions including only filming when clashes were over and when there was no immediate conflict in the vicinity. On the day he was injured, he said he’d only filmed with the drone for about five minutes and completed the filming when he was hit. He told our partners at Forbidden Stories he wasn’t wearing his press vest because he felt identifying himself as a journalist put him at greater risk.
The IDF previously told Le Monde that it had “eliminated by an IAF aircraft” a “terrorist cell using a drone, posing an imminent threat to forces in the Shati area.” Apparently the same strike was referenced in this reporting from February 25.
It’s not clear where the threatened forces referred to in the IDF statement were. It was reported that the IDF conducted a two-week-long raid in Al-Shati Refugee Camp in early February but it was apparently finished by February 15.
Based on SkySat imagery from Planet Labs, IDF vehicles were visible earlier in the month on February 8 about 2.5km from Al-Shati Refugee Camp near Gaza City’s Islamic University campus. The vehicles were gone a week later in February 14 imagery.
Photos and videos show that the IDF were present about 3.5km south of Al-Shati Refugee Camp along the Al-Rashid Road throughout the month of February, though it’s not clear if they were still present at the location when Al-Hajj was filming.
After the strike, SkySat imagery from Planet Labs shows that Al-Hajj’s home south of Gaza City in the Zeitoun neighbourhood was destroyed. It was standing in February 24 imagery but in February 28 imagery showed that it was gone.
We asked the IDF about Al-Hajj’s case including asking them to explain the immediate threat that was posed by the drone, why he was hit and what information they had about him but they did not respond to specific questions about this case.
Al-Hajj told our partners Forbidden Stories the accusation that he was part of a terrorist cell or affiliated with Hamas was a “false and unfounded charge.”
Additionally he said he was checked by IDF troops twice after the incident, in Al-Shifa Hospital where he was admitted and again when he left the Gaza Strip via a Netzarim checkpoint to travel to Qatar for medical treatment. “If I were Hamas, I would not have gone out of the Gaza Strip for treatment,” he said.
To continue documenting the changes in Al-Shati Refugee Camp brought about by the war, Bellingcat used drone images provided by Forbidden Stories to create a 3D model of the current state of the area through photogrammetry, a technique that reconstructs objects in 3D by analysing the parallax between multiple photos.
Forbidden Stories also provided drone images of Jabalia, previously one of the most inaccessible areas in Gaza for journalists, which Bellingcat used to create an additional 3D model.
Photogrammetry is the science of extracting measurements from photographs. In this case, photogrammetry is employed to extract large scale, measured 3D models from a dataset of aerial photographs of Gaza captured by a drone.
Bellingcat processed the 3D models of Jabalia Refugee Camp and Al-Shati Refugee Camp using Agisoft Metashape, which requires a paid license. Alternative open-source programs for photogrammetry include Meshroom and COLMAP.
The 3D models were created from the drone photos in four steps, though different steps may be applicable to different scenarios. First, corresponding features are detected and matched between images. Then, using the corresponding features, camera positions are triangulated using the camera parameters (ie. focal length, pixel size, lens distortion) and repeatedly adjusted to increase the accuracy of the reconstructed camera positions through bundle block adjustment. Next, depth maps are created for each image using dense stereo matching, which compares images from similar viewpoints to find the small differences between them caused by parallax. These depth maps are used to create a 3D mesh that serves as an accurate recreation of Gaza. Finally, a texture is created by projecting the original drone photos onto the mesh in a way that seamlessly blends them, giving the final result of a photorealistic and dimensionally accurate 3D model.
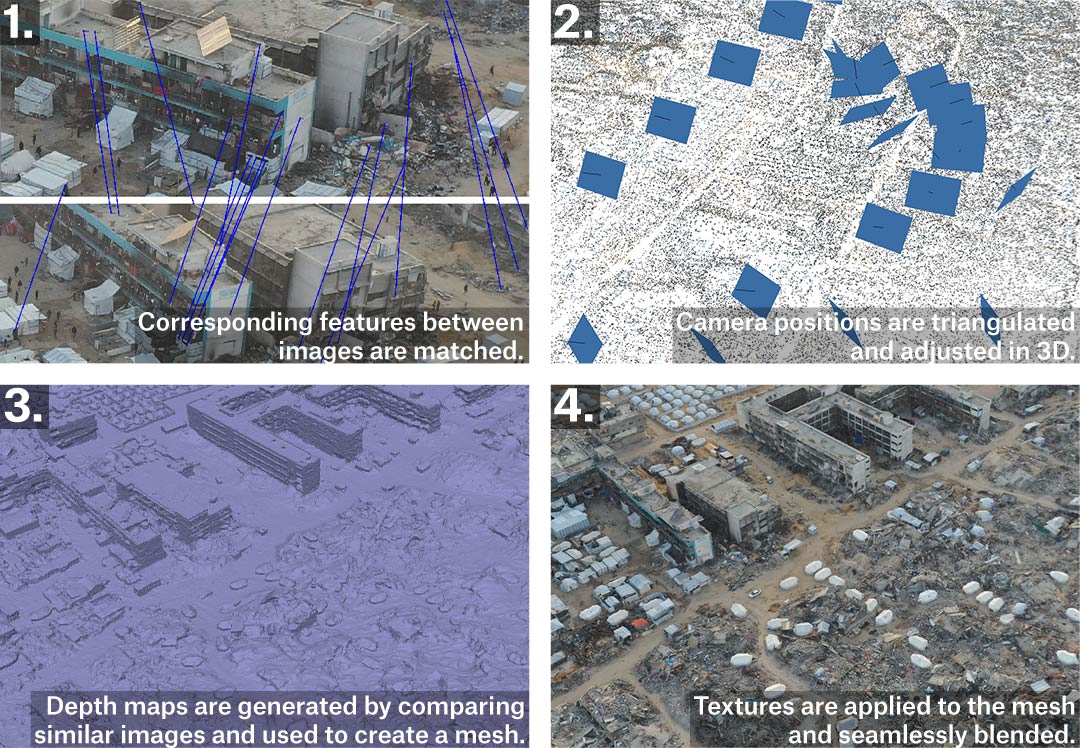
Photogrammetry and the 3D models do have some shortcomings – in particular, areas not visible to the camera cannot be accurately reconstructed, such as the insides of heavily damaged buildings that are hidden by overhanging floor slabs. Further, the varying distance between the camera and the features it captures leads to variances in the level of detail in the model, as does the varying number of photographs of any given feature – for example the narrow alleys in Al-Shati Refugee Camp can only be seen from certain angles in the photogrammetry, meaning they aren’t as accurately depicted as more visible areas such as the courtyards of UNRWA schools in Jabalia Refugee Camp.
While satellite images can be difficult to interpret and are limited in resolution, the 3D models produced with photogrammetry allow viewers to place themselves in the environment. This approach provides an unparalleled look at the landscape of Gaza after nearly eighteen months of war, including buildings reduced to rubble, craters left behind by intense bombing, and thousands of tents sheltering displaced persons. A similar technique has been used in other open source investigations, notably in the recreation of the Mariupol Drama Theatre in Ukraine which was used as a civilian shelter until it was bombed by Russian forces in 2022, as well as numerous investigations by Forensic Architecture.
Within the models presented on this page, we have identified key sites including schools, homes and areas damaged by fighting.
About a month before Al-Hajj was injured in Al-Shati Refugee Camp, Mustapha Thuraya and his colleague Hamza Al-Dahdouh were killed in an IDF strike while they were driving in southern Gaza on their way back from reporting in Al-Nasr Village. Thuraya was a freelance video journalist who had filmed for Al Jazeera, AFP, Reuters, and Getty Images among others. He was killed on January 7, 2024 in Al-Nasr Village northeast of Rafah, shortly after filming with his drone.
According to reporting by the Washington Post, Thuraya and Al-Dahdouh arrived at the location about 10:30am, when an airstrike forced them to leave the area by car. They were following an ambulance when they were struck while on the road at approximately 11:10am.
Thuraya began actively covering the war not long after it started, sharing dozens of videos on his social media pages. In many of the videos, his drone controls are visible in his hands as he filmed himself in front of scenes of destruction. In some of the videos he can be seen wearing a press vest, though it is unclear if he was wearing it on the day he was hit.
The final thing Thuraya filmed with his drone was the site of an IDF airstrike in southern Gaza that took place the same day. The area he was filming is a rural part of southern Gaza that sits between Khan Yunis to the north and Rafah to the south. Overall, the area was relatively untouched by Israeli ground operations, though satellite imagery shows that the IDF cleared a small area of greenhouses within 1km of the airstrike location in late July and August 2024. Recent Planet Labs imagery from January 2025 shows that most of the larger area is still intact, including the majority of the greenhouses.


Before and after satellite imagery from Planet Labs shows the location where Mustafa Thuraya and his colleagues were filming shortly before they left in their vehicle and were killed while on the road south. The most recent imagery shows that some greenhouses have been destroyed but otherwise the area is largely unchanged. Credit: Planet Labs PBC.
The IDF initially claimed the January 7 strike on Thuraya and Al-Dahdouh’s car was in response to drone activity that posed a threat to IDF troops. They later released further reasoning for the strike, stating that Israel’s military intelligence department had confirmed that Dahdouh was a member of Palestinian Islamic Jihad and Thuraya was a member of Hamas, — something rejected by both Al Jazeera, which they were working for at the time — and the journalists’ families.
The Washington Post, quoting Thuraya’s friend and fellow journalist Shadi al-Tabatiby, said Thuraya had previously worked for around five years as a photographer for the Ministry of Religious Endowments, part of Gaza’s Hamas-led government. It’s not clear when his employment ended.
Our analysis found the closest potential IDF activity to where the strike on Thuraya’s vehicle took place — clearing activity that was visible near a cluster of buildings — was more than 5km away, something that’s visible in Planet SkySat imagery from the day of the strike. An analysis from The Washington Post came to a similar conclusion regarding the IDF presence near where Thuraya was filming, even though they analysed a smaller area, finding no evidence of IDF military activity or deployments within 2km of the site.
The Washington Post was also able to review the drone footage filmed by Thuraya and found that no IDF “soldiers, aircraft or other military equipment” was visible in the footage.
The IDF did not respond to the consortium’s specific questions about Thuraya and the circumstances surrounding his killing.
While the area in southern Gaza that Thuraya was filming before he was killed has remained mostly unchanged, Rafah — where he and Al-Dahdouh were returning to following the filming — has been decimated.
Drone imagery is still dangerous to capture in the south, even during the ceasefire. AFP published drone footage shortly after the first phase of the ceasefire was agreed, but it only covered a small area in Rafah. High resolution satellite imagery remains one of our best ways to observe the mass destruction in Rafah. Bellingcat covered this in August last year, but since then more buildings have been destroyed with entire neighborhoods that were previously standing demolished, particularly near the border areas.
Hundreds of buildings in both the central Rafah area near the large marketplace and the Al-Ganinam neighbourhood have been demolished. The few remaining buildings in the Tal as-Sultan neighbourhood we examined in the August investigation have also been razed to the ground.
Bellingcat is sharing the same satellite imagery analyzed in last year’s piece alongside more recent Planet imagery captured after the ceasefire on January 30 2025.
Credit: Planet Labs PBC.
Prior to the ceasefire the Committee to Protect Journalists identified at least three other drone journalists who were killed in IDF strikes, but we have not been able to find further open source details on circumstances around their deaths.
One area that was difficult to film prior to the recent ceasefire because it was too dangerous was the Jabalia Refugee Camp and its surrounding area. This was one of the worst affected areas of Gaza, which Bellingcat documented earlier this year.
Bellingcat was able to create a photogrammetry model of one of the worst hit areas in Jabalia Refugee Camp using drone footage provided by Forbidden Stories which was captured during the recent ceasefire.
On Saturday, March 15, two IDF air strikes in the northern Gaza city of Beit Lahia killed at least seven people, including Mahmoud Samir Isleem Al-Basos also known as Mahmoud Al-Basos, a drone journalist who previously provided work to Reuters and the Turkish news agency Anadolu
Among the dead were aid workers and cameramen on a mission for the London-based Al-Khair Foundation who said they were filming preparations of a Ramadan iftar meal and documenting site preparation for the extension of the camp.
“We were deeply saddened to learn that journalist Mahmoud Al-Basos, whose work Reuters published in the past few weeks, was killed in Gaza by an Israeli strike while on a mission for the Al-Khair Foundation. Our thoughts are with his family at this difficult time,” a Reuters spokesperson told us.
Mahmoud Samir Isleem Al-Basos was previously hired by Forbidden Stories to film drone footage for this project during the recent ceasefire. This initiative aimed to continue the work of drone journalists who had been killed while documenting the war and help readers visualise the unprecedented scale of destruction through detailed 3D aerial maps.
The IDF stated the March 15 strikes targeted “terrorists,” including two operating a drone, and released a list of names and photos. The IDF statement contained misidentifications and names of individuals the media office in Gaza said had not been killed, causing confusion.
Mahmoud Samir Isleem Al-Basos was neither named nor pictured in the list published by the IDF. Instead, the IDF listed another individual, with a similar name, describing him as a “Hamas terrorist operating under journalistic cover,” and said there was a link between the drone used in Beit Lahia and Islamic Jihad.
However, the consortium’s investigations indicate the individual named by the IDF has no direct link to Mahmoud Samir Isleem Al-Basos, and was not killed in the strike.
Al-Khair Foundation said, meanwhile, they “utterly refute” any claims that their team were connected to militants. They say that the members were deliberately targeted while on a “purely humanitarian mission.”
We geolocated the two strikes in Beit Lahia, and according to our findings, the first was approximately 2km from the Israeli border and an IDF outpost situated nearby and the second approximately 3km away, raising questions about the threat described by the IDF.
Asked twice by the consortium to provide evidence to support the different accusations, the IDF refused, stating it “will not elaborate on the published statements”.
The Committee to Protect Journalists have added Mahmoud Samir Isleem Al-Basos to their list of slain journalists.
Reserve Lieutenant Colonel Maurice Hirsch, who served for 19 years in the Israeli army’s legal corps, told our partners at Paper Trail Media there is an inherent risk in flying a drone during a conflict in proximity to fighting forces.
He said if a soldier spotted a drone in a combat zone near fighting forces, “I certainly wouldn’t assume any wrongdoing if that drone and its operators were targeted (…) it wouldn’t be unreasonable to assume they were part of an enemy force.”
Our partners at Forbidden Stories also spoke to IDF reservist Michael Ofer-Ziv who served during the recent conflict, including for the first two months of the war in the Israeli military centre of Sde Teiman where he spent his time observing black-and-white footage filmed from Gaza. His role was to verify that the IDF wasn’t firing on its own soldiers. Ofer-Ziv completed his tour in December and has refused to return to service, signing a letter stating that he is no longer willing to participate in the war.
“At no point during this war did I receive an official document outlining the rules of engagement. And that’s a problem, because it leaves a lot of room for interpretation,” he said.
He didn’t know of the Gazan drone journalists we investigated but said there was an “understanding and a general vibe in the war room” that “if you see anyone piloting a drone, and that drone is not ours, you shoot the drone and the person who uses it, no questions asked.”
Asked about journalists using drones he told Forbidden Stories: “We never spoke of it.”
We contacted the IDF as part of the investigative consortium and asked whether they had a specific policy for dealing with drones in Gaza, and if so how they distinguished civilians from military targets. We asked about the individual cases listed above but were not provided any further details. The IDF has previously claimed that Thuraya was a member of Hamas, a claim which Al Jazeera and his family deny, and stated they hit a “terrorist cell” target in the IDF strike that injured Al-Hajj. Al-Hajj says this a “false and unfounded” charge.
The IDF did not answer specific questions about individual cases, nor did they provide further details or evidence about the incidents outlined above, but they told us the IDF rejects outright the allegation of systemic attack on journalists.
“The IDF cannot address operational directives and regulations as they are classified. However, every operational action or strike is mandated by IDF directives, which instruct commanders to apply the basic rules of the law of armed conflict (LOAC).”
They reiterated that the IDF is committed to principles of distinction, proportionality and precautions and that the IDF only strikes members of organised armed groups and individuals directly participating in hostilities. They told us some of the people listed by Forbidden Stories were members of Hamas’ military wing and were therefore lawful targets under international law, but they did not provide evidence to support this.
They also told us that “the IDF takes all feasible measures to mitigate harm to civilians, including journalists. Regarding objects, the IDF only strikes military objects. The IDF does not deliberately strike civilian objects, including those affiliated with media outlets or belonging to journalists, provided that they are not legitimate military targets.”
In their reply, they stated “the incidents have been referred to relevant mechanisms for further investigation.” But did not confirm whether the specific cases highlighted here are being investigated, and did not specify which incidents they were referring to. They also stated that exceptional incidents are subject to lessons-learned processes and are thoroughly examined and addressed accordingly by the appropriate enforcement mechanisms, and may lead the relevant cases to command, disciplinary, or criminal measures.
The Committee to Protect Journalists told us that drone use for journalism is still a relatively new trend.
“We encourage journalists generally to do their own risk assessments depending on their own situation on a case by case basis,” Doja Daoud, CPJ’s Levant Program Coordinator, told us.
She made clear that: “A journalist shouldn’t be killed and should be protected under international law.”
Daoud said CPJ had documented cases where drone journalists were killed. And in at least one case, a journalist had told them his drone had been disabled or controlled remotely.
“So there are other ways to deal with a drone, even in conflict areas or in a proximity of Israeli soldiers, without killing a journalist.”
As for IDF claims about journalists being combatants, Daoud said in many cases, including that of Mustapha Thuraya, CPJ is still yet to see any clear proof.
“Israel has repeatedly made similar unproven claims without producing any credible evidence. And to date CPJ has documented multiple cases with no evidence at all that any journalist was engaged in militant activity.”
“Attempts to smear, delegitimise, and criminalise journalists who are doing their job are outrageous and irresponsible as they put journalists at further risk. And targeting journalists with disinformation endangers them more.”
Irene Khan, the United Nations Special Rapporteur on Freedom of Expression and Opinion told us that with no western reporters allowed in, local Palestinian journalists, “are putting their lives on the line so that we may be better informed on what is happening and so that the atrocities being performed there can be exposed.”
Using drones to show what’s happening has only increased that risk, with Khan adding that since using commercial drones as a tool is still relatively new — for both journalists and combatants — and the rules are less clear.
“International humanitarian law does not say that you are not allowed to use drones, because it is a civilian object and there are many civilian objects that can be converted and used for military purposes. But it is not wrong as a civilian to use it.”
But, Khan says, the onus is on the combatants — the IDF and armed groups in Gaza — to ensure civilians are not being targeted if it’s difficult to distinguish the purpose of a drone. From a legal point of view, international humanitarian law heavily favours journalists.
“So the onus is actually on the combatants to make sure that if we cannot distinguish, then we need to do more to ascertain whether we might, by mistake, kill a civilian, we might kill a journalist.”
“And in all those areas, I think the standards that the IDF seem to be applying are lower than what I would call due diligence. I think there has been a tendency on the side of the IDF to assume that some of these journalists have links with Hamas and therefore are legitimate targets.”
With such a high journalist death toll throughout the war, Khan says there needs to be more done to protect journalists in the future — including carrying out independent investigations.
“I come back to the issue of impunity. It has to be addressed. So every time a journalist is killed, there should be a full investigation as to what happened and to make sure that if there was a mistake made, what are they doing correcting those mistakes? … And I don’t understand if the IDF is so sure that they didn’t make a mistake, why are they not allowing others to come in and investigate it?”
In one of the cases where the IDF completed an investigation into one of its strikes on civilians, they said its strikes on a World Central Kitchen aid convoy last year was the result of aid workers being misidentified as gunmen. A major and colonel were dismissed and a brigade commander was formally reprimanded.
Some Palestinian journalists are continuing to film with mobile phones, cameras and drones, despite the risks.
With the recent ceasefire collapse, the risk to journalists operating on the ground is likely to increase again, heavily restricting our view of the impact of the conflict on Palestinian communities in the Gaza strip.
Youssr Youssef, Magdalena Hervada, Charlotte Maher and Logan Williams contributed to this report.
Photogrammetry models in this piece were created using Agisoft Metashape and Cesium. Source Credit: Forbidden Stories/Stringer. Photogrammetry model: Bellingcat/ Thomas Bordeaux.
Bellingcat would like to thank our partners at Forbidden Stories, Die Zeit, Der Standard, Le Monde, RFI, ARIJ and Paper Trail Media for collaborating on this project.
The post Shot From Above: The Dangerous Work of Drone Journalists in Gaza appeared first on bellingcat.